This post was co-authored by Levi Gundert with contributions from Emmanuel Tacheau and Joel Esler.
In the last month we have observed high levels of traffic consistent with the new “RIG” exploit kit (EK), as identified by Kahu Security. This new EK reportedly began being advertised on criminal forums in April, which coincides with when we first began blocking this traffic on April 24th. Whilst the release of a new EK is not uncommon, RIG’s appearance is significant in three ways. First, because of the sheer amount of traffic we are seeing – we have so far blocked requests to over 90 domains for more than 17% of our Cloud Web Security (CWS) customers. Second, because we have seen it being used to distribute “Cryptowall”, the latest ransomware to follow in the success of the now infamous “Cryptolocker”. And third, because it continues the trend of an increased reliance upon Silverlight in EKs which we have previously written about for both the Fiesta and Angler kits. Like these other kits, we have seen RIG using malvertising to perform a drive-by attack on visitors to high profile, legitimate websites. This accounts for the high amount of traffic we have seen in the last month.
Exploitation
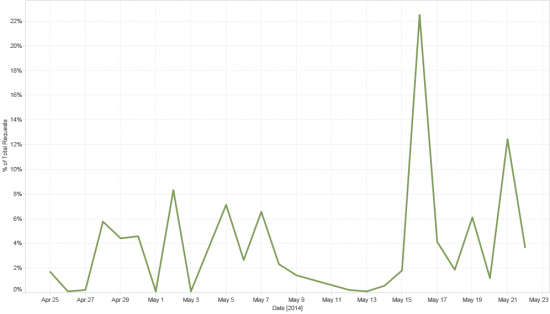
The above chart shows the number of requests over time for RIG landing pages between April 24th and May 22. These landing pages have a similar URI structure: query string which contains a constant alphanumeric string, a vertical bar, and then a variable alphanumeric string. E.g:
proxy.php?PHPSSESID=njrMNruDMlmbScafcaqfH7sWaBLPThnJkpDZw-4|YmIwOWQyNDZhY2MxMGRjODZmYjk0ZDMxZmZmMzNkMmIThe constant string which they are using before the vertical bar has changed over time:
| njrMNruDMlmbScafcaqfH7sWaBLPThnJkpDZw-4 | Until May 16 |
| njrMNruDMlmbScafcaqfH6dbZBCNAhXUhduH2_aR | May 16 – 18 |
| njrMNruDMh7GA5zBJPPcTKVDKU7WGFnYmMzMhe6JVg | May 16 – 21 |
| njrMNruDMhvJFIPILuXASbtANlCDQgTe2c7B2w | After May 21 |
Visitors to the landing pages get served one of several exploits, which helpfully identify themselves via the “req” query string:
| req=jar / req=xml | java |
| req=xap | silverlight |
| req=swf OR swfIE | flash |
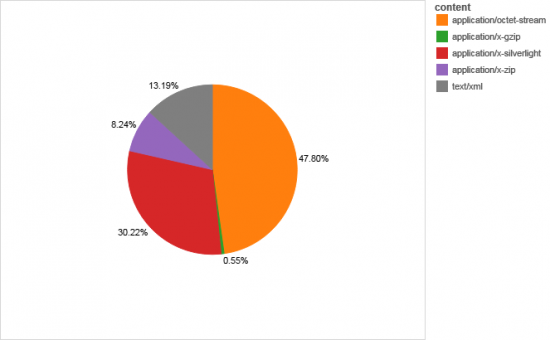
If we look at the content type of the files requested, we can see that Flash, which is detected as “application/octet-stream” makes up the bulk of the requests, followed by Silverlight. The java applet is distributed via Java Web Start which makes use of jnlp files: these are detected as “text/xml”.
We have observed RIG using files with the following MD5s :
Java:d2b2f4b7f03df66db1fda29575193774
e7962ae9d44b7a2ddf89395a6b329fca
e98db4d3d52fc3957a99423ccb171903
fe4c2dabfe2da3eed6bb8adbb9c04cab
Silverlight:
1705ea199cbbd2bb4fc53935c60a10be
22cc36263808e35e36c6043fe09e287c
75096049badc5043f7c0fc335edc2cfe
76039da2c7db3d19bf702ac0ee28ed7c
76dfbb5231b05b1e47c965ed9e50ec7b
94a10b6225b04b2d834fd4d62cbf9d42
a6f406897b8b690ea7db53ac31c8e8df
bb07beb887f8a6d06114809ef326d9f6
fd9b4272d58327ace6ccad8550a33d17
Flash:
09ad04f6d65b157f1ad7f40b0dafbbba
4233c65ebaa35256aca49ddaeae2d1bc
4848a2c3cd6e874b6ec1413434c98ab4
487e5961618724eadce3c2489cb4cbbc
4c156f2c9743a41d0c85f61620424de5
54eead3f0cb46485d38115d5f0311c68
584acc95b71c59df236ce2a3aeb0a619
9a8f29b504382c5a9fae056f58352a7b
9e819e71ee8da5f9c4185bb13fd3c456
b67a4fd9c4e481731190035d94f0da52
d18d92c17d2fd18d7009b3769ea5df81
d99103c9ff0f443e5359ae53cd37e2a2
ff6d47461dd904b1ff2cb1f9eb1f63ad
These appear to be exploiting the following vulnerabilities:
- Silverlight: cve-2013-0074
- Java: cve-2013-2465 and cve-2012-0507
- Flash: cve-2013-0634
Cryptowall
Upon successful exploitation the payload is downloaded from paths with the query parameter “req=mp3”. We have observed this infection path resulting in Cryptowall ransomware. The following message was present as a unicode Registry Key after infection:
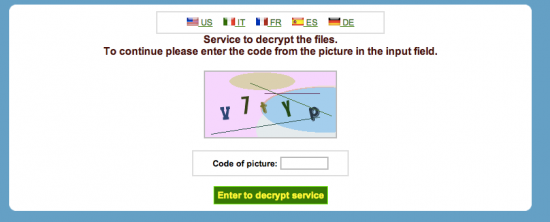
Path: HKEY_USERS\Software\9BEFA355ED9F4D1C986110581468323D Name: 2 Type: unicode Data: What happened to your files ?All of your files were protected by a strong encryption with RSA-2048 using CryptoWall.More information about the encryption keys using RSA-2048 can be found here: http://en.wikipedia.org/wiki/RSA_(cryptosystem) ******What does this mean ?This means that the structure and data within your files have been irrevocably changed, you will not be able to work with them, read them or see them,it is the same thing as losing them forever, but with our help, you can restore them. ****How did this happen? Especially for you, on our server was generated the secret key pair RSA-2048 – public and private.All your files were encrypted with the public key, which has been transferred to your computer via the Internet. Decrypting of your files is only possible with the help of the private key and decrypt program, which is on our secret server. ****What do I do ?Alas, if you do not take the necessary measures for the specified time then the conditions for obtaining the private key will be changed.If you really value your data, then we suggest you do not waste valuable time searching for other solutions because they do not exist. ****For more specific instructions, please visit your personal home page, there are a few different addresses pointing to your page below: 1.hxxps://kpai7ycr7jxqkilp[.]torexplorer[.]com/5f2i 2.hxxps://kpai7ycr7jxqkilp[.]tor2web[.]org/5f2i 3.hxxps://kpai7ycr7jxqkilp[.]onion[.]to/5f2i ****If for some reasons the addresses are not available, follow these steps: 1.Download and install tor-browser: http://www.torproject.org/projects/torbrowser.html.en 2.After a successful installation, run the browser and wait for initialization. 3.Type in the address bar: kpai7ycr7jxqkilp[.]onion/5f2i4.Follow the instructions on the site. ****IMPORTANT INFORMATION: Your personal page: hxxps://kpai7ycr7jxqkilp[.]torexplorer[.]com/5f2i **Yourpersonal page (using TOR): kpai7ycr7jxqkilp[.]onion/5f2i Your personal identification number (if you open the site (or TOR ‘s) directly): 5f2iLike other forms of ransomware, Cryptowall encrypts your local files and requires you to pay a ransom for the key stored on their servers. Upon infecting our test system, we were provided with the above links to TOR sites, and a personal identifcation number. Visiting the page presents you with a captcha followed by information about your ransom:
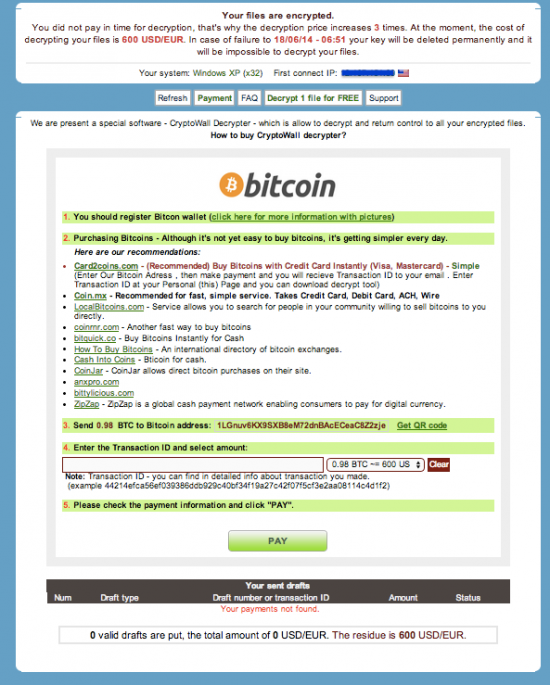
At the time of writing, our ransom had reportedly been increased three times to $600, with a deadline of 18/06/14 at 06:51 after which time the data would be irretrievable. This threat should be taken seriously – other ransomware has been known to make good on its warnings of data loss. Given the recent high profile reports of an FBI shutdown of Cryptolocker, it is worth remembering that whilst Cryptolocker has proven to be an extremely potent threat it is just one of several forms of ransomware including Cryptowall and Cryptodefense. Ransomware has proved to be a very successful form of extortion and we are likely to see new variants on the Cryptolocker theme for quite some time.
Traffic generation and distribution
The many-to-one relationship between websites and the affiliate ads included on them (the same ads can be served across many sites, and the same site can serve many different ads) makes determining the precise path which sent users to the malicious landing pages difficult. However, ad-networks like to track where their clicks came from, and because there are many stages of redirection involved in the complicated distribution of ads, they don’t usually have direct access to this information in the form of an HTTP header referer (sic) field. To get around this they often pass information about the original referrer across the various redirects using a query string parameter. For example, this is one of the referrer URLs to a RIG landing page:
ads1.solocpm.com/a.aspx?ZoneID=44709&Task=Get&PageID=1399370014&SiteID=1&BMPClickURL=http://ams1.ib.adnxs.com/click?991S6E8y1[…]./referrer=http%3A%2F%2Fwww.theguardian.com%2Fuk-news%2F2014%2Fmay%2F06%2Fboston-college-tapes-gerry-adams/clickenc=
Looking at the query string we can see that although this request came from ads1.solocpm.com, the “BMPClickURL” parameter suggests that it was redirected from the domain of another ad-network -ams1.ib.adnxs.com – who have used their own “./” separator to nest additional information within the BMPClickURL parameter. This information includes a “referrer” field which suggests that the original ad was encountered at “http://www.theguardian.com/uk-news/2014/may/06/boston-college-tapes-gerry-adams/clickenc=” (the guardian is a high-profile UK news site). Around 47% of the requests for RIG landing pages that we have seen came from this ads1.solocpm.com host, and of these, 90 were redirects from adnxs.com domains. Extracting the referrer fields from these requests gives us a sample of the variety of sites likely playing host to the malicious ads, including several high-profile ones such as altervista.org, apps.facebook.com and ebay.in (full list below).
We can also look at the location of our CWS customers encountering RIG to get a sense of which users are being redirected:
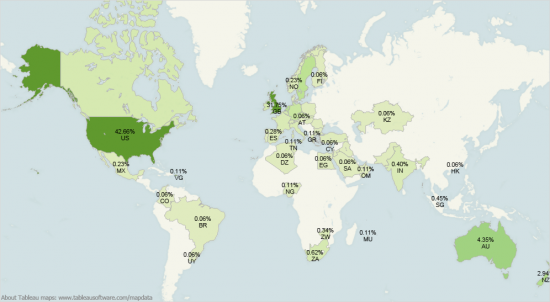
The US is, predictably, the most effected, with the UK coming in second.
Until May 22 RIG appears to have been making use of both newly registered domains and compromised legitimate sites to both host its landing pages and serve its exploits, all from paths ending in “proxy.php” (full list below).
A look at the landing page URLs reveals a high prevalence of the tell-tale “/wp-content/themes/” path which suggests that at least some of these domains are running the WordPress content management system. Using the Plecost fingerprinting tool which is included in Kali Linux, we can check all the domains for WordPress installations and plugins. An scan of the compromised domains returns responses from 35 of them, of which 29 are identified as running WordPress (versions from 2.9.x – 3.9.x). The variety in plugins and versions running on these sites suggests that these domains were probably compromised through a brute-force attack, rather than the exploitation of a particular vulnerability in the WordPress platform. Using existing legitimate sites to host the EK alleviates the need to create and maintain a dedicated domain infrastructure, and mitigates some of the problems associated with doing so: registering new domains, randomizing naming, using multiple email addresses, etc., in order to avoid easy attribution.
However after May 22 distribution appears to be from newly registered domains only using a variety of paths (full list below), including:
/config.php
/img/
/img/index.php
/index.php
/js/
/js/index.php
/video_plugin.php
The switch is probably an attempt to avoid detection after having gained visibility over the last month. Despite this change, the query string pattern for both the landing pages and the exploits remains constant after this switch.
Conclusion
There is a continuous churn in the EK market: new kits arrive, old kits mutate and evolve. RIG may have been very active during May, but no doubt that will soon change. However amidst the churn, patterns emerge: Silverlight continues to rise in prevalence, and Java exploits appear to be on the wane. We have seen a lot of exploit kits generating their traffic using malvertising recently, and this will surely continue to be a powerful and readily exploitable way of infecting users. When it comes to dealing with ransomware the best advice is to be proactive: maintain regular and full backups incase the worst should happen. But it bears remembering that however malicious the payload an EK happens to be armed with, it is still only as good as its exploits. Regularly updated and patched machines which do not have rich media platforms such as Flash and Silverlight enabled remain relatively immune from these kinds of attacks.
IOCs
Sourcefire VRT Signature ID numbers: 30936, 30934, 30935
Sample RIG landing page URIs
Sample RIG exploit and payload URIs
Domains seen hosting RIG from “proxy.php” before May 22:
atinsms.ir elainessalon.net bogacsi.hu musik2.org aiusdya6sdatshdajfaga.info autoclip.ml berluskonisimi.info blekorossda.info electrajack.cf fasgdjayagagasdagaaf.info fashizmuainua.info favoros19.info fekybutch.ga flowerscat.ga gimlerboy.ga huhundrakk.ml huiashdasu.ml iuaysjdkaoasd.info lightboss.ml lookmegafo.info miapiacheis.info misterjoy.ml mushdiasda.info mustafabustafa.info namelover.cf pepetsiam.ga quitmeon.ml reactman.ml restorefor.ml rightways.cf rocketman.cf rocketsuns.cf saiduhasdkasdsjad.info speedmans.ml sportcart.ml starvisit.ml testmeganrak.info toparkbuy.ml tutiasdutias.ml vitalaminda.ml waltersleep.ml whereisdisa.info wichstars.ml yourplane.cf retailpotential.com falklandsurgery.co.uk partnercis.de rudiniemeijer.nl takneveshteha.ir accionsocialcatolica.com northcapedesign.com drhoffman.com mobilsohbethatti.com sohbetnumarasi.org adanaslaw.com salomeasroom.com footyspeak.com rythmochoeur.com sweetdimension.net kuchar24.cz annex.mykula.org chiwifoto.com thedesigningschool.com alkaids.info grepolimetaf.info kennylarkson.info vasilopulos.info ghlu.org 14allcoaching.com buypva.net krudo.net itnews001.com joyofplenty.org condoasistremblant.com balatonlelle.org humancore.org androiduydu.net drahmetaslan.com bosnet.su laskaroutbound.com hana-books.net mywaydesign.org 46.182.30.59 testmeganrak.info vistkuklicha.info world.huasdusiasd.info www.bobversus.com queenstownnow.com lsbclimatesolutions.com quebradeparadigma.net cyberscape.net dmt.no buyer2.eazybestbuyuk.co.uk
Domains seen hosting RIG after May 22 change of path:
barateon.ga boxstercar.ml carparksme.ml clarkslave.ml clockspart.ml crashway.ml crymain.ml fatherspy.ga favoritezoo.co.vu fitnessspot.ga flywithandy.co.vu fortunesolders.cu.ma grandcanyons.info ladywish.ml lighexposive.info lightnightss.info likerintermen.info likervodka.ga littlemarry.co.vu lorensman.co.vu meganstatsun.info niceparty.ml pizzacra.ml restwater.ml sisterbony.co.vu swiftmonth.info teachersandy.co.vu teapots.ga trainpain.co.vu trestiask.co.vu tumblerbest.ml vekselpapi.info wichdeutch.info www.alexdime.info www.popbackit.ml www.vekselpapi.info www.versacemod.ml www.wolfexpand.info xeroxpay.ga yearsun.ml zambialife.ml
Example domains extracted from the query string of ads1.solocpm.com referrers:
altervista.org amung.us apne.tv apps.facebook.com awkwardfamilyphotos.com detik.com ebay.in elderscrolls.wikia.com elmundo.es gmx.co.uk gmx.fr go.com homepage.voetbalzone.nl html.rincondelvago.com izismile.com ja606.co.uk jerusalempost.com linkiest.com mail2web.com marca.com messagerie-12.sfr.fr newspage.voetbalzone.nl pi-news.net streetmap.co.uk studymode.com tamilo.com thatgrapejuice.net u4961p3019.ilyke.net webmail.earthlink.net wiki.answers.com wimp.com www.articlesbase.com www.brotherjohnf.com www.carzone.ie www.cheezburger.com www.findagrave.com www.hibapress.com www.ibancalculator.com www.ilfattoquotidiano.it www.jetztspielen.de www.mathe-lexikon.at www.myzimbabwe.co.zw www.net.hr www.search-document.com www.shetlink.com www.streetmap.co.uk www.theguardian.com www.thelocal.se www.thesportsbank.net www.thetallestman.com www.verkenner.be www.vesselfinder.com www.worldupdates.in www.yasni.info xtensionplus.com






According to the analysis of Cryptolocker done by Emisoft back in September (http://blog.emsisoft.com/2013/09/10/cryptolocker-a-new-ransomware-variant/), Cryptolocker uses AES 256 to encrypt the files (generating one AES key per file extension locally), and one RSA 2048 public key from the Command and Control Server to encrypt the AES keys. That makes sense.
I have seen no similar reporting on Cryptowall. Everything that I have been able to find seems to indicate that Cryptowall is using RSA 2048 to encrypt the files, with no mention of AES or other private key algorithm.
Can you confirm that, unlike Cryptolocker, Cryptowall is using one Command and Control Server provided RSA 2048 public key exclusively to encrypt the victim’s files?
Thank you.
Ted