Buzz… I pull out my phone and see my pre-boarding reminder. I click the flight number pre-authorized and -populated in my ridesharing app. A car arrives minutes later, and the next thing I know my driver has pulled onto SFO’s tarmac. Directly in front of me, I see my plane’s boarding stairs about a hundred feet away. At the bottom of the stairs, a friendly cabin crew member checks my electronic boarding pass and biometric identity.
Sadly, the era of direct airplane boarding is not yet here. A decade ago, we always needed to first visit an airline counter to retrieve our boarding pass and perhaps check our bags. And then, quite nearby, pass through a TSA checkpoint. If we had bulky luggage, we accepted some extra travel time. And while the checkpoint delays increased when we added advanced security after 9/11, they reverted to previous levels using more efficient routing via TSA PreCheck or Clear. Many of us save some time by checking in online and packing light to avoid checking baggage, but none of us can directly board a plane — imagine the user experience if we could.
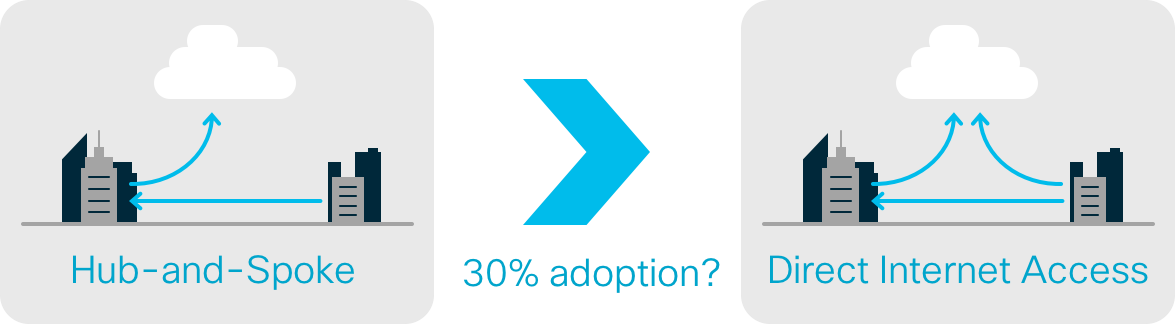
For enterprise networking, we entered the direct internet access (DIA) era a decade ago, but the transition from hub-and-spoke has been very slow. I don’t know about you, but I would be boarding planes directly today if I could. So, why have only 30% of enterprises deployed DIA at their branches? Keep reading to learn why.
Let’s back up and answer why enterprises are even adopting direct internet access (DIA) at branches and what it is. First, consider that 80% of an enterprise’s distributed workforce accesses the network from a branch. And it’s where 90% of the enterprise’s revenue is directly or indirectly earned. So, there’s many business outcomes — from increasing sales conversations and business intelligence to improving customer or employee experiences — that short-staffed IT teams must enable at the branch. One change is supporting non-traditional users (e.g. guests) and devices (e.g. IoT) to connect to the network. And another change is shifting application access from the data center to multiple clouds, such as Office 365 and AWS. So, IT teams want a direct route for guest user, IoT device, or Office 365 application traffic from branch locations to the internet.
Scalability, compliance, and security has caused too much turbulence
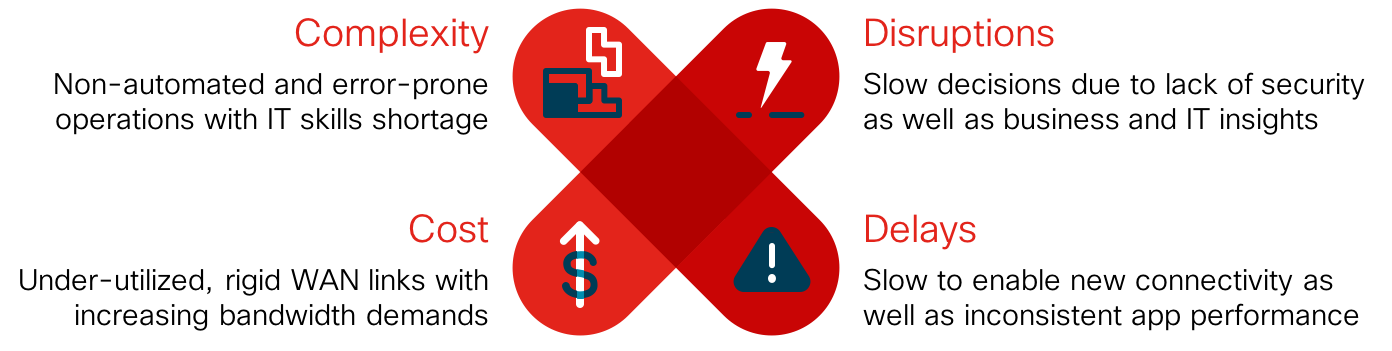
A key problem with my fictitious analogy was scalability. Imagine coordinating thousands of cars across SFO’s tarmac. Similarly, configuring tens to thousands of DIA breakouts plus site-to-site connections across your enterprise network has been complex. Most branch locations — from retail stores and hospitality venues to healthcare clinics and financial offices — have no on-premises IT staff. So, adding a separate internet circuit to every branch router for direct guest, IoT, or Office 365 access is a nightmare.
But an even bigger problem with my analogy was compliance and security. While I may have been pre-authorized to board, TSA must isolate me from possibly boarding a different plane. And even if my flight is secure, the destination airport may contain threats. Back to enterprise networking, if we enabled guest users or IoT devices to access the same internet circuit already used for point-of-sale systems at the branch without segmentation, it’d be a PCI violation. And if we route our branch traffic direct to internet rather than backhauling it through our data center’s security stack, infections and intrusions would skyrocket.
For the last two decades, branch users needed to connect to the data center to access your infrastructure (e.g. file servers) or software (e.g. customer relationship management). And so locating your internet edge nearby with a centralized security stack was efficient. Cisco built the routers and switches to connect our branch, campus, and data center locations altogether as a wide area network (WAN). Together with your service provider, Cisco co-founded an alphabet soup of technologies like MPLS, OSPF and IP multicast to securely carry voice, video, and other application traffic site-to-site or between data centers over the WAN. But today, this rigid WAN architecture is akin to our airports — it’s secure, but not a great experience. Branch users, connected devices, and application usage experience more delays and disruptions, and the IT team incurs more cost and complexity.
Software-defined architectures provides a smooth journey
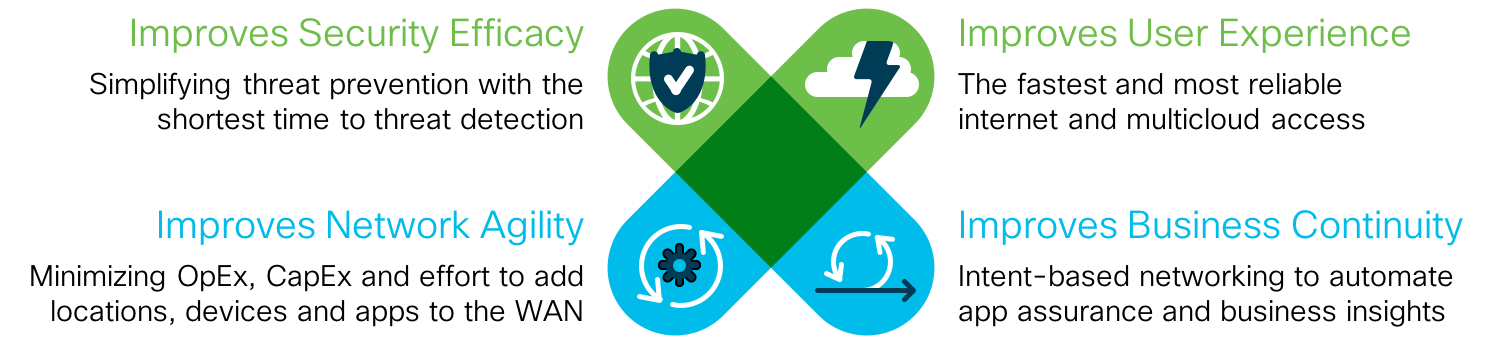
Just as Cisco’s software-defined access solutions have transformed and secured the data center and campus, Cisco’s agile, software-defined WAN solutions are transforming and securing the branch. By 2020, over half of WAN edge infrastructure refreshes will be based on SD-WAN routers and over 60% of branch offices will have deployed DIA; according to Gartner. The internet edge with a centralized security stack must be extended and distributed to the branch and/or cloud without adding cost or complexity. And secure connectivity over the public internet must be secured equal or better than your service provider’s private MPLS to enable a hybrid WAN.
PIX was developed by Cisco two decades ago and became one of the first widely adopted firewalls. Cisco continues to innovate by embedding next-gen firewall and other security capabilities directly into the network at both the branch edge and the cloud edge. MPLS was co-developed by Cisco as the first secure, private WAN fabric. Cisco continues to innovate with edge-to-edge segmentation and zero-trust authentication over the public internet with proven scalability.
As the hub-and-spoke era enters decline, and the direct internet access era takes off, there is no networking and security vendor more trusted than Cisco. We offer a cloud-managed and -delivered full security stack and secure SD-WAN fabric that is integrated into thin, rich, or full-stack routers. We encourage you to learn more about how Cisco will help you enable secure branch transformation from the branch to cloud edge with the most flexibility. And most importantly, with the quickest time to value.
To learn more visit, Secure Branch on cisco.com, Secure Branch at-a-glance, or Secure Branch on ThreatWise TV. Or visit our Network Security booth at Cisco Live US from June 10-14.






excellent blog Barry. The airport analogy is spot on. In line with your TSA analogy, as we move more and more of our corporate "crown jewels" to an off-prem multi-cloud environment, security, both data, and access, become primary to enable the business to succeed.