News agencies like ABC News, CNN, and others have run stories on the FBI sting operation against more than 100 hackers who were involved in using and/or distributing the Blackshades RAT (articles in the hyperlinks for reference). For a mere US$40, a novice computer user can become a hacker and gain access to anyone’s computer, including gaining control over their video camera. If this novice hacker in the making needs help operating the RAT, many video instructions can be found on YouTube. This would be a form of free technical support. With over an estimated 500,000 computers infected, that leaves behind a serious footprint of compromised devices. As Marty Roesch, Cisco VP, Security Architect would say, “If you knew you were going to be compromised, would you do security differently?”
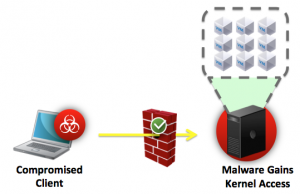
With over a half a million computers compromised from a single remote access toolkit, it is reasonable to think that a high percentage of those compromised computers would unknowingly be brought back to work and connected to the corporate network. Although inexpensive, the Blackshades RAT has an extensive set of capabilities such as keystroke logger, web cam control, full file access, etc. More than enough for the cyber attacker to assume the full identity of the owner of the compromised computer to allow them easy access to the business critical servers inside the data center as depicted in the diagram.
Most organizations will have implemented perimeter security and some level of segmentation with access control policies to ensure only authorized users can access information in the data center on a “need to know” basis, but otherwise there may be very little threat defense capabilities.. Unfortunately, this approach is based on outdated assumptions:
- The “authorized” user is really who they say they are.
- The authorized user is in control of their device and the device accessing the data center has not been compromised.
With the capabilities provided by Blackshades RAT, or most any other RAT of choice, the cyber attacker can assume the identity of the owner of the compromised computer.
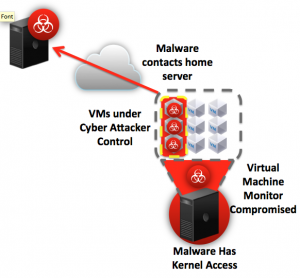
As a result, the cyber attacker has direct access to the data center and will begin to attempt to compromise the servers and applications in the data center. Most enterprises will have hardened their perimeter, but may have little to no visibility of the threats that are inside of their perimeter defenses. This leaves the servers vulnerable to exploits such as virtual machine-based rootkits (VMBR). Successful VMBR exploits such as Blue Pill by Joanna Rutkowska, have been demonstrated way back in August of 2006 at Black Hat by researchers.
Essentially, the attacker goes back to the “Well of Malware” for additional capabilities as needed until they find success in attacking the data center. I define the “Well of Malware” essentially as an open community of cyber attackers sharing information and accelerating innovation in the development of malware. This collaborative model results in a plethora of capabilities where even the novice cyber attacker can become successful in a matter of hours. One proof point on how effective this innovation engine has become, we need to remember that one of the original authors of Blackshades was arrested in 2012 and yet Blackshades continues to be developed by the community.
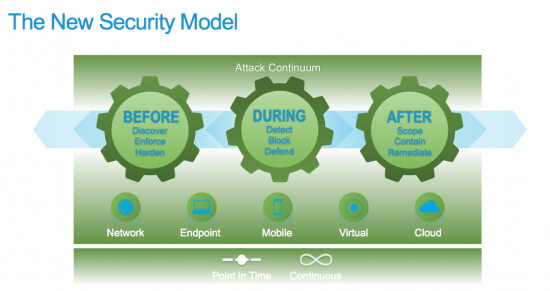
In order to begin to develop a serious response to these cyber attackers, we must look at new ways to give cyber defenders the capabilities to stop these attacks. Cisco Sourcefire has developed a new security model, called the Attack Continuum, which is a simplified way to view the cyber attack problem. By looking at the “Before, During, and After” phases of the cyber attack separately, we can begin to identify the required capabilities across the attack continuum for a successful response. The model also reminds us that our capabilities must address the needs of each attack vector while giving us both point-in-time and continuous capabilities throughout the continuum.
Although this new model may provide a fresh way to look at the problem, for some it may seem too theoretical to be useful to any organization trying to implement comprehensive security architecture. Our next Cisco Validated Design in the Secure Data Center for the Enterprise Solution Portfolio will be focused on showing how organizations can make this model a reality, secure their data centers, and as a result give their cyber defenders the capabilities they need to defend their organization against the highly capable cyber attackers.