At Cisco, our leadership made the decision over twenty four years ago that we would clearly publicly communicate security vulnerabilities or other issues that could potentially expose customers to risk. This is when the Cisco Product Security Incident Response Team (PSIRT) was born. Our team and the security vulnerability process has evolved to meet customer needs for over the last two decades.
The industry has also evolved and many other vendors have created PSIRTs to better protect their customers. However, some vendors are just getting started. This is why the Forum of Incident Response and Security Teams (FIRST) created the Product Security Incident Response Team (PSIRT) Framework. The main purpose of this framework is to help organizations create, maintain, and grow capabilities related to product security and security vulnerability disclosure. This is a collaborative effort that presents different capabilities, services and outcomes of a PSIRT.
The Framework identifies core responsibilities of PSIRT teams, providing guidance on how to build capabilities to investigate and disclose security vulnerabilities, along with remediations, to their customers in a transparent way.
Is This Why There Are So Many Vulnerability Reports Nowadays?
Technology is evolving at a very fast pace. The number of products, software packages, and connected devices will continue to rise. One reason for the increase in reported vulnerabilities is the fact that the industry is definitely getting better at finding vulnerabilities. For instance, the following figure, created by the National Vulnerability Database (NVD), illustrates the distribution of vulnerabilities disclosed in the industry by severity over time.
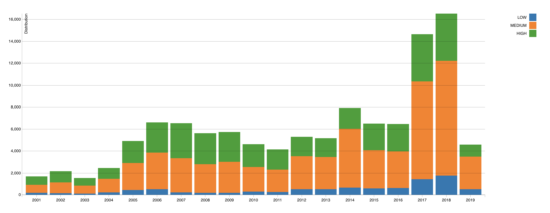
Because customers are demanding greater transparency, more vendors are creating PSIRTs and becoming more capable of disclosing security vulnerabilities to their customers.
Security vulnerability disclosure and remediation can be disruptive for technology operations, administrators, and end users. Our goal at Cisco is always try to reduce the number of vulnerabilities and continuously enhance our products. With that acknowledgement, it is vital to remember a few factors that drive the purpose behind our vulnerability disclosures. Most importantly, we have a high bar for transparency. At Cisco, we disclose vulnerabilities regardless of how the vulnerability was found or who found it. In fact, the majority of our disclosures are vulnerabilities that we find internally. We disclose these vulnerabilities with a goal of helping customers understand and manage their risk.
We also assign Common Weakness Enumeration (CWE) identifiers to all vulnerabilities disclosed. CWE helps us spot trends across our broad portfolio of hundreds of product lines. Cisco performs root cause analysis to enhance our Cisco Secure Development Lifecycle.
Cisco will continue to provide these resources enable customers protect against cyber threat actors. Our customers can count on our commitment to be transparent, so they can manage their risks.
PSIRTs Working Together
PSIRTs must work together to protect the ecosystem! As stated in the PSIRT Services Framework: “Nurturing relationships between peer PSIRTs can help in information-sharing and potential mutual assistance and/or coordination for incidents. Working with these peer organizations can help fill in vital data to remediate vulnerabilities and exposes the organization to the peer’s expertise as the two groups consult on issues. The PSIRT should establish communication channels (both normal and secured) with key peer PSIRTs. Establishing and nurturing relationships with industry peers is critical for information sharing and coordinating on issues that affect both organizations.”
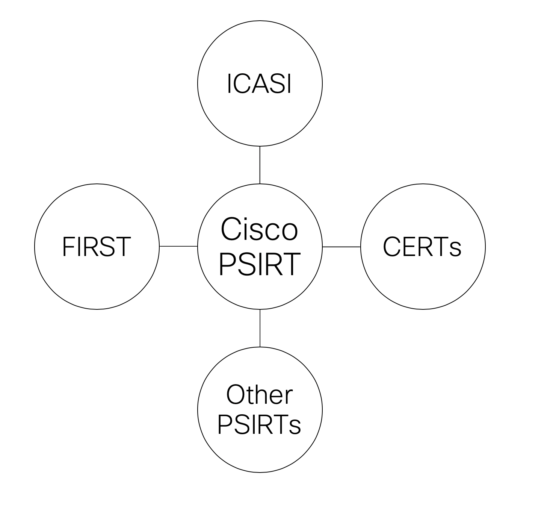
At Cisco, we work with numerous PSIRTs and other security teams. We also co-founders and active members of the Industry Consortium for Advancement of Security on the Internet (ICASI). Through the Unified Security Incident Response Plan (USIRP) process, ICASI enables PSIRTs from member companies as well as select, invited outside organizations to collaborate quickly and effectively to resolve complex, multi-stakeholder Internet security issues.
Cisco PSIRT works closely with many other PSIRTs, ICASI, several CERTs and coordination agencies, and FIRST on an ongoing basis.
PSIRTs Working With Security Researchers
Security researchers and security research are vital to the ecosystem! PSIRT teams should always positively engage with security researchers while investigating and disclosing security vulnerabilities. The Framework provides guidance to new PSIRTs on how to collaborate and engage with security researchers in the industry.
At Cisco, we work very closely with numerous security researchers in the industry and we even have our own industry-leading security research organization called Talos. Talos works very closely with Cisco PSIRT and with many other PSIRTs in the industry. Properly engaging with security researchers can speed communications and efforts around vulnerability reporting and remediation.
Setting A Higher Standard
As my colleague Anthony Grieco stated in a recent post, “there should be no such thing as implicit trust in today’s world. In fact, we believe the standards should be set higher, not only for Cisco but for all technology providers around the globe, to shift the role from a vendor to a trusted partner.”
If you are a technology provider, I invite you to become familiar with FIRST’s Product Security Incident Response Team (PSIRT) Framework. If you are a customer, ask your technology vendor about their policy on vulnerability disclosure and become familiar with their PSIRT.