Container orchestration and automation is taking the DevOps world by storm. Docker is the de-facto standard in the realm of containers. When a parallel for container orchestration is drawn, Kubernetes is the go-to orchestration solution for automating and scaling a container deployment, be it on-premise or in the public cloud.
Kubernetes is a highly scalable, open-source container orchestration framework. It draws its roots from the Google Borg and Omega internal cluster orchestration architectures used by Google for Gmail and Search capabilities.
Cisco Stealthwatch Cloud can easily integrate into an on-premise, private cloud or public cloud Kubernetes deployment. Public cloud capabilities include full visibility into AWS, Azure and GCP Kubernetes frameworks.
Our Kubernetes visibility provides insight and analytics into network traffic within containers, pods and nodes that organizations have not had east-west visibility into before. It’s an unprecedented level of access into inter-pod and intra-pod communications with your distributed containerized applications.
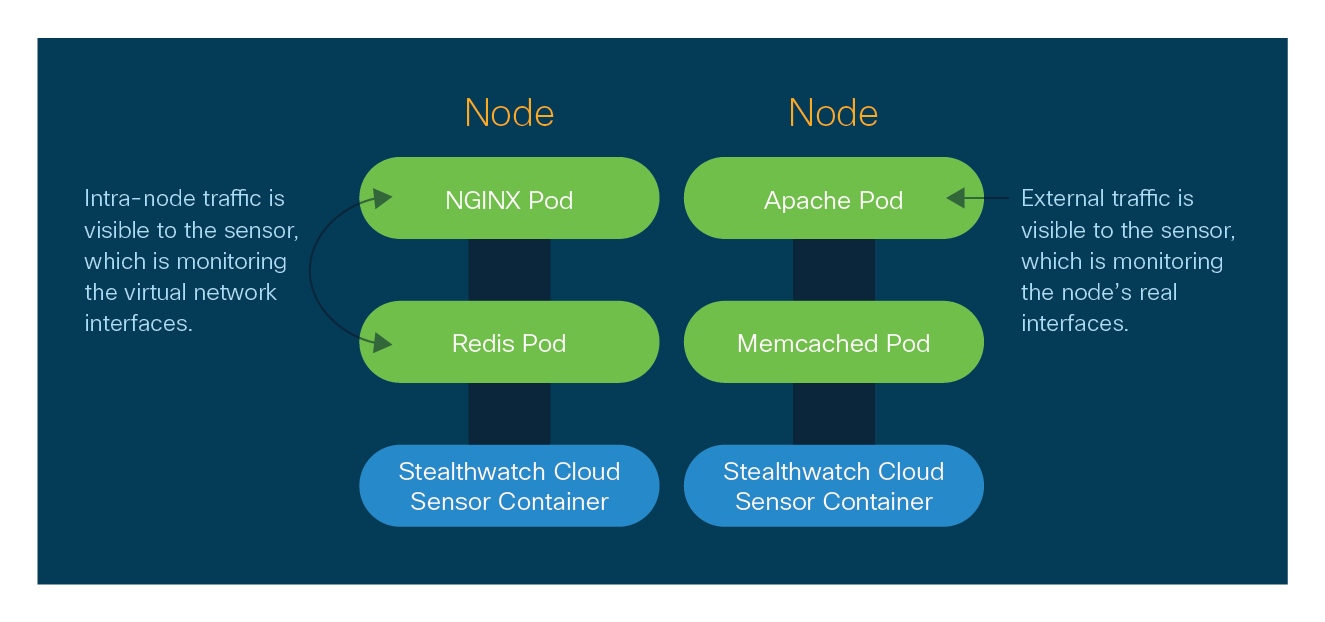
Stealthwatch Cloud deploys a lightweight sensor onto each Kubernetes Node, including the Master Node. This allows Stealthwatch Cloud the unique capability to monitor, baseline and detect security anomalies deep into the cluster including container to container traffic, pod to pod and node to node traffic. The sensor monitors all traffic within the Kubernetes abstraction layer and illuminates all east-west traffic, leaving no dark spots or blind areas of exposure.
Visibility and anomaly detection deep into the Kubernetes container network traffic domain allow Stealthwatch Cloud to quickly alert on zero day threats, application exploits and breach indicators of compromise within a matter of minutes, instead of weeks or months like traditional security tools.
Stealthwatch Cloud is able to deploy a daemonset configuration onto your Kubernetes cluster so that when a node deploys…a SWC sensor deploys. This also applies to contraction. As your cluster expands and contracts, SWC sensors will also expand and contract on every node to ensure that you will automatically have full visibility into all network traffic on what is by default, a highly scalable and dynamic container management system.
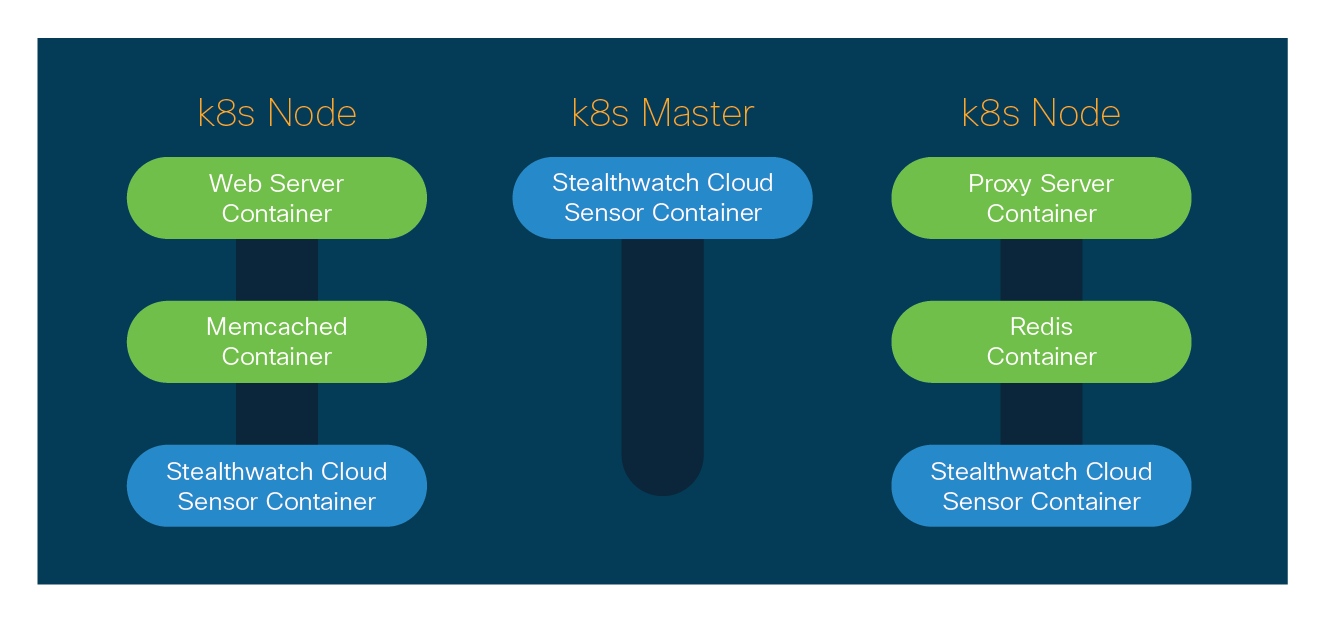
The end result is total end-to-end visibility into all traffic within and in/out of your Kubernetes environment. Combine this with on-premises and public cloud visibility into a single pane of glass and you’ll find that Stealthwatch Cloud provides an unparalleled capability for traffic visibility, policy verification, and breach detection for all of your network assets.
To learn more about Cisco Stealthwatch Cloud, visit https://cisco.com/go/stealthwatch-cloud






An easy to monitor and detect breaches!
Great overview. Really good solution