It wasn’t until late 2017 that threat researchers discovered spam campaigns delivering crypto payloads using email attachments. In some cases, a Word document downloads the crypto payload via a malicious macro. Attackers also continue hiding malware in email attachments. It’s safe to assume that the trend of using attachments in attacks isn’t going away. In fact, our 2018 Annual Cybersecurity Report (ACR) shows that attackers are getting even better at hiding malware in attachments to evade detection by sophisticated sandboxing technologies. Once these email attachments make it through, it’s easy to get users to trigger the event that downloads malware.
Two new ways attackers are hiding threats in files to evade sandboxing technologies
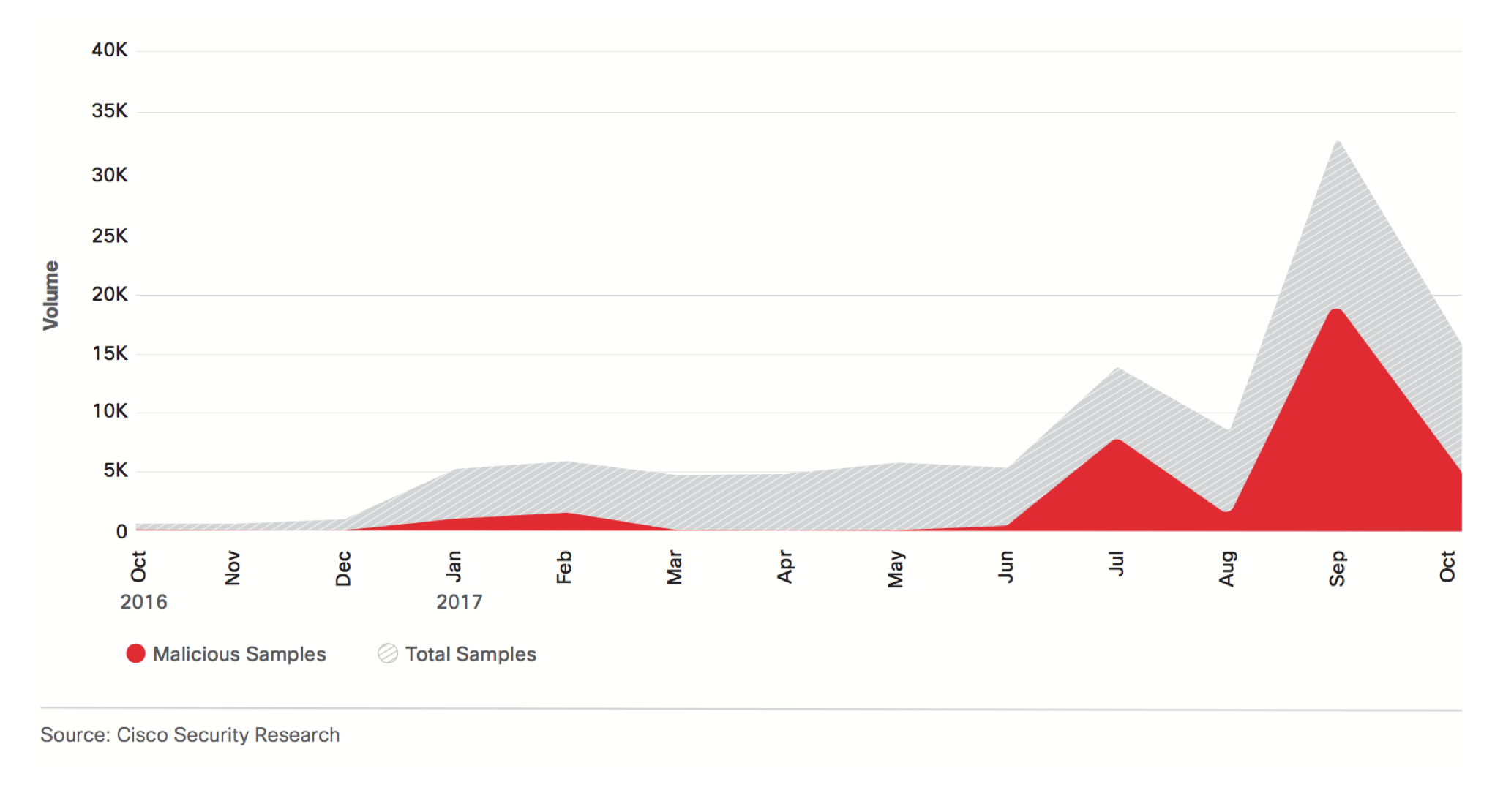
How does this happen? There are two new ways. The first isn’t when users open the malicious attachment, but when they close it. This works because the sandbox doesn’t usually close the attachment during the analysis and so the file is deemed safe because the event is not triggered and the sandbox lets it through. Now the user is free to open it and eventually close it. When closed, the attack method uses the “document_close” event to deliver the malicious payload. The chart below shows there was a spike in this type of attack in September 2017.
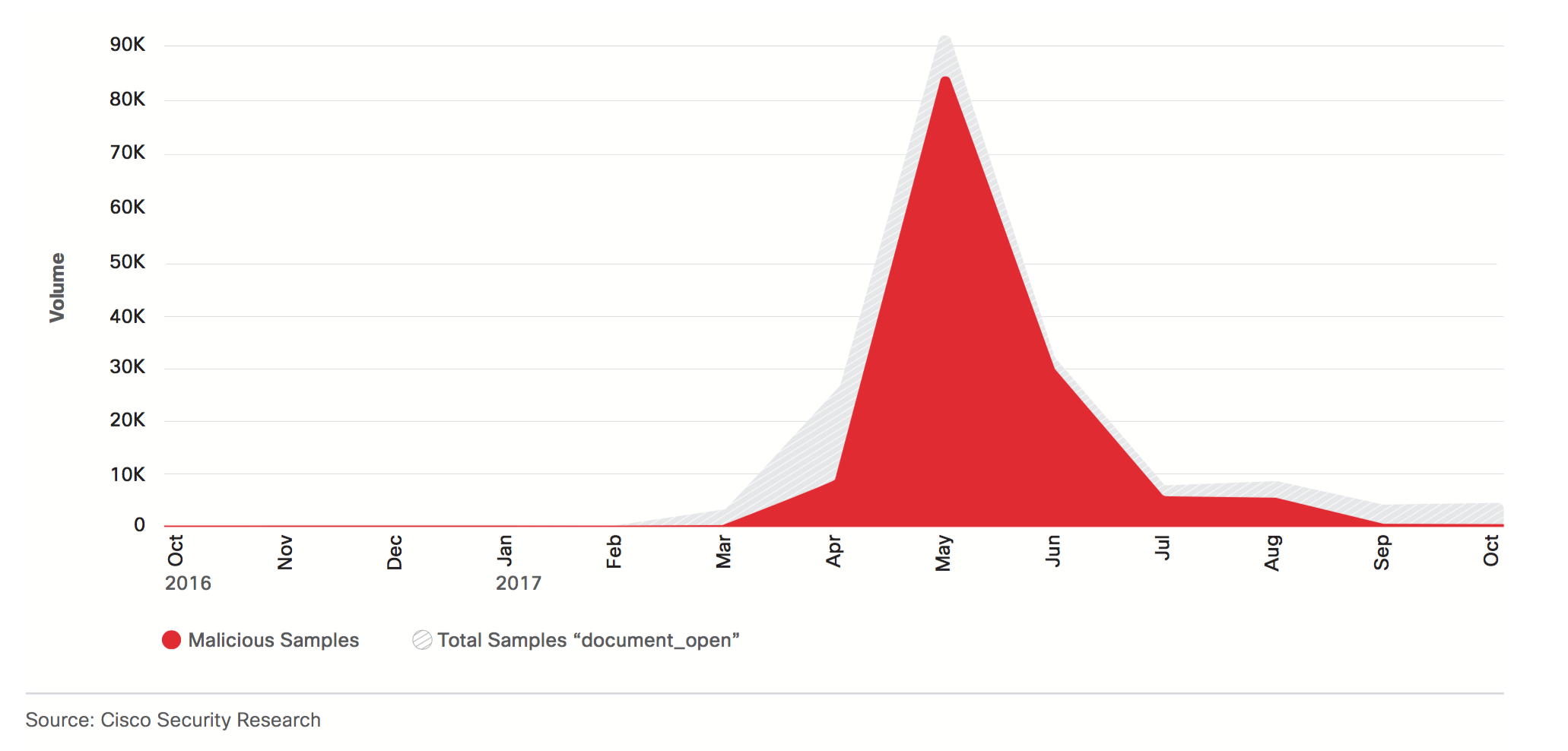
In the second method, attackers embed malicious documents within PDF files. Today’s sandboxes often fail to check files that are embedded within files. The PDF itself isn’t malicious (the threat is in the embedded file), so the sandbox lets the file through. Once it reaches a user’s inbox, he is likely to click on the embedded file – which triggers the malware download. This type of attack was particularly prevalent in May 2017 – Word documents were embedded within PDFs (see chart below).
How Cisco Email Security and Threat Grid keep you ahead of cryptomining or malware attacks
Now on to the most important topic – how to protect against email attachments being used in cryptomining or malware programmed to evade detection. You can with Cisco Email Security, which includes Advanced Malware Protection (AMP) and Threat Grid. When an email with an attachment comes in, AMP analyzes the file’s reputation and determines its disposition – clean, malicious or unknown. Malicious and clean files do not require additional investigation; however, unknown files are uploaded to the file analysis service – Threat Grid. Threat Grid is a powerful technology that applies both static and dynamic analysis techniques. It helps analyze, detect and understand if mining activity or malware is present, what it is doing, how large of a threat it poses and how best to defend against it. The analysis takes 7 to 15 minutes. Once completed, Threat Grid provides an analysis report along with a threat score that Advanced Malware Protection (AMP) utilizes when convicting the file. Once a file is convicted, it is blocked and the email with the attachment is not delivered to the user. This cloud-based analysis and threat intelligence system identifies the type of behavior mentioned in the two new techniques attackers are using to evade sandbox detection. Using “content-aware” features, Threat Grid ensures these types of attacks do not evade sandbox analysis to stop malicious files from landing in users’ inboxes. Threat Grid also has indicators to detect if mining activity is present. For a deeper understanding of how AMP and Threat Grid work on Cisco Email Security, read the detailed blog on this topic. You can also read the blog about the new Threat Grid UI to learn how all the valuable UI changes help you get to the relevant information faster.
A powerful email security solution is a critical part of your security strategy because most breaches start with email. Cisco Email Security leverages the power of Cisco Talos, one of the largest threat research teams in the world, in addition to Threat Grid. With such robust threat intelligence, Cisco Email Security customers block more threats. And AMP on Cisco Email Security helps customers see more threats in more places via the AMP everywhere architecture. It shares its analysis and verdicts globally for improved threat efficacy for all AMP customers. With the help of this powerful trio – Talos, AMP and Threat Grid – Cisco Email Security has been protecting thousands of organizations globally against old and new threats alike for over a decade.
Here’s what customers had to share about how Cisco Email Security impacts their organizations:
- “Cisco Email Security puts me in the driver’s seat and not on the defensive side. It is a welcoming conversation when I discuss cybersecurity with my president and with the other vice presidents.” – Evan Kobolakis, VP of ITS & Chief Information Officer, State University of New York at Old Westbury
- “Cisco Email Security has literally taken email security off our management plate and allowed us to focus on other areas. It catches everything! It’s peace of mind knowing that we made the perfect decision for email security!” – Steven Wujek, Senior IT Architect, Technology Concepts & Design
- “We started with Microsoft’s Office 365 built-in tools, but they do not do a good enough job. Cisco Email Security is much better.” – Security Manager, Large Enterprise Health Care Company
Learn about what else customers have to say about Cisco Email Security from feedback gathered in February 2018.
Email remains a vital distribution channel for malware according to the 2018 Cisco Annual Cybersecurity report. The great news is Cisco detects threats in hours not weeks. The Cisco median time to detection is only 4.6 hours, a 204% decrease from the 14-hour median reported the year prior. With advanced threat defense from Cisco Email Security you will stay ahead of attackers’ latest tactics whether they involve malware or miner payloads and no matter what new techniques they employ to breach your organization.
Get more information about Cisco Email Security.





