With over 8 billion “things” being connected today, IoT security has undoubtedly evolved from a mysterious buzzword to one of the biggest real threats to our network today. According to Gartner, over 51% of survey respondents believe that cybersecurity is the number one technology-related challenge for IoT deployment.
Overwhelmed by the countless number of IoT security comments and stories, let’s try to demystify this seemingly complex concept. To begin, let me ask you three simple questions: What types of IoT devices are connected to your network? What behaviors are appropriate for these IoT devices? Is there an industry standard to follow while connecting these IoT devices? If you don’t know the answers to these questions yet, that’s when we say the IoT security risks are probably right around the corner staring at you.
What is MUD?
To answer the above three questions, Cisco has been working on a solution known as Manufacturer Usage Description (MUD) to arm IoT security with you.
The key idea of MUD is to facilitate device visibility and segmentation by allowing your network administrators to effortlessly identify the type of IoT device and define the corresponding appropriate behaviors for that device. To do this accurately, we are introducing a participant to the conversation: the manufacturer. IoT manufacturers are able to disclose to us what their devices are, and what network policies they need for the devices to correctly function. This whitelist statement is something that customers can use to deploy access policies in their own networks without any guesswork.
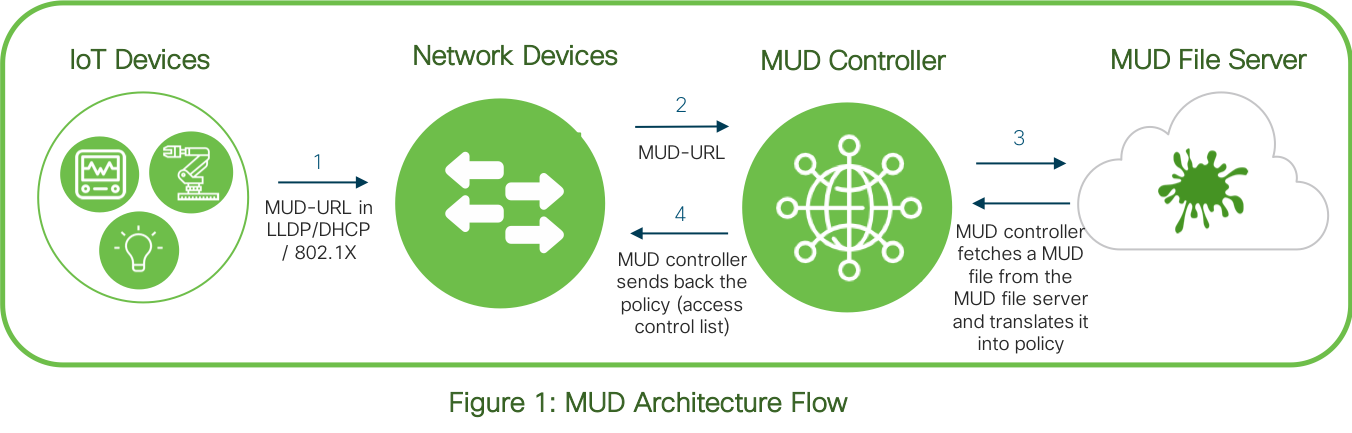
As shown in Figure 1, an IoT device first sends out a pre-embedded MUD-URL to the network devices (e.g. switch & AAA server), through which the MUD-URL will be received by the MUD controller (software). According to the specific MUD-URL, a matching MUD file will be provided from the MUD file server and translated into policy format through the MUD controller, to then enforce the access control list to the device.
Clear benefits to both customers and device manufacturers brought by MUD
If you get the overall idea of MUD so far, you may see that IoT device manufacturers and customers are two key stakeholders in the MUD ecosystem. MUD offers distinct benefits for customers and manufactures:
Benefits to customers:
- Automate IoT device type identification thus reducing operational costs
- Simplify and scale IoT device access management by automating policy enforcement process
- Reduce threat surface of exploding number of IoT devices by regulating traffic and thus avoiding lateral infections
- Secure enterprise network through standard-based approach
Benefits to manufacturers:
- Improve customer satisfaction and adoption due to reduced operational costs and security risks
- Enhance device security through standard-based onboarding procedure
- Differentiate device offerings with embedded network-based device security feature
- Reduce product support costs to customers by following an easy-to-implement process
In addition to these benefits, we’ve received positive feedback from our partners:
“MUD technology is valuable for Innovative Lighting. MUD technology will enhance our commissioning process by identifying our devices on the network. Furthermore, MUD technology will provide the appropriate access control policy promoting a more secure system. We look forward to working more with Cisco and the MUD technology.”
-Harry Aller, CTO at Innovative Lighting
“MUD was selected to protect Molex IoT solution against malicious parties. MUD is a relatively simple solution to implement at the device level, light on constrained IoT devices but takes advantage of strong network infrastructure including network switches and authorization server. Our goal to reduce exposure footprint and the overall solution allows us to provide a level of security to our customers that is scalable and flexible at the same time. The ability to whitelist specific devices in the field allows us to lock down the network but also to respond quickly to events that may take place post deployment.”
-Mo Alhroub, Manager of Software Engineering at Molex
MUD is approved as an Internet Standard and released as RFC8520 by IETF
I am delighted to announce that MUD has been officially approved as an Internet Standard by the Internet Engineering Task Force (IETF) and is now released as RFC 8520. You can find all of the details here: https://datatracker.ietf.org/doc/rfc8520/. Meanwhile, MUD is also part of the NIST Mitigating IoT-Based DDoS project, and an optional component of the Open Connectivity Foundation’s framework now.
MUD 1.0 is ready
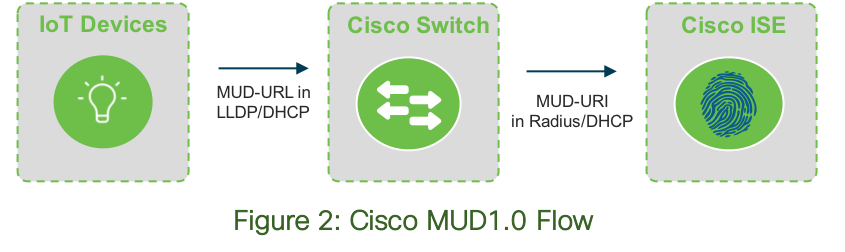
Besides the IETF approval, I am also thrilled to announce that we are launching MUD1.0, the first phase of the entire MUD solution. While MUD itself is an open standard, Cisco is pioneering our unique version by leveraging Cisco switch and ISE (Identity Service Engine, a AAA server) as the network devices shown in Figure 1.
In this Cisco MUD1.0 release, we focus on providing device visibility by enabling the IoT device identification inside the enterprise network. As shown in Figure 2, the IoT device sends out the MUD-URL to the switch and then passes it to ISE. The administrators will see the device specific information on ISE UI including the device model, manufacturer, etc. Specifically, MUD1.0 supports profiling IoT devices, creating profiling policies dynamically, and automating the entire process of creating policies and Endpoint Identity Groups. Furthermore, administrators can leverage these profiling policies to create Authorization Policies and Profiles manually for securely on-boarding IoT devices.
To make the sophisticated story simple, through MUD1.0, you would know exactly what devices are coming to your network the minute they are connected. Even more, you can define policies for these IoT devices. Isn’t that amazing?!
With MUD1.0 released, future releases will more fully automate the policy control part. On top of MUD1.0 when ISE receives the MUD-URL to extract the visibility information, the MUD-URL will be passed to the MUD controller (software) which will then go out to the MUD server to get the MUD file and translate the content into policy (as shown in Figure 1). The network devices will then enforce the appropriate policy onto the devices. The whole process will be fully automated. Want more flexibility as well? No worries, we’ve got you covered! Before the automation process, you get the choice to edit the recommended policy as needed.
Next steps
Join us at Cisco Live San Diego US 2019, to check out the MUD capabilities in person! We will have a demo partnering with Molex (Networking + Security Innovation Forum, demo pod #8, 6/10/2019-6/13/2019), and a Technical Breakout session (on 6/12/2019 at 4PM) at San Diego Convention Center.
Moving forward, we are upgrading and further building a MUD Devnet website. There will be clear step-by-step guidance for both end customers and device manufactures to help you understand how the solution works and get the support needed. Stay tuned!
Reach out to Cisco sales representatives if you are interested in deploying MUD1.0 on your network. Or shoot an email to mud@cisco.com, if you have any other questions or are interested in being our partners. We have all of the experts here to support you!





