On Tuesday May 28, 2013 at 17:30 UTC a massive pharmaceutical-based spam campaign began, using the Subject: header “Only 24 Hours Left to Shop!”. Cisco witnessed volume rates peaking as high as 8 out of every 10 spam messages being sent. The indiscriminate nature of the attack’s recipients suggests that most anti-spam vendors, including Cisco, will have blocked this attack very quickly.

This is an “old school” technique which has fallen out of favor with spam operations in recent years. Global spam volumes have been trending down over the past few years, with some notable spikes here and there. The flavor of this attack is reminiscent of the shotgun-style blast-everything-and-everyone spam attacks of yore. The idea here is not necessarily to evade the spam filters but rather to maximize the mail that does make it past the filters. If we suppose an anti-spam vendor catches this attack and blocks 99.99% of it, the remaining 0.01% that made it through, given the amount of volume that was sent in such a short time, still adds up to significant revenue for the spammer.
Below is a screen capture of the Canadian Pharmacy website served by the domain doctormace.ru.

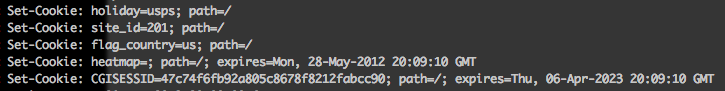
An interesting aspect of the Canadian Pharmacy fulfillment web site is the cookies they set for their web visitors. Notice that they are tracking not only the country where the visitor is from, but there is a site identification number, a “heatmap” cookie, a session identifier which lasts far into the future, and a “holiday” cookie set to the value of “usps”. In any case, this pharma gang is definitely intent on tracking their loyal customers and other visitors.
Checking some of the IP addresses that have been witnessed carrying out the sending, leads Cisco to believe that the botnet in this case is Kelihos:


Because this message had such high volume and was directed at a very poorly compiled list of recipients which included spam traps, Cisco caught this attack in its infancy. As with most spam campaigns of this type we expect the content of the spam, including the sending IPs, and domain in the URLs, to change with some frequency.
* Special thanks to Craig Williams for his help putting together this blog post.


CONNECT WITH US