Indicators of Compromise (“IOC”) are used to suggest a system has been affected by some form of malware. An Indicator of Compromise can be anything from a file name to the behavior observed while malware is actively running on an infected system.
Where do they look? Social media, new feeds, industry reports, Threat Grid sample analysis reports — all of these are excellent sources for Indicators of Compromise. Artifacts that are left over after the malware has executed are potential IOCs. Even the lack of artifacts can indicate there may be a problem.
Why is this important? Because understanding what IOCs are being observed can help us to protect our systems and our users in several ways:
- Proactively
- Retrospectively
- Incident Response
Proactively: Having the knowledge of what IOCs are out there can help us develop defense methodologies to prevent new malware infections. These can be used to develop signatures (including YARA, open IOC, AV signatures, and even Behavioral Indicators, which are a type of signature-based detection), set firewall rules, and improve defensive mechanisms, in order to prevent malware attacks. By proactively blocking network locations, for example, we are able to both protect ourselves from malicious locations and prevent malware communications with command and control.
Retrospectively: We can use knowledge of IOCs to deny potential threats the ability to gather any information during the reconnaissance phase of the planned attack. This knowledge also helps us to identify threats during the malware delivery, exploitation, and installation phases, and provides important opportunities to deny attackers the ongoing access they desire.
Incident Response: Incident responders can use IOC information to aid in threat triage and remediation. IOCs help to identify specific strains of malware, and provide invaluable information for responders. This information enables responders to better understand how threats were able to infiltrate their systems. By knowing what IOCs to look for, we can quickly and efficiently locate and resolve any damage the threat may have caused to our system and our users.
There are many different defense strategies that can be implemented to protect an organization. In our experience, each organization is like a unique snowflake; no two are alike. Each one requires extensive, detailed knowledge of the infrastructure in question to be able to utilize all the information available. There are many different IOCs. Knowing which ones will be useful, which ones you can consume, and which ones are not useful, is a combination of experience and knowledge of the tools in place that you can leverage to protect your organization.
AMP Threat Grid provides an extensive selection of IOCs that can be leveraged to protect your organization, and only limited by your ability to consume them. Often the simplest IOCs come in the form of malware information feeds.
AMP Threat Grid provides the following feeds to our customers:
| Feed | Description |
| autorun-registry | Contains registry entry data derived from querying registry changes known for persistence |
| banking-dns | Banking Trojan Network Communications |
| dll-hijacking-dns | Contains domains communicated to by samples leveraging DLL Sideloading and/or hijacking techniques |
| doc-net-com-dns | Document (PDF, Office) Network Communications |
| downloaded-pe-dns | Samples Downloading Executables Network Communications |
| dynamic-dns | Samples Leveraging Dynamic DNS Providers |
| irc-dns | Internet Relay Chat (IRC) Network Communications |
| modified-hosts-dns | Modified Windows Hosts File Network Communications |
| parked-dns | Parked Domains resolving to RFC1918, Localhost and Broadcast Addresses |
| public-ip-check-dns | Check For Public IP Address Network Communications |
| ransomware-dns | Samples Communicating with Ransomware Servers |
| rat-dns | Remote Access Trojan (RAT) Network Communications |
| scheduled-tasks | Feed containing scheduled task data observed during sample execution |
| sinkholed-ip-dns | DNS entries for samples communicating with a known DNS sinkhole |
| stolen-cert-dns | DNS Entries observed from samples signed with a stolen certificate |
For more detailed information on specific threats, we provide users with access to our analysis reports. These reports provide highly detailed information that can be used in each of the three aspects we discussed above. The reports are curated subsets of the complete analysis document. The sample metadata is included in the feeds:
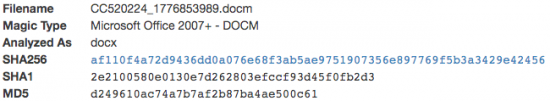
Figure 1: Metadata in each sample
We call out specific behaviors based on their severity and confidence. These behaviors are categorized as malicious, suspicious, and informational. Malicious behaviors are indicated in red
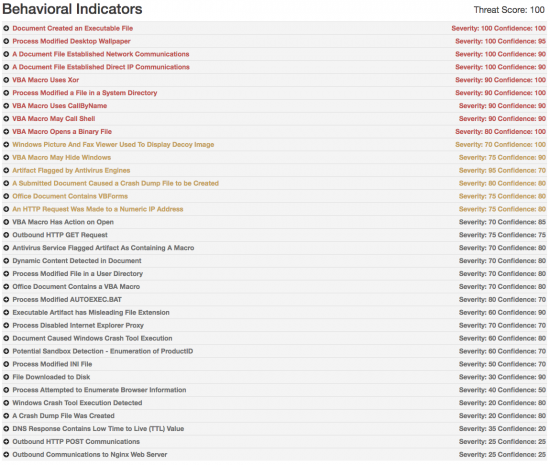
Figure 2: Behavioral Indicators
In addition, we provide detailed descriptions and artifact information associated with the behaviors to aid analysts and responders. Clicking on the “+” sign will open an explanation and detailed view of each behavioral Indicator:
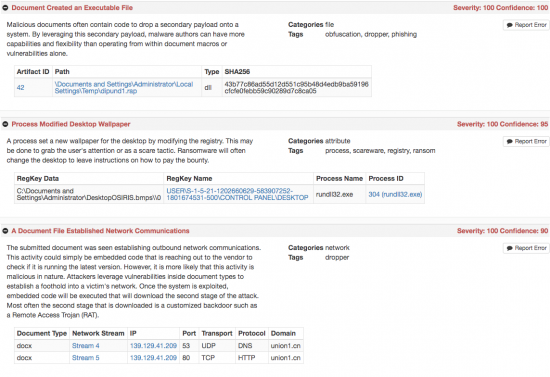
Figure 3: Explanation of the behavioral indicators
We can use these specific behaviors to aid in the discovery of infected systems. We provide detailed network information as well as the complete PCAPs that may be downloaded by the user if further analysis is desired.
This is the network overview:
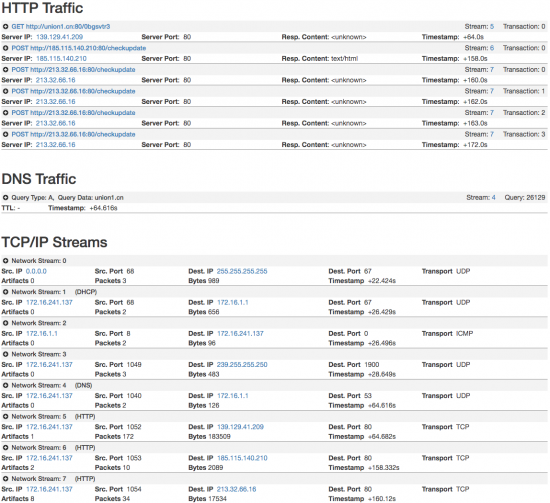
Figure 4: Network traffic generated by analyzed sample
Again, each of these items can be expanded to gain new insights on the network. This level of detail can provide invaluable knowledge about what the malware is attempting to do.
- TCP streams trying to call out – pivot off these to find out if they are malicious (good plug for Chrome extension)
- If IP are still connecting to ransomware CNC, can block connection up front
- Or if buried in Word Macro, block file hash in A4E

Figure 5: Word document is requesting information
The report shows all the processes that are launched when the sample is executed, and how the malware is being installed and run on the system. This allows responders to see precisely what a particular malware sample is doing on a system. This knowledge aids in speeding remediation, and allows defenders to modify and architect defenses to allow rapid detection and containment of the malware.
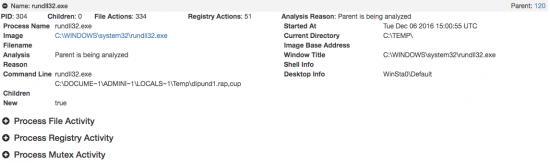
Figure 6 Word is executing a DLL
In addition to the process information, we also extract the commands being used to launch the malware. We notice from the behavioral indicators (Figure 1 & 2) that the document in our example appears to be malicious. We can see from the command and the disk artifacts that this is the analysis report for the most recent iteration of the Locky ransomware. Here is a short video showing all all this in action:
You can see from just these few examples where we can find IOCs and what we can do with them once we find them. From signatures for IDS/IPS and WAF, to YARA signatures, firewall rules, AV signatures, or strings to search through logs, the possibilities for finding useful Indicators of Compromise are limited only by one’s ability to creatively use the information to which we have access.
Happy hunting!





