This blog was co-authored by Kevin Brooks, Alex Chiu, Joel Esler, Martin Lee, Emmanuel Tacheau, Andrew Tsonchev, and Craig Williams.
On the 21st of July, 2014, Cisco TRAC became aware that the website dwnews.com was serving malicious Adobe Flash content. This site is a Chinese language news website covering events in East Asia from a US base. The site is extremely popular, rated by Alexa’s global traffic ranking as the 1759th most visited website worldwide, and the 28th most visited in South Korea. In addition the news site also receives a substantial number of visitors from Japan, the United States and China.
This malware campaign does not appear to be tightly targeted. Twenty-seven companies across eight verticals have been affected:
Banking & Finance
Energy, Oil, and Gas
Engineering & Construction
Insurance
Legal
Manufacturing
Pharmaceutical & Chemical
Retail & Wholesale
This is indicative of the campaign acting as a drive-by attack targeting anyone attempting to view one of the affected sites.
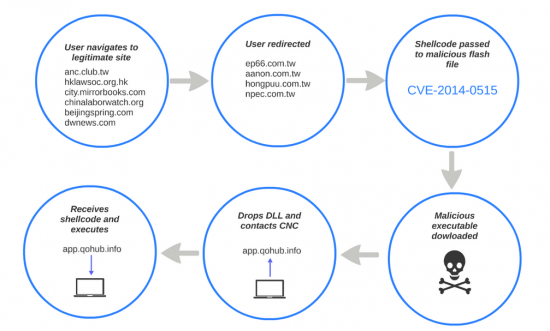
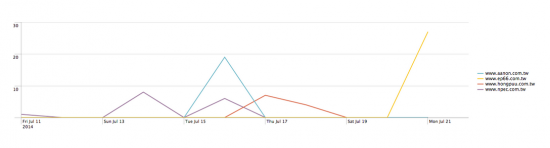
This particular attack has been ongoing since at least July 11th, 2014, and has affected a series of sites including:
anc.club.tw
hklawsoc.org.hk
city.mirrorbooks.com
chinalaborwatch.org
beijingspring.com
dwnews.com
Associated malicious files have been observed being served from:
ep66.com.tw
aanon.com.tw
hongpuu.com.tw
npec.com.tw
For example, on July 21st visitors to dwnews.com received content from “http://www.ep66.com.tw/f.html” which in turn loaded a malicious Flash file “http://www.ep66.com.tw/flash.swf”. This file, with the SHA256 of 301657a0ad4eb91fd95f2be0a789a16a637c2e2caa5fa019040021f376a852cc, exploits CVE-2014-0515 — a buffer overflow vulnerability in Adobe Flash which allows for execution of arbitrary code.
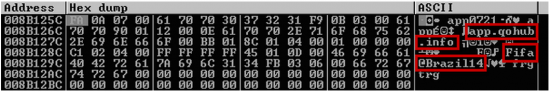
The source of f.html shows that the purpose of this html file is to load the malicious “Flash.swf” which contains the exploit used in the attack. However, the shellcode to be executed during the attack is passed to the Flash file through the FlashVars parameter which contains a large amount of hex data. Within this data is an obfuscated URL.
![]()
The obfuscation may exist in order to hide the presence of a URL in transferred data from simplistic detection strategies. The actual URL is disguised by a simple rearrangement cipher.

Making a request for “http://www.ep66.com.tw/setup.exe” returns an executable file with SHA256 sum 7f39e5b9d46386dd8142ef40ae526343274bdd5f27e38c07b457d290a277e807.
Taking a Closer Look
A quick look at the malware’s activity reveals some fairly interesting behavior. In particular, the malware appears to drop a DLL file and call out to a server. Opening the DLL in a disassembler shows a long list of shellcode MOV instructions. However, additional shellcode is obfuscated, requiring the correct XOR key before execution can take place. The shellcode proceeds to build a large random block of 256 bytes using the time stamp counter (instruction RDTSC).
Once the shellcode finishes executing and loading all of its libraries, strings are retrieved from the bottom of its data and moved into memory for use. These strings contain what appears to be a hostname, app.qohub.info, communication port number along with a unique string, “Fifa@Brazil14” which is subsequently used in encrypting communication with the command and control server. The domain name qohub.info is common between several variants of the this malware, although the subdomain name may vary.
Next, the shellcode prepares the request with the random 256 bytes created using the timestamp counter earlier. It sends this set of data as the body of a message and waits for a response from the server. The port used by the malware to communicate with the Command and Control (C&C) server is static at 443, but the communication protocol is definitely not SSL/TLS. The client receives the response message from the C&C, which it decodes with the “Fifa@Brazil14” key.
Finally, the shellcode expects to receive two more chunks of data: a 4-byte size of N and N-bytes of data. The shellcode grabs the 4 bytes and uses that value in VirtualAlloc as the memory size to allocate. This 4 byte value must match the size of the “data” portion in the response because this is shellcode sent from the server and directly executed. The N-bytes of data are decrypted with the same key, “Fifa@Brazil14”, and are promptly called for execution.
Conclusion
This malware campaign serves as another reminder of the importance of keeping your system software up-to-date. Attackers were able to compromise legitimate sites, including the high traffic news website dwnews.com, to covertly redirect users to the exploit landing page. The exploit utilized the previously disclosed Adobe Flash vulnerability, CVE-2014-0515, to compromise users and force the download of the actual malicious payload.
The payload contains an embedded and disguised DLL. When run, the DLL accepts coded instructions from a remote server that are decoded and executed on the infected machine. This allows attackers to remotely control infected machines and issue whatever instructions they may wish to give.
Compromised websites serving this kind of malware are not obvious to users. Malware can be silently installed on users’ machines without any user interaction other than visiting a website and without any indication that anything out of the ordinary occurred. Maintaining fully patched systems limits the effectiveness of attacks. However, for organizations to fully protect themselves, they will need to deploy multiple layers of protection and to remain vigilant for further similar attacks.
Protecting Users Against These Threats
 |
CWS or WSA web scanning will prevent the download of such threats. The Network Security protection of IPS and NGFW is ideal to detect and block attempts of malware to communicate with the command and control server. Advanced malware protection (AMP) is best suited to detect and block this type of complex threat. This particular threat is not spread by email, so ESA is not applicable in this case. |




The malware you’re describing is Poison Ivy.
Poison Ivy is the overall attack kit. This particular threat actor uses the Fifa@brazil2014 admin key. Poison Ivy’s anonymity and feature set make it a prime tool for attackers.