Why is platform-based a key imperative for next-generation firewalls (NGFWs)? In our previous blog posts, we outlined what it means to be threat-centric, integrating best-in-class security layers with shared intelligence across all layers to combat advanced multi-vector threats.
Multiple point products create considerable management complexity and cost for IT staff who are under tremendous pressure to efficiently manage IT environments, keep operational costs low, and maintain the best defenses to keep pace with the dynamic threat landscape.
To protect extended networks, the idea of being platform-based entails delivering a more effective yet simplified architecture with fewer security devices to manage and deploy. Unifying security layers in a single device not only closes gaps that attackers exploit but this architecture also reduces cost and complexity in a number of ways.
Many traditional NGFWs are poorly integrated and cannot share intelligence between security layers, which leads to lower threat effectiveness and inability to address advanced attacks. Further, integration into customer work streams is cumbersome because there is no central point of intelligence correlation—this increases time and resource required to address security issues on the network. Additionally, enterprises often hire additional staff to install and manage these disparate security solutions—and employ manual operational processes that are inefficient, costly, and slow to respond to threats.
Cisco ASA with FirePOWER Services Streamlines Operations
Cisco ASA with FirePOWER Services unifies security across the all defense layers and leverages shared visibility to more effectively protect against threats through an integrated threat defense platform. This multi-layered approach delivers superior threat protection and scalable security to branch offices, Internet edge sites, and even large data centers.
Cisco ASA is centrally managed by the Cisco FireSIGHT Management Center, which provides security teams with comprehensive visibility into and control over activity within the network. It simplifies operations by automating key security tasks including event impact assessment, policy tuning, and user identification.
Impact Assessment
Cisco FireSIGHT’s comprehensive impact assessment relies on information from passive discovery, including operating systems, client-side applications and hosts. It allows IT staff to focus on the smaller subset of events they are vulnerable to and prioritizes threats targeting those vulnerabilities. For instance, an event can be flagged for immediate action if the collective intelligence gathered indicates that an immediate response is required. This helps to focus staff’s attention, and can eliminate up to 99 percent of the “noise” associated with security monitoring and response. Assessing the impact of detected events is crucial to security productivity. False positives—or alerts that are actually non-events, consume huge amounts of resources.
Policy Tuning
FireSIGHT’s contextual awareness of an organization’s unique environment, as well as the threats that impact it, allow it to automatically recommend new security policy rules to deploy to harden defenses as the IT environment and threat landscape evolves. Automated tuning reduces total costs of ownership compared to completing such tasks manually and maximizes security effectiveness.
User Identification
When adverse events occur, linking individual users to the event must occur quickly. Cisco FireSIGHT compiles and determines user identities, making it easy to identify the affected person and quickly quarantine the infection. Sharing the source of infection across other security layers helps stop its spread and speeds remediation.
Security Task Automation Delivers Operational Cost Savings
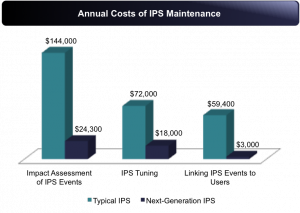
The SANS Institute conducted a study to show the value of security task automation to a typical 7,000 employee company, including impact assessment, policy tuning, user identification, and more. As the diagram below demonstrates, the savings are considerable. Larger organizations will benefit even more.
Source: SANS Institute, “Calculating Total Cost of Ownership on Intrusion Prevention Technology” White Paper, 2/2014.
Finally, simplified integration via open APIs is crucial to ensure NGFWs fit seamlessly within existing customer work streams and can leverage a robust, third-party technology partner ecosystem. The eStreamer API allows organizations to interface with the rich ecosystem of third-party solutions, including vulnerability management scanners, SIEMs, software management trouble ticketing systems, and more, to improve total cost of ownership.
Cisco ASA with FirePOWER Services’ platform-based architecture delivers superior TCO, requires less effort to install and maintain, all while delivering highly automated integrated threat defense. The result is savings in time and budget when compared to more traditional NGFWs and piecemeal solutions that are less effective, labor intensive and deliver an inefficient response.
To learn more about the Cisco ASA with FirePOWER services, visit http://www.cisco.com/c/en/us/products/security/asa-firepower-services/index.html.


Whom ever is managing this site, I work for NetXperts and the name of the city is wrong. The city should be San Ramon. We need for it to be corrected.
Thank you.