Many colleagues, customers, and Cisco partners have asked me, “Why isn’t Cisco AMP for Endpoints included in Gartner’s recent Magic Quadrant for Endpoint Protection Platforms (EPP)?” The answer to us is pretty simple. AMP was not categorized as a traditional “EPP,” and hence, was not included in the report.
According to Gartner, “Endpoint protection platforms form the basis of the enterprise’s toolset to provide anti-malware scanning along with many other endpoint security features.”[i] In their Magic Quadrant for EPP, they say, “the enterprise endpoint protection platform (EPP) is an integrated solution that has the following capabilities: anti-malware, personal firewall, port and device control.”[ii] In their category of “anti-malware scanning and protection”[iii], Gartner says that “signature detection”[iv] is a “required criteria for anti-malware scanning and protection.”[v] So to us, this means an EPP is primarily the definition of a preventative tool that performs endpoint antimalware scanning and relies heavily on signature-based detection methods – also known as antivirus (AV).
Cisco AMP for Endpoints goes beyond prevention, signature-based detection, and AV. Sure, AMP for Endpoints includes certain preventative capabilities, uses signature-based detection (among many other engines) when checking the disposition of files upon initial inspection, and will block malware in real-time. But the primary value of AMP for Endpoints is it provides deep visibility into file activity on your endpoints, detects malicious behavior that other security layers may miss, and gives you the control to stop it. At the end of the day, advanced malware can evade your front-line defenses (like antivirus, firewall, IPS) and get inside. You’ll never be able to prevent 100% of attacks. AMP for Endpoints gives you the visibility into executable and file activity that you need to quickly spot attacks that slip by your front-line defenses, and lets you remediate malware with a few clicks. Watch this demo to see what I mean.
AMP for Endpoints is comprised of four primary capabilities that give you that deep visibility and control:
- Threat Intelligence: The Cisco Talos group analyzes millions of malware samples and terabytes of data per day, and pushes that intelligence to AMP for Endpoints so users are protected 24/7. Good threat intelligence lets you strengthen your front-line defenses.
- Sandboxing: Advanced sandboxing capabilities, powered by the Threat Grid engine, perform automated static and dynamic analysis of files against 550+ behavioral indicators to uncover stealthy threats.
- Point-in-Time Malware Detection and Blocking: Using one-to-one signature matching, machine learning, and fuzzy fingerprinting, AMP analyzes files at point of entry to catch and block known and unknown malware in real-time.
- Continuous Analysis, Retrospective Security, Remediation: Once a file enters your network, AMP continues to watch, analyze, and record its activity, regardless of the file’s disposition. If malicious behavior is spotted later, AMP sends your security team a retrospective alert that contains the complete recorded history of the threat: where the malware came from, where it’s been, and what it’s doing. Then, AMP gives you the control to contain and remediate it with a few clicks.
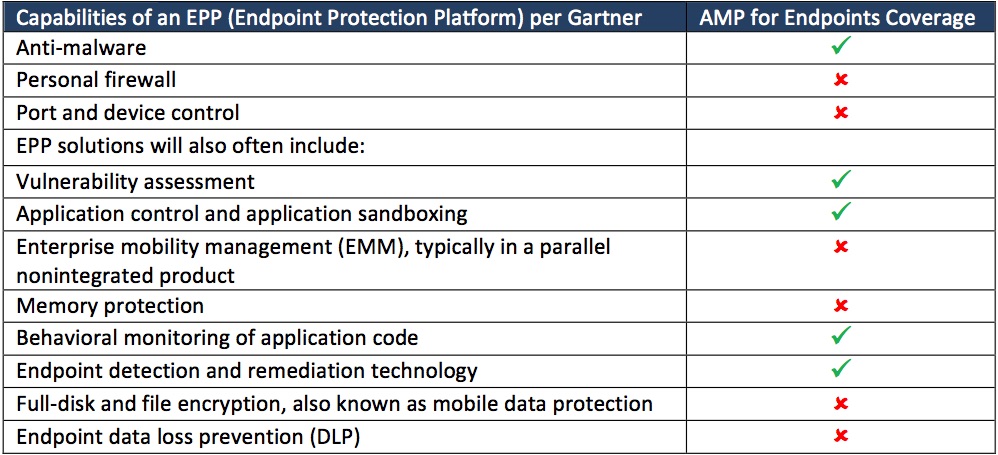
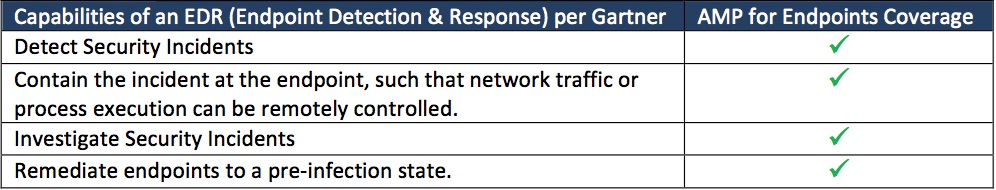
So given these capabilities, where do we think AMP for Endpoints falls in Gartner’s definitions and categories? AMP for Endpoints has some qualities of an EPP (as discussed above and see table below), but definitely most closely aligns to an EDR (Endpoint Detection & Response) solution. Gartner defines EDR solutions as having these four primary capabilities: detect security incidents; contain the incident at the endpoint, such that network traffic or process execution can be remotely controlled; investigate security incidents; and remediate endpoints to a pre-infection state.[vi] These are mostly response mechanisms, and yes, AMP for Endpoints surely hits 100% of these per the overview above. But AMP for Endpoints isn’t just about response, and goes further than that. AMP does malware inspection, detection, and blocking on the front-end, provides preventative capabilities like vulnerability mapping and low prevalence executable identification, and includes built-in sandboxing to analyze unknown files at point-of-entry.
Although AMP for Endpoints is more likely a hybrid of an EDR, EPP, and Next Gen EPP solution, Cisco is included in Gartner’s Market Guide for EDR Solutions (published in December 2015) for its AMP for Endpoints solution. There is currently no magic quadrant published by Gartner on this category. We look forward to further research in the future and hope to show AMP for Endpoints’ strength in each category of the security triad: prevention, detection and response.
But no matter what the parameters are for each category, EPP or EDR, an organization’s approach to finding the right endpoint security solution is still the same. Focus on the capabilities that your organization needs to effectively protect against threats. If you want to get the best threat intelligence to strengthen your defenses, sandboxing to uncover stealthy files, scanning of files at point of entry to detect and block malware in real time… and if advanced stealthy malware evades this and other front line defenses, the ability to continuously analyze file activity so you can quickly detect malicious behavior, see where malware came from, where it’s been, what it’s doing, and the ability to remediate malware with a few clicks… then AMP for Endpoints should be on your short list.
To learn more about AMP for Endpoints, visit www.cisco.com/go/ampendpoint
How AMP for Endpoints meets the EPP capabilities Gartner has noted these solutions will often include:
How AMP for Endpoints meets the EDR solution capabilities as noted by Gartner:
[i] “Evaluation Criteria for Endpoint Protection Platforms”, Gartner, Inc. Mario de Boer. March 24, 2015.
[ii] “Magic Quadrant for Endpoint Protection Platforms”, Gartner, Inc. Peter Firstbrook, Eric Ouellet. February 1, 2016.
[iii] “Evaluation Criteria for Endpoint Protection Platforms”, Gartner, Inc. Mario de Boer. March 24, 2015.
[iv] “Evaluation Criteria for Endpoint Protection Platforms”, Gartner, Inc. Mario de Boer. March 24, 2015.
[v] “Evaluation Criteria for Endpoint Protection Platforms”, Gartner, Inc. Mario de Boer. March 24, 2015.
[vi] “Market Guide for Endpoint Detection and Response Solutions,” Gartner, Inc. Peter Firstbrook, Neil MacDonald. December 16, 2015.






Well written document. There are really no competitors to AMP for Endpoints. It especially compliments other products including AMP technologies including ESA, WSA, CWS, ISR4300, ASA5500X, FirePOWER appliances.
This still seems to ignore the real time case of protection from the zero-day introduction of something maliciously executing – where is the whitelist management of allowable executables?
Hi jmccoy,
Neither of Gartner’s categories (EPP or EDR) explicitly call out zero-day detection as a required capability per se. But speaking for Cisco AMP for Endpoints, we do on-device static and dynamic behavioral analysis of files to detect zero-day threats and APTs. And AMP for Endpoints includes whitelisting.