Let’s face it, malware is everywhere now, and it’s here to stay. The statistics are staggering. According to the 2014 Cisco Annual Security Report, “100 percent of the business networks analyzed by Cisco had traffic going to websites that host malware” and 96 percent of the business networks analyzed had connections to known hijacked infrastructure or compromised sites. It’s a pretty scary reality for organizations and the security teams that are tasked with protecting these organizations from threats.
Not only is malware abundant and pervasive, but it comes in all shapes and sizes, including trojans, adware, worms, downloaders, droppers, ransomware, and polymorphic malware to name a few. Furthermore, it’s attacking us on all fronts, regardless of the device or operating system that we are using.
When you look at the different types of malware out in the real world, you see the more common malware variants, as well as the not-so-common ones. There is a cast of characters that we know pretty well, including Zeus trojan horse, the W32.Changeup worm, and Cryptolocker among others. While these attacks are still infecting hosts across the globe, we are more familiar with what they look like, their signatures, and their behavior. Why? Because we have collected threat intelligence on them, and as a result, using products like Cisco Advanced Malware Protection, can more easily detect these attacks and stop them.
But what about the new kids on the block? The little guys? The one-offs? The new malware that we haven’t come across in the real world yet, or even the targeted attacks, designed specifically to attack a single application at a particular organization? These are usually the hardest to detect or see in an environment. This type of malware is especially good at evading detection because we simply haven’t seen it before and don’t have the malware signatures or even a read on the behavior of the malware to detect it in the first place.
To combat this malware and protect against these types of targeted attacks, you must be able to find things that are odd or uncommon, that stand out as being weird, the type of stuff that flies under the radar. It only takes one well-planned, stealthy piece of malware to cause a breach. Even if you detect 99 percent of known malware, that remaining 1 percent is poised and ready to make your organization tomorrow’s headline news.
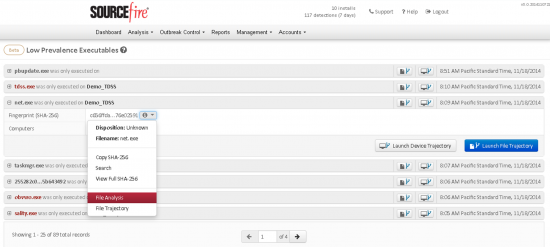
Cisco AMP for Endpoints helps you find those executables that are odd or uncommon, that stand out as being weird, not only by using Indications of Compromise, but through AMP’s Prevalence feature. Prevalence displays files that have been executed across your organization ordered from lowest to highest number of instances. This can help you surface previously undetected threats that were only seen by a small number of users or not at all. Generally, files executed by a large number of users tend to be legitimate applications while those executed by only one or two users may be malicious (such as a targeted advanced persistent threat) or questionable applications you may not want in your network.
AMP users and Incident Response practitioners alike are finding the Prevalence feature in Cisco AMP for Endpoints to be an especially powerful tool in combatting attacks. We recently sat down with John Ode and Colby Clark who talked about the importance of having visibility into “least prevalent” traffic. Take a few minutes and see what they had to say about the value that they’ve seen this capability bring to organizations.






Hello dear
My problem with Role Base CLI
I just want to an access to configure router OSPF
I created view OSPF-TUNE
————————————-
parser view OSPF-TUNE
R1(config-view)#commands exec include configure terminal
R1(config-view)#commands configure include router ospf
————————————
But when I entered the OSPF-TUNE
R1#?
Exec commands:
configure Enter configuration mode
enable Turn on privileged commands
exit Exit from the EXEC
show Show running system information
R1#conf t
Enter configuration commands, one per line. End with CNTL/Z.
R1(config)#?
Configure commands:
do To run exec commands in config mode
exit Exit from configure mode
router Enable a routing process
I just want to an access to configure router OSPF But…
R1(config)#router ?
bgp Border Gateway Protocol (BGP)
isis ISO IS-IS
iso-igrp IGRP for OSI networks
mobile Mobile routes
odr On Demand stub Routes
ospf Open Shortest Path First (OSPF)
rip Routing Information Protocol (RIP)
Please Help Me…
Hello dear
My problem with Role Base CLI
I just want to an access to configure router OSPF
I created view OSPF-TUNE
————————————-
parser view OSPF-TUNE
R1(config-view)#commands exec include configure terminal
R1(config-view)#commands configure include router ospf
————————————
But when I entered the OSPF-TUNE
R1#?
Exec commands:
configure Enter configuration mode
enable Turn on privileged commands
exit Exit from the EXEC
show Show running system information
R1#conf t
Enter configuration commands, one per line. End with CNTL/Z.
R1(config)#?
Configure commands:
do To run exec commands in config mode
exit Exit from configure mode
router Enable a routing process
I just want to an access to configure router OSPF But…
R1(config)#router ?
bgp Border Gateway Protocol (BGP)
isis ISO IS-IS
iso-igrp IGRP for OSI networks
mobile Mobile routes
odr On Demand stub Routes
ospf Open Shortest Path First (OSPF)
rip Routing Information Protocol (RIP)
Please Help Me…