[This is part one of a four-part blog series about DevSecOps.]
Today, companies are transforming their business to offer customers connected digital experiences where products and services are increasingly powered by mobile, cloud and data analytics capabilities. Developers in turn are moving to Development Operations (DevOps) processes to meet the need for greater agility and scale.
In the recent blog, “Who Gives a Cloud?”, Ruba Borno, Cisco’s Vice President, Growth Initiatives and Chief of Staff to CEO discusses the six imperatives every organization should be thinking about when approaching business digitization. Two of which are Security and Automation. In this Blog series, we will discuss how DevOps teams can achieve security automation and evolve their practices to integrate security.
Security controls are more and more becoming dynamic where they are context driven based on user, device, location, data and threats to address a changing business landscape and increasing cyber risks. Frequent advisories on critical software vulnerabilities in open source and vendor products is now the norm driving the need for agility in security responsiveness. With the industry transitioning to software defined infrastructure, we have the same opportunity with software defined security to enable security to be nimble and dynamic.
DevSecOps enables security to become a differentiator by bridging DevOps workflows with Information Security (Infosec) Operations to embed security as code, testing and validation during development, and by leveraging automation to run continuous operations.
Cisco Defines and Drives DevSecOps by;
1) Establishing a DevSecOps Manifesto
2) Running Agile Security Hackathons
3) Enacting Security Guardrails
4) Automating and delivering security as Code via Continuous Security Buddy (CSB)
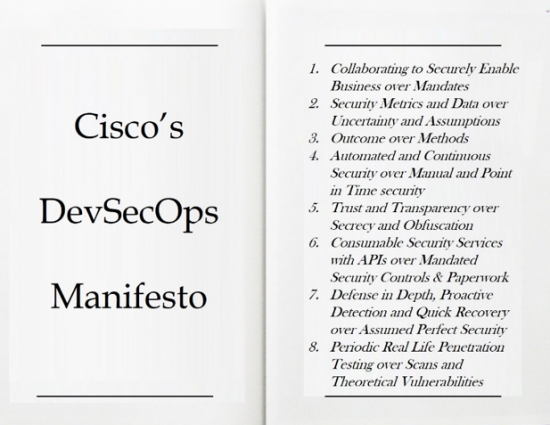
Establishing a Cloud Security Manifesto
When we engage with our internal business partners, we use clearly defined guiding principles to drive security throughout the process. This helps establish the mutual trust between the Engineering, Operations and the Security teams. We modified the manifesto provided by devsecops.org to meet our business and security needs.
In summary, the manifesto describes how we approach DevSecOps by:
- Enabling businesses to address their most critical security requirements over a checklist or security mandates
- Providing metrics to measure real, not theoretical security risks
- Defining outcomes and providing the means to achieve them
- Automating security configurations, testing and validation in the CI/CD pipeline
- Sharing security information with transparency
- Ensuring all security capabilities are done via authorized API calls
For security to be continuous it is necessary to balance offensive approaches via secure code, configurations and testing with quick detection and response to operational issues. While much of this can be automated, we do need humans to conduct real life penetration testing periodically and attend to operational security needs.
In Part 1 of this series, we have established a foundation for DevSecOps practices and in Part 2 of DevSecOps, we will share our practice of running Agile hackathons and building Security Guard-rails. Please stay tuned and in the mean-time we welcome your comments.






this is great, devsecops a way to go Sujata. workloads in cloud needs to be handled along with CI, CD. great Manifesto
Every App needs to provision fast and agile by the business nowadays. But this very insecure. Please protect your workloads customer.