 The proven value of Software-as-a-Service (SaaS) solutions, that we all access daily from multiple devices, makes the cloud a reality, but SaaS also creates an environment in which anyone, anywhere in an organization, can be attacked at any time. Modern Networks go beyond traditional walls and include data centers, endpoints, virtual and mobile – all linked by cloud services. To some the cloud is an attack vector while to others it’s a business enabler. Security as a Service bridges these two definitions to deliver the scale of cloud engines to address security challenges found anywhere in the Modern Network, whether physical, virtual, local or remote.
The proven value of Software-as-a-Service (SaaS) solutions, that we all access daily from multiple devices, makes the cloud a reality, but SaaS also creates an environment in which anyone, anywhere in an organization, can be attacked at any time. Modern Networks go beyond traditional walls and include data centers, endpoints, virtual and mobile – all linked by cloud services. To some the cloud is an attack vector while to others it’s a business enabler. Security as a Service bridges these two definitions to deliver the scale of cloud engines to address security challenges found anywhere in the Modern Network, whether physical, virtual, local or remote.
Two recent stories from our Cloud Web Security (CWS) Service , illustrate the power of the cloud to address security concerns. The first focuses on the sheer processing power we can deliver from our global data center estate, and the second covers the elastic capacity our investment in Next Generation infrastructure provides, ensuring we can turn up the dial when our customers need more bandwidth, delivered securely.
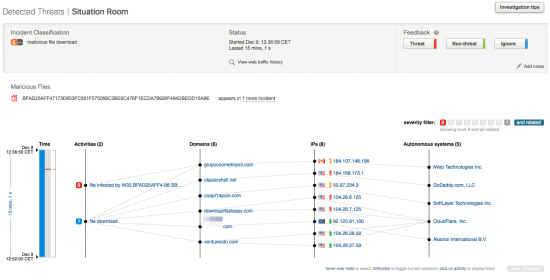
The first example goes to the heart of our latest announcement, demonstrating how the cloud can learn from one environment and quick leverage that learning to improve the security coverage of all customers. Last week the CWS team release CWS Premium for advanced threat protection. CWS Premium combines the two distinct services of Advanced Malware Protection (AMP) which examines file reputation, file behavioral analysis, inclusive of sandboxing and retrospective alerting of infected hosts, and Cognitive Threat Analytics (CTA), which uses machine learning to examine traffic patterns for anomalous behavior indicative of compromise. The combination of these two announcements brings enterprise-class advanced threat protection delivered from the cloud and addresses the number one request from our growing global customer base.
During the AMP pilot we learned something about the power of the cloud-delivered service. A beta user submitted an unknown file to the AMP sandbox, a file not known to anyone – external verification showed zero detects. What happened next showed that the file was far from benign and produced a very detailed set of reports and analysis. The high level summary goes like this: Our sandbox discovered that the file was in fact malware, and then classified the file as malicious in the AMP cloud, sending a retrospective alert to the CWS user. This enabled the user to see where the file came from, the behavior of the file over time and what other systems had been infected. Moving outside this customer, with the AMP cloud aware of the malicious nature of this file, over the next 12 hours the file was detected and removed in nine other CWS enterprise customers, without anyone having to make a decision to change policy or reconfigure existing solutions. This demonstrates the closed loop nature of our system, teaching itself and automatically projecting its new knowledge by way of protection to all of our customers – all without human intervention. If those nine customers within the first 12 hours had – at a conservative estimate – 15,000 end points each, that’s 135,000 users protected without anyone actually doing anything. Within 24 hours that number of customers was beyond 30, and the number of estimated end users at almost half a million and no one pushed a button after the original file was submitted to the cloud.
The second example pivots us away from advanced threats and demonstrates the power of the cloud to scale. We are always updating and investing, growing to meet capacity, and recently we became aware that a very popular consumer hardware and software vendor was about to release an upgraded version of its operating system to potentially test that capacity. I can’t name names, but it’s safe to say that fans of the device worldwide were thrilled by news of new software, and were eager to download the update the instant it was released. This posed a number of challenges, particularly for web security services. Traffic volumes after past such events have increased between 15-20% worldwide, which not only places a strain on our customers’ networks but also means our cloud-delivered service has to be ready to process a vast increase in capacity.
How vast an increase? The daily volume of CWS traffic for this particular update spiked to 16TB. Stop for a moment to imagine 16TB. Imagine a premium Netflix account, streaming 1GB per hour in HD. Now imagine watching 1,000 hours of video, that’s 41 days worth of constantly watching HD movies. That’s 1TB. It would take 656 days – almost two years of data streaming at the same rate and about 4,500 movies – to equal 16TB, the same amount of extra data rammed through the global CWS estate in 24 hours with no degradation of service. And that’s 16TB of additional traffic, not counting the rest of the daily web content being processed.
Our mission has been to proactively ensure that CWS customers continued to experience excellent performance from their own networks during the first few days of the update availability, while delivering the stable, high-performing CWS service that customers have come to expect. We tuned data centers in readiness, advised customers of the impending spike, gave them the option to block the relevant traffic if they chose and we monitored traffic patterns in real time to optimize loads. No support cases raised and no drop in performance. Mission accomplished.
Today’s cyber attacks threaten precious Intellectual Property (IP), valuable customer information and state secrets. You only have to look at the daily news headlines to find about the next high-profile attack. In fact, Cisco reports stopping an average of 320 million cyber attacks each day, up substantially year over year. That’s like everyone in the US launching a cyber attack each and every day. The web is the attack vector in an increasing number of these cases. To protect valuable resources requires a threat-centric, operational model that is advanced beyond an attacker’s abilities and addresses the extended network and evolving business environment. Whether harnessing cloud power or offering scalability, CWS is a crucial component in enabling organizations to embrace this approach and capitalize on the efficiencies that a cloud-based model offers.
For more information, visit: http://cisco.com/go/cws






Thanks for the read. Malaware is always a hassle especially when dealing with it in inhjected formatted code. Truly a nightmare thanks for sharing. http://www.joshhacks.com
Hi Raja,nice gains by CWS but can you comment on the longterm prospects for scansafe in regards to recent rumors about the service being cut???
Thanks for your comment Pat.
Cisco Cloud Web Security (CWS) continues to add functionality and grow in sophistication. Rumors about the service are just that – rumors, without basis.
CWS continues to be an important part of Cisco’s security portfolio.
still i wonder about the ISR integrations – all experience with ISR and CWS was so poor. traffic redirection – broken. user granularity and AD integration – broken. reporting in the CWS portal – broken or so very slow to be unused by the team.
is the CWS still viable product, or is this the life support? we used since before the Cisco bought scansafe and then nothing improve ever, only got worse. shameful neglecting.
Raja – WHAT HAPPEN?
Thanks for your comment Manish – as a general rule we roll out updates to the service every two weeks and so we are continually striving to improve customer experience. Specifically , in addition to the AMP announcement, last week we also launched the Log Extraction feature, giving CWS customers faster access to their logs, and enabling integration with other security devices such as SIEM. This was the number one customer request.
In addition to the announcements listed above, all CWS connectors continue to receive investment and engineering resources. A recent example are two improvements to the ISR G2 connector, released within the last 30 days.
The first, Cloud Whitelisting allows users to create exception lists through the ScanCenter portal that are automatically downloaded and enforced on ISR G2 routers. The second, Integrated Telemetry, allows for the automatic reporting of telemetry data back to Cisco TAC to simplify the investigation of customer reported issues. This improves the closed-loop of information from customer environments to our cloud, also allowing Cisco to further fine-tune the efficacy of our cloud-delivered security engines. Customers are required to explicitly change configuration settings to send telemetry data to Cisco, which contains no company specific or personally identifiable information (PII).
Hi,
I really like the title of this article, applause! and the content is really interesting. I woul like to ask permission is I can quote this on my blog, I am also discussing Cloud and other stuff related to it. Thanks.
Hi Reggie!
I am an editor on the Cisco Security blog. Thanks for reading and asking for permission to quote Raja. Like most blogs, we encourage sharing information that we publish here. We simply ask that if you quote Raja’s post, please include a link back to this page as source attribution.
Thanks for your inquiry and for reading the Cisco Security blog!