If you attended a Cisco Live or an RSA conference in the past couple of years you may have come across a display entitled “Cisco Security at Work”. This display, often referred to as the Threatwall, is a live display of threats on the wireless network at the conferences where it is deployed. Currently we have the Threatwall deployed at Mobile World Congress (MWC) 2019.

As open networks that event attendees can join, conference wireless networks are always interesting and over the last few years we have observed varying threats and trends in networks and so far, MWC has proven to be no exception.
First a brief description of the Threatwall. We feed the Threatwall with a ten gigabit SPAN from the edge of the wireless network which is sent through a Firepower appliance and a Stealthwatch Flow Sensor, facilitating the four screens which we display two visuals from the version 2.3 of the Firepower Management Console (FMC)) and version 7.0 of the Stealthwatch Management Console (SMC). In the deployment at MWC this week we are even using a beta version of the Stealthwatch 7.1 Flow Sensor that generates enhanced telemetry to better power Encrypted Traffic Analytics.
Here are some stats about the network after the first day of the conference as seen in both the FMC and the SMC dashboards:
- Over 58,000 hosts have joined the network, communicating 1.1T of internal (east-west traffic) and 46.8T of traffic exchanged between the conference network and the outside world
- Of the 46.8T of traffic, approximately 29.7T of it was encrypted
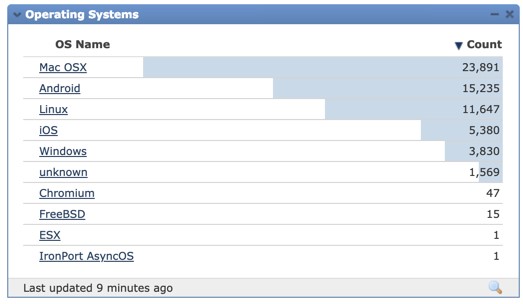
- The more than 58,000 hosts are of varying device types, with those running Mac OSX/iOS being the most prevalent.

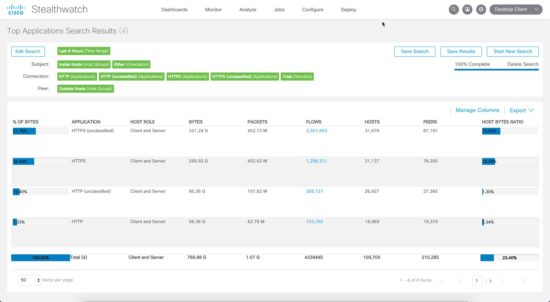
The growth in encrypted traffic is interesting and continues a trend we’ve been seeing over the past several years. Digging deeper we can see that HTTPS is by far the most prevalent application on the network. The char below, Traffic by Application, is also potentially misleading as some of the listed applications (ex. Facebook) are in fact communicating over HTTPS.

Digging deeper in Stealthwatch we can actually see that there is approximately a 85%:15% ratio of HTTPS:HTTP traffic on the show floor today. This ratio is consistent with what we have seen on other conference networks and the percentage of HTTPS is slowly increasing at every event.
As a network that attracts many different people and devices, the MWC network, like any conference network, also attracts its fair share of threats and other oddities. The first observation of note is the number of hosts identified by Stealthwatch as scanning the network interior (23). Seven hosts on the inside network successfully connected to an SMB share on the internet and 89 DNS servers that are not the ones provided by the wireless network’s DHCP server.

Using DNS services other than those issued by the corporate network is a common methodology in malicious software and flipping over into the FMC we can see that there have been a number of hosts that appear to be infected with various forms of malware, specifically trojans that are reaching outbound.
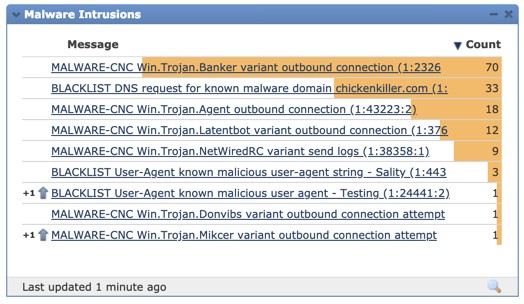
We can also see that the trend of using a point of presence on a victim device to perform cryptomining is still quite prevalent. The first time we saw this trend in the Threatwall was at Cisco Live Barcelona 2018 and it continued throughout 2018 and now into 2019.
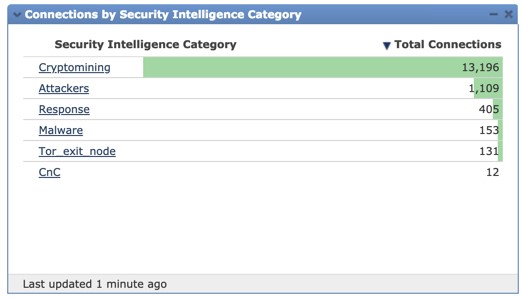
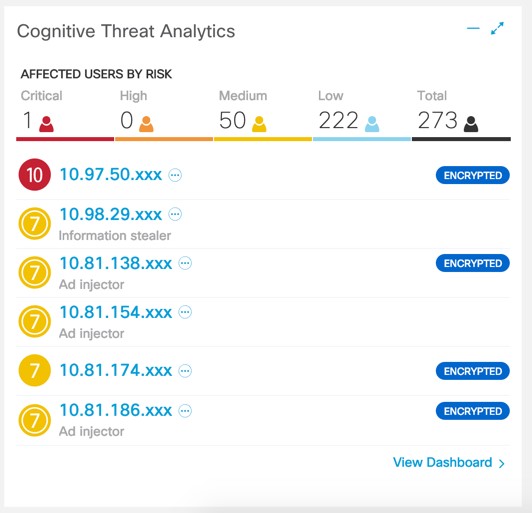
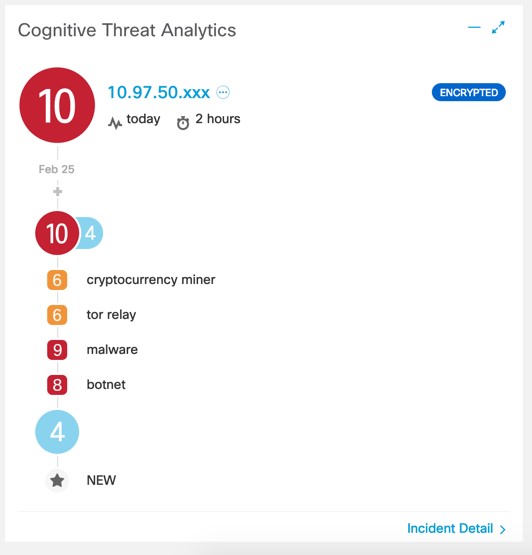
Now let’s take a look at Cognitive Intelligence and what threats it has detected using its multi-layer machine learning engine, inclusive of encrypted traffic analytics. We can see that there were several threats detected and identified in encrypted traffic, a number of these being ad injectors and information stealers. By clicking on one high severity threat we can see that it is indeed a cryptominer, identified using encrypted traffic analytics.

Finally, if we look at the details of the highest severity host detected by Cognitive Intelligence, we can see that this host has a variety of bad or unwanted behaviour, inclusive of the use of TOR, cryptomining and what looks like malware activity. Read this blog for more on how Stealthwatch analytics can detect cryptomining in encrypted traffic.
Conference networks consist of a varying collection of mobile devices coming together from all over the world and every time we deploy the Threatwall, we see interesting things and capture general trends in terms of what types of devices, traffic patterns, and threats are emerging. If you are at MWC in Barcelona this week I would encourage you to come by the Cisco booth and take a look at what we are seeing on the conference network in real time.
And if you miss Cisco Security at Work at MWC this week, the Threatwall will be deployed again next week at the RSA Conference in San Francisco. Hope to see you there!





