For security strategies to succeed, security needs a seat at the table. In my work as an investigations manager for Cisco, I’ve seen first-hand how much more passion and enthusiasm enterprise leaders will put into security efforts when there is support all the way to the top of the organization.
The Cisco Security Capabilities Benchmark Study, as detailed in the Cisco 2015 Annual Security Report, shows that when there is executive-level responsibility for security, organizations are in a better position to tackle security challenges. As part of the survey, Cisco asked chief information security (CISO) and security operations managers about their views on security readiness. The good news, from my standpoint, is that 91 percent of the security professionals surveyed said their organization has an executive with direct responsibility for security – usually a CISO or CSO. It’s an encouraging finding, because security leaders help define and enforce policies.
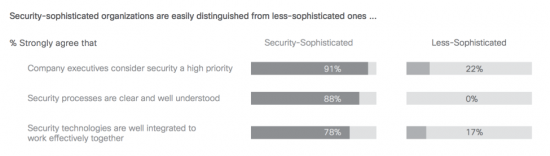
However, just because there’s a leader with a security-related title doesn’t mean that all of an organization’s security problems are solved. The Cisco study found that organizations categorized as having a sophisticated security posture – for example, those that have well-documented policies – are more likely to believe that security is a high priority.
As seen the table below, 91 percent of survey respondents from sophisticated companies strongly agree that their executives see security as a high priority. On the other hand, only 22 percent of respondents from the least-sophisticated companies agree with this statement. Eighty-eight percent of respondents from sophisticated companies strongly agree that security processes in their organizations are clear and understood. None of the respondents from the least-sophisticated companies agreed with this point.
In other findings from the Cisco Security Capabilities Benchmark Study, CISOs showed a markedly higher level of confidence in their security postures than security operations managers. For example, 62 percent of CISOs said they strongly agree that security processes in their organization are clear and well understood, compared to only 48 percent of security operations managers. Also, 59 percent of CISOs said they strongly agree that these processes are optimized and that they now focus on process improvement, compared to 46 percent of security managers.
At Cisco, we suspect this gap in confidence between CISOs and security operations managers occurs because of their different viewpoints on day-to-day security activities. Because CISOs are not as hands-on when it comes to solving security challenges, they have a rosier view of their security landscape. Security operations managers, who are close to the ground resolving both major and minor security issues, probably have a more realistic outlook.
It’s good to see that security professionals are feeling confident about their security readiness, but the benchmark study also pointed to signs that respondents may be somewhat overconfident. For example, less than 50 percent of respondents said they used common and readily available tools that can help prevent security breaches, including patching, user provisioning, and endpoint forensics. If security organizations are not making frequent use of these fundamental tools, then their confidence may be somewhat misplaced. It also means we still have work to do when it comes to educating our security colleagues about the most effective ways to respond to cybersecurity challenges.
Read the Cisco Security Capabilities Benchmark Study in its entirety in the Cisco 2015 Annual Security Report.






I can agree with this article, and I share the same sentiments of the security operations managers. I believe that our approach to Cybersecurity could be more effective if we only approach it by placing priority on fixing the human aspect of information security first, and then using the Technological and Law aspects as supporting mechanisms. However, we have lost our way and CISOs/CSOs have forgotten in which direction they ought to go. Its like having a vehicle (a car) with a family inside traveling from florida (point A) to New York (point B), and knowing that the car is supporting the family’s desire to move from point “A” to point “B”. I fear that most Security Officers have derailed their organizations main goal by allowing the car to produce the desired direction of the family, which means that the family is now being forced to follow into the direction where the vehicle is taking them. In essence straying away from the organizations original goal.
Regards,
Omar gentles