Black Hat USA is my favorite Cybersecurity conference of the year, a relaxed atmosphere with fellow professionals and reunions with friends developed over the years. The Black Hat NOC is run by UBM, and Cisco Security is honored to be a technology partner for malware analysis/threat intelligence and DNS. I was in Las Vegas for a week, as the team arrives early to set up the network that will support the conference Trainings, Briefings, sponsors and attendees; about 20,000 people. The NOC team quickly deployed a secure wireless network for the conference, with Gigamon providing twin 10GB per second trunks into the Mandalay Bay Conference Center. UBM recommended they turn off their Conference WiFi for the week, as we provide our own infrastructure and it would be safer for them. 😊
The Palo Alto Networks team pointed their firewall’s DNS to Cisco Umbrella, and routed the traffic to Ruckus, who set up over 100 access points and VLANs for each classroom and meeting room. This allows us to have control and visibility, just in case a training event on exploits / attacks mistakenly or deliberately spills over, or some other attack / DDOS occurred. A span of the traffic went to RSA NetWitness Platform v11 for identity and network forensics, backed by one half petabyte of storage, with the potentially malicious attachments of emails and web down loads sent to Cisco Threat Grid for dynamic analysis. The RSA team also brought their NetWitness Orchestrator for automation, including tying in a honey pot and a map of the conference center so the physical location of any network incident could be instantly visually identified.
ATT&CK!
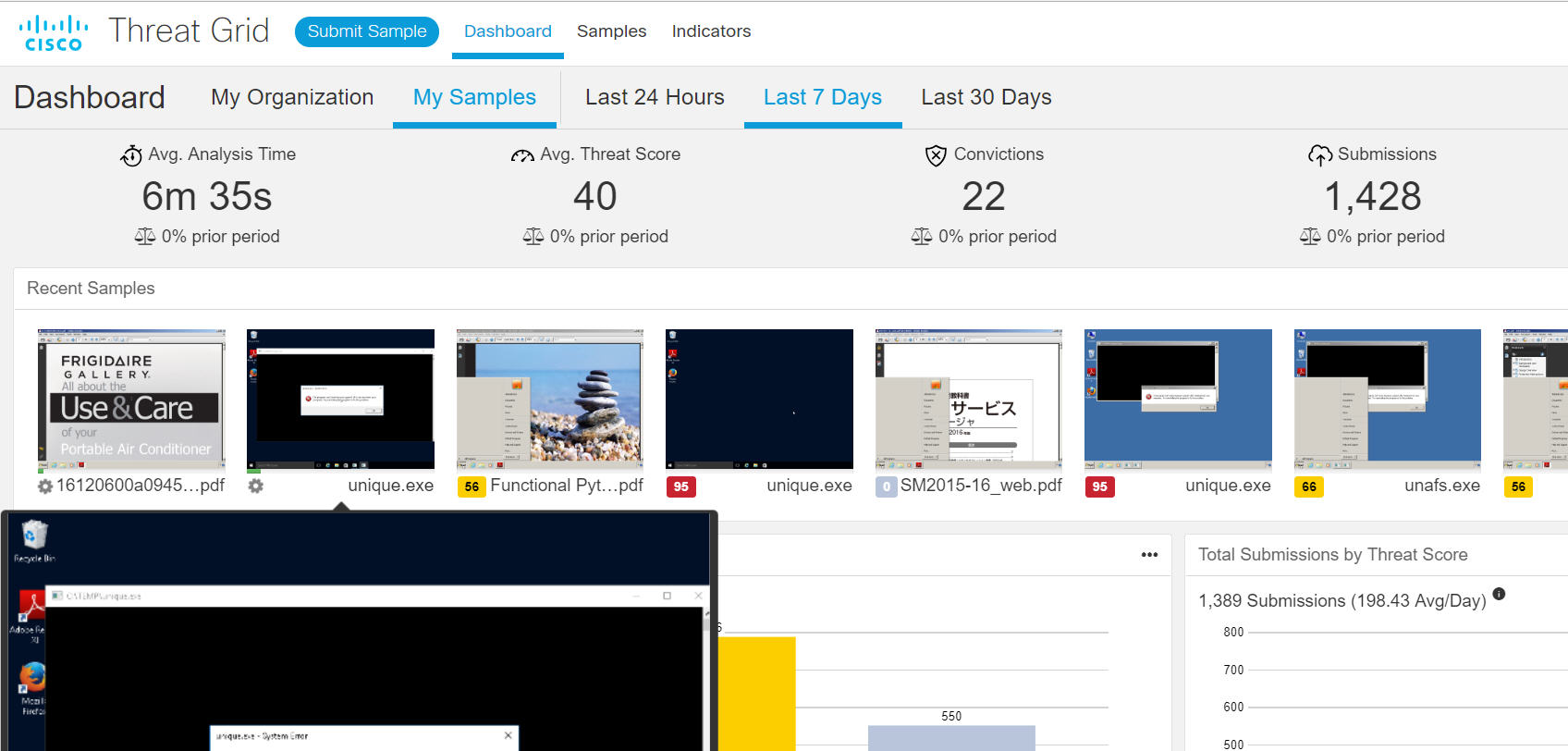
As samples came into Threat Grid, the NOC team could see them detonating in the virtualized environment. The team would often stop and look as a stream of files entered, and the automation began. It was a unique visual, whcih most had never seen before. By default, the playbook of random cursor movements is used in the virtual machine, to emulate user activity. We could click on the thumbnail to interact with the sample in the Threat Grid Glovebox.
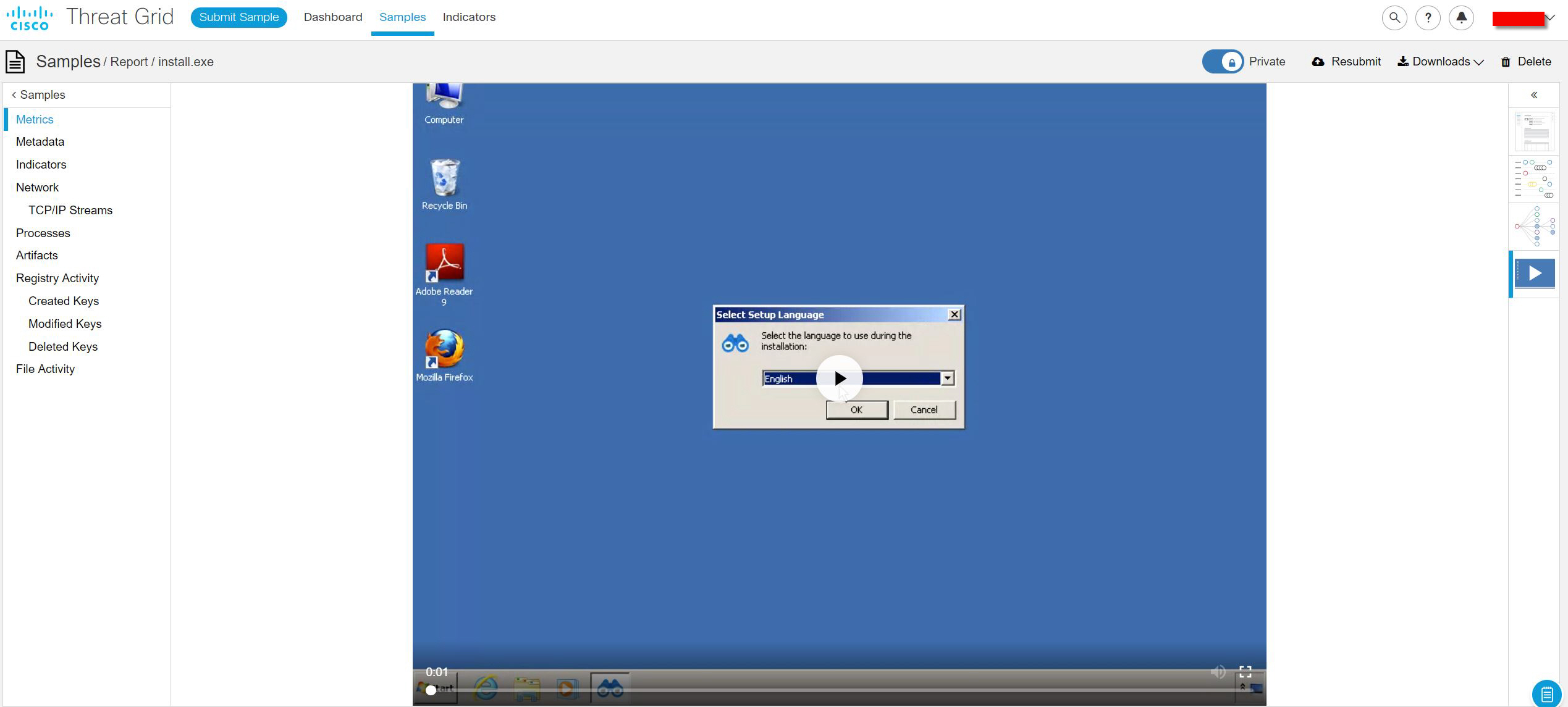
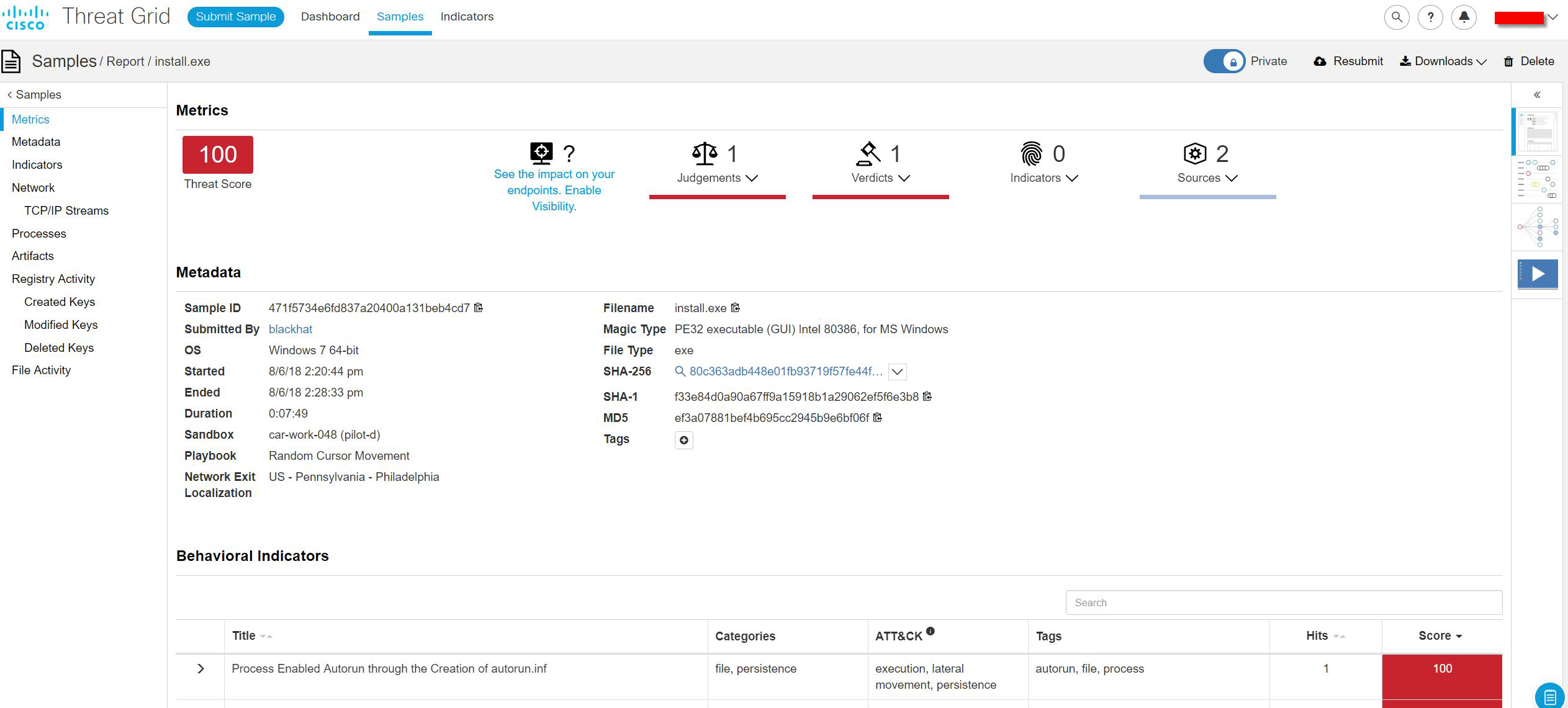
When we would see an installer come in, we would click into the Glovebox and install it, such as this install.exe that was downloaded by a user during one of the training events.
As I went through the installation and the application launched, I quickly realized it was a keystroke logger on steroids. You can select the users to monitor and set up remote viewing of the logs and collected data.
In addition to the logging of keystrokes, by default it monitors clipboard text, USB drive insertions, Skype IM chats and web browser/search history.
It also offers the feature of turning the computer into a listening / recording device.
And, saving the webcam and screen captures; as well as Skype video calls.
I alerted the RSA response team, as this not something authorized on the Black Hat assets, like the registration computers; nor would we want it spreading laterally in the conference network, nor would we allow it on an enterprise network. Since we don’t own the endpoints, with the exception of the conference registration computers, most remediation is blocking an abusive user from the network. I also reviewed the analysis report for more details.
New to Threat Grid is the integration of MITRE’s Adversarial Tactics, Techniques, and Common Knowledge (“ATT&CK”) framework tactics to behavioral indicators in the sample analysis report, the Indicators manager page, and individual behavioral indicators pages. The ATT&CK knowledge base can be useful for threat risk assessment, security improvements and defense effectiveness verification. So, for each behavioral indicator, like Potential Code Injection Detected, we could better understand the tactics.
Spear phishing bait in the clear
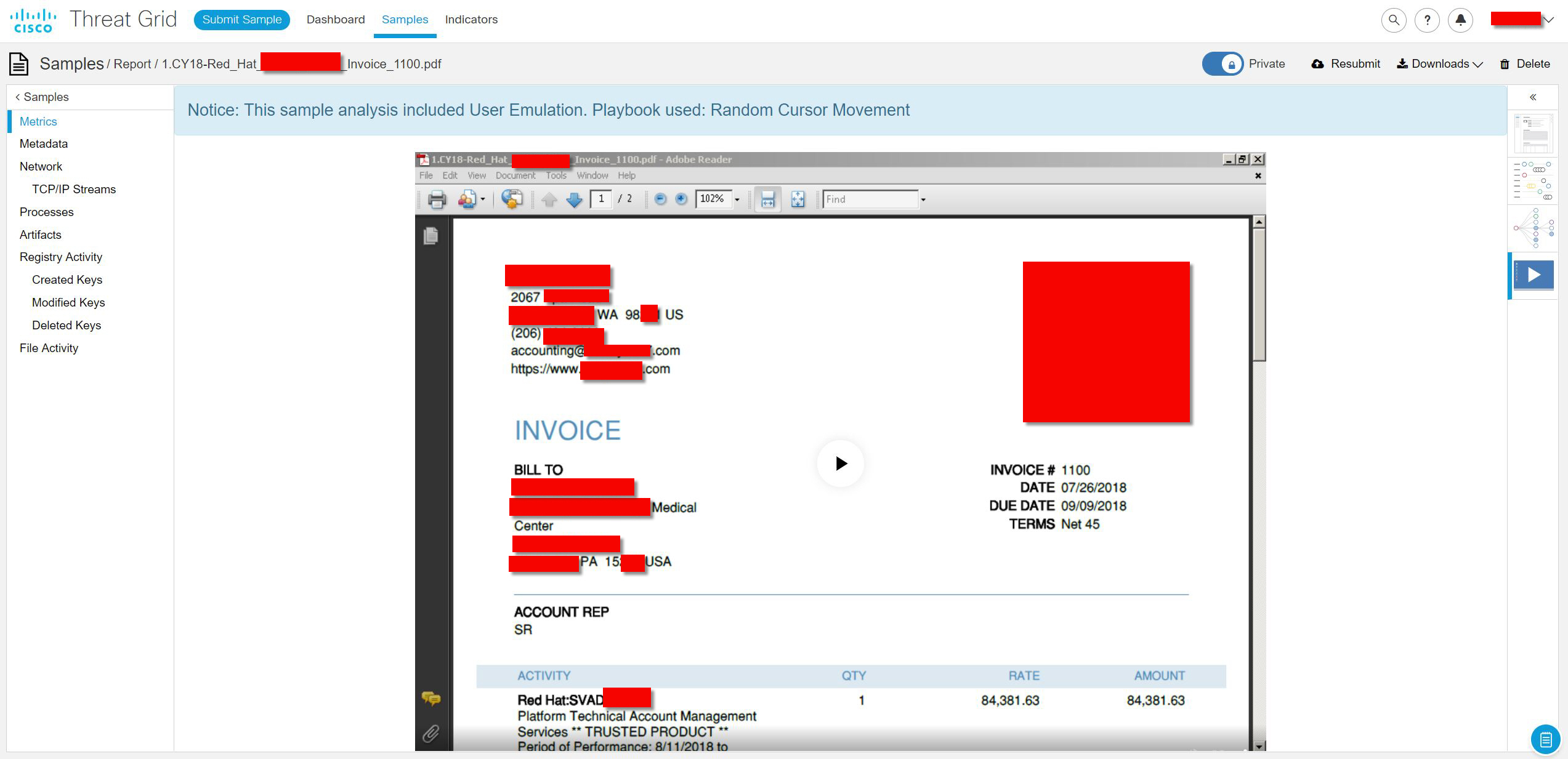
Like at RSA Conferences in San Francisco and Singapore this year, we saw many financial documents as attachments to emails sent with unsecure protocols, such as POP3 and HTTP. Each could be used by an attacker, sniffing the public network; to craft a custom spear phishing lure, as they had legitimate business and financial information; such as the email addresses of the sender/receiver, account information, billing address and the types of products/services the email recipient expected to receive.
In this case, we alerted the RSA NetWitness team, who tracked the estimate back to the sender, the CTO of a cybersecurity consulting firm who provided value added services and sold cybersecurity products from a major sponsor of Black Hat. Knowing the security hardware and model numbers at a location only further aids a potential attacker. The CTO’s emails were all in plain text, with a simple password.
The unencrypted emails continued through the conference training days, attaching several documents containing financial information, including an invoice to a Pennsylvania based hospital for $84,000 in services.
Many other users downloaded financial documents using http instead of https protocols. Read about the NOC tour we gave Rob Pegoraro of The Parallax news service, highlighting these issues, here.
Double the DNS Requests
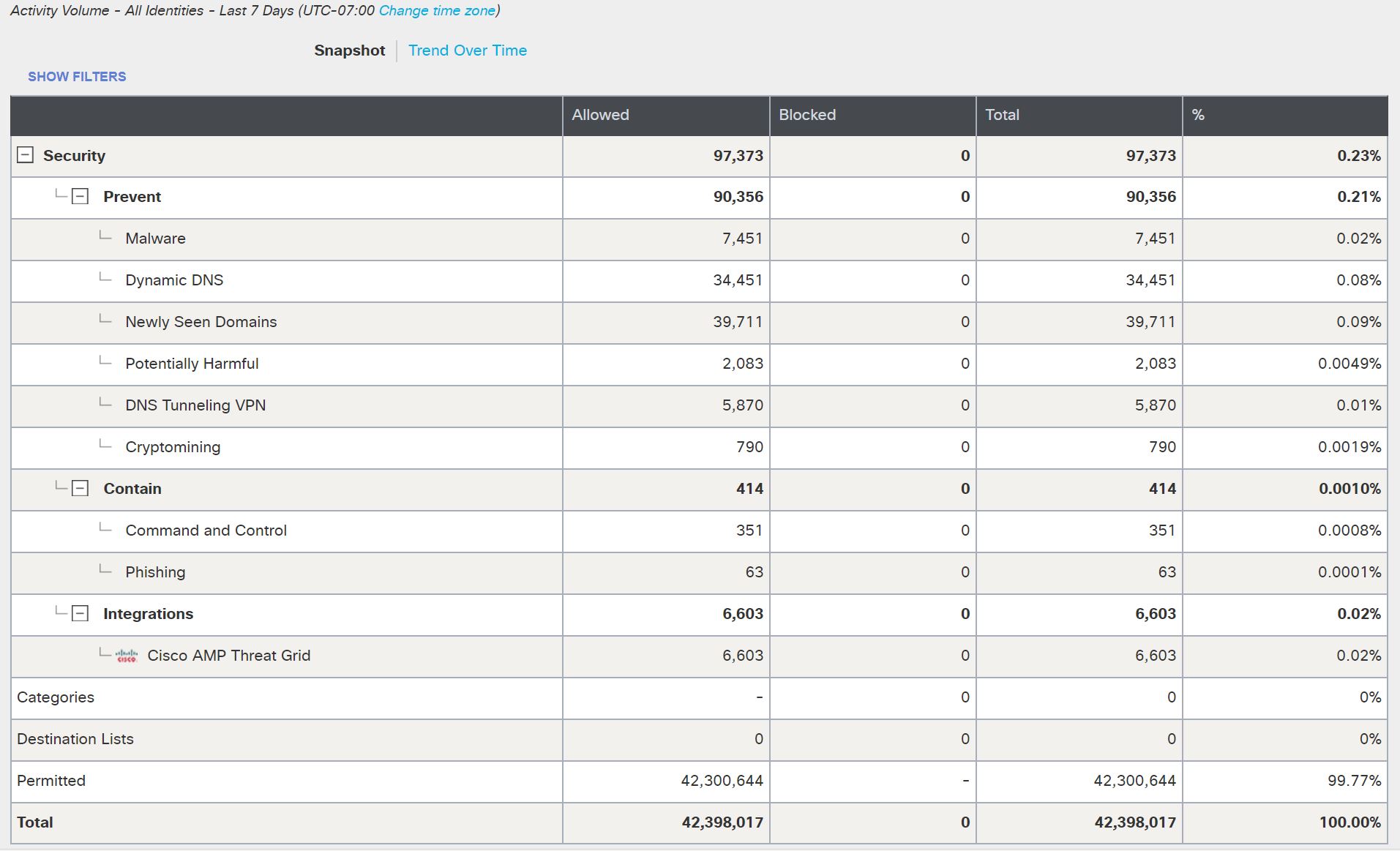
At Black Hat USA 2017, we introduced Cisco Umbrella to the NOC and in that conference we saw about 17 million DNS requests. That volume more than doubled this year, with Window update requests firing off immediately as the conference assets came on line, to over 42 million DNS requests.
With the Total Request report, we could see the ebbs and flows of the traffic, with the Trainings utilizing DNS requests much more than the Briefings and Business Hall.
By default, Cisco Umbrella will block all DNS queries to domains known to have associations with Malware. Since this is an educational conference, all blocking is turned off. Thus when a presenter apparently showed the dangers of mistyping popular URLs, without DNS protection, the web traffic was allowed. Note: Links go to the Cisco Umbrella reports for each domain.
| Destination | Categories |
| southwest[.]cm | Gambling, Malware |
| soutwest[.]com | Parked Domains, Malware |
| southwewst[.]com | Malware |
| soutwest[.]com | Parked Domains, Malware |
| southwest[.]us | Malware |
| diwney[.]com | Malware |
| disneycom[.]com | Malware |
| fannniemae[.]com | Malware |
| capityalone[.]com | Malware |
| capiatlone[.]com | Malware |
| capitalone[.]it | Malware |
| capitlone[.]com | Parked Domains, Malware |
| ccapitalone[.]com | Parked Domains, Malware |
| capitlone[.]com | Parked Domains, Malware |
| amewricanexpress[.]com | Malware |
| emericanexpress[.]com | Malware |
| amewricanexpress[.]com | Malware |
| googlew[.]com | Search Engines, Malware |
| googke[.]com | Malware |
| googlw[.]com | Malware, Web Hosting |
| googke[.]com | Malware |
| goggle[.]com | Parked Domains, Web Spam, Malware |
| googe[.]com | Search Engines, Malware |
| herwhey[.]com | Malware |
We were able to use the Umbrella Investigate intelligence to further understand the global traffic and threat.
Including, the registration, associated IP addresses and distribution of requesters. I’m wondering if Southwest Airlines has a call center in Ireland?
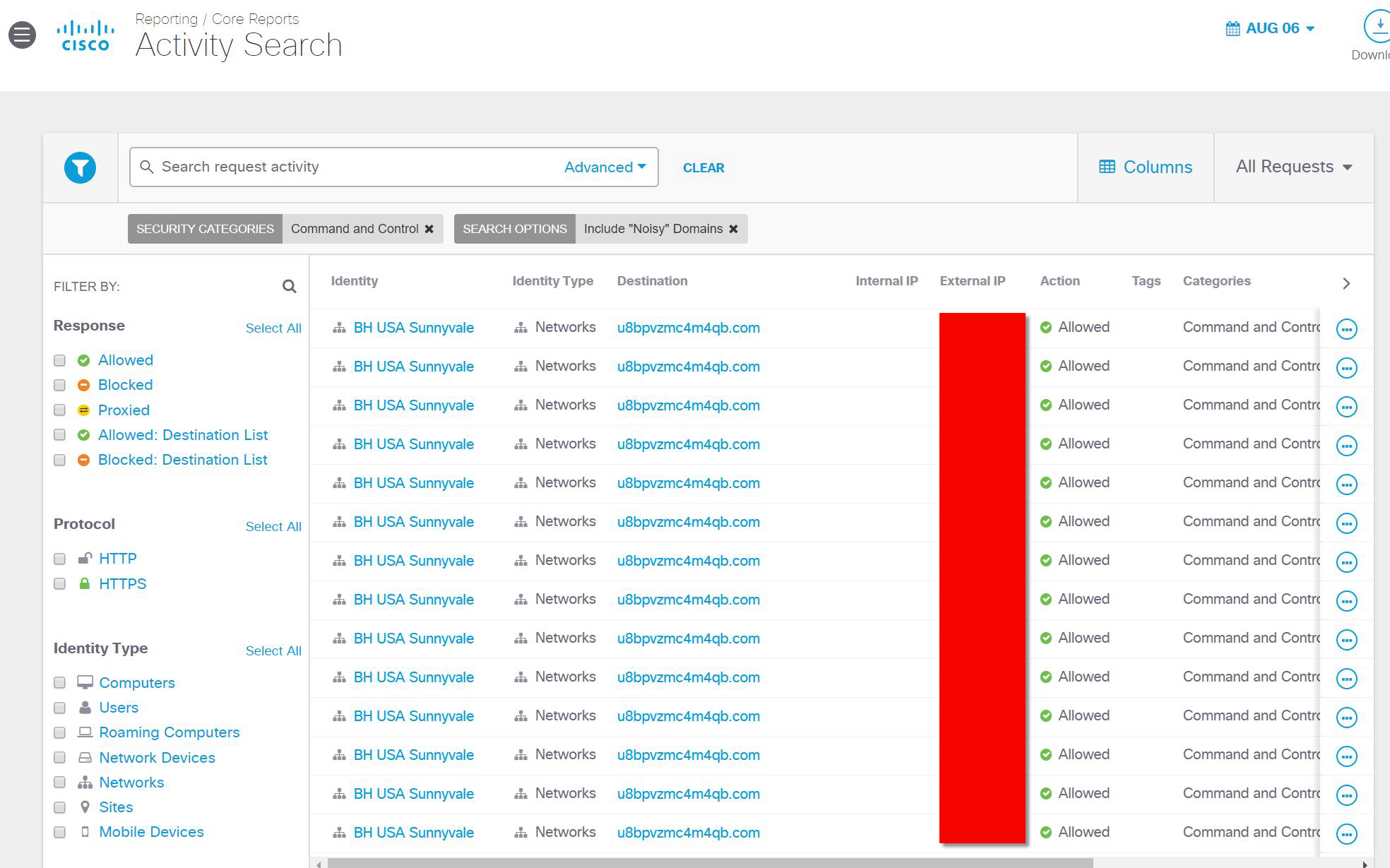
Command and Control
By default, Command and Control traffic is also blocked in an enterprise deployment of Umbrella Protect. The blocking is also turned off for this educational conference. However, I noted a lot of traffic to the same domain.
Clicking on the destination link, we could see the intervals of communication, during conference hours
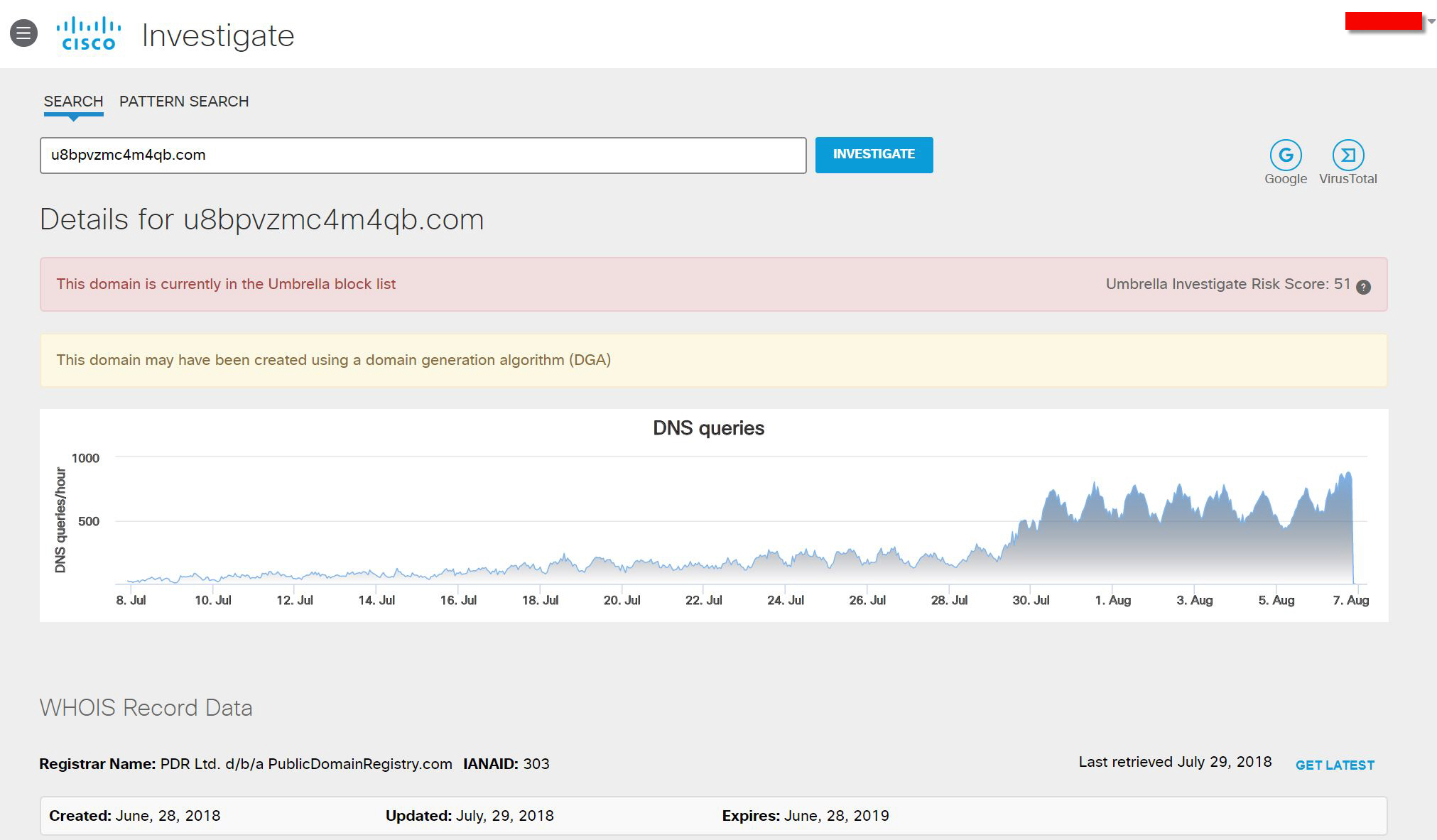
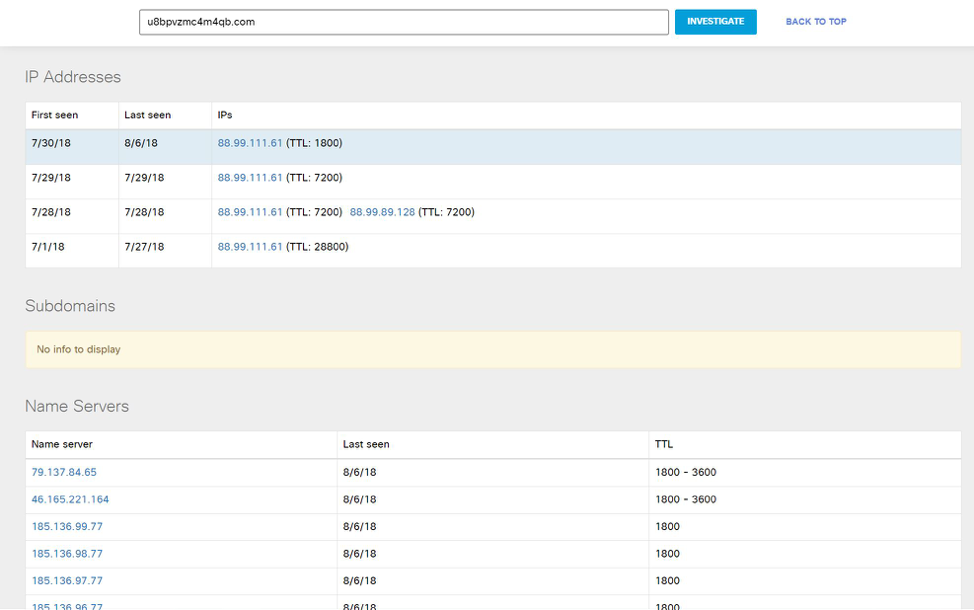
I pivoted to Umbrella Investigate for additional information. The domain was about five weeks old, with increasing global connections.
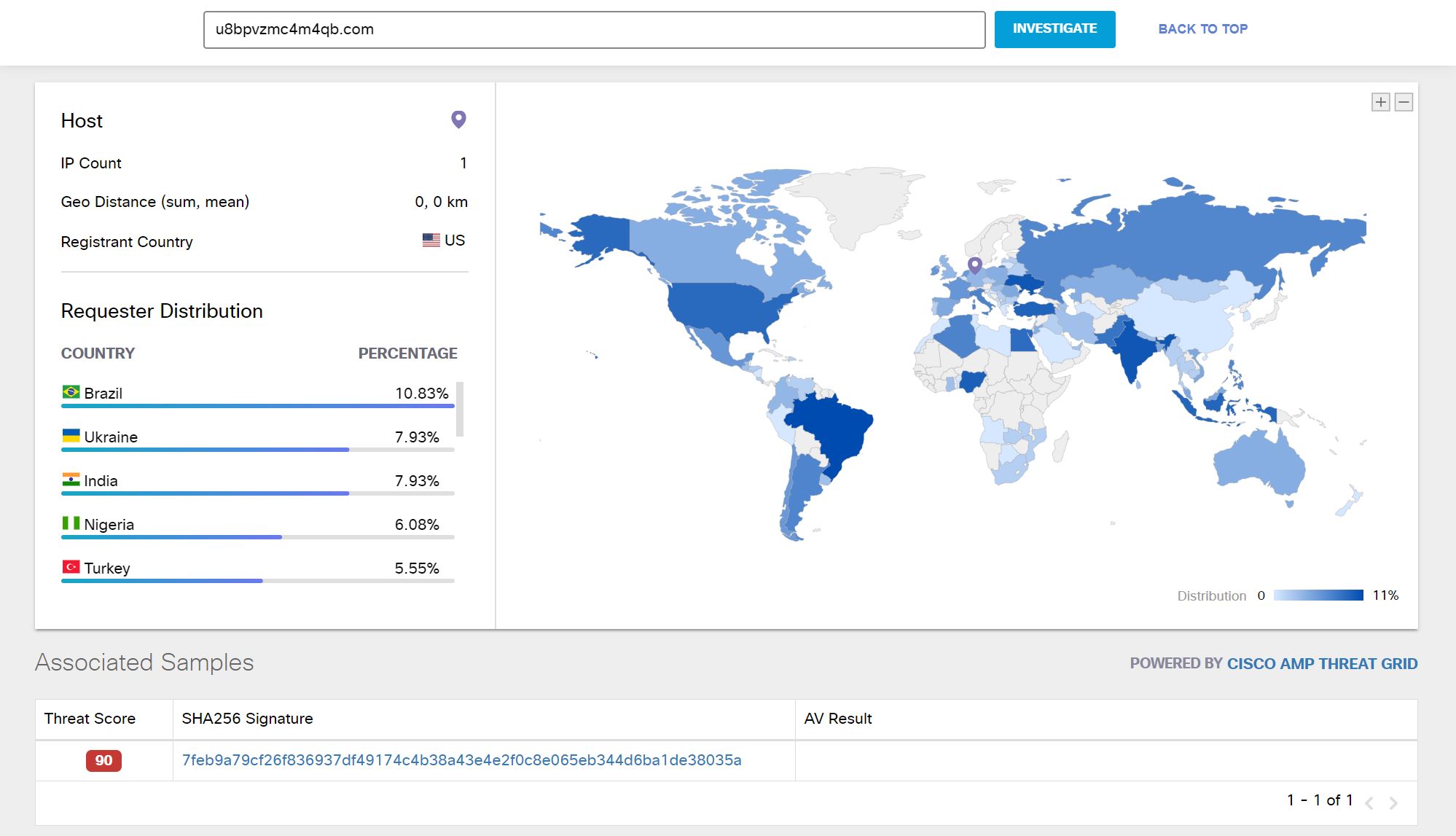
The distribution of Requesters was truly global.
I determined the IP addresses associated and took the intelligence to the RSA NetWitness team.
With the domain intelligence, the RSA team was able to track back to the user who was requesting the domain and evaluate other traffic. An incident ticket for monitoring was created, and the same user was beaconing out to dozens of IP addresses and apparently infected with a monero crypotomining javascript, looking at the indicators of compromise in NetWitness.
It would not be Black Hat / DefCon week without some pranks. On Sunday evening, a user unleashed a DNS flood of over 200,000 requests to a fake domain. The system handled it and we monitored to ensure it did not happen again.
Cisco Women in Cybersecurity
Black Hat is such a wonderful venue to sharing stories and knowledge. When I joined the Black Hat NOC crew, there was only one other female on the technical teams. Now, we have about a half dozen women on the team between the several member companies. I’m proud of the UBM leadership for encouraging the fellow managers to look out for qualified women to bring into the NOC team.
In additional to my regular duties at Cisco, which are to manage the partner ecosystems for Threat Grid, AMP for Endpoints and Cisco Security Connector; I volunteered as the Global Lead for the Attract Pillar for Cisco Women in Cybersecurity. We were proud to be a part of the Cisco recruiting team at the Black Hat Career Zone, to encourage women to consider a career in Cybersecurity at Cisco.
We also have initiatives to help Build the next generation of female Cybersecurity professionals and to Connect with other groups who are doing great work to support women. There are many career opportunities at Cisco Security. Check us out! J 
If you would like some hands on experience with some of the technology in the Black Hat NOC, I will be at the INsecurity Conference 2018 in Chicago, at 10:00 AM, 24 October 2018, with the track, “Tracking Ransomware – Using Behavior to Find New Threats“.
Acknowledgements: Thanks to my awesome teammates for the cloud-based Cisco Security at the Black Hat USA NOC, Michael Auger and Nick Frangia. Also, thanks to all of our Black Hat NOC partners; especially Percy Tucker and Sean Ennis of RSA Security. And to Grifter, Bart Stump, Steve Fink and Melissa Parker of UBM/Black Hat. See you in London for Black Hat Europe 2018!