Our core mission in the NOC is network resilience. We also provide integrated security, visibility and automation, a SOC inside the NOC.
In part one, we covered:
- Designing the Black Hat Network, by Evan Basta
- AP Placement Planning, by Sandro Fasser
- Wi-Fi Air Marshal, by Jérémy Couture, Head of SOC, Paris 2024 Olympic Games
- Meraki Dashboards, by Rossi Rosario Burgos
- Meraki Systems Manager, by Paul Fidler
- A Better Way to Design Training SSIDs/VLANs, by Paul Fidler
In part two, we are going deep with security:
- Integrating Security
- First Time at Black Hat, by Jérémy Couture, Head of SOC, Paris 2024 Olympic Games
- Trojan on an Attendee Laptop, by Ryan MacLennan
- Automated Account Provisioning, by Adi Sankar
- Integrating Meraki Scanning Data with Umbrella Security Events, by Christian Clasen
- Domain Name Service Statistics, by Adi Sankar
Integrating Security
As the needs of Black Hat evolved, so did the Cisco Secure Technologies in the NOC:
- Cisco SecureX: Extended Detection and Response actions / Automations
- Cisco Umbrella: DNS visibility and security
- Cisco Secure Malware Analytics (Formerly Threat Grid): for sandboxing and integrated threat intelligence
- Cisco Webex: for incident delivery and collaboration
- Cisco Security Connector: iOS device security and visibility, connected with Meraki Systems Manager
The SecureX dashboard made it easy to see the status of each of the connected Cisco Secure technologies.

Since joining the Black Hat NOC in 2016, my goal remains integration and automation. As a NOC team comprised of many technologies and companies, we are pleased that this Black Hat NOC was the most integrated to date, to provide an overall SOC cybersecurity architecture solution.
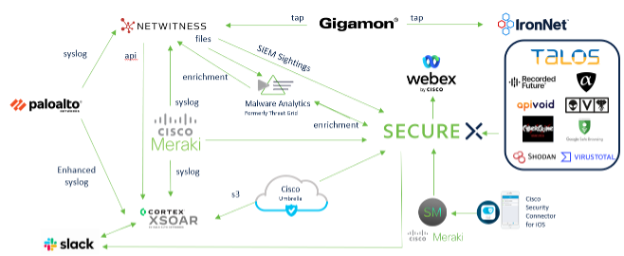
We have ideas for even more integrations for Black Hat Asia and Black Hat USA 2023. Thank you, Piotr Jarzynka, for designing the integration diagram.
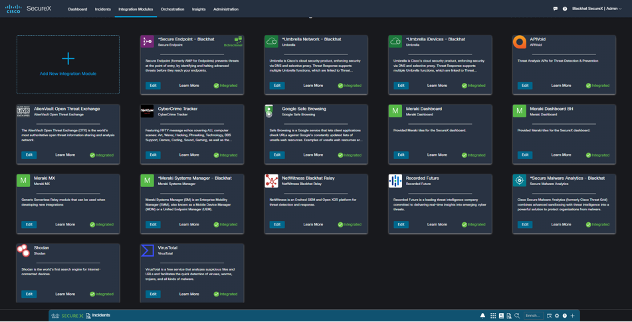
Below are the SecureX threat response integrations for Black Hat Europe, empowering analysts to investigate Indicators of Compromise very quickly, with one search.
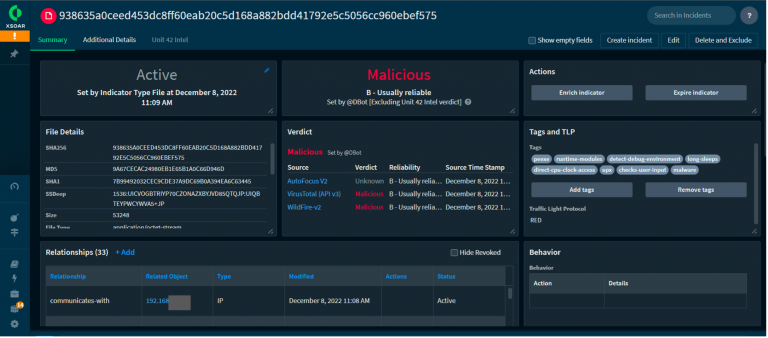
The original Black Hat NOC integration for Cisco was NetWitness sending suspicious files to Threat Grid (know Secure Malware Analytics). We expanded that in 2022 with Palo Alto Networks Cortex XSOAR and used it in London, for investigation of malicious payload attack.
NetWitness observed a targeted attack against the Black Hat network. The attack was intended to compromise the network.
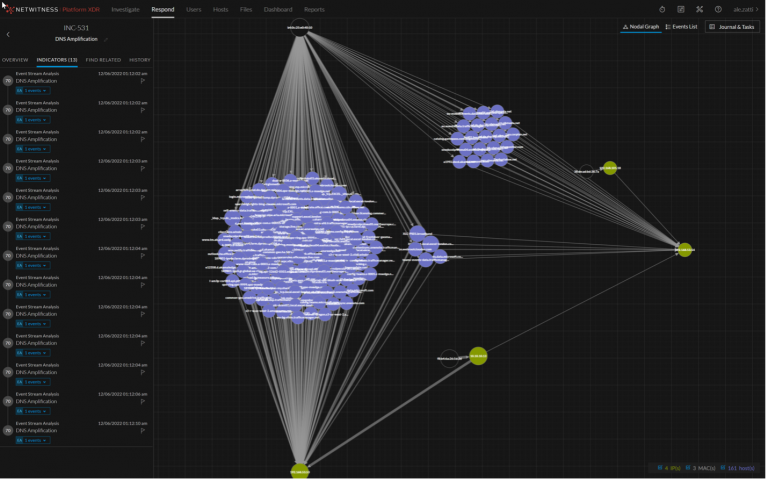
NetWitness extracted the payload and sent it to Secure Malware Analytics for detonation.

Reviewing the analysis report, we were able to quickly determine it was the MyDoom worm, which would have been very damaging.
The attack was blocked at the perimeter and the analysts were able to track and enrich the incident in XSOAR.
First Time at Black Hat, by Jérémy Couture, Head of SOC, Paris 2024 Olympic Games
My first time at Black Hat turned out to be an incredible journey!
Thanks to the cybersecurity partnership between Paris 2024 and Cisco, I was able to integrate into the Cisco Crew, to operate the NOC/SOC as a Threat Hunter on the most dangerous network in the world for this European Edition of Black Hat.
My first day, I helped with deploying the network by installing the wireless Meraki APs on the venue, understanding how they were configured and how they could help analysts to identify and locate any client connected to the network that could have a bad behavior during the event, the idea being to protect the attendees if an attack was to spray on the network.

Following this “physical” deployment, I’ve been able to access the whole Cisco Secure environment including Meraki, Secure Malware Analytics, Umbrella, SecureX and the other Black Hat NOC partners software tools.
SecureX was definitely the product on which I wanted to step up. By having so fantastic professionals around me, we were able to dig in the product, identifying potential use cases to deploy in the orchestration module and expected integrations for Paris 2024.

Time was flying and so were the attendees to the conference, a network without user is fun but can be quite boring as nothing happens, having so many cybersecurity professional at the same place testing different security malwares, attacks and so on led us to very interesting investigations. A paradox at the Black Hat, we do not want to block malicious content as it could be part of exercises or training classes, quite a different mindset as what we, security defenders, are used to! Using the different components, we were able to find some observables/IOCs that we investigate through SecureX, SecureX being connected to all the other components helped us to enrich the observables (IPs, urls, domains…), understanding the criticality of what we identified (such as malware payloads) and even led us to poke the folks in the training classes to let them know that something really wrong was happening on their devices.

Being part of the Black Hat NOC was an incredible experience, I was able to meet fantastic professionals, fully committed on making the event a success for all attendees and exhibitors. It also helped me to better understand how products, that we use or will use within Paris 2024, could be leveraged to our needs and which indicators could be added to our various Dashboards, helping us to identify, instantaneously, that something is happening.
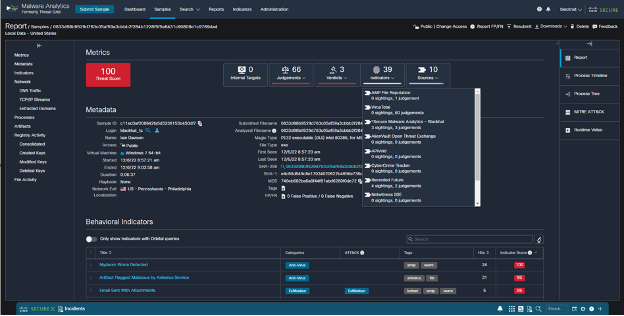
Trojan on an Attendee Laptop, by Ryan MacLennan
During the last day of Black Hat Europe, our NOC partner, NetWitness saw some files being downloaded on the network. The integration again automatically carved out the file and submitted the Cisco Secure Malware Analytics (SMA) platform. One of those files came back as a trojan, after SMA detonated the file in a sandbox environment. The specific hash is the below SHA-256:
938635a0ceed453dc8ff60eab20c5d168a882bdd41792e5c5056cc960ebef575
The screenshot below shows some of the behaviors that influenced the decision:
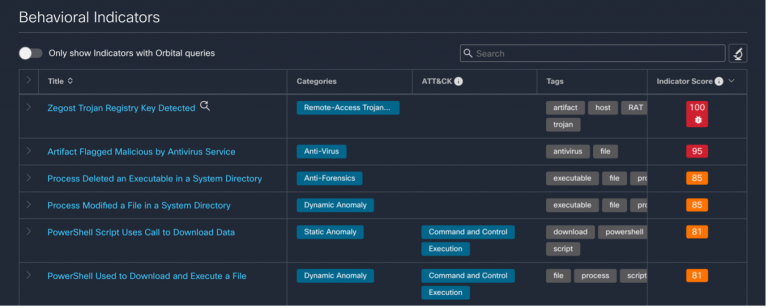
The result of seeing these behaviors caused SMA to give it the highest judgement score available to a detonated file:
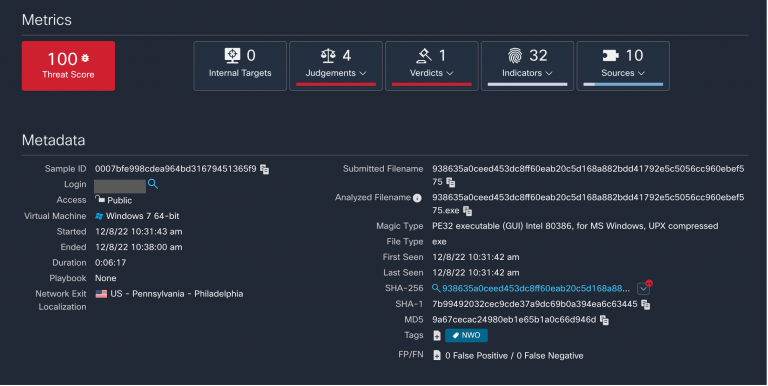
After this judgement was made, we connected with the Palo Alto Networks team, and they found the IP address associated with the file download.
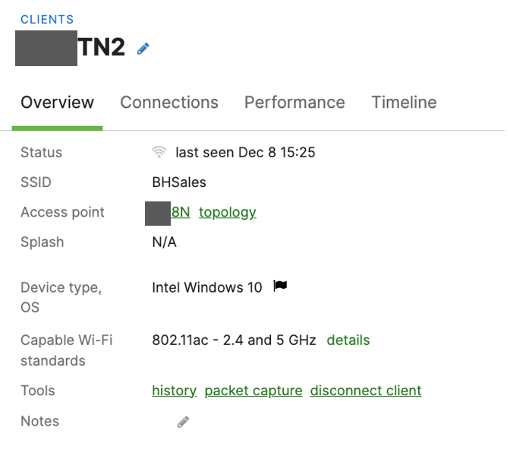
Once we had this information, we went to the Meraki dashboard and did a search for the IP address. The search returned only one client that has been associated with the address for the entire Black Hat conference.
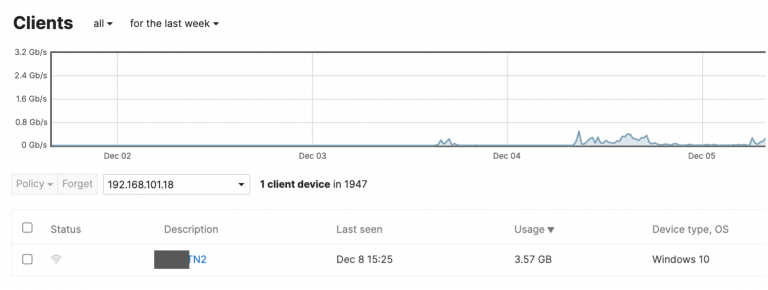
Knowing that there has only been one client associated with the address made finding the attendee easier. We then needed to know where they were and Meraki had this figured out. After opening the client’s profile, we saw what SSID and access point (AP) they were connected to using the Meraki location map.
We then found the attendee and let them know to have their IT inspect their laptop to make sure it is clean.
Apart from the technical challenges of running a temporary network for N thousand people, the Black Hat event reminded us that success doesn’t happen without teamwork; that leadership isn’t just about keeping the project on track. It is also about looking after the team and that small details in planning, build up and tear down can be just as important, as having all the right tools and fantastically skilled Individuals using them during the event itself.
Automated Account Provisioning, by Adi Sankar
In the Cisco Secure technology stack, within the Black Hat NOC, we use SecureX Single Sign-on. This reduces the confusion of managing multiple accounts and passwords. It also streamlines the integrations between the Cisco products and our fellow NOC partners. We have an open ecosystem approach to integrations and access in the NOC, so we will provision Cisco Secure accounts for any staff member of the NOC. Logging into each individual console and creating an account is time consuming and can often lead to confusion on which tools to provision and which permission levels are needed.
To automate this process, I developed two workflows: one to create non-admin users for NOC partners and one to create administrator accounts in all the tools for Cisco staff. The workflows create accounts in SecureX, Secure Malware Analytics (Threat Grid), Umbrella DNS and Meraki dashboard, all using SecureX Single Sign-On.
Here is what the workflow looks like for creating non-admin users.
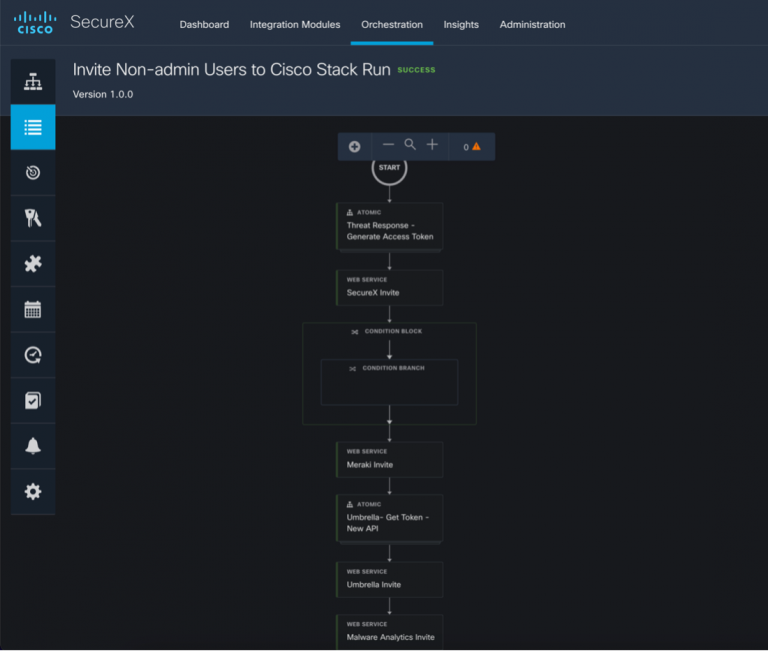
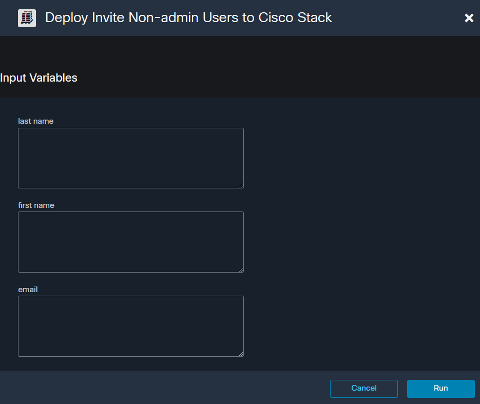
The workflow requires three inputs: first name, last name, and email. Click Run.
The sequence of API calls is as follows:
- Generate a SecureX token to access the SecureX API including the “admin/invite:write, invite:write” scopes.
- Invite the User to SecureX using the invite API (https://visibility.amp.cisco.com/iroh/invite/index.html#/). In the body of this POST the role is set to “user”. In the Administrator workflow this would be set to “admin” allowing full access to SecureX.
- If the invite fails due to a duplicate invite, print an error message in Webex teams.
- Invite the user to the Meraki dashboard using the “admins” API (https://api.meraki.com/api/v1/organizations/{organizationId}/admins). In the body of this call, the organization access is set to none, and access to two networks (Wireless network and Systems Manager) are set to “read-only” to ensure the user cannot make any changes to affect the network. In the Administrator version org access is still set to none but “full” permissions are provided to the two networks, something we do not want all users to have.
- Generate a token to the new Umbrella API using https://api.umbrella.com/auth/v2/token with the following scopes (read admin users, write admin users, read admin roles). This single endpoint for generating a token based on scopes has made using the Umbrella API significantly easier.
- Then invite the user to Umbrella using the “admins” API at (https://api.umbrella.com/admin/v2/users) and in the body of this POST the “role ID” is set to 2 to ensure read-only permissions are provisioned for Umbrella.
- Create a user in Secure Malware analytics using the API at (https://panacea.threatgrid.com/api/v3/organizations/<ORG_ID>/users). The body of this request simply creates a Malware Analytics login using the users last name and appending “_blackhat”
- The last call is to send a password reset email for the Malware Analytics user. (https://panacea.threatgrid.com/api/v3/users/<LOGIN>/password-email) They can set their password via the email, login to the Malware Analytics console and then link their SecureX sign-on account, which means they will no longer need to use their Malware Analytics credentials.
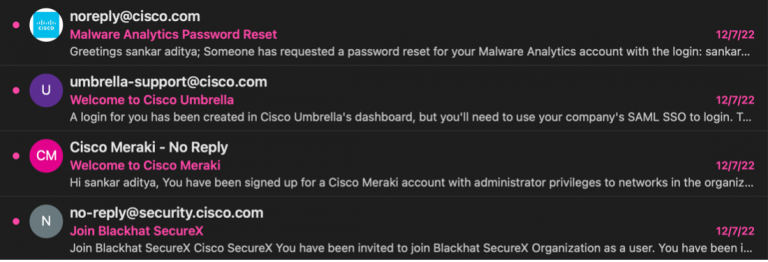
Once the workflow has completed successfully, the user will receive four emails to create a SecureX Sign-On account and accept the invitations to the various products. These workflows really improved our responsiveness to account provisioning requests and makes it much easier to collaborate with other NOC partners.
Integrating Meraki Scanning Data with Umbrella Security Events, by Christian Clasen
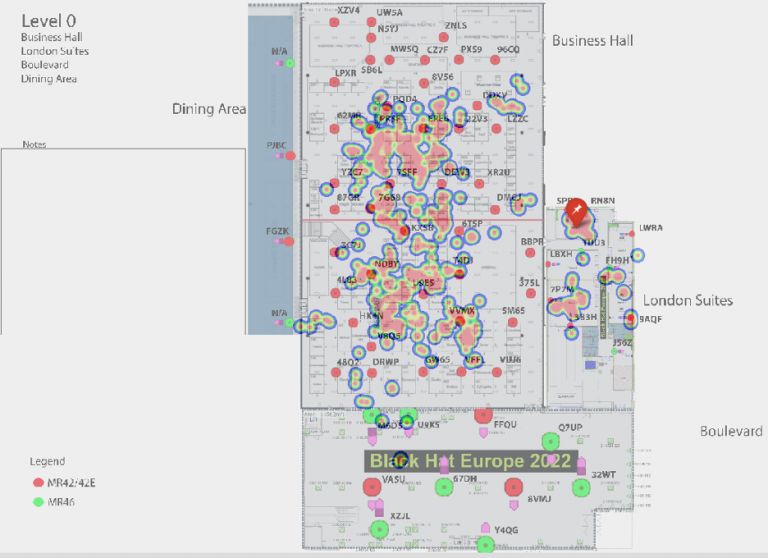
Over the previous Black Hat events, we have been utilizing Meraki scanning data to get location data for individual clients, as they roamed conference. In the initial blog post (Black Hat Asia 2022), we created a Docker container to accept the data from the Meraki Scanning API and save it for future analysis. At Black Hat USA 2022, we wrote about how to use Python Folium to use the flat text files to generate chronological heatmaps that illustrated the density of clients throughout the conference.
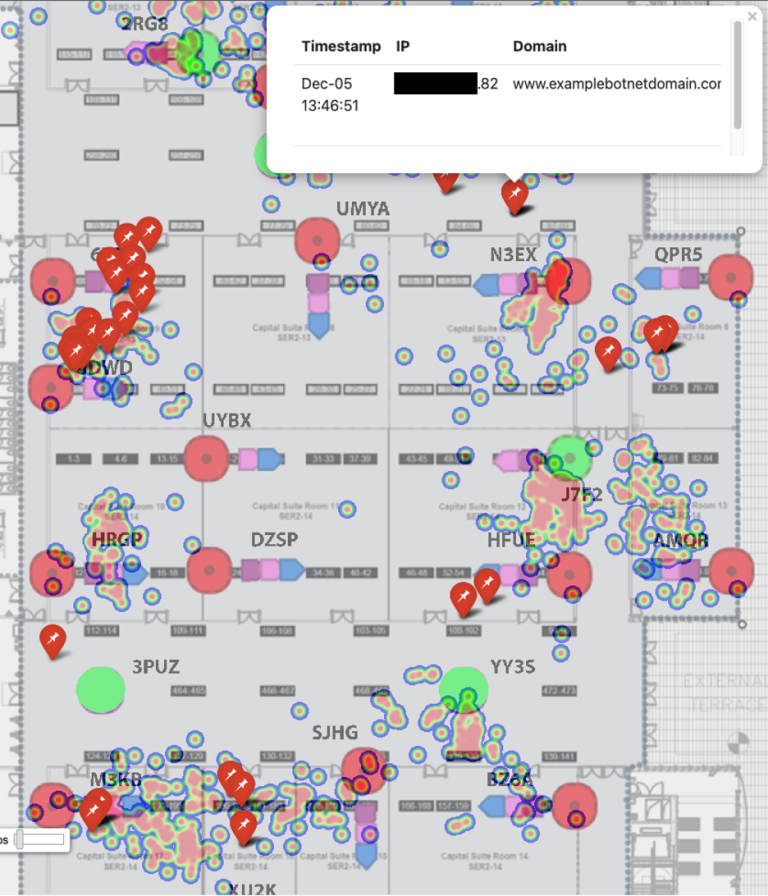
This time around, we’ve stepped it up again by integrating Umbrella DNS Security events and adding the ability to track clients across the heatmap using their local IP address.
To improve the portability of our data and the efficiency of our code, we began by moving from flat JSON files to a proper database. We chose SQLite this time around, though going forward we will likely use Mongo.
Both can be queried directly into Python Pandas dataframes which is what will give us the optimal performance we are looking for. We have a dedicated Docker container (Meraki-Receiver) that will validate the incoming data stream from the Meraki dashboard and insert the values into the database.
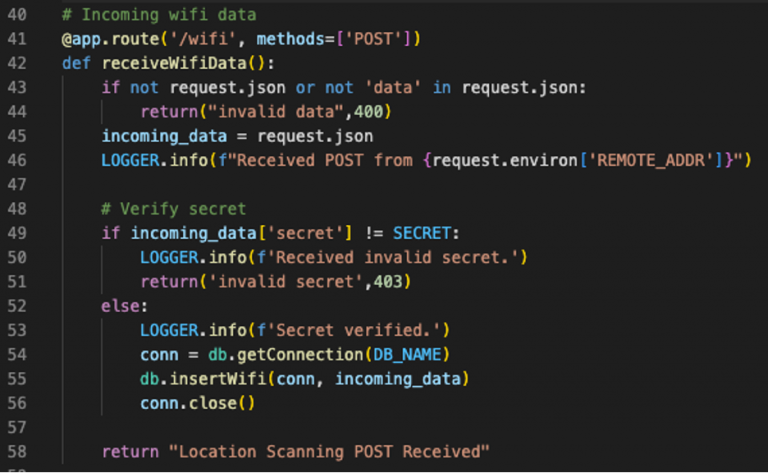
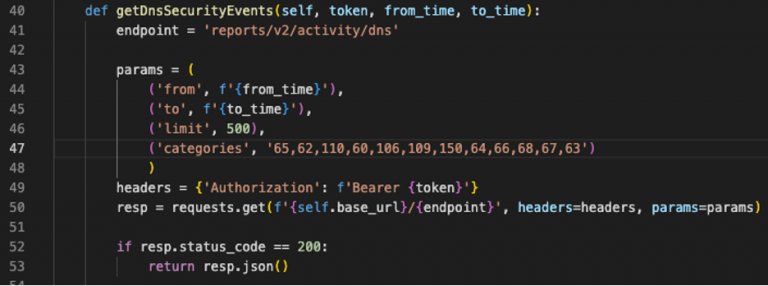
The database is stored on a Docker volume that can be mounted by our second container, the Meraki-Mapper. Though this container’s primary purpose is building the heatmaps, it also performs the task of retrieving and correlating Umbrella DNS security events. That is, any DNS query from the Black Hat network that matches one of several predefined security categories. Umbrella’s APIs were recently improved to add OAuth and simplify the URI scheme for each endpoint. After retrieving a token, we can get all security events in the time frame of the current heatmap with one call.
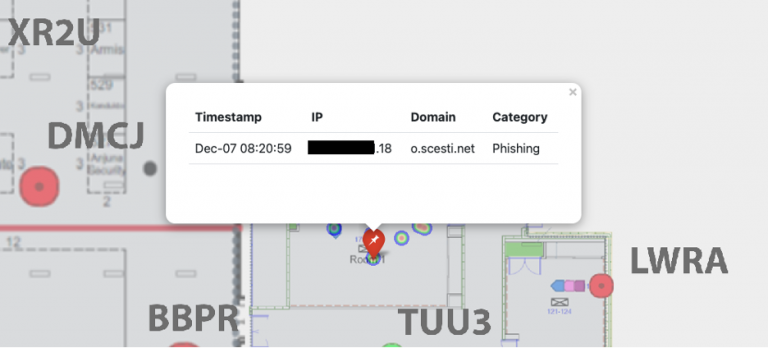
What we want to do with these events is to create Folium Markers. These are static “pins” that will sit on the map to indicate where the DNS query originated from. Clicking on a marker will popup more information about the query and the client who sent it.
Thanks to the Umbrella Virtual Appliances in the Black Hat network, we have the internal IP address of the client who sent the DNS query. We also have the internal IP address in the Meraki scanning data, along with the latitude and longitude. After converting the database query into a Pandas dataframe, our logic takes the IP address from the DNS query and finds all instances in the database of location data for that IP within a 5-minute window (the resolution of our heatmap).
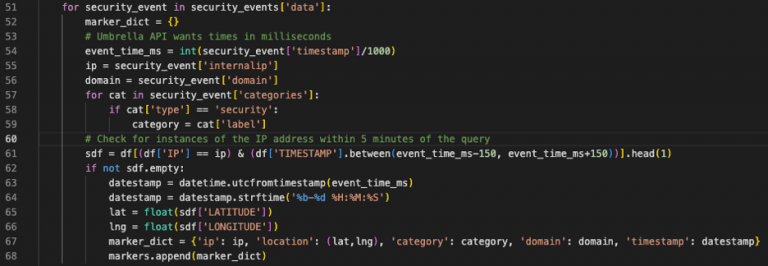
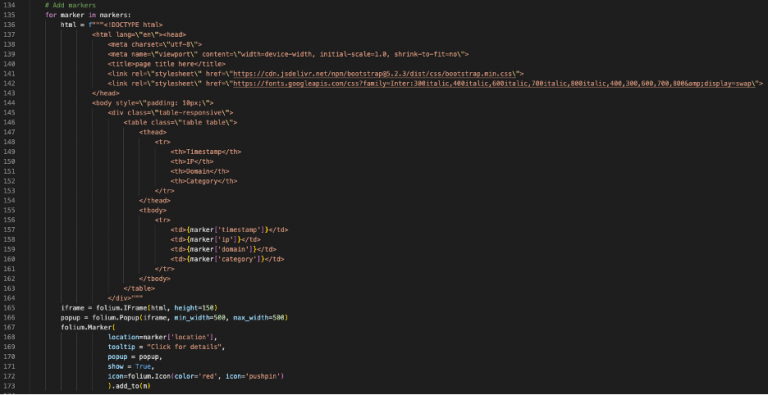
What we end up with is a list of dictionaries representing the markers we want to add to the map. Using Bootstrap, we can format the popup for each event to make it look a bit more polished. Folium’s Popup plugin allows for an iFrame for each marker popup.
The result is a moving heatmap covering an entire day on a given conference floor, complete with markers indicating security events (the red pushpin icon).
Clicking on the pushpin shows the details of the query, allowing us in the NOC to see the exact location of the client when they sent it.
To further improve this service during the next conference, we plan to implement a web page where NOC staff can submit an IP address and immediately get map tracking that client through the conference floor. This should give us an even more efficient way to find and notify folks who are either behaving maliciously or appear to be infected.
Domain Name Service Statistics, by Adi Sankar
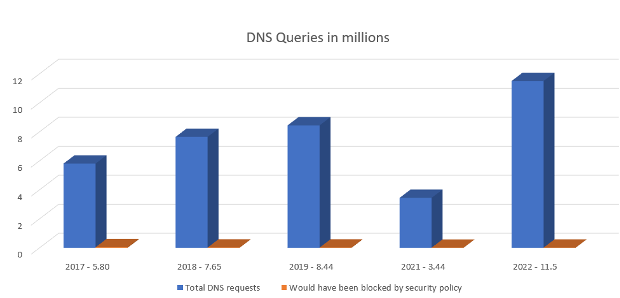
For years we have been tracking the DNS stats at the Blackhat conferences. The post-pandemic 2022 numbers look like we never skipped a beat after the dip in DNS queries from 2021, seen in the bar graph below. This year’s attendance saw well over 11 million total DNS queries.
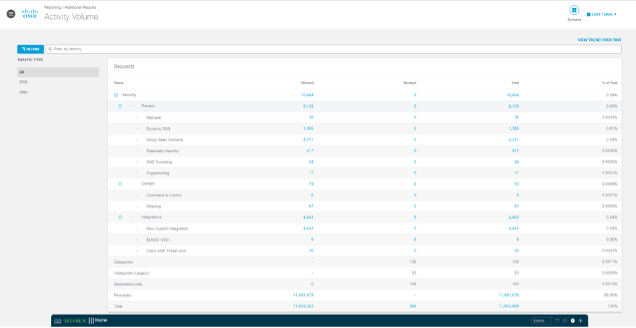
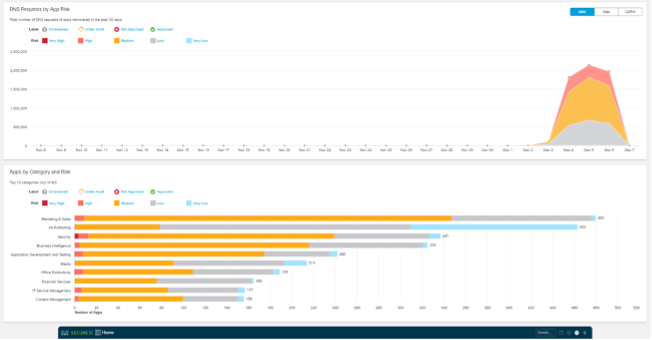
The Activity volume view from Umbrella gives a top-level level glance of activity by category, which we can drill into for deeper threat hunting. On trend with the previous Black Hat Europe events, the top Security categories were Dynamic DNS and Newly Seen Domains. However, it’s worth noting a proportionally larger increase in the cryptomining and phishing categories from 9 to 17 and 28 to 73, respectively, compared to last year.
These years, Black Hat saw over 4,100 apps connect to the network, which is nearly double of what was seen last year. However, still not topping over 6,100 apps seen at Black Hat USA early this year.
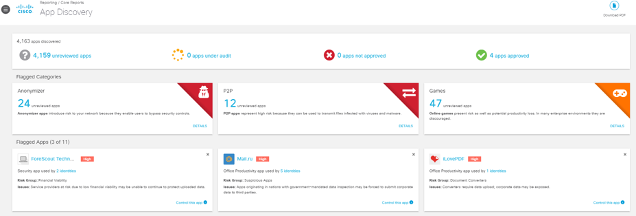
Should the need arise, we can block any application, such as Mail.ru above.
Black Hat Europe 2022 was the best planned and executed NOC in my experience, with the most integrations and visibility. This allowed us the time to deal with problems, which will always arise.
We are very proud of the collaboration of the team and the NOC partners.
Black Hat Asia will be in May 2023, at the Marina Bay Sands, Singapore…hope to see you there!
Acknowledgments
Thank you to the Cisco NOC team:
- Cisco Secure: Ian Redden, Christian Clasen, Aditya Sankar, Ryan MacLennan, Guillaume Buisson, Jerome Schneider, Robert Taylor, Piotr Jarzynka, Tim Wadhwa-Brown and Matthieu Sprunck
- Threat Hunter / Paris 2024 Olympics SOC: Jérémy Couture
- Meraki Network: Evan Basta, Sandro Fasser, Rossi Rosario Burgos, Otis Ioannou, Asmae Boutkhil, Jeffry Handal and Aleksandar Dimitrov Vladimirov
- Meraki Systems Manager: Paul Fidler
Also, to our NOC partners NetWitness (especially David Glover, Iain Davidson, Alessandro Contini and Alessandro Zatti), Palo Alto Networks (especially James Holland, Matt Ford, Matt Smith and Mathew Chase), Gigamon, IronNet, and the entire Black Hat / Informa Tech staff (especially Grifter ‘Neil Wyler’, Bart Stump, Steve Fink, James Pope, Jess Stafford and Steve Oldenbourg).

About Black Hat
For 25 years, Black Hat has provided attendees with the very latest in information security research, development, and trends. These high-profile global events and trainings are driven by the needs of the security community, striving to bring together the best minds in the industry. Black Hat inspires professionals at all career levels, encouraging growth and collaboration among academia, world-class researchers, and leaders in the public and private sectors. Black Hat Briefings and Trainings are held annually in the United States, Europe and USA. More information is available at: blackhat.com. Black Hat is brought to you by Informa Tech.
We’d love to hear what you think. Ask a Question, Comment Below, and Stay Connected with Cisco Secure on social!
Cisco Secure Social Channels





