This post was authored by Andrea Allievi & Earl Carter
Ransomware continues to impact a large number of organizations and the malware continues to evolve. In January, we examined Cryptowall 2.0 and highlighted new features incorporated into the dropper and Cryptowall binary. When Cryptowall 3.0 appeared, we were interested in seeing what new functionality was incorporated into this latest variant in the Cryptowall series.
The latest 3.0 sample that we analyzed was in a zip file. This zip file contains multiple dropper files which are essentially identical in functionality except for the encryption algorithm used to obfuscate the dropper and eventually build the Cryptowall 3.0 binary.
Similar to the 2.0 version, the dropper is encrypted with a custom algorithm three times, but that is where the similarities end. In the 3.0 sample that we analyzed, the following dropper features (which we identified as being operational in version 2.0) have been removed:
- Switching between 32 and 64 bit operation
- Employing multiple exploits in the dropper
- Anti-VM check to prevent running in virtual environment
Examining the dropper in the 3.0 sample indicates that it includes a lot of useless API calls and dead code. Apparently the dropper for this version of Cryptowall has been streamlined. The lack of any exploits in the dropper seems to indicate that the malware authors are focusing more on using exploit kits as an attack vector, since the exploit kit’s functionality could be used to gain privilege escalation on the system. Without privilege escalation, attempting to turn off many enabled security features on the system is likely to fail.
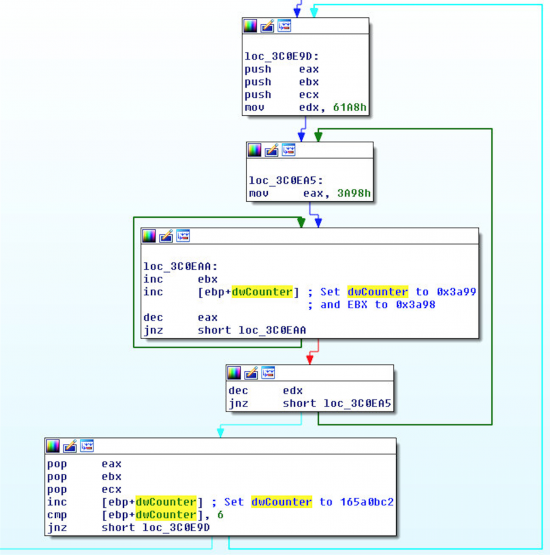
Constructing the Unencrypted Cryptowall Binary
During the first decryption stage, the dropper reads its encrypted code, decrypts and stores it at RVA 0x1B9E0A0 (in the data section). The second stage decryption code begins by locating the byte pattern (0x35, 0x5e, 0x74) inside its “.data” section. Once this location is identified, it starts decrypting the data following that marker directly onto the stack. Finally, the third stage begins by transferring execution to the unencrypted code that was placed on the stack. During this third stage, the code builds the small IAT (more or less 30 APIs) that is needed to extract and decrypt the BASE64-encoded resource (ID 62) placed inside the “Message Tables” group. The resource is decoded and then decrypted. The decrypted resource is a file that contains the last encryption stage code.
The last stage builds another IAT, cycles between all running processes trying to find out if its own process name is “perl.exe” or “python.exe”. If the check indicates that the parent process name is “perl.exe” or “python.exe”, then the program runs the following endless loop and never runs the Cryptowall 3.0 code.
If the parent process is not “perl.exe” of “python.exe”, the encrypted code inside the resource (that is actual a PE file) is decrypted into an external buffer; a process is created in a suspended state (backed by the original packed executable) and the same trick used in the CryptoWall 2.0 is employed to inject the clean PE inside the suspended process (ZwUnmapViewOfSection / VirtualAllocEx / WriteProcessMemory). Finally the execution control is released to the clean CryptoWall 3.0 Code.
Cryptowall 3.0 Analysis
The CryptoWall 3.0 initialization code is the same as the previous version of the infection: a big IAT is built and the code is injected in a new spawned “explorer.exe”. The code located in the “explorer.exe” process installs Cryptowall 3.0 in the target system in exactly the same manner as the previous version (“Run” / “RunOnce” registry keys and “Startup” start menu folder). Finally all the system protections (and all System volume shadow images) are disabled and the code is injected in a new spawned “svchost.exe” process.
Main SVCHOST Code
The code injected inside the “Svchost.exe” process implements the main malware functionality. It starts building the large IAT and creating the main event. Cryptowall 3.0 acquires a lot of system information (like the computer name, main processor speed and type, and so on…) and generates a global MD5 used as Victim ID. One of the new feature of CryptoWall 3.0 is the usage of I2P network. The dropper generates its I2P network proxy and Url lists. In the dropper we have analysed, we found the following I2P CryptoWall Urls:
proxy1-1-1.i2p
proxy2-2-2.i2p
proxy3-3-3.i2p
proxy4-4-4.i2p
proxy5-5-5.i2p
Cryptowall registers the victim workstation to its Command & Control server: a request string is generated in the following format:
{<Request ID>|crypt1|<Victim PC MD5>|<OS Ver Index>..||External Ip Address}
To obtain the external Ip Address, Cryptowall 3.0 uses the same algorithm seen in its previous version. This string is encoded for the I2P network, and it is sent through an I2P Proxy. The included I2P proxy list contains the following addresses:
91.121.12.127:4141
5.199.165.160:8080
94.247.28.26:2525
194.58.109.158:2525
195.29.106.157:4444
94.247.31.19:8080
194.58.109.137:3435
94.247.28.156:8081
209.148.85.151:8080
Here is an example of Cryptowall Command & Control server registration string with a request ID of 1:
{1|crypt1|9831374BF569D58A8BED493DF407F4EF|5|1|2||5.170.247.119}
The CryptoWall 3.0 dropper tests each Proxy address, searching for the live ones. The connection will be established to the target I2P Url through the chosen proxy. A POST request is made, containing the encoded request string. The Command & Control server answers with a 3 digit ID. The ID is verified, and if all has gone fine, the dropper spawns the Main CryptoWall Thread.
THE MAIN CRYPTOWALL THREAD
The main CryptoWall thread initializes the Windows Crypto functions and creates the main registry key: “HKCU\<Victim Pc MD5>”. It tries to acquire the Public key for the later files encryption, using another well-formed Command & Control Message (ID 7):
{7|crypt1|<Victim PC MD5>|1}
The Received public key is verified and imported in the Windows Cryptographic Provider using the “CryptImportPublicKeyInfo” API. The text version of the public key is stored in the registry, by a registry value name generated by a Cryptowall routine, using index 2 (the actual value name is calculated starting from the Victim PC MD5). The hash of the public key is used by the bad guys to generate the “User personal code”.
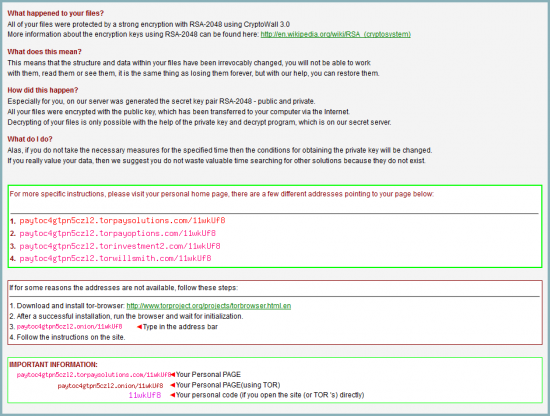
The hash of the public key is also calculated and used to retrieve the CryptoWall PNG wallpaper, and to compile the “Decrypt Instruction” files. These instructions are based on the geolocation of the hosts IP address. This means that the instructions should hopefully appear in the native language of the user of the computer.
When the PNG Wallpaper has been correctly downloaded, it is stored in the registry value with index 5. Even the decrypt instructions files are generated and saved on disk.
Finally the code cycles between all the mounted volumes (obtained using “GetLogicalDriveStrings” API), and spawn one CryptoWall Encryption thread for each volume that is not an optical drive.
IOCs
Cryptowall 3.0.zip hash –
(sha256: 838e19ff3f52952c292f945054520eb5707c80a389b1f88770b1ccc09f966c65).
Dropper 1 hash –
(sha256: 9e06d2ce0741e039311261acc3d3acbaba12e02af8a8f163be926ca90230fa89)
Dropper 2 hash –
(sha256: 55e866cc8580e5f9f7f6560e478f3b37b3362e9f94e88439beef6026c86c80be)
Dropper 3 hash –
(sha256: 45317968759d3e37282ceb75149f627d648534c5b4685f6da3966d8f6fca662d)
I2P Proxy Addresses:
91.121.12.127:4141
5.199.165.160:8080
94.247.28.26:2525
194.58.109.158:2525
195.29.106.157:4444
94.247.31.19:8080
194.58.109.137:3435
94.247.28.156:8081
209.148.85.151:8080
CONCLUSION
The dropper we analyzed is much more streamlined in functionality. Many of the dropper features deployed in Cryptowall 2.0 are no longer present in the 3.0 sample. New functionality has also been added, such as incorporating I2P network communication. Ransomware variants continue to try to improve the stealth of their network communications using networks such as TOR and I2P.
Identifying and stopping ransomware variants definitely requires a layered security approach. Breaking any step in the attack chain will successfully prevent this attack. Therefore, blocking the initial phishing emails, blocking network connections to known malicious content, as well as stopping malicious process activity are critical to combating ransomware and preventing it from holding your data hostage.
Establishing a solid backup and restore policy is also crucial to overcoming attacks to your data, whether they occur from natural disasters, such as a storm, or whether they occur from a malicious attack across the network. Many companies believed they had a solid backup plan only to find the malware encrypted the backup to prevent them from restoring any data. It is imperative to adhere to industry wide best practices which include making sure that you backup copies are safe from both physical destruction, as well as corruption from viruses and other malicious software.
Protecting Users from These Threats
Advanced Malware Protection (AMP) is ideally suited to prevent the execution of the malware used by these threat actors.
CWS or WSA web scanning prevents access to malicious websites used in these types of attacks.
The Network Security protection of IPS and NGFW have up-to-date signatures to detect malicious network activity by threat actors.
ESA can block spear phishing emails sent by threat actors as part of their campaign.






Excellent analysis guys! keep up the good work.
excelente informacion, muy bien documentada.
so what can be done to remove the infection?
Hi!
Thanks everybody for the compliments. This analysis is small because we would like to highlight that the new CryptoWall 3 dropper has lost many interesting features…
To correctly remove the infection a simple deletion of all CryptoWall entries located in the following places is enough:
– HKCU\Software\Microsoft\Windows\CurrentVersion\Run
– HKCU\Software\Microsoft\Windows\CurrentVersion\RunOnce
– The executables located in the Startup folder of the start menù
– All the CryptoWall 3.0 generated files located in each encrypted folder
Unfortunately after the infection has encrypted the user files, there is no easy way to decrypt them, because the Private Key is located inside the Bad guys servers.
Are there specific names we can look for in those registry entries or file names in the startup folder? Or does it generate a random name?
I suppose you could create a PowerShell Scheduled Task with a whitelist of names that are allowed to be there. Then anything that pops up could generate an email or alert.
Is there a way to recover the files? I dont have any backups or restore option for files enabled.
Please help!!
If and Enterprise were to try and block I2p protocal/network, how would that effectively be achomplished?
The I2P proxy on 91.121.12[.]127 was taken down by OVH.
Thats great and all but is there a chance a decryptor would come out? Can I put my hard drive in my safe and wait 10 years?
Yes, that’s my question, too! Any hope at all of flaws? Is it still too early or is it hopeless?
Is it reasonable to expect that program for decryption will appear? I’m a patient man…
Nice article Andrea!
Can it be removed from a flash drive? It appears like these bandits infected a flashdrive I was using as well as most of my files on the laptop.
If an “Individual or individuals” has the time to create this issue. What power does an entire network of IT experts and businesses have against the one or ones who created this ransomware encryption….
Who wants to be first to team up and solve the issue and take the credit for that solution!? The great part to seeing this well written blog here is that it’s not from an Antivirus company. Also other sites out there that offer online decryption for Cryptolocker, why not Cryptowall 3.0???
https://www.fireeye.com/blog/executive-perspective/2014/08/your-locker-of-information-for-cryptolocker-decryption.html
Currently there is no known way to decrypt the files encrypted by Cryptowall. You may notice that there is a tool to decrypt CryptoLocker files. They did not break the decryption on CryptoLocker. When law enforcement took down CryptoLocker, they confiscated the hard drives and amassed a list of potential encryption keys. So in reality, you submit an encrypted file to the decryption tool and it searches through the keys looking for the one that correctly decrypts the file. Without having gained access to the original keys, there would not be a tool to decrypt the CryptoLocker files.
I have worked on this malware a bit. It is true that we cannot decrypt… but there are work arounds to retrieving your files… check out shadow explorer and learn to browse individual system restore checkpoints for unencrypted versions of your files. I have helped a few customers get their files back this way.
What about WinXP?
you’re joking right?
Rich,
I have been infected by CryptWall 3.0 and according to it, can’t access anything. Any information you can give me to get some help with this situation to retrieve my files would be greately appreciated. I included my email account and I don’t want to touch the computer any more than I have to to try to remove and retrieve the encrypted files. They are my life.
Thanks, Graig for explaining this!
Hello,
Just wanted to share what worked for me…after removing the virus I found information about a possible fix…shadowexplorer…so far this is working very well. I am able to export earlier “shadow” saved versions of the files that are not encrypted at all!
Jack I would like more information on how you did this. I’ve been infected and have my life on my computer. My email is mariewlock@gmail.com.
I have had my NAS and my backups encrypted with Cryptowall 3.0 recently. I have paid the ransom and received the keys. I ran the decrypter and it seemed to be going great but it completed way too quick and when I went to run it again, it just completes and nothing is decrypted. There are 15 years of photos including that of my three children growing up. The computer that was infected has been blown away due to the fact that nothing on it was of any value – everything we value is on the NAS.
I have tried looking for shadow copies and anything else I can think of. I’ve just about lost hope. If anyone has any idea how I can decrypt these files, I would be indebted to them.
***Just to reiterate – I have the keys and decrypter***
One way to try and access the infomation is to run a portable linux os from thumb drive. Its how I repair windows operating systems. its something you can try?
Please sendme the decrypt soft and key. I will try help you.
Hi there. We have been hit by the Cryptowall virus. Decrypt key didn’t work for us. Any ideas most gratefully received.
Many thanks
Nicola
How are you doing?
I have a decryptor that works fine, you can select folders to decrypt yourself.
If you have your public/private keypair this one should do it.
if you give me your email, I can try to help you out.
Hi there. Reading this with interest as we had Cryptowall 3 last week, paid ransom and decrypt key hasn’t worked. Any ideas or help gratefully received.
Nicola
In exploring a cryptowall 23 infected PC I found a file that listed every encrypted file. If your mapped drive letter changed this database might be pointing to the wrong drive now that things have changed. The decryption should have been run on the infected machine before any removal action is taken.
I had a friend recover the deleted copies of the encrypted files using a “undelete” tool…the name escapes me. His was a 2.0 infection. I tried using GetDataBack on a 3.0 infection today without much luck. I got some files that had been deleted before the infection but nothing that could be called complete.
Why are the bad guys always smarter than the good guys?
Excellent research on how it attacks and how it encrypts but are no good smart guys to come up with some decryption software??
They aren’t, it’s just that the bad guys have the element of surprise, you have to know about an infection before it can be noticed and removed. To decrypt the files you normally have to have the key, and each key is unique to the computer that was infected( From what I understand about the infection anyway).
Has anyone paid the ransom and giot the keys and actually got all files back?
We have had to deal with this several times with our clients, four to be exact. Each time, the computer that got hit had critical data that was stored locally. We paid the ransom and received the key that decrypted all the files.
How long before they gave access to the decyrptor?
Its not that the bad guys are smarter its because people are always whining of things like increased security so Microsoft says OK here is a way to encrypt files on your personal PC using unbreakable encryption, then the bad guys say “Wow really? You practically just dumped that one in our hands”, invention Cryptowall is born.
It will be the same with those new super secure Android phone variants, someone will use the technology in the phone against the user and completely brick it.
I don’t understand why people need to encrypt their files on their PC anyway, seriously your that worried someone will get into your excel sheet of possible cat names? No one cares about your secret chili recipe I swear and everyone looks at porn.
The latest version removes the system restore points and shadow copies so unless you have a backup you’re in trouble.
So, I’m running CryptoPrevent but having read this I’m wondering — given that it’s possible to derive the Victime ID/registry key that CryptoWall3 would use, is it possible to create a dummy registry key and make it immutable to prevent infection? i.e. would the installation terminate before encryption if unable to create or modify the registy key?
Or else, is it prudent/possible to monitor the registry for changes and force shutdown if the telltale registry key appears and/or is changed from dummy values?
Where are these bastards physically located?
If I have the 2048-bit private key (paid to get it), is there a way to decrypt the files using windows’ own or another trusted encryption/decryption tool? Ideally I’d like a powershell script I can point at the privatekey, a manafest of encrypted files, and let it call windows’ own CryptUnprotectData() to decrypt and replace the encrypted file (or create a clean copy). Please help with suggetions if I already have the private key -Thanks
I was infected by CryptoWall 2.0 last year on my office laptop. Luckily, our network was not infected at the time. I paid the ransom and was able to retrieve 99% of my files with the exception of a few Outlook .pst files. I now pay Backblaze annually to run a continuous backup of everything on my hard drive that is personal in nature. This gives me great piece of mind. Little did I know that although my files were restored, the date and time stamp information that tells me when the files were created or last modified was lost after decryption. The bad guys don’t tell you this. So, my ability to sort and find files based on date and time is no longer an option with the retired files. Having daily back-ups is the way to go. Fast forward 1 year and someone within our company notice today that CryptoWall 3.0 had found it’s way to our network server. Luckily, our IT guys complete daily back-ups that are not infected. The cost of lost productivity across the globe due to this virus is immeasurable.
hello friends blogs.cisco.com:
I’ve been trying to find the decrypt.zip file, which contains the Decrypt.exe and keys.
Any attempt to find a solution could come to investigate these files, 03 files statistically decrypt.zip would be needed.
I request your files having decrypt.zip send it to me at my e thomas.paine333@gmail.com indicating if cryptowall 1,2 or 3.
Should you find any solution no doubt that the’ll do arrive.
thanks for the help
The Cryptowall 3.0 versions that I’ve seen so far (newest being from early March) can’t deleted System Restore points if UAC is enabled at any level.
Can anyone actually confirm that the newest versions will delete the SR points even if UAC is in place?
Just reinstalled OS for one of my friends. PC was infected with Cryptowall 3.0. Installed brand new HDD and 2 days later he is telling me that he gets the same message pop up on his screen to decrypt. I just wonder, Is it possible to get virus back without user interaction with firewall and updated antivirus installed? Thank you.
Hello my computer has been infected with Cryptowall 3.0 and I would like to know if somebody knows how to descrypt files. I also speaks Spanish and French. Thank you very much for your help.
Hi guys, I got infected 3 weeks back and I have decided to pay the ransom now. I was not able to open the one file that they have decrypted for free. Still I am trying my last chance by paying the ransom. Can anybody confirm if the payment works or not?