Written by Evgeny Mirolyubov, Ben Greenbaum, Jesse Munos on behalf of the AMP for Endpoints engineering and research team
The AMP for Endpoints engineering and research team continuously releases new features and capabilities in the AMP for Endpoints Console with the goal of providing a superior user experience while addressing feedback from customers, partners, and prospects. But it doesn’t stop there. That same team also invests a lot of time and effort into continually improving the security efficacy of the product. These improvements often come in the form of new security engines and capabilities.
In short, the team is tireless, working 24/7 to ensure business continuity for our customers. This blog highlights some of the enhancements that were made available in the last quarter.
Device Trajectory version 2
One of the critical prerequisites for effective incident response and threat hunting is in-depth historical endpoint visibility and comprehensive data collection. The Device Trajectory feature of AMP for Endpoints has been delivering these capabilities for years now. Most recently we have run through multiple iterations to improve its performance, data representation, and usability even further. Customers are now able to locate spikes in endpoint activity easily (representing an increase in network or file activity), precisely identify and double-click on compromises using the improved timeline feature, and enjoy enhanced activity filter customization. Performance improvements are achieved by loading the data on demand as you scroll through the timeline allowing access to a full 30 days of historical data. On top of that, the new Device Trajectory shows a more in-depth view of the endpoint; you can now see the full relationship mappings between clean processes and files.
New search capabilities are now available as well (not reflected in the video above). If you are an AMP for Endpoints user, you can experience the new Device Trajectory by enrolling into a public beta (navigate to Management -> Beta Features in the AMP Console). We sincerely thank our customers and partners for their valuable feedback provided during the open beta.
Threat Severity
When understanding and prioritizing alerts becomes a challenge, high-impact threats can be left without proper attention. The new threat severity feature was introduced to help security teams make better-informed incident triage and response decisions. Sorting by severity brings the most severe compromises to the top of your AMP Console Inbox. Related events now have associated severity tags (Critical, High, Medium, Low) and corresponding color-coding. The tags are assigned by Cisco’s research team based on the global threat landscape knowledge and are continuously tuned to maintain a high level of accuracy. Critical severity level represents incidents involving known malware families identified with very high precision (for example, Cloud IOCs signifying that Poweliks infection has been identified post-compromised). High severity tag can be assigned to incidents representing generic malicious behaviors and generic malware, not attributed to a particular family (for example, ‘Executed Malware’ events). And finally, Medium and Low severity levels are reserved for possibly malicious or risky detections, that could indicate about a potential compromise or degraded security posture (for example, ‘Threat Detected’ or ‘Vulnerable Application Detected’ events).
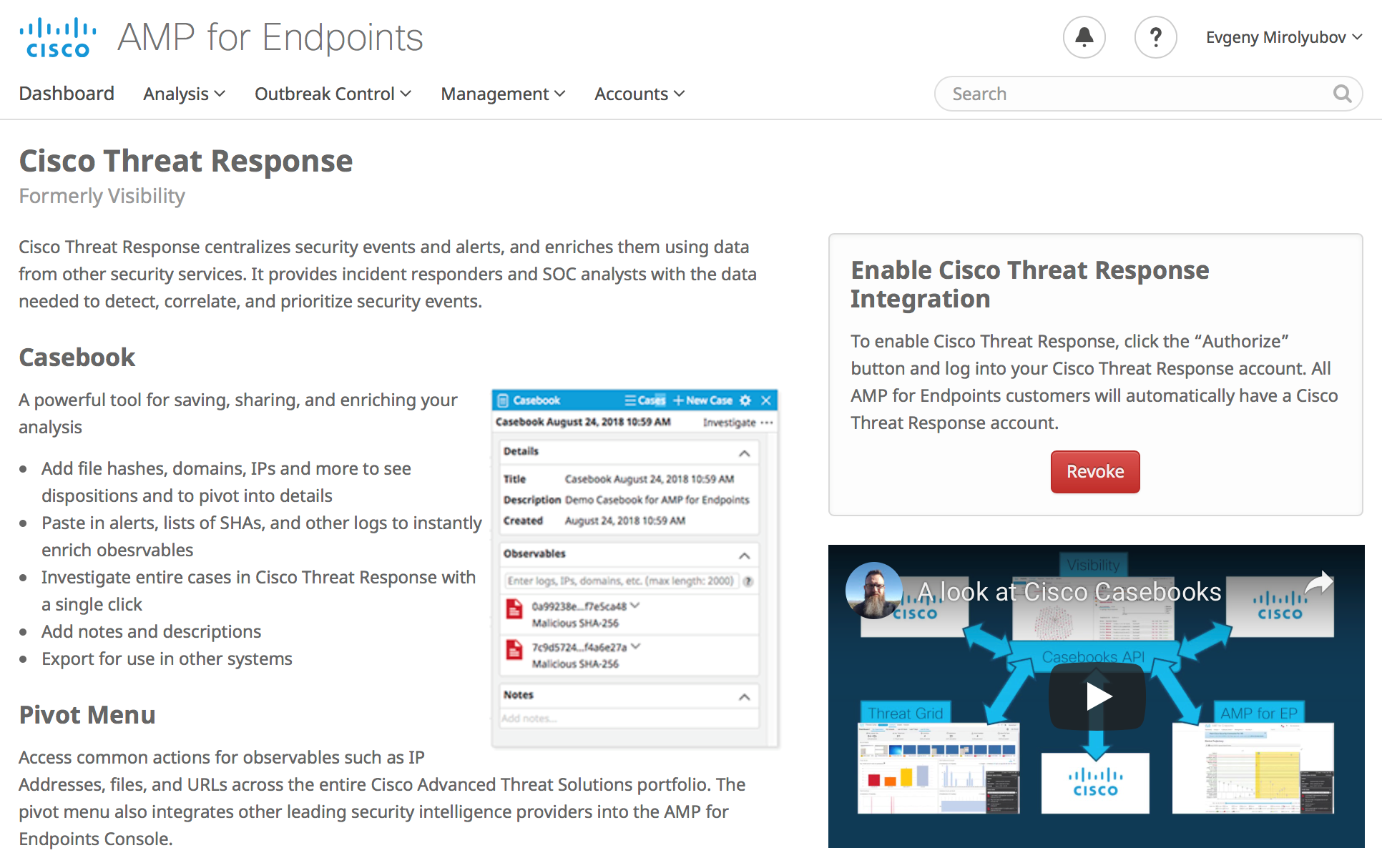
Casebook and Pivot Menus
The daily workflows can be significantly optimized through the integrated case management tool named “Casebook”. This is a powerful tool for gathering and pivoting on observables, assigning names to investigations, taking notes, and much more. Casebook and the pivot menus allow you to execute common actions for observables such as IP addresses, files, and URLs across the entire Cisco Advanced Threat Solutions portfolio from pretty much anywhere in the AMP Console. As a result, it provides enhanced user experience through tighter integrations. This feature is made possible by Cisco Threat Response, our new integration platform that helps you increase the efficiency and effectiveness of your existing Cisco Security investments. You can enable Casebooks and Pivot Menus under your AMP for Endpoints account settings.
New Overview Page
What could be more powerful for the business leaders than seeing the real-time value of their investments? The new Overview Page is designed to serve as a visual representation, that gives executives a quick and easy way to view their endpoint security state. Such information allows executives and security staff an “At A Glance” view of critical security metrics. The color-coded indicators provide an easy to parse summary of threats, compromises, vulnerabilities, and more while simultaneously allowing users to rapidly pivot into specific areas of interest.
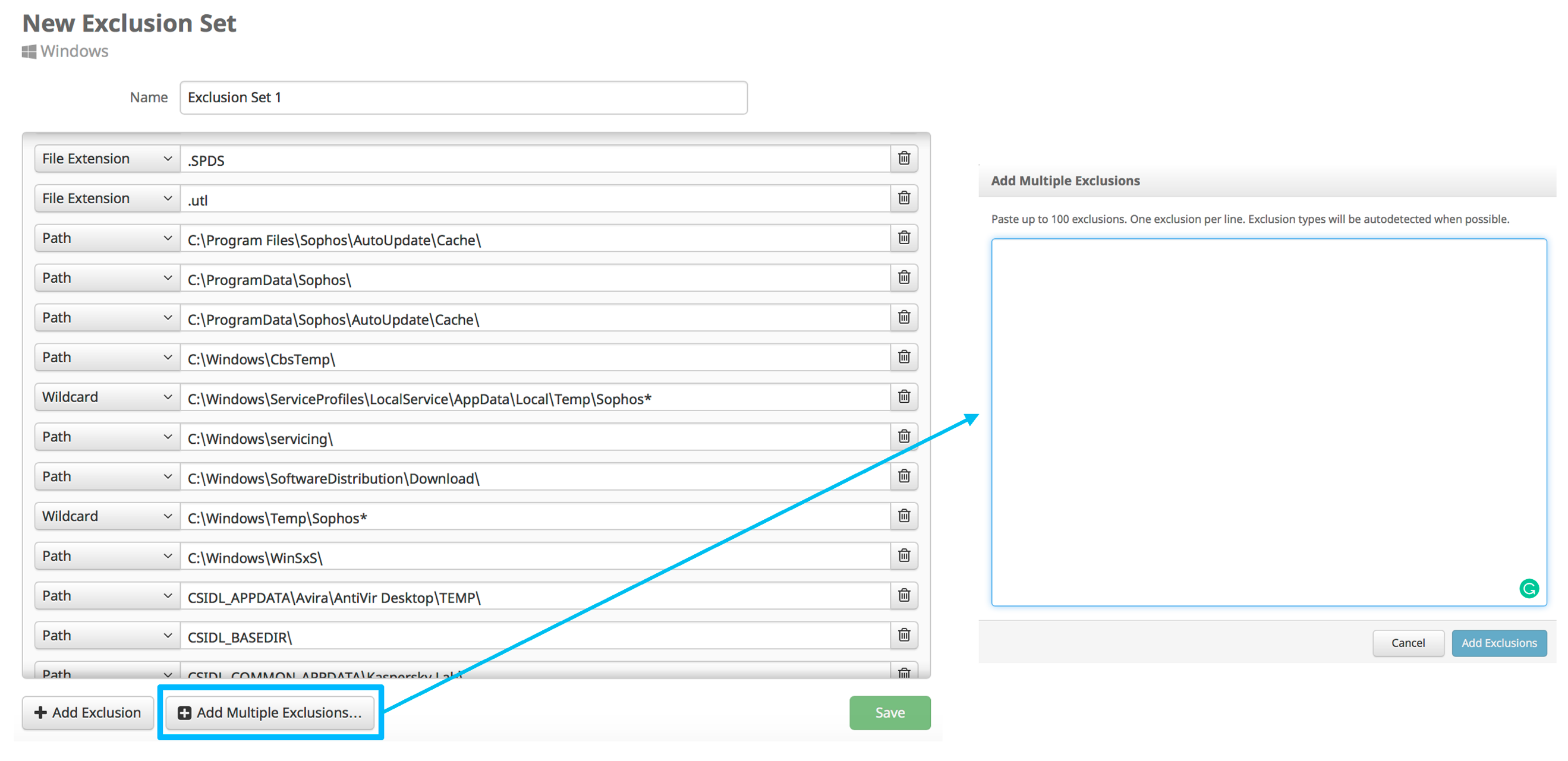
New Exclusions User Interface
An exclusion set is a list of directories, file extensions, processes, or threat names that won’t be scanned or convicted by the AMP Connector (or other endpoint security products). Sometimes exclusions are necessary to ensure a healthy balance of performance and security on an endpoint system. The key is that exclusions often need to be uniquely tailored to each customer environment based on business needs and security policies. The AMP for Endpoints engineering team has recently updated the user interface of the Exclusions configuration page to bring it to a consistent look and feel in line with the rest of the interface. Additionally, AMP Console administrators are now able to apply multiple Exclusion Lists to a single policy. Although the user interface has changed, the functionality of Exclusions stays fundamentally the same.
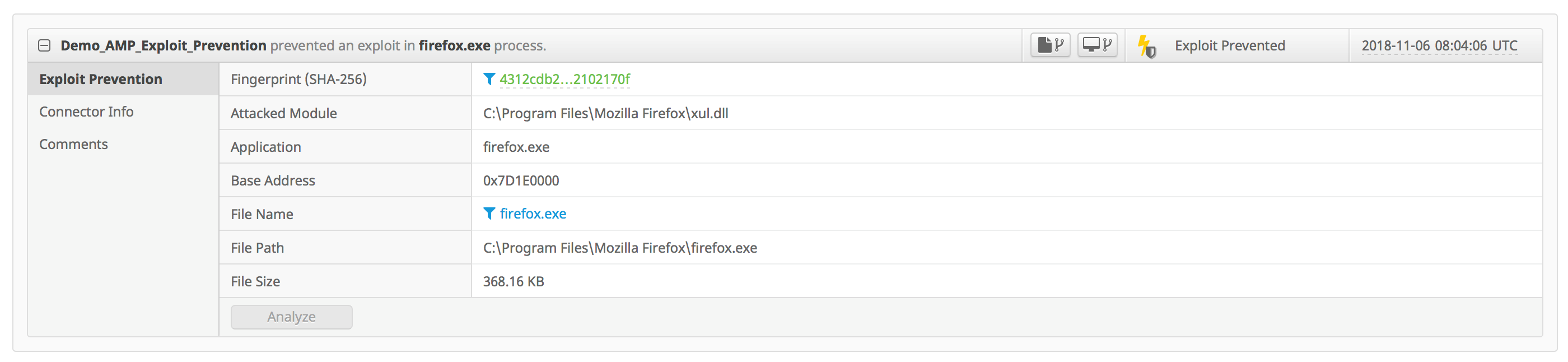
Exploit Prevention Enhancements
Strong prevention capability is one of the most highly-desired building blocks of any endpoint security offering. That may include preventing exploits (0-day or against unpatched vulnerabilities), evasive malware, and file-less attacks, all without relying on rules or signatures for detection. The Exploit Prevention engine, first introduced in AMP for Endpoints with the AMP Windows Connector version 6.0.5, has been enhanced to provide greater coverage against the evolving threat landscape. It does so by applying a truly proactive prevention technology, that does not affect system performance or imply compatibility issues. The ease of enabling Exploit Prevention and the value it provides has led to the rapid adoption, and we strive to continue improving the protection levels. Check back soon for a technical whitepaper on that strong prevention capability.
Сross-Layer Analytics
The value of leveraging machine learning in endpoint security is apparent. It should be clarified however, that machine learning is a part of the solution to the problem, not the solution itself. At Cisco, we achieve the best efficacy through what we call Cross-Layer Analytics, which is a combination of multiple algorithms to process diverse sets of data from both endpoint and network. One example of how it is done is by associating the process hashes and associated command line arguments used during binary execution with network communication and destination servers. That drives higher catch rates for detection of novel variants of polymorphic malware without reliance on static or dynamic analysis techniques (which have their benefits and drawbacks). The threat knowledge produced by Cross-Layer Analytics is then automatically fed back into the threat actor modeling, endpoint and network data analysis phases, allowing the system to reinforce those lessons for future use. You can learn more about the capabilities and their related benefits by reviewing the blogs below.
- Cognitive Intelligence: Empowering Security Analysts, Defeating Polymorphic Malware
- Defeating Polymorphic Malware with Cognitive Intelligence. Part 2: Command Line Argument Clustering
Take a Tour Videos
As we continue to improve operational experience using the product, the team has taken up the challenge of recording brief videos to help explain new features and capabilities. Look out for tiny “Take a Tour” or “Feature Overview” buttons throughout the AMP for Endpoints Console!
Additional New Features and Enhancements
What we have described in this blog only includes the highlights of what the team has been working on in the recent months. Please see the official Release Notes for more details.
Additional Resources
AMP for Endpoints at Cisco’s Developer Network
AMP for Endpoints now has a dedicated section in Cisco’s DevNet resources: https://developer.cisco.com/amp-for-endpoints
The AMP for Endpoints API allows customers to expedite their investigations by identifying which endpoints have seen a file, create custom file lists, move endpoints in and out of triage groups, ingest events into 3rd party tools, and much more. Check back for updates as we continue to enhance this page.
AMP for Endpoints Demo
Neil Patel has recently recorded a demo of some of the main features and capabilities of AMP for Endpoints. You can find it here.
AMP for Endpoints Protection Lattice
In case you missed it, some time ago I recorded a brief video explaining the Protection Lattice provided by the product. While this is not comprehensive explanation, it provides a high-level view of the protection capabilities provided. You can find it here.
Additional Blogs
If you are interested in learning more about the feature, capabilities, and enhancements in AMP for Endpoints, please feel free to review other write-ups available at Cisco Blogs platform here.
Cisco Live! Barcelona
If you are attending Cisco Live Barcelona, join us for a comprehensive 8-hour technical deep dive to learn more about Cisco’s Endpoint Security and Advanced Threat offerings. Look for TECSEC-2599.







"Fall" (autumn) is Mar-May in some parts of the world…
Anonymous,
thank you for your comment, will consider this! To be more specific, this update covers features and capabilities released during the three months of September, October, and November.