Detecting threats, such as malware, rogue insiders, and credential abuse, within public cloud environments can be a major challenge. Traditionally, organizations have tried to solve this problem by overlaying a patchwork of agents across the cloud surface to detect bad activity. This approach requires significant costs and effort to deploy, maintain, and manage in dynamic environments such as the cloud.
Instead organizations need a quick, automated, and easy security solution to monitor their cloud environments. Cisco Stealthwatch Cloud can now deliver behavioral security analytics, comprehensive visibility, and effective threat detection in Microsoft Azure environments in minutes.
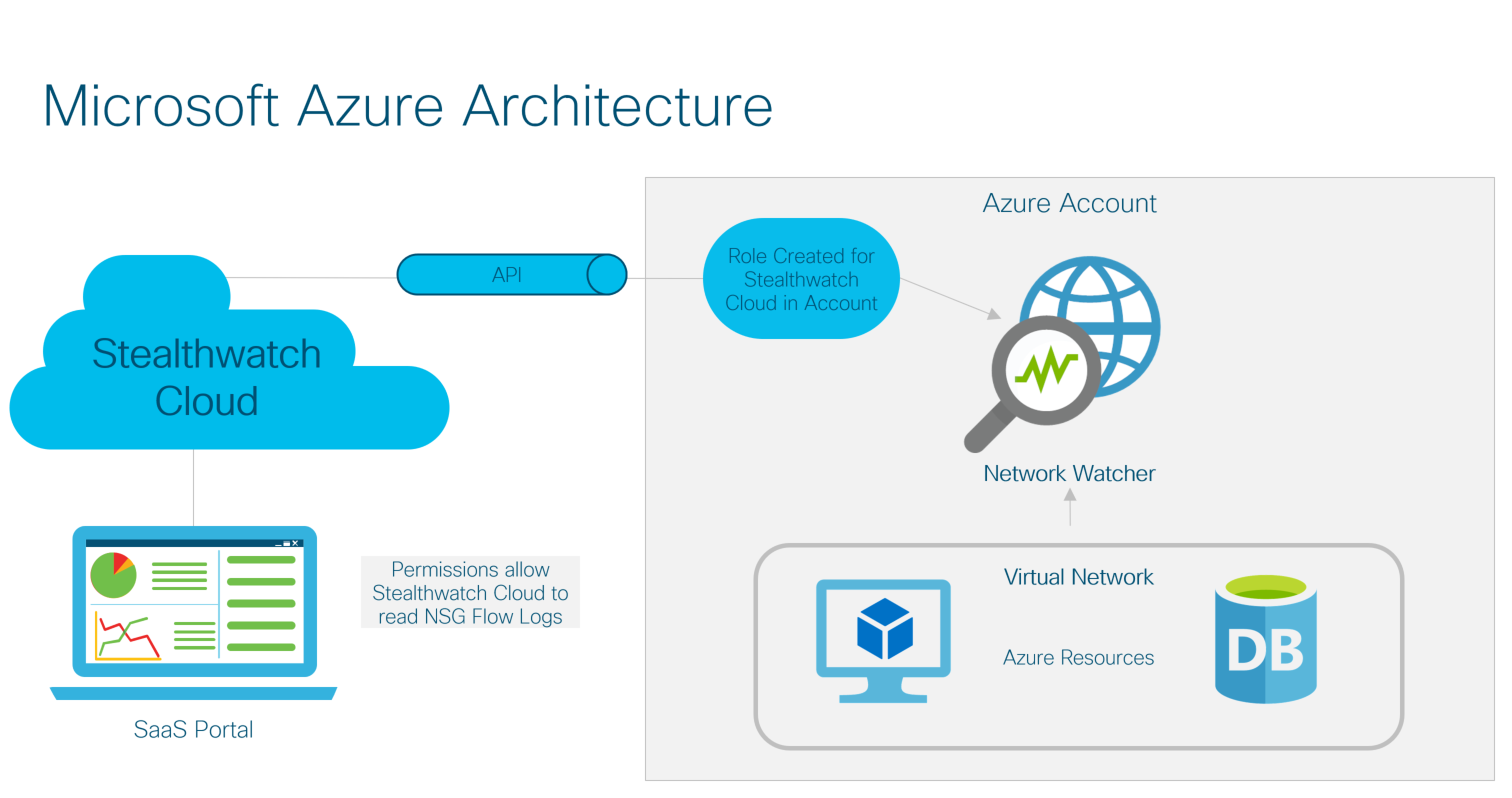
With the support of network security group (NSG) flow logs version 2 in Azure, Stealthwatch Cloud can deploy in as little as 10 minutes via API with no need for an agent. The update to Flow logs v2 is currently being rolled out to Azure public regions. It is currently available in the Azure West Central US region, with deployment continuing over the next coming weeks.
Interested? Try a free 60-day trial of Stealthwatch Cloud today!
Here are a few key benefits of Stealthwatch Cloud:
Low-noise, effective threat detection
One of the most resource-draining problems for a security team is false alerts. According to the Cisco 2018 Annual Cybersecurity Report, only 56 percent of security alerts are investigated, and of those, only 34 percent are deemed legitimate alerts. A noisy security solution consumes security analysts’ time, and even worse, may lead to real threats going undetected or uninvestigated.
Stealthwatch Cloud was purpose-built to be a low-noise, valuable security solution. Every time a customer closes an alert, they see the most important dialog window in Stealthwatch Cloud:
To date, 94 percent of Stealthwatch Cloud alerts are rated “helpful” by customers. In other words, when Stealthwatch Cloud asks for your attention, there is a good chance you will be glad you investigated it.
Easy, agentless deployment
With NSG flow logs version 2, which is currently being rolled out, Stealthwatch Cloud can now be deployed in Azure environments without the need for agents or sensors. This allows for quick and easy deployment. In many cases, Stealthwatch Cloud can be deployed in 10 minutes or less with minimal setup or configuration. In addition, this allows Stealthwatch Cloud to keep up with highly dynamic environments and maintain a record of resource activity even after they have been torn down.
Low-configuration needs
Organizations adopt the cloud because it is cost-efficient, highly available, and automated. Security solutions that require heavy management and oversight can undercut these benefits. If a solution requires someone to manually classify resources and configure analytics, it can quickly become a full-time job in the ever-changing environment of the public cloud.
Stealthwatch Cloud is a cloud-native solution that requires minimal oversight and management to be valuable. Using entity modeling technology, Stealthwatch Cloud automatically determines what role each resource plays on the network and how it normally behaves. It then uses this model to identify suspicious and known-bad behaviors. For instance, if a cloud resource never communicates with outside hosts on the Internet, but one day starts sending a large amount of data to a never-before-seen server, it could be a sign of data exfiltration. Stealthwatch Cloud would detect this information in real time and trigger an alert on it.
In addition, Stealthwatch Cloud is a software as a service (SaaS). There is no need to maintain hardware or apply patches, and new features are added monthly. It is available in subscription usage-based or term-based licenses.
Try it today!
Interested in Cisco Stealthwatch Cloud? You can try it today with our no-risk, 60-day free trial. To sign up, click here.





