IoT, The Oppressed Project
We are now in the era of IoT “Internet of Things”. It’s a concept that not only has the potential to impact how we live but also how we work. And as things become more connected, people become more concerned about their security and privacy. I have gone through a lot of technical conversation about IoT and realized how paranoid people are about their connected devices and appliances.
Why paranoid?
The future Internet will be an IPv6 network interconnecting traditional computers and a large number of smart objects or networks such as Wireless Sensor Networks (WSNs). By 2020 there will be over 26 Billion connected devices and some estimate this number to be more than 100 Billion connected devices. This includes mobile phones, Smart TVs, washing machines, wearable devices, Microwave, Fridges, headphones, door locks, garage door openers, scales, home alarms, hubs for multiple devices, remote power outlets and almost anything else you can think of like your car and airplane jet engines.
Ways of securing the traditional Internet networks have been established and tested. The IoT is a hybrid network of the Internet and resource-constrained networks, and it is, therefore, reasonable to explore the options of using security mechanisms standardized for the Internet in the IoT.
What will we do about managing the usernames and passwords of every single connected device? What about our privacy? What if some hacker was able to control our video cameras? More and more questions are being asked and more security concerns are being escalated. Do we really have to be paranoid about IoT?
IoT was already there
Most of us have Computers, Laptops, Tablets, Mobile phones, Printers, Game consoles, Media players, Storage device, Video Cameras and Satellite Receivers which are already connected to our home networks. Those are some of the Internet of Things devices and we were OK with that although if some hacker could hack into one of the cameras connected to one of the Laptops or even to one of the Smart TVs, he could see what’s going on inside the home 😉
So what is the problem?
The problem is not with IoT, the problem is with how we understand IoT. IoT not only means the interconnectedness of appliances, computers, microprocessors and machines, all of which have IP addresses or some form of digital identification, it also means the interconnectedness of devices coupled with automated and centralized data collection and analysis capabilities from those devices or processors linked to them. This leads to tremendous possibilities to develop new applications for the IoT, such as home automation and home security management, smart energy monitoring and management, item and shipment tracking, surveillance and military, smart cities, health monitoring, logistics monitoring and management. Due to the global connectivity and sensitivity of applications, security in real deployments in the IoT is a requirement.
Cisco is very clear about IoT Security:
“IoT security requires a new approach that combines physical and cyber security components.”
Learn how Cisco can help you more securely implement the opportunities and benefits the IoT can bring. IoT Security
Please watch this video, where Dan O’Malley and “Rick the Radio Guy” give an overview about how Cisco IPICS open standards and integrated technologies enable Internet of Things Secure Mobile Communications and Communications Interoperability to support mission needs for Public Safety, Defense, Manufacturing, Utilities, Transportation, Mining, and more.
What to do?
“#security should be the #1 thing companies focus on in the wake of #IoT” – CEO John Chambers http://cscoengs.co.vu/1ucx8GY
“It is not often that companies learn from the past, even rarer that they draw the correct conclusions from it.” – Henry Kissinger
I hope companies will break this trend when it comes to security in the Internet of Things (IoT). Here, I will give some tips for both end users and service providers to secure IoT.
End users
 1. Hardening your Router
1. Hardening your Router
- Change the Default Username and Password. Do not ever use the default username/password of any device not only your router.
- Hide your SSID and choose something clever. Never use something related to your location like “Maher’s office room”
- Encrypt Your Wireless Network. If you’re using WEP encryption, get that changed as soon as you can, then move on to some of the other methods.
- Segmenting the network. Set up one network for each group of devices, by this, if one segment is hacked, all the other devices are not accessible and remain safe.
- Use MAC address filter so the router assign only an IP for each device that’s in the MAC address list and all unknown devices will be blocked from accessing the network.
- Disable guest network access.
- Use a firewall, whether it’s a stand-alone device or one turned on inside the router.
2. Keep your Network devices up-to-date
It is very easy to gain access to your computer/devices if there are security holes in any software that you have installed. NBC news reported of a family that had an Internet enabled baby monitor that was hacked by an intruder. The intruder likely used a program that scans IP addresses for open ports that have security and web cameras connected to them. They had a three years old camera with outdated firmware that enabled the intruder access.
For this reason it is critical that you keep your software up-to-date. This rule applies to all devices in your home network, like smart phones and even Wi-Fi devices such as your baby monitor. But ensure that devices receiving updates over the web are doing so over secure systems. Ensure that connectivity is secure and use devices that provide for two-factor authentication.
3. Use OOB systems
Governmental departments and Banks use IoT linked devices, but they are mainly out of reach from hackers because they are OOB (Out Of Band). But keep in mind that these OOB systems are subject to insider attacks.
4. Stay informed
Information about managing and securing IoT devices can be obtained from some organizations such as FIPS and National Institute of Standards and Technology. These organizations address critical steps that are needed to secure and protect information and critical systems.
5. Secure the location of your IoT linked devices
Data should be protected physically and virtually and this should be done by your IoT service provider. Be sure to have a contract that outlines the provider’s responsibilities if there is a breach of its system.
Service Providers
In this section, I will point some tips without going deep in Details.
1. The communication in IoT should be secured with:
- Authentication services
- Integrity
- Confidentiality
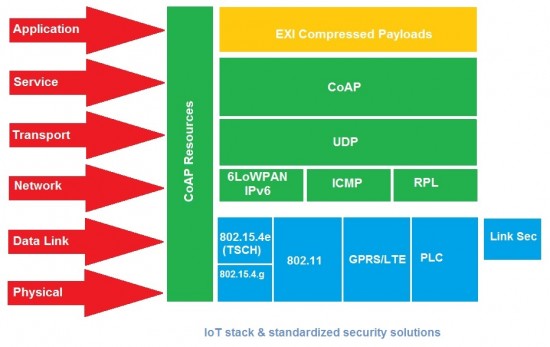
This can be achieved at different layers:
- At the link layer, with IEEE 802.15.4 security.
- At the network layer with IP security (Ipsec).
- At the transport layer with Datagram Transport Layer Security (DTLS).
Even if the IoT is secured with encryption and authentication, the sensor nodes are vulnerable to wireless attacks, Therefore, an IDS and firewalls are needed.
2. Network Security
The Network can be attacked even if there is a communication security that protects messages. Such attacks are aimed to disrupt networks by interrupting the routing topology or by launching DoS attacks. IDS, therefor, are required to detect any malicious activities in the network. Firewalls are required as well to block any unauthorized access to the network.
6LoWPAN networks in IoT are vulnerable to a number of attacks from the Internet and from inside the network and are easier to compromise a resource-constrained wireless node than a typical Internet host. Considering the novel characteristics of the IoT it is worth investigating the applicability of current IDS and firewall techniques in the IoT, or designing a novel IDS and firewall exploiting the contemporary IoT features and protocols.
3. Data Security
It is very important to protect sensitive data stored on any IoT device. As we know, most of the IoT devices are wirelessly connected and it is hard to protect each connected node with smart cards or TPM. Software based solutions can be used to secure such sensitive stored data.
4. The following security services are necessary in the IoT:
- Confidentiality: Any attacker can intercept messages between the source and destination, therefore E2E message secrecy is required in the IoT.
- Data Integrity: Message Integrity Codes (MIC) are mostly used to provide this service
- Source Integrity or Authentication: communication between end points should be verified
- Availability: Services that applications offer should be always available and work properly.
- Replay Protection: There should be mechanisms to detect duplicate or replayed messages.
In the end, I want to say “As long as there is a mind to invent, there is a mind to crack. Just do what you have to do”.
I hope this has been informative for you and I would like to thank you for reading.





“As long as there is a mind to invent, there is a mind to crack. Just do what you have to do”.
That’s true, there is no 100% security, but we have to do what we have to do 🙂
You’re right, I would be lying if I say internet is 100% secured. Thank you, Dima!
Dear sir. I just wanted to thank you for your clear explanation and interesting way to present the information. I really appreciate it.
Oh, you’re welcome!. Thanks a lot for your comment and I hope it helps.
The article very nice and useful, i like it, Thank’s Mr Maher
Glad to hear. You’re always welcome! 🙂
Very informative article, Thanks for sharing.
You’re welcome, Dr Rabab!
Clear and precise and necessary information.
There will be a Spanish translation for this item?
Thank you very much S. Maher
Rosa, I will try to prepare another Spanish version. Stay tuned.
Maher, happy to help with the spanish translation, just ping me.
Oh, that’s really very nice of you Mr. Agatiello!
ACTUALLY, very nice and convincing article…thank you very much
Glad you liked it, and you’re welcome, Kinda!
Thank you so much, Maher 🙂 Very informative article.
You’re welcome, Mohamed 🙂 and thanks for your comment!
ايه الحلاوه دى يا دين النبى
الله اكبر عليك با حبيب والديك
مفيش اروع ولا احسن و لا اوضح من كده كلام
إتس فيري جود سبيتش
مع انى ماليش ف المجال ده بس انا كعاتف اتبسطت
My apologies, but I don’t get what you meant?!
nice and necessary article…thank you
Oh, you’re welcome!. So glad that you find it useful.
I need to thank for this good article
You’re welcome!
Great article :))
Thank you, Elda!
looking forward to your next article.
It won’t be soon I think 🙂
Very good aritcle. You suggest using a set of features (like network segmentation) are vendors in the consumer space working on providing those kind of products. Just to segment you need vlan support (of some kind maybe PVLANs will work) multiple SSID support etc. Can I go buy this today?
Thank you, Fred for your comment!. For your question, yes of course you can buy this today, for example Cisco WRV210 Wireless-G VPN Router suports multiple SSIDs and VLANs provide separate, secure networks. You can read more about it at http://www.cisco.com/c/en/us/products/collateral/routers/wrv210-wireless-g-vpn-router-rangebooster/data_sheet_c78-502735.html
The main issue with the internet of everything is that the term is so broad as to be hard to establish what it applies to exactly. If this term is grounded in devices that can access the internet that in itself is not useful. It needs to extend to a few design constraints as well so that the discussion can be grounded. If the IoE is limited to products that use sensors and actuators and are controlled by software that has the capability to access the internet, then we are limiting it to something that can be pointed to as examples. The main problem I see is one of accessibility to the capabilities for everyone who can do some basic coding. A good candidate is Python given that its origins as a teaching language make it suitable for a broader range of people to learn and use in everyday practice. The only IoT toolkit that I know of that can go from toy prototype to commercial product is TOI, thingsoninternet.biz and their VIPER solution. I saw that they have an kickstarter campaign now so it is something that anyone can access and use. This makes the discussion of IoE more grounded in the specifics of this and other toolkits like it so that we can consider where this all goes in the future once everyone can code a solution themselves without being an electronics engineer.
We’re on the same page, Ray
Ray thanks for the pointer, I became a backer and cant wait to see the results
Thanks Maher, very nice article. It´s important to show security as an important part of the IoT adventure, not a stopper, but a necessary piece in this exciting puzzle.
Thank you very much, Gabriel for your comment!. I totally agree with you, Security is an important part of the IoT and it should be designed in from the start and not being added as an afterthought.
thank’s a lot
You’re welcome, Tom!