Pieter-Jan Nefkens is a Cisco Champion, an elite group of technical experts who are passionate about IT and enjoy sharing their knowledge, expertise, and thoughts across the social web and with Cisco. The program has been running for over four years and has earned two industry awards as an industry best practice. Learn more about the program at http://cs.co/ciscochampion.
=============================================
At one of the projects that I’m currently working on, confusion was rising around the terms Cisco DNA, DNA Center and the implementation of Cisco DNA Center. It didn’t take me much effort to clear up the confusion but it does provide the need for an explanation on Cisco DNA, DNA Center, Software-Defined Access, Network Function Virtualization, Analytics, Automation and Smart Networks.
Reason enough for me to write down my thoughts and vision on the ever emerging trends, developments, tools and changes that will come to the network world.
Cisco Digital Network Architecture (DNA)
Cisco Digital Network Architecture is not a product, it is not a solution, it is a vision on how a network infrastructure is designed and implemented to fulfil the needs of modern, digitized, environments. In recent years more and more companies have conformed to an architecture frameworks like TOGAF and work under these architecture frameworks. I might write another blog about architecture frameworks in the future.
From a TOGAF perspective, Cisco DNA is part of the technology architecture, for the network infrastructure.
In present day, the reliability and quality of a network is such a commodity that there is limited to no understanding that a relatively small change like adding a VLAN for a new network service, can have huge consequences and downtime if not executed properly, which can result in these changes take longer than perhaps necessary. Thanks to devops, agile development and digitization a huge pressure is put on IT departments to adopt and deliver faster to the organization, but of course without any reduction to speed, reliability and safety of the network infrastructure.
Cisco DNA represents an architecture for how network infrastructure can be designed in such a way that the network (as part of IT) can adopt faster to meet the requirements and pressure from the organization. The Cisco DNA architecture is based on the following principles upon which the solution model for the modern network infrastructure (design, implement and management) is built:
There is a layered approach with abstraction to this framework, so that each tool / process can fit in the right place. This way, an open framework is used where best in class can be placed at the right layer.
Design principle #1: Security everywhere
Security is essential in any environment, public or commercial. With the recent threats of ransomware, including Not Petya and other hacks no extra explanation is needed. A secure network is critical for the security of the data that runs through the organization. By using the network as a sensor and enforcer (the network sees all flows), the network infrastructure can support in analysing the threats and risks to the organization. So the network must become a sensor and enforcer in the security framework. Of course the before-during-after paradigm for a security framework assists in this design guide as well.
Design principle #2: Virtualize everything
SDN has become common in many organizations, where the control plane is separated from the data plane (software defines how data flows through the network). SDN was always restricted to the type of hardware that is in place, e.g. a switch doesn’t have router functionality, a firewall is not a router, etc. What if you could virtualize these network functions in such a way so that the software defines what role the hardware has, without impact on performance (hardware asics)?
This means that a network component can fulfil different network functions during its lifecycle, being a switch, a firewall, a router, a WAAS or any new network function that is invented. Based on this design guide that all network functions are virtualized, an SDN controller can truly control the behaviour of the network infrastructure
Design principle #3: Designed for automation
Design the network in such a way that automation can take place. Automation is key to fast, standardized, delivery of changes across the infrastructure. This can only take place if the network infrastructure is standardized on software releases and configurations.
For example, only when the voice VLAN on all branch locations is the same, can a generic standardized policy (and assignment) be created for voice devices.
Design principle #4: Cloud service management
Cloud has become a common part of many IT environments. Cloud applications have very high availability and capacity. By using the cloud one can define and provision network services (applications, services) and policies (who is allowed to do what) from a central environment. Of course there is choice to run this centrally managed cloud app in a public cloud or on premise, depending on the organizations requirements and cloud maturity.
Design principle #5: Pervasive analytics
Machine Intelligence, big data lakes, and analysis of microflows help with the prediction of failures in your network. By proper analysis, problems in performance or behaviour can be predicted in a proactive manner. As an example, we all know that when a client cannot connect, it’s always the network. But with pervasive analytics, telemetry reports that the DHCP server isn’t responding back on the DHCP requests, so it is more a DHCP server problem. The average time to resolve a problem and find a root cause can be reduced dramatically because pervasive analytics provide you the insight. Perhaps this design guide could be the best part of the business case for DNA, imagination is only the limitation to what can be done.
Design principle #6: DNA-ready infrastructure
On the bottom is the infrastructure layer, consisting of all network components like your routers, switches, firewalls and wireless controllers. It doesn’t matter if the equipment is physical or virtual like ASAv, CRS1000V, or NGFWv.
The features of DNA (faster delivery of services, detecting problems and increasing flexibility) can only be implemented if your network devices are also DNA-ready. In fact, almost all actual switches, wireless components, firewalls and routers are DNA ready. Proper life cycle management is supportive for this.
DNA Framework
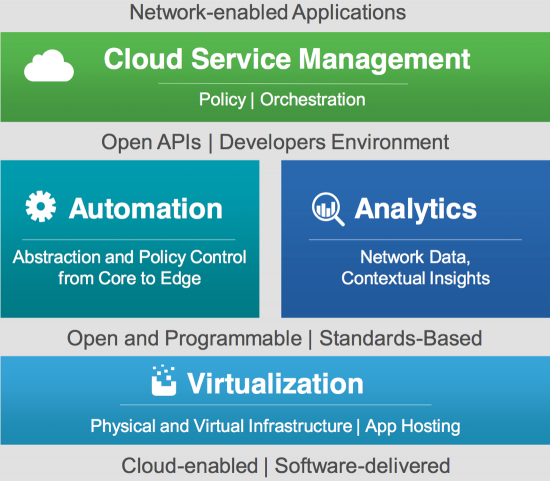
Principles alone do not create an architecture, it also needs a conceptual framework in which the different elements come together for the solution that meets the requirements (both technical and from the business) and the design principles. The network infrastructure communicates, via open API’s, with two processes:
• Automation is responsible for the so-called day0 (provisioning of new equipment) and day1 operations (create, change, update or delete of services). These API’s could be implemented in different ways, although more and more devices supported NETCONF and YANG models.The automation block can be filled with different kind of tools, for example APIC for ACI, Cisco NSO or APIC-EM for campus networks. It is dependent of the organisation itself.
• Analytics tooling receives telemetry information from the network infrastructure, also based on open API’s. This could provide all sorts of metrics, like netflow, SNMP, Syslog, but also some API-related data like reading out TCAM’s or probes.
Analytic tools can use this data and configuration to analyse and extract threats, risks and performance trends. Of course, different applications can be used for analytics, such as Stealthwatch and ETA for threat analytics, or another analysis tool.
Above the automations and analytics blocks is a superordinate (like an umbrella) process in which the network infrastructure can be defined as applications, services and endpoints. This process, which is centrally located, is responsible for pushing the proper configuration templates to the automation process and translating the data from analytics for visibility and the quality of the endpoints connected to the network.
This solution architecture takes a network infrastructure quite some steps further than a validated collapsed core design, a Cisco SAFE architecture or a validated design for datacenters. It is much more a vision and abstraction model under which different network designs can be implemented. The principle thought is that every network is like a snowflake, all are unique, but with 80% similarities. Cisco DNA is used as basis for the Cisco Network. Intuitive and Intent Based Networking.
Model, Tools and technology
A model is one step, but that doesn’t bring any company to a network infrastructure ready to adopt changes faster and become a more predictive less complex network. For that, Cisco has announced (and available) several products and solutions, that meet the above mentioned model. Below is a list of products from Cisco with a short explanation on its role within DNA.
DNA Center
DNA Center was announced at Cisco Live Las Vegas in June 2017. DNA Center is the single centralized management interface for Cisco’s Intent-based networking solution. It uses templates based on Cisco best practices and validated designs to enable the configuration of Cisco products and using network automation for solutions like software defined access (SDA). DNA Center is the integration of the blocks automation, analytics and centralized tool in a single appliance (DNA Center Appliance).
Cisco Enterprise Services Automation (ESA)
This is a separate application that communicates with APIC-EM (automation) to realise network function virtualizations on Cisco NFV platforms (ENCS5400, UCS-E series). It is used to define, deploy, and manage these virtual services on the platform. It is logical that in time this will also be featured in DNA Center.
Campus Fabric / Software Defined Access (SDA)
Software Defined Access is a (scalable) solution for campus networks to quickly, reliably and easily define new networks, including security and microsegmentations. It is based on a logical layer3 network infrastructure for connectivity (underlay) and clients are connecting to virtual networks based on VXLAN for data transport and LISP for control. As VLAN’s are not used anymore, time to deliver new services is cut down dramatically and problems with STP and VLAN’s are history as there is no layer2 network anymore.
Cisco Network Services Orchestrator (NSO)
Cisco NSO is a Network Services Orchestrator, also an automation tool. NSO is the result of the acquisition of tail-f in which the network infrastructure is based on a YANG model. On top of this YANG model services can be defined and deployed. So-called network endpoint devices (NED) take care of the translation from the YANG model with services to a configuration of the device. NSO is from the ISP world and is making its move to the enterprise however it doesn not currently support DNA Center. NSO is vendor-independent and there are also NED’s for other vendors like Citrix Netscaler, etc.
Cisco ISE
ISE is an integral part of the DNA framework, although it doesn’t fit in automation or analytics, as it provides both functions for device identity. ISE provides the identity services for your network and is used in Software-Defined Access (SD-Access) deployments to provide the SGT’s to the proper network port.
Enterprise Threat Analytics (ETA)
ETA is a newly announced analytics product that is capable of analysing behaviour of encrypted traffic in such a way that threats and other traffic can be detected without SSL decryption. It is used to determine if anomalies, like malware, are on your network or not.
Stealthwatch
Stealthwatch is clearly an analytics tool, which is used within the network as a sensor, based on Netflow. ETA and Stealthwatch are closely related with each other.
DNA Center Assurance
Assurance is also an analytics tool, in which telemetry is extracted from the network. CMX is an example, but DNA Center Assurance takes analytics much further, like detecting if the DHCP server isn’t responding to requests, or that a client is entering a black hole, or that your network is hitting a known caveat.
DNA-Ready Infrastructure Devices:
Almost all modern Cisco Switches, Routers, Firewalls, Wireless Controllers support DNA. Rule of thumbis that if the device has the UADP ASIC, it is DNA-ready and supports SD-Acesss. Most of these devices are Cisco IOS-XE based, like the Catalyst 3650/3850, ISR 4k and the WLC 5520’s. The new Catalyst 9000 has the new UADP 2.0 ASIC which enables it to support ETA.
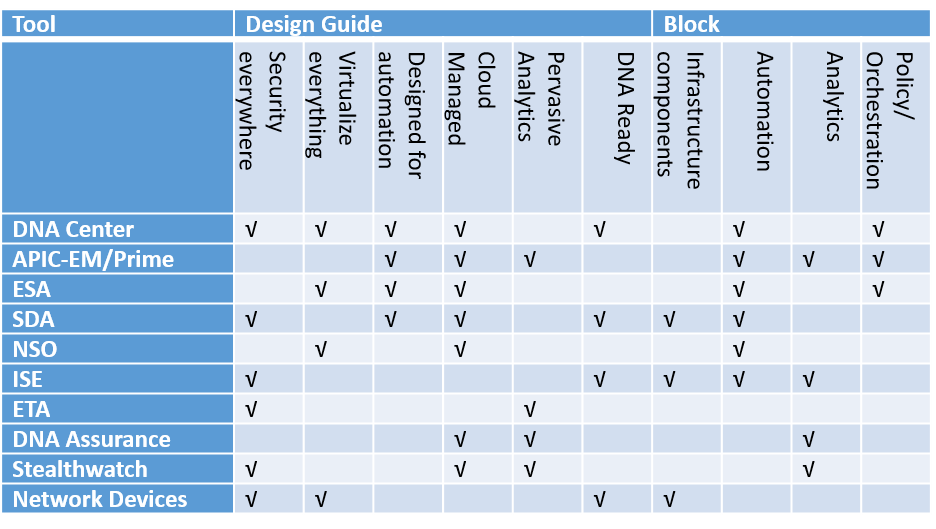
The table below provides an overview which tool fits in which design guide and DNA Center solution block:
The Cisco Digital Network Architecture is defining a vision for the networks that need to be built to support the huge amount of devices that will be interconnected and be flexible enough as nobody can foresee the future. Implementation is not a one-step-fits-all solution that is easily implemented. It is a journey that starts today and allows enterprises to adopt and build on the DNA framework for readiness and agility in the digital world.




