We are thrilled to announce that Cisco’s unified OT security and networking architecture is named “Smart Manufacturing Solution of the Year” in the 2024 IoT Breakthrough Awards.
Industrial security can be a complex undertaking, and yet OT security is quintessential for modern Industrial IoT (IIoT) operations. IIoT systems generally contain a variety of interconnected systems and technologies, each with its own security needs. Some of these are older and not designed with modern security threats in mind. Furthermore, OT teams, with their limited resources, may not be able to dedicate adequate time and personnel to security, and IT teams often do not understand operations well enough. Potential production losses resulting from increased security measures can also sometimes conflict with the need to address security concerns.
OT security has, therefore, traditionally been an afterthought and built using a piecemeal approach, relying on a patchwork of solutions provided by different vendors, each designed to provide only a single security function. Customers are forced to deploy point solutions that lead to unnecessary hardware deluge, increased complexity, and an overall security solution that does not scale or deliver.
Listen to a narration of the blog on YouTube.
An integrated network and security architecture
At Cisco we take a simpler, scalable, and more effective approach by integrating security functions directly into the network fabric. Our innovations enable the industrial network to replace the many one-function point products.
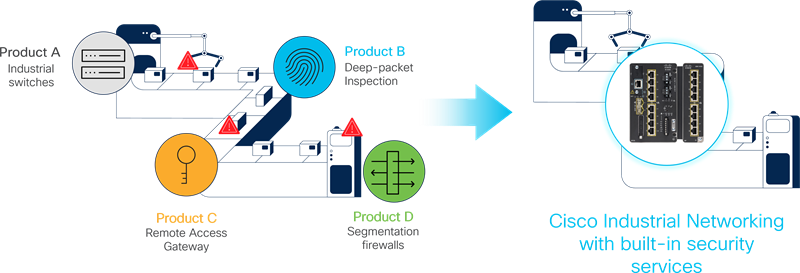
With a unified industrial security and networking architecture, Cisco brings simplicity and scale to both connect and protect operations. It reduces complexity by delivering visibility, segmentation, remote access, and other security services on Cisco industrial switches and routers without the need to introduce additional hardware.
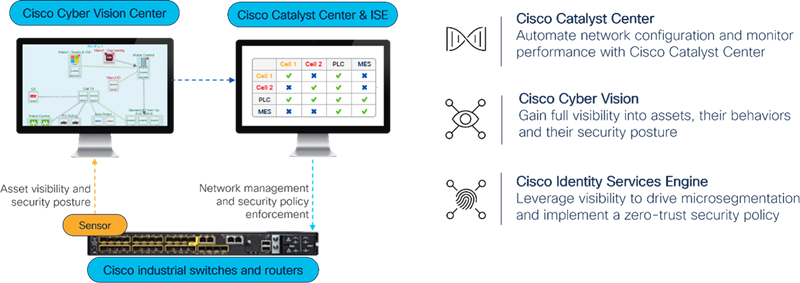
- Visibility into connected assets, network traffic, and assessing existing asset vulnerabilities is recognized as the first step in securing operations. Traditional security vendors provide a deep packet inspection (DPI) server for this purpose to which you need to span traffic from your switch ports, adding to the network complexity and costs. Cisco Cyber Vision runs within Cisco industrial devices and performs the same functions without the extra server, complications, and expense.
- The second step once visibility is established is to partition your industrial network into smaller segments to contain any malware that may find its way inside, but in a way that allows legitimate traffic to flow unhindered. Traditionally, this network segmentation has been done with sets of firewalls or Access Control Lists (ACL) configuration in switches. Both are either expensive, difficult to get right and maintain, or both. Native capabilities in Cisco Industrial Ethernet Switches allow dynamic and automated multiple levels of segmentation without the firewalls or manual ACLs.
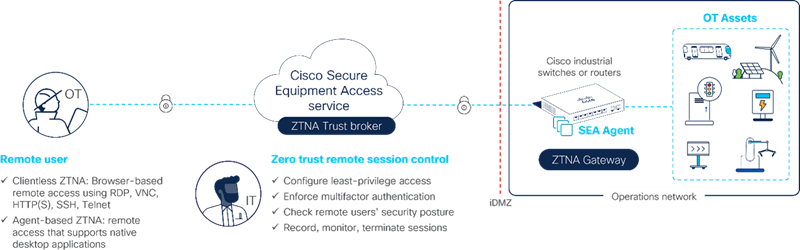
- A third necessity is to enable operations personnel to securely access industrial assets remotely. Traditionally, organizations have depended on solutions like VPNs that require frequent manual updates to firewall rules and jump server settings, potentially unsecure methods such as cellular gateways, to name a few. With the Secure Equipment Access solution, Cisco industrial network equipment enables secure zero-trust network access (ZTNA) by embedding ZTNA gateway functionality without the need for extra servers. Enabling remote access is now just a software feature to activate in your Cisco industrial network.
Put the award-winning solution to work for you
We have not only designed an award-winning architecture, but we have also made it easy for you to adopt it, meeting you in your security journey where you are and guiding you gradually to where you want to be. Our four-step process can lead you from building a solid security foundation, through visibility, remote access, and segmentation to incident reporting and response.
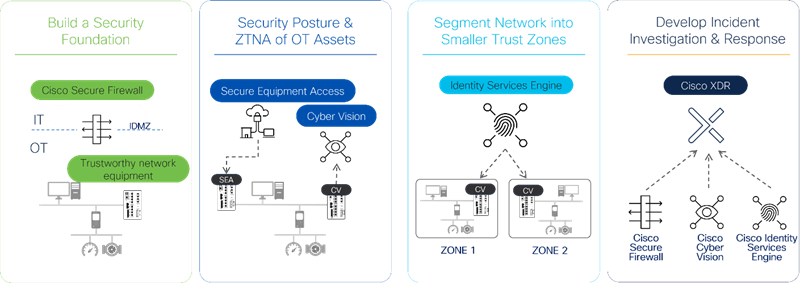
The network embedded security architecture scales across all OT use cases like manufacturing, transportation, utilities, oil & gas, renewable power generation, and mining among others.
We are grateful to the IoT Breakthrough Award judges for recognizing the benefits of our integrated security and networking architecture.
For more details and to discover what’s possible, please refer to the whitepaper, Harness the Power of Networking to Secure Industrial Operations, or set up a free no-obligation consult with one of our experts.




