As we think of Healthcare and Big data Analytics, some of the topics that come to fore front are personalized medicines, managing readmissions, identifying health risk indexes and many more. While each of these is important areas that benefit from power of Big Data Analytics, one of the areas that is at table stakes in Healthcare is protecting critical care systems. Can the power of big data analytics provide us a protective shield?
Before we dive in, the question that comes up is why is Healthcare Security any different and why Big Data Analytics instead of the traditional approaches to protection that we have today.
This was the topic of my presentation at the recently concluded COM.BigData 2014 conference in Washington DC: ‘Dynamic Protection for Critical Care Systems using Cisco Cloud web security (CWS): Unleashing the power of Big Data Analytics’.
While the Health IT transitions are opening up healthcare access in newer ways that has significant security implications, there are additional trends that are making Healthcare a prime target.
According to the World Privacy Forum, the street value of a stolen Healthcare data is ~ $50 as compared to $1 for a stolen social security number. The Ponemon Institute, in its third annual report on Medical Identity theft, 2012, estimates the economic impact of medical identity theft at 41.3 billion per year, a significant increase from 30.9 billion per year in 2011. In addition, new attack models such as ransomware can capitalize on the sensitivity of the situation, where the question is not about losing your data, but your life. Adding up all these, healthcare industry is an attractive target.
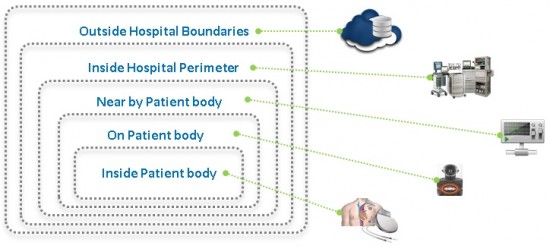
On one hand, the perimeter of where the critical systems are located has expanded significantly, while on the other hand, the sophistication of malwares has increased exponentially. Dynamically morphing, obfuscated and evasive breeds of malwares are capable of sneaking through the perimeter defenses. Combining these two, relying on the current perimeter and rules based security models to protect the critical care systems is a risky endeavor.
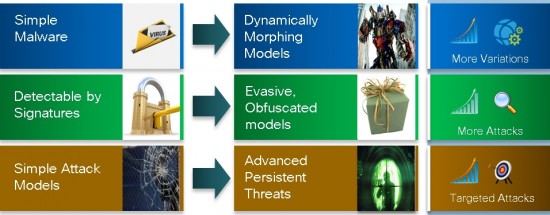
Keeping up with the evolving threats is time consuming, manual, and complex and requires expertise that might not be the core competency of healthcare systems. With changed models of attack such as Advanced Persistent threats, the protection strategy must account for the entire continuum of attack – before, during and after.
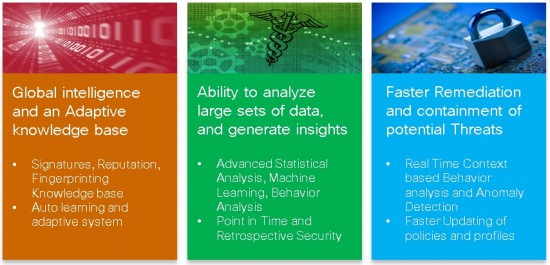
This is where the protective shield of analytics can help protect the critical systems by leveraging the ability to mine large sets of traffic in real time, adapt, learn, remediate and contain potential threats.
Bringing all these together, Cisco’s Cloud web security (CWS) and its related portfolio is a classic example of how the power of big data analytics is unleashed in securing critical systems. Cisco worldwide threat intelligence, advanced threat defense capabilities leverages the big data to perform behavioral analysis, anomaly detection, evasion resistance, reputation and retrospection and much more to identify threats in real time to detect, block and mitigate threats against your critical assets.
To put big data in perspective, Cisco Security Intelligence Operations (SIO) analyses daily more than 100 TB of security intelligence, and 16 billion web requests to detect and mitigate threats. It also has granular visibility and control of more than 150,000 applications and micro-applications. It defends against zero-day web malware through dynamic reputation and real-time threat intelligence gathered from advanced statistical modeling and machine learning.
Compare this with your current perimeter based protection models. Are your critical systems safe today?
To view the entire paper, click here. To learn more on how Cisco can help, visit the security solutions on cisco.com.





