There’s no question, the employee-led mobility revolution has arrived. Will the Bring-Your-Own-Device (BYOD) policies that must inevitably follow come soon enough?
Everyone is bringing their devices, everywhere they go. People, no matter their occupation, want to check the news, keep in touch, catch up on email, and stay productive or entertained wherever they are. So the real question for government organizations becomes, “how do we address this mobile explosion and the proliferation of employee devices?”
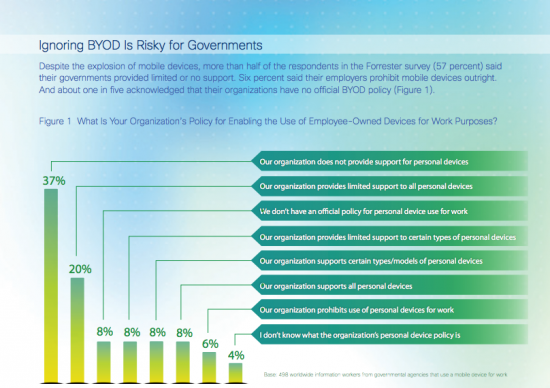
 Many have yet to implement BYOD policies for fear of the security implications and exposing sensitive data. But what is the security risk of doing nothing? In a recent Forrester survey of 498 government employees from around the world, more than half of the respondents (57%) said their organizations provided limited or no support for employee devices and some even said their employers prohibit mobile devices outright. The survey also revealed that 3 out of 10 government workers in these situations find “alternative ways” of using their device for work.
Many have yet to implement BYOD policies for fear of the security implications and exposing sensitive data. But what is the security risk of doing nothing? In a recent Forrester survey of 498 government employees from around the world, more than half of the respondents (57%) said their organizations provided limited or no support for employee devices and some even said their employers prohibit mobile devices outright. The survey also revealed that 3 out of 10 government workers in these situations find “alternative ways” of using their device for work.
This poses a problem for government agencies: having no policy or prohibiting devices is risky because employees are bringing and using their devices anyway.
Finding work-arounds isn’t just for hackers and the technologically acute. At the IACP (International Association of Chiefs of Police) annual event in San Diego this year, I heard a police officer describe how, before his department had an official BYOD policy, he and his fellow officers would take photos of possible suspects on their own mobile phones and insecurely send them to each other for identification purposes at times when, had they not done so and waited to follow proper protocol, they would have lost their suspects. Did they make the right call?
Some agencies are already using BYOD to their advantage, allowing employees to select their own devices, improving employee satisfaction, response times, and productivity. To find out the percentage of Forrester survey respondents who believe that BYOD improves productivity and also to see specific examples of cost savings from government agencies, click the image below to read on in our interactive PDF white paper. The paper also discusses how to implement a secure BYOD policy, one that is enforced based on a user’s role, type of device, location, and more.






I am not terribly tech savvy But I have to think that if government employees are going to carry around devices with peoples information on them (ie IRS) Or information that could pose a security risk Hire security measures need to be in place. If your device is lost or stolen the information should be able to be remotely removed Or some type of electronic self destruct. For the everyday person and their work computer it could be extremely productive to be able to take it with you. Again some companies have security risks That could be protected in a similar way.