When I examined President Trump’s cybersecurity executive order, I focused on two things: What it really means and what are its most important aspects.
Formally titled the Presidential Executive Order on Strengthening the Cybersecurity of Federal Networks and Critical Infrastructure, the order was issued May 11.
In my first post on this subject I focused on what immediately struck me as a new demand for executive and leadership accountability. This is a topic that this president is fairly unique in emphasizing, and I think he has clearly demonstrated that he’s willing to hold people accountable in his administration.

But there is another important part buried deep within the order (Sec. 3 (d)), one that cyber experts have largely overlooked: the cyber workforce, which the order addresses in a requirement for workforce development. The provision calls for several specific measures to assess the state of the cyber workforce, and to add to its ranks.
As a nation, we face a massive skills shortage for defenders in cyberspace. The evolution of this role has changed from the basic skills of a “firewall guy” to one that requires the operator to possess detailed technical capabilities. Today’s cyber defender must be able to perform advanced security analysis and be equipped to take definitive actions within the network to address security incidents as they occur.
This is a unique skillset and one that is created over many years of training. But here is the real challenge – we really don’t have many people with those skills. Estimates vary, but we need somewhere between 500,000 and 1 million such people just to fill today’s gaps.
The challenge is even sharper for the federal government because in most cases, agencies cannot hire foreign nationals for those jobs. Many such federal positions also require the employee to have an active security clearance.
So what do we do here?
Deep technical training of skilled personnel is clearly part of the answer, but so is trustworthy automation and a lot of it. But the details really matter here and this is the heart of the issue.
Today, many of these training environments have been built using open source toolkits including many of the federal government’s own defensive cyber operations toolsets. They build virtual networks for training and use inexpensive off-the-shelf or open source components. These systems are inexpensive, but they do not accurately replicate real networks and circumstances for the operators and provide very limited support options for a large training environment.
It will be absolutely critical for the US Government to partner with industry on adapting commercial toolsets and capabilities as well as building real-world virtual environments based on commercial products in use today to help adequately prepare the students for what they will see and use in the real world cyber jungle.
We must build extremely robust cyber defense classrooms that are rooted in large, individualized virtual environments (virtual networks) on a per student basis. And these classrooms must provide each student their own virtualized cyber workspace with a host of commercial products that are in common use today.
But training our next generation of cyber defenders on open source routers, switches, firewalls, IPS, and VPN technologies is both a disservice to the student and also provides the government a false sense of security. These operators will be completely unprepared to face real-world challenges when they emerge with their newly minted “Cyber Defender” badges.
So how do we go about solving this? It’s actually not all that complicated.
The federal government must focus its acquisition strategy on commercially available virtualized offerings. This means virtual routers, switches, firewalls, IDS, VPN Gateways, email and web security. Most importantly, the government should use commercial threat analytics running within these virtual training environments.
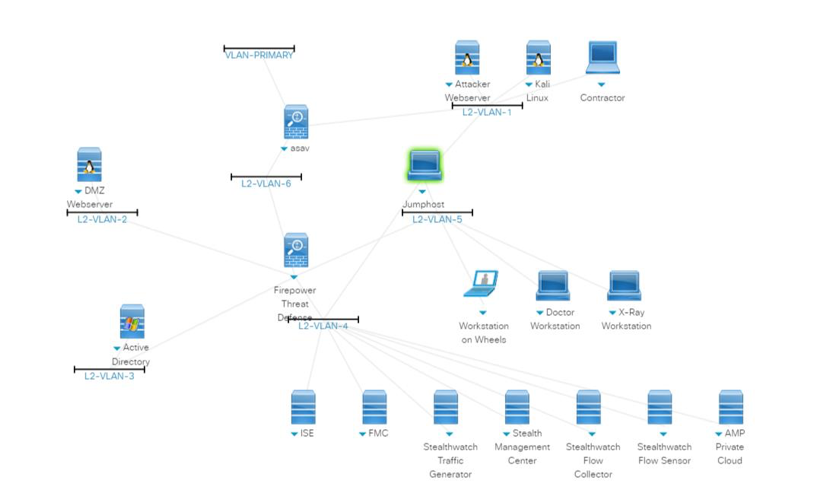
A simple example shown below is a cyber threat response clinic that Cisco runs to help train our own people and partners on defensive tactics.
Finally, the government must focus on building partnerships within the cyber defense industry – focusing on the products and technologies that are actually deployed today. That will help ensure that training environments closely mirror the types of network landscapes and threats that the trainees will one day face in real life.






Hello Really Nice article. Can you please upload the clear picture. The infograph in the post ??
This site had mentioned this once – Kaise Kare
Kaise Kare, please email me at mihardy@cisco.com and I’ll try to help you with that.
Although not directly applicable to other countries, reading the executive order is also of interest to me. Thanks for pointing that out.
Great writing, Andrew – thanks for call attention to this issue and offering a real-world solution!