 Over the last few years, cybersecurity without doubt, has emerged as the top of mind concern in Industrial Control Systems (ICS). But, it is the breadth and depth of ransomware attacks in 2017 that has led industries in manufacturing, utilities, oil & gas, mining etc. scrambling from what was a concern, into action of implementing security in their industrial networks.
Over the last few years, cybersecurity without doubt, has emerged as the top of mind concern in Industrial Control Systems (ICS). But, it is the breadth and depth of ransomware attacks in 2017 that has led industries in manufacturing, utilities, oil & gas, mining etc. scrambling from what was a concern, into action of implementing security in their industrial networks.
But what does it take to implement effective security in industrial networks? As detailed in the 2017 Midyear Cybersecurity Report published by Cisco, industrial customers face two major challenges when embarking on this task. The first, is lack of visibility of industrial assets, and the second is an operational challenge arising from friction between IT and Operations Technology (OT) teams.
It’s no secret that lack of visibility is a problem in industrial environments. Most users are simply not aware of the full scope of industrial assets connected to their networks. While this lack of visibility is a major issue from an availability perspective – as it takes much longer for OT to root cause machine downtimes caused by communication issues, the problem takes on a different dimension when it comes to cybersecurity. Defining security policies based solely on network attributes such as IP and MAC addresses as identifiers is challenging. The enterprise IT world has solved this problem by enabling security platforms to profile enterprise assets such as phones, tablets, laptops, printers etc. to get identity attributes like device type, make, model, vendor and so on, and integrating with directory and domain systems to get contextual information that indicates the “who” and “when” aspects of communication flows. This higher order visibility of identity and context, greatly simplifies the definition of security policies. In contrast, ICS environments are filled with myriad devices that run a multitude of control protocols which are alien to typical security platforms. The lack of visibility arising due to this problem, coupled with the fact that the number of endpoints in ICS environments are an order of magnitude higher than enterprise environments makes defining security policies in industrial networks extremely challenging.
When it comes to implementing security on the plant floor the friction between IT and OT is often mischaracterized as a problem of “control”. As in, “Does IT or OT own ICS security?”. In reality this has less to do with control, but it is rather an issue of interdependency. In most industries, customers have a centralized IT group responsible for supporting widely-distributed ICS networks such as factories, electric substations, oils & gas fields, mines etc. Each of those distributed plant networks, are supported by a dedicated onsite cross-function process control/network OT team. As it stands today, most OT teams are quickly ramping up on IT networking skills, but still lack expertise in cybersecurity. So, any attempt at implementing security at the process network level requires the centralized IT team to deploy the security infrastructure and maintain security policies. In such a situation, the local OT team is dependent on the remote IT team to modify security policies on the network to accommodate adds, moves, and changes to industrial endpoints and the control system needed for day-to-day operations. This interdepartmental coordination is not achievable in real-time, and quite often changes to the control systems made by the controls team cause security policy violations set by IT, leading to downtime and an unacceptable impact to production. So, the frictions arising on ownership of cybersecurity are actually driven by the necessity for local OT teams to be self-reliant to maintain day-to-day operations.
However, the lack of cybersecurity skillset by the local team is a barrier to adoption, and quite often any attempt to secure an industrial network rarely makes it below the industrial DMZ.
The solution depends on two factors – visibility and automation.
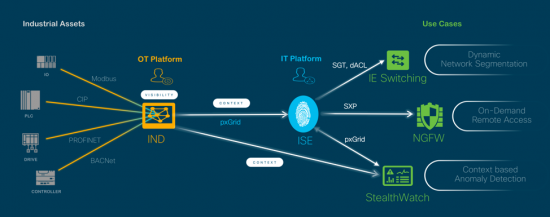
Cisco has integrated its Industrial Network Director (IND) and Cisco Identity Services Engine (ISE) platforms using the pxGrid infrastructure to provide such a solution.
IND is an industrial network management system built to meet the needs of OT personnel managing the industrial process network. With its built in industrial protocol stacks, IND is able to discover industrial endpoints such as controllers, IO, HMI, drives etc. and visualize a converged topology map of the industrial network and the control devices. By providing visibility of these industrial assets to ISE, a whole slew of existing Cisco differentiating security capabilities such as Scalable Group ACL (SGACL) segmentation, Scalable Group Firewall (SGFW) rules, Context based Host Groups etc. from the enterprise space to are made relevant on the industrial network.
By integrating IND with ISE, we are able to create a unique value proposition where IT is able to manage the security infrastructure and define security policies on the industrial network, while OT is in control of granting visibility to industrial assets and providing context to plant floor operations.
Here are a few examples of OT personnel implementing IT defined policies:
- Dynamic Network Segmentation:
Ability to segment the industrial network such that only certain assets can communicate with each other. Using IND, OT personnel can apply policies to assets with a click.
- On-Demand Remote Access
OT personnel can allow a machine builder remote access on demand. Using IND, OT personnel permit remote access to a specific asset by modifying the asset attribute tag.
- Flow Based Anomaly Detection
When an asset exhibits suspicious traffic patterns, IND can provide detailed information about the suspicious asset by communicating with the visibility tools directly.
For more details on how Cisco turns visibility and intent into Network policy with IND and ISE view this short video.
Using this framework, OT is not only able to seed the security platforms with the identity of industrial assets, but they can use the integrated topology map of process network on IND to express intent. By grouping and tagging assets on the IND user interface, OT users can signal intent over pxGrid to dynamically select IT pre-defined security policies on ISE. This run-time automation of selecting security policies eliminates the dependency that local OT team has on the remote IT team to accommodate changes, and enables them to run a secure plant floor on their own operating schedule. Such a framework allows for IT experts to own the security infrastructure and maintain a secure industrial network, while putting control back in the hands of OT personnel by giving them the ability to express operational intent and automatically have the system select the appropriate IT defined security policies without requiring network or security skills.
Come visit us in Hall 6.0, Stand #G30 at Hannover Messe from 23rd – 27th April 2018 to see all the use cases in action!
You can learn more about the demos in the pre-show blog.



