For several years now, Cisco has been advocating for Fog Computing as an essential element of a scalable, reliable and cost effective IoT architecture. By developing Industrial IoT solutions based on Cisco IOx, data originating from “things” can be locally filtered, analyzed and manipulated on IIoT routers and switches deployed at the edge of OT infrastructures. Processing data at the edge mandates the development of security and privacy best practices to arise within a Fog Computing environment. It is not only about protecting data transported through the Cisco IOx devices, but also securing Fog Computing data and applications potentially running on hundreds to thousands IIoT devices.
Security has never been a single feature, mechanism or protocol. It is a multi-layer’s scheme that requires, as when building a house, strong foundations. Combining best security practices for both Cisco IOS network services and IOx computing through each phase of Fog Computing roll-out (as shown on Figure 1), establishes the groundwork.
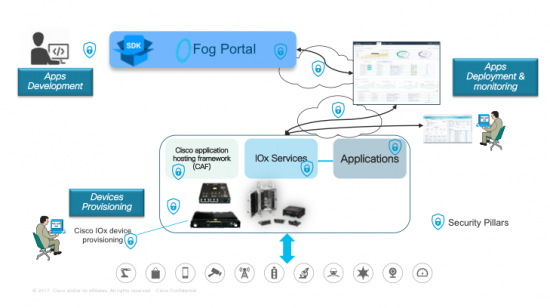
Laying this foundation based on the following 4 security pillars can help IT and operations managers ensure data integrity.
Cisco IOx Security pillars
![]() Access control
Access control
Deployment and management of applications in a Fog Computing environment may dictate roll-based user authentication, enabling the network manager and the applications manager to separately perform their tasks.
- Applications manager authentication performing IOx applications management tasks through Fog Director or IOx Local Manager (i.e. applications’ install/upgrade, start/stop, validate and monitor) can be validated through an Enterprise Radius server, therefore restricting login access to prevent unauthorized users.
- Privileged IOS network manager can perform network performance operations such as device provisioning (i.e. IOx network’s interface configuration and troubleshooting, Guest-OS start/stop, and login access) with the correct remotely or on-site, just based on their “role” rather than login or location.
![]() Integrity
Integrity
While hardware and software integrity of Cisco Industrial IOT devices was discussed in [hardening], a Fog Computing environment requires additional capabilities to ensure the robustness of the IOx platform’s security, such as:
- Digitally signed Guest-OS software bundled with Cisco IOS or compute module images, and leveraging Trust Anchor Module (TAM) capabilities from Cisco ACT2 chipset, help ensure integrity of the operating system.
- Isolation of applications either deployed as Docker, leveraging Docker Tool Chain when building an IOx container application, Platform as a Service (PaaS), Linux container or Virtual Machine (CGR 1000 Compute module only), protect resources and applications.
- Application signature validation, verifies the identity of the source when deploying applications. It may leverage a Trust anchor based on RSA private key (PEM format) to sign the package and x509 client certificate (PEM format) included in a signed application’s package. Mandating the installation of signed applications is managed through all IOx tools (IOxclient, IOx Local Manager and Fog Director) to avoid uncontrolled code.
- Secure delegated access through OAuth API, authenticates access to the API on a user’s behalf, without an application accessing username or password.
- Pluggable authentication module (PAM) mechanism allows developers to benefit from multiple low-level authentication schemes through high-level application programming interface (API).
![]() Data confidentiality and privacy
Data confidentiality and privacy
Fog nodes may run applications which require data to be stored locally either on embedded flash or mSATA SSD drive on new IR829M. Recent IOx release added secure storage services [SSS] capabilities that securely store certificates, keys, and user data in a device. Users and applications can access SSS services running in the host through REST based APIs, through which an application can carve out data encryption. Additionally, application development can benefit from well-known Linux services (Cgroups, SMACK, SELinux, Name Space capabilities…) for additional protection.
Not only data is protection is a must ,but IOx control commands – i.e. start/stop, install/uninstall applications – call for confidentiality, which is achieved through SSL/TLS. This ensures traffic protection between Fog devices and management services, including network file transfer of all files being pushed to the IOx devices. In addition, it is recommended to protect and/or isolate data traffic via best practices leveraging Cisco IOS network services configurations (e.g. IPsec VPN, VRF, VLAN…)
Threat detection and mitigation
Distributed network traffic analysis through IOx applications is another facet of Fog computing. For example, partners like [Sentryo] leverage features such as port mirroring, on IE 4000 Series or IP Traffic Export on IR800 Series to offer traffic analytics software agents, analyzing received and transmitted traffic flows through Cisco IOx devices.
Operations Managers need to detect potential anomalies in applications’ behaviors as well as record measurements for further analysis and capacity planning. Cisco IOx Local Manager and Fog Director tools or APIs enable IOx applications profiling to track consumed computing resources. It is complemented by the automation of Cisco IOx devices provisioning and management as offered by most recent developments done on DNA-C, IoT FND or Kinetic’s GMM, enabling to scale while maintaining security policies across IOx devices.
Let us know other security challenges your organization is facing and come visit us in Cisco Live Orlando World of Solutions and IOx Devnet Zone from June 10th – 14th, 2018 to discuss all security concerns!



