Now, more than ever, we’re living in a world that needs secure connectivity. It’s how we work from home. It’s the most fundamental and essential element that’s driving businesses forward through this global pandemic. And it’s something that you, our customers, have the power to not only enable but accelerate and advance today.
Enabling business continuity
A few weeks back, I wrote about best practices from Cisco’s IT team for driving business continuity – which included discussions on how to enable secure connectivity, collaboration, applications, and how to handle complex use cases. I also introduced Share IT Solutions, a community forum to enable business continuity where IT professionals can:
- Share their IT challenges
- Get input from the community
- Share best practices that enable businesses to thrive
Over the next few weeks, I’ll be sharing use cases, scenarios, and solutions to demonstrate how our customers can take these best practices and apply them to their own businesses. For each use case you’ll have access to instructions, specific code, or demonstrations from the DevNet Automation Exchange.
Today, I’m here to take a deeper dive into connectivity.
Explore the two solutions below to learn how you can advance connectivity for your organization and drive business continuity forward.
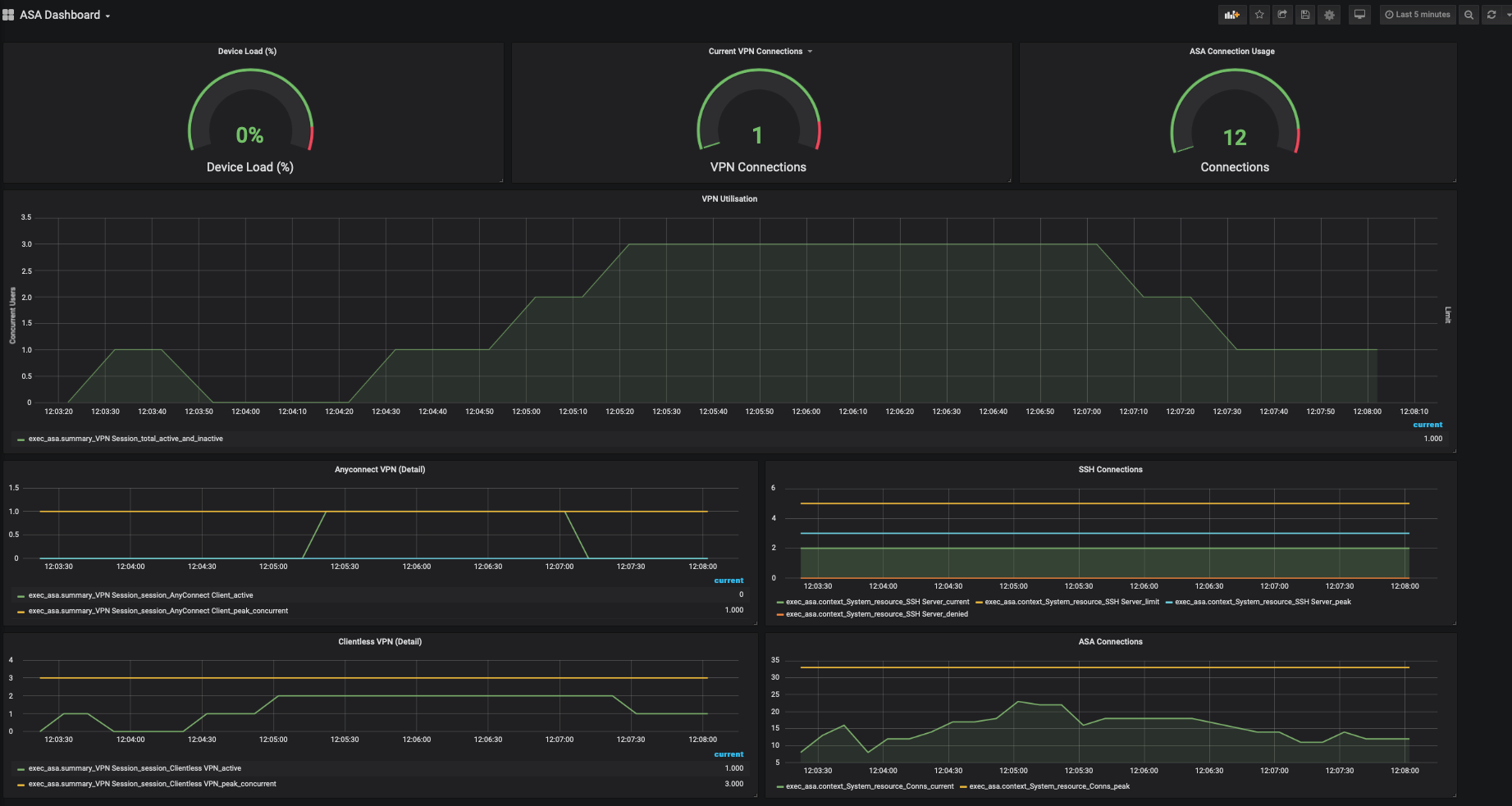
Solution #1: Monitor VPN utilization with the open source TIG data stack
In the past, decisions about Virtual Private Network (VPN) utilization and how to monitor and manage traffic traditionally were made by IT. In a time where everyone is working from home, decisions that used to fall to IT are now business decisions that impact overall operations. That’s why business leaders need simple ways to visualize VPN utilization via dashboards. These dashboards enable business leaders to quickly and continuously monitor VPN utilization to understand trends in usage, when peaks will occur and to monitor for potential risks and issues. Using the open source Telegraf, InfluxDB and Grafana (TIG) data stack, you can collect data from Cisco Adaptive Security Appliance (ASA) devices, store the data, and visualize the data for analysis. To get the code that will enable you to create the JavaScript Object Notation (JSON) output necessary to utilize the TIG stack, visit the DevNet Automation Exchange. Not only does this solution help you monitor VPN utilization today, it will also help you conduct retrospective analysis.
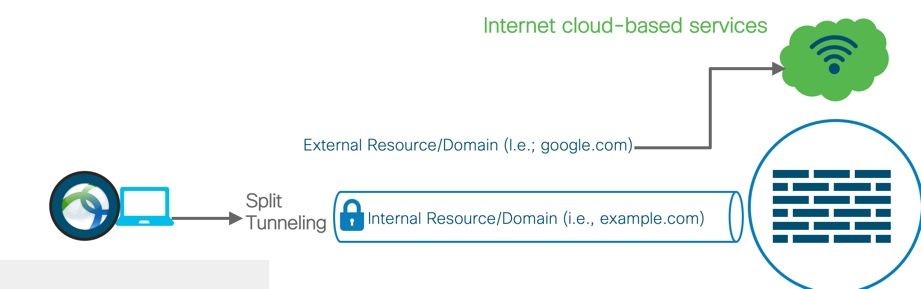
Solution #2: Improve performance of your VPN with dynamic split tunneling
So many users need access to the VPN now that remote work is the norm. And sometimes capacity can be an issue. With dynamic split tunneling, you can exclude specific – typically cloud service – domains, like Webex, from the VPN tunnel. This essentially allows for less traffic flowing through the VPN tunnel, improving the performance of applications and adding capacity for more users. Cisco ASA devices along with Cisco AnyConnect can be configured with this feature, and you can test the configuration in Cisco Modeling Labs (CML) before committing it to production.
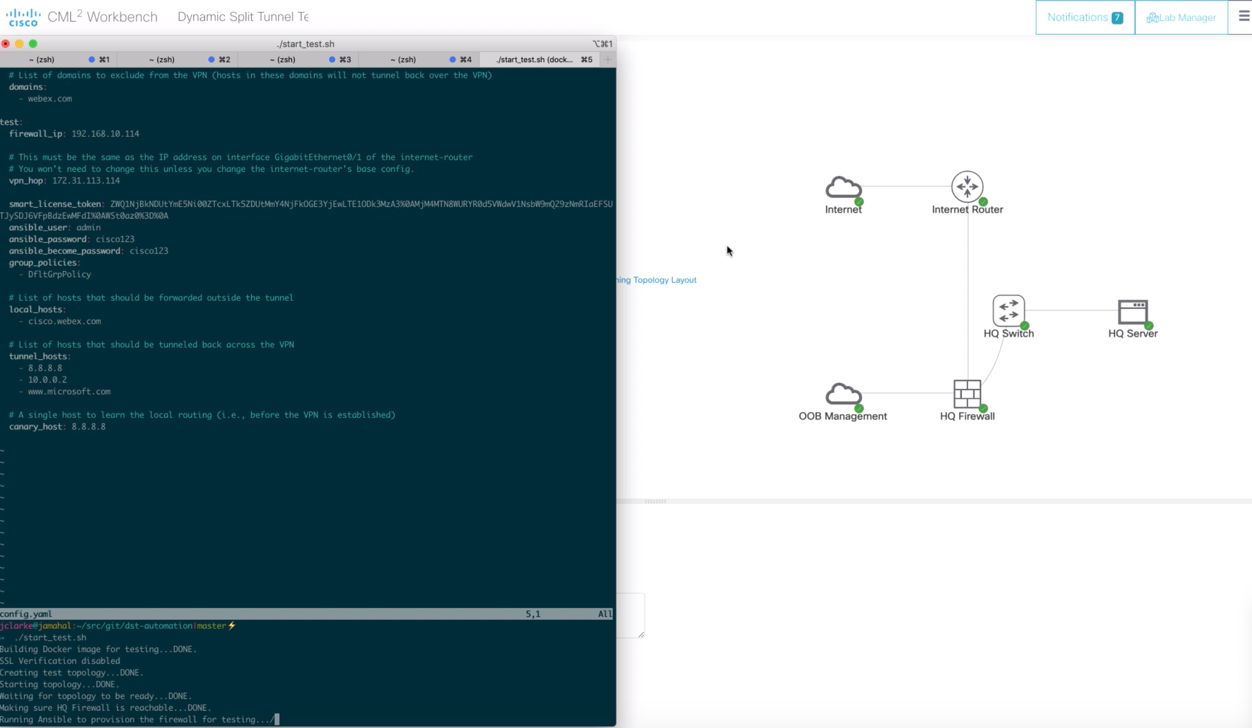
To test and deploy dynamic split tunneling using CML and Ansible, you’ll use an Infrastructure as Code (IaC) workflow. With Python code from the DevNet Automation Exchange, you’ll create a test topology that excludes certain cloud-based application domains from the VPN tunnel. Ansible will translate the code to configuration in a virtual topology that will be tested with an AnyConnect client, and then deployed into production if all tests pass. To get the code that will get you started, visit the DevNet Automation Exchange. To learn how to set this up manually, visit the Cisco community site. By channeling traffic outside of the VPN, you add scale for more users, while at the same time, giving users a better experience with applications.
We invite you to join the conversation
You’ve heard it from us – how we’re providing real IT solutions around connectivity to advance digital transformation and enable business continuity. Now we want to hear from you. Do you have a question about a specific element of your network? Have you been hit particularly hard with an IT challenge that you could use advice to find a solution for? Want to share your own innovation in IT that’s helping your business work from home? Join the conversation, find more use cases, scenarios and solutions in the Share IT Solutions community. Let us know what’s working for you and how we can help curate a solution together.
We’d love to hear what you think. Ask a question or leave a comment below.
And stay connected with Cisco DevNet on social!
Twitter @CiscoDevNet | Facebook | LinkedIn
Visit the new Developer Video Channel





I got a whitelisted IP from purevpn for secure remote access. Surprisingly, it already comes with the split tunneling feature. You can test it to be sure though by getting a trial