Anyone who has followed me on Social (or watched my Snack Minute appearances) knows that I’ve spent a lot of time talking about Infrastructure as Code, especially when it comes to HashiCorp and Terraform. The ability to define infrastructure by its intended end-state – regardless of the order in which the resources used to create that state are defined, and do so across public and private zones – is something amazing to behold. This is especially true because these projects can be contained within a single folder, with very few external dependencies. (Only one, really – to have the Terraform binary installed on the system initiating the workflow.)
The challenge for infrastructure developers
The contained nature and few dependencies make Terraform configuration something that lends itself naturally to being utilized in some sort of continuous integration/continuous deployment (CI/CD) pipeline. Thus, utilizing the same tools that software developers do on a daily basis to drive infrastructure automation at the drop of a git push. The challenge for infrastructure developers is that standard CI/CD processes need to be adapted and tested in depth. The processes need to deal with networks and fabrics requiring well-defined inventories and understanding of the current running environment. State is not something that is generally considered when compiling and building applications because the full source of truth exists within the project or repository. This isn’t to trivialize the process of application CI/CD, but simply to highlight that sometimes the tools available aren’t always easy to build or consume.
Using the standard pull request (PR) workflow to drive automation
There is an easier answer, however, and it leverages the standard pull request (PR) workflow that any infrastructure developer is familiar with to drive automation (and archive the changes being made) within any standard SCM available (including on-prem and SaaS versions). By using a piece of software called Atlantis, some webhooks, and Terraform HCL, we can perform Terraform actions (plan, apply) just by initiating a pull request from the feature branch into main without having to set up complex CI/CD steps to define each stage and action to be performed! In a matter of minutes you can setup and test on your local workstation using a GitHub account and ngrok.
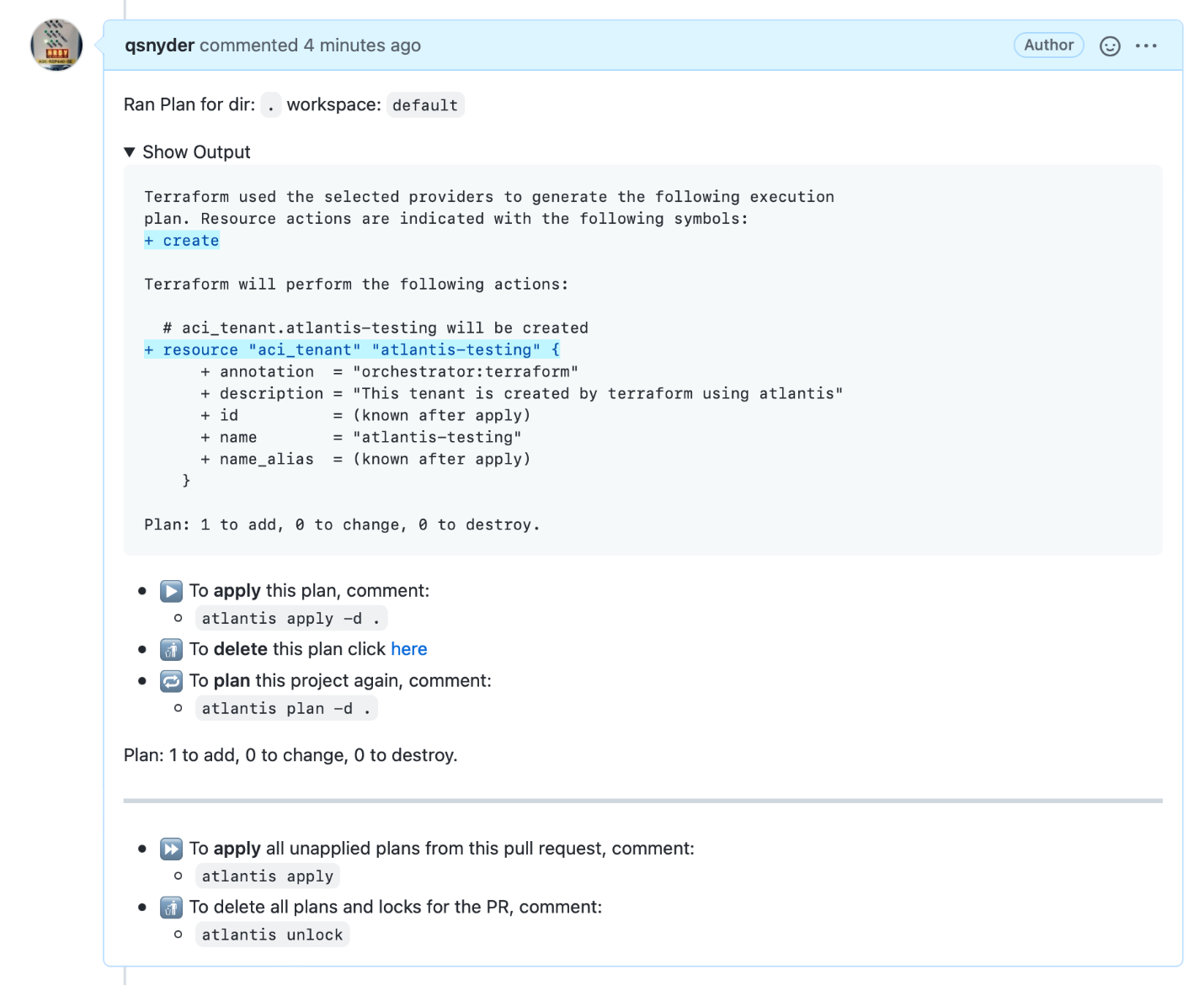
When a pull request is imitated from the SCM, a webhook is fired to the Atlantis server, which will then pull down the committed HCL files in the feature branch and perform a terraform plan command. This output is then displayed within the PR workflow as a comment, allowing all contributors in the repo to see the changes that will be made from the configuration. No more local testing or configuration drift.
When everything looks good, you can apply the changes through a simple PR comment…
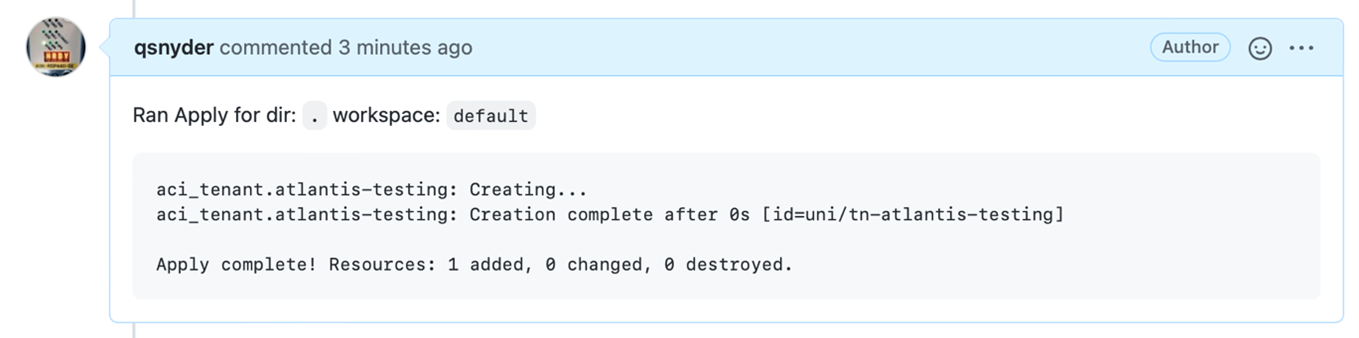
… which will then perform the configuration change on the end target using Terraform and display the results (the same as would be seen when running Terraform locally) within the PR.
Ensure consistency of changes
Additionally, Atlantis ensures that multiple PRs cannot be opened concurrently within the same repository, ensuring that only a single change is being processed at any one time. This ensures consistency of changes and a linear archive of all operations archived within the PR. Once the PR is closed and all changes have been made, the lock on the repository is cleared and further changes can be made.
Live demo of Atlantis in action
For more information, or a live demo of Atlantis in action – be sure to check out my Snack Minute episode (below) where we dive deeper into the setup and running of Atlantis. When you’re ready to try it out yourself, head over to https://www.runatlantis.io where you can explore a test drive or how to enable Atlantis pull-request automation within your own repositories or organization.
See Pull Request Automation in Action with Cisco Application Centric Infrastructure.
If you’re already using Atlantis (or need help getting started), please leave me a comment below or tag me on Twitter with your requests or use cases. I love seeing people building incredible things with Terraform.
We’d love to hear what you think. Ask a question or leave a comment below.
And stay connected with Cisco DevNet on social!
LinkedIn | Twitter @CiscoDevNet | Facebook | Developer Video Channel




