Your organization depends on your network. As networks become more and more complex, the question arises: How do you know what the network is really doing?
Today’s data centers can extend far beyond their on-premises physical location. Data and applications can be with a co-location provider or across multiple cloud providers. For many organizations, data is distributed all around the globe in a web of micro-services and containers and, consequently, outside direct view and control.
With this wide variation of locations, the deployment of Cisco Nexus 9000 switches varies as well. They might provide a Data Center Interconnect (DCI), Cloud to Cloud Connectivity, or external connectivity to sites on the Internet. However, across this vast variation in deployment use-cases, one thing is common—there can be blind spots!
Consider that, whether for the Internet, Cloud Connectivity or Data Center Interconnect, the transport infrastructure is often provided by an external entity. This external entity, either a Service Provider or your Backbone team, more than likely doesn’t give you operational access and visibility into what some might call the “sausage making” of networking. And that limits visibility and therefore control.
Gaining Deeper Visibility
Visibility into transport infrastructure is essential to optimize the efficient and reliable management of the network. Deeper visibility provides key performance indicators (KPI) such as throughput, path information, latency, jitter, and loss. This information assists in rapidly detecting and remediating transient network degradations—those that can only be detected with continuous monitoring of KPIs over time. Even more importantly, recording this data effectively provides visibility back in time to not just mitigate issues, but to identify and correlate their root causes so they can be eliminated before they reoccur.
In the past, IT used a variety of approaches to attempt to collect actionable KPI data. For example:
- Placing compute resources in a co-location for the purpose of collecting telemetry data
- Connecting a server outside the DMZ for the purpose of measuring performance
- Adding a collector to the DCI to provide visibility
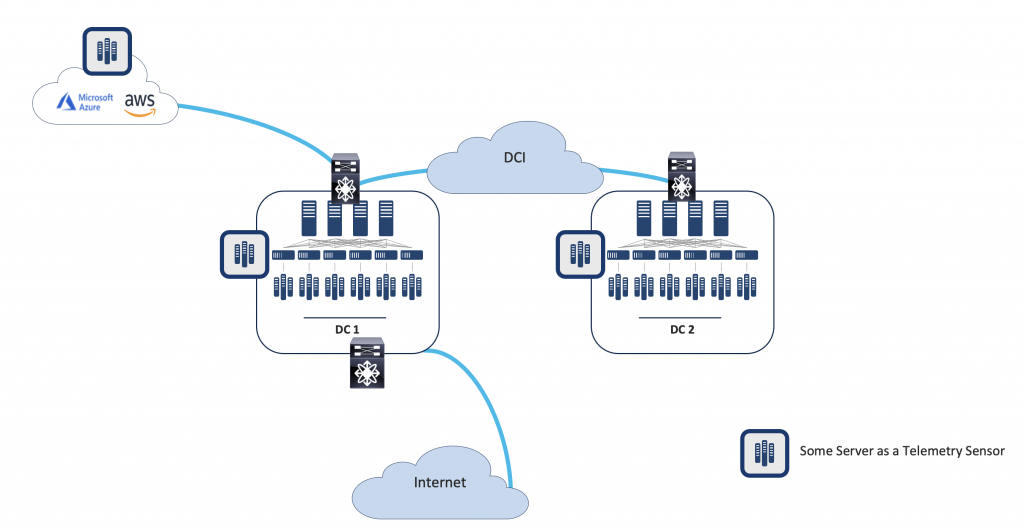
However, as Figure 1 shows, they might not be in the exact data path through which all traffic will pass. Also, using passive data collection does not provide critical visibility into the network paths that data traverses.
Integration with a ThousandEyes
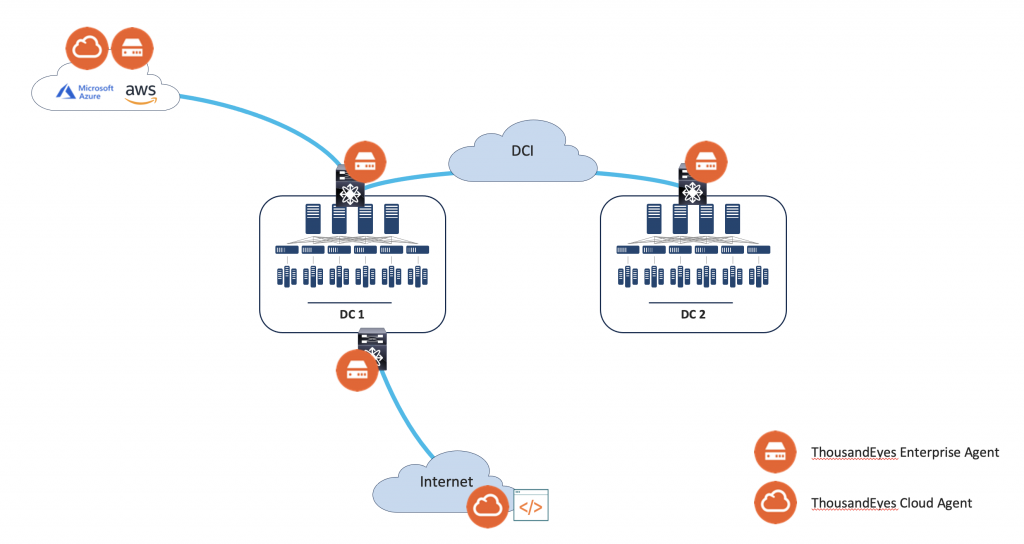
In August 2020, Cisco completed the acquisition of ThousandEyes, an Internet and cloud intelligence platform capable of expanding visibility into, and delivering insights about, the digital delivery of applications and services over the Internet and the cloud. With Cisco’s strong Cloud and Data Center network portfolio, the integration of the ThousandEyes vantage points into the Nexus 9000 enables unprecedented visibility through ThousandEyes from Nexus 9000 switches.
Instead of placing additional compute resources in co-locations, connecting them outside your DMZ, or adding them to your DCI, you can install ThousandEyes Enterprise Agents on Cisco Nexus 9000 switches. The agents measure across the exact paths that data passes gathering crucial KPIs wherever a Cisco Nexus 9000 is present (see Figure 2).
ThousandEyes and Nexus 9000 Integration Details
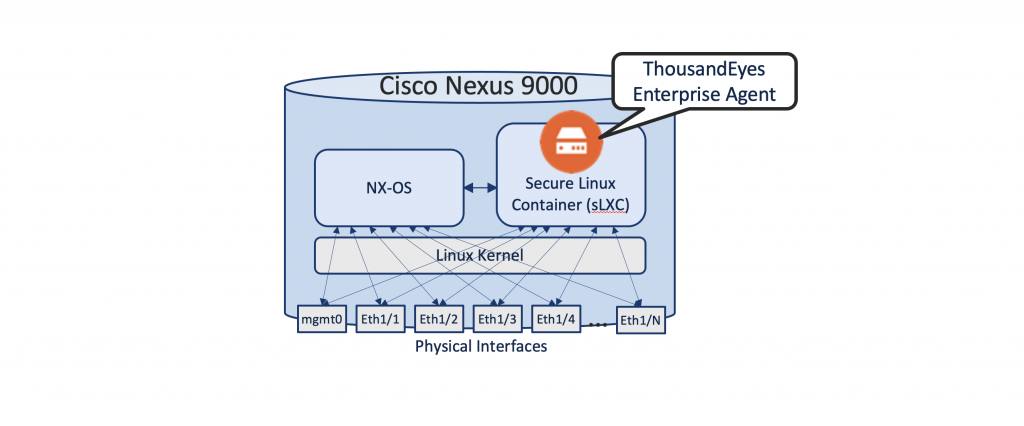
The Cisco Nexus 9000, in ACI or NX-OS mode, provides a hosting environment embedded in the switch’s Network Operating System (NOS) itself. Within NX-OS is a dedicated and secured Linux Container (sLXC) environment for the ThousandEyes Enterprise Agent called Guest-Shell. The agent is hosted in the sLXC and can access the switch’s bridging and routing tables for all its reachability needs. As communication to and from the agent resides in the Nexus 9000 itself, Control Plane Policing (CoPP) can enforce the allowed data-rate for additional protection. Figure 3 shows a schematic diagram of the ThousandEyes Enterprise Agent in a Cisco Nexus 9000 with NX-OS.
Scalability, of course, is a key consideration. With tens, hundreds, or even thousands of switches in a network, simplified agent lifecycle management is crucial. While the ThousandEyes Enterprise Agent can be manually installed into the NX-OS Guest-Shell, the Cisco Nexus Dashboard Fabric Controller (NDFC) provides an integrated workflow to activate the functionality with a single click (see Figure 4).
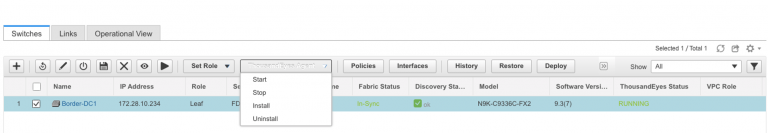
The automated install/uninstall in NDFC, provides all necessary configuration settings so the latest version of the ThousandEyes Enterprise Agent can be directly downloaded from the Cisco Repository. Furthermore, the agent will also be automatically onboarded to the ThousandEyes Dashboard for the Test Setup phase of deployment. While Cisco NDFC provides unified configuration and installation of agents, you can still choose to use other tools such as Ansible Playbooks to perform these tasks.
Better Together for Deep Visibility
Operating a data center network requires a versatile and flexible approach to management with deep visibility into the network, including transport infrastructure. The deep linking and integration of Data Center Interconnect (inter-DC) visibility (ThousandEyes) with data center infrastructure (Cisco Nexus 9000) provides access to the KPIs needed to measure performance, quickly detect and resolve network issues, and correlate root causes to eliminate issues in the future.
Cisco continues to integrate new capabilities into Cisco Nexus Dashboard to provide a granular view into the many corners of the extended enterprise network. Today Nexus Dashboard has deepening integrations with Nexus 9000 switches, Cisco ACI, Cisco NDFC, and App Dynamics. As part of roadmap, Cisco Nexus Dashboard and ThousandEyes integration intends to improve end-to-end visibility from data center, to cloud, to applications and the workforce in the future. With Cisco Nexus Dashboard as a single-point of control for visibility and insights, IT has the ability to foresee and mitigate many of the potential issues that impact the workforce and business operations before they become impediments to progress and profits. And so, the journey continues…
For more information about how to increase visibility into your enterprise and wide area networks read:
Ruling the Hybrid Cloud with Cisco Nexus Dashboard One View



