ShareThis provides a mechanism for web surfers to share content online through a customizable widget. According to the information on their website, ShareThis interacts with “more than 94% of U.S. Internet users across more than 2 million publisher sites and 120+ social media channels.” On the evening of August 21, 2013, ShareThis reported that their website was experiencing “technical difficulties.” They posted a follow-up tweet the morning of August 22 declaring that the service was functioning properly. What ShareThis did not disclose however, was that their GoDaddy domain account was compromised by the Syrian Electronic Army.

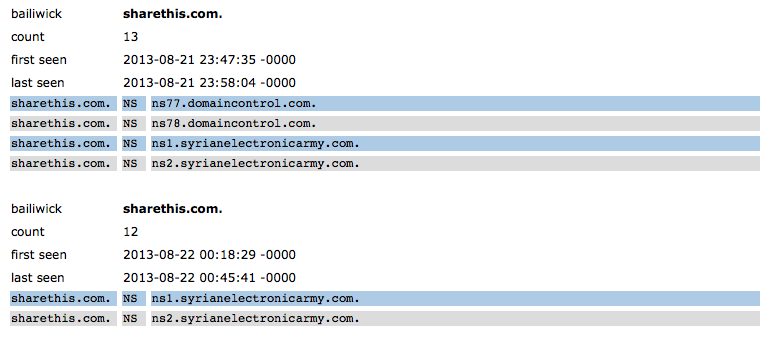
A whois lookup informs us that the “sharethis.com” domain name is registered at GoDaddy, and usually has its nameservers pointed to Akamai. However starting on the 21st of August, the nameservers for “sharethis.com” were pointed to nameservers used by the Syrian Electronic Army. The following data was found in passive DNS. (Please note that domaincontrol.com belongs to GoDaddy)

After the attack on Outbrain last week, and the recent attack on ShareThis, it has become clear that the Syrian Electronic Army has turned to focus not just on media organizations themselves, but also any third-party that media organizations use to load web content. This presents an interesting security dilemma for media organizations and their visitors. Essentially, being only as strong as their weakest link, media sites depending on third-parties for content have increased the chances of their users being compromised by attackers.
There are precautions users can take when visiting media sites. Using a browser plugin such as RequestPolicy is one tool that can help keep you safe. This Firefox plugin restricts your browser to only load content from the domain located in the address bar. You can right click to bring up a menu which enables you to load specific third-party content you wish to allow.






The SEA controlled Domains total 3 and are operating from Moscow Russia, with the obvious permission of Russian state security, which was not reported and the Name Server is at the same IP.
Hosted @ 141.105.64.37 in Moscow Russia
Domain WhoIs & Name Server
1 qatar-leaks.com
2 sea.sy
3 syrianelectronicarmy.com
4 ns1.syrianelectronicarmy.com
The Go Daddy whois shows “Updated Date: 2012-01-05 17:06:02”. If the account at the registrar were compromised, wouldn’t this date be more recent? Could it be that DNSDB detected instead a DNS poisoning?