While I love our ops guys, to be honest, ops reports can be eye-wateringly boring. However, our spreadsheet Jedi recently pointed out something that was, instead, eye-opening:
The number of Cisco Network Services Orchestrator (NSO) device licenses we are selling (actual licenses, not through ELAs, etc.) has been doubling year-over-year for the last couple of years and the momentum doesn’t appear to be abating. That, if nothing else, shows that infrastructure automation has reached a tipping point. Today, most organizations, service provider and enterprise alike, now get that automation is a core competency: if you are not automating your business processes you will lose to your peers that are because they are going to have advantages in with both cost structure (hence, pricing and profitability) and the customer experience they can deliver.
Web companies like Google, Facebook and Netflix made a compelling case for the benefits of automation and inspired many of our customers to embark on their own automation journey. However, our customers soon discovered that everyone’s journey is unique. Web companies have a level of control of their hardware and software infrastructure that typical enterprise and service provider operations teams could only dream about. Almost every data center I have ever been in is like a scrapbook of every IT trend that caught someone’s eye. While web operators get to automate customized software stacks running on sleek, new bespoke hardware, for many of the rest of us, trying to automate is like trying to run the Iditarod with a llama, a cassowary and a hedgehog. We have seen a lot since NSO (then Tail-f NCS) first went into production in 2010 and I can tell you, the road to automation is not always pretty (that hedgehog gets cranky). In the intervening nine years we’ve shed some tears and maybe a little bit of blood but NSO, today, reflects the accumulated wisdom of every lesson we have learned walking side-by-side with our customers on their automation journey.
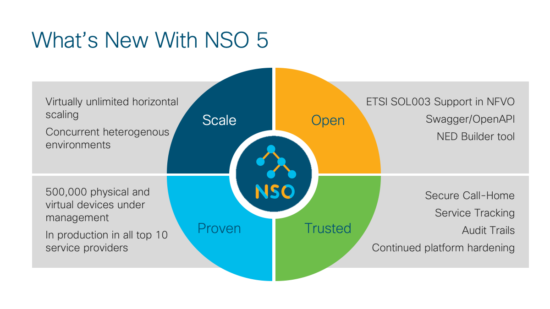
Longevity is not always viewed as a positive in our industry, but I would argue this is one area where it truly matters: we have solved customer problems that others have not even seen yet. Our latest announcement, NSO 5 is a perfect example of that. We are moving beyond “Automation 1.0” fundamentals and starting to address what comes next as you try and scale your automation tool chain across vendors, across technology domains, across services and across locations:
Let’s start with open as that has been part of NSO’s DNA since day 1:
- Swagger/OpenAPI support – OpenAPI is an API description format for REST interfaces. An OpenAPI file can be written in YAML or JSON (so machine and human readable) and can describe the entire API. Swagger is a set of open source tooling that allows you to design, build document and consume REST APIs.
- Network Element Driver Builder – A tool that allows you to generate your own network element drivers (NEDs) for NETCONF devices without manual steps
- ETSI SOL003 – On the Function Pack front, we’ll be releasing support for the ETSI SOL003 specification for the NFVO Function Pack. One that note, we are also running early customer trials for SOL001, SOL004 and SOL006 support
Scale is one of those “what’s next” topics. Automating a single service or a single domain is one thing. Automating multiple services across multiple technology domains at global scale is something else. As the span of control of your automation tooling expands, you inevitably run into issues where the YANG namespace or NED versioning for one service or technology domain conflicts with another service or domain. With NSO 5, we are releasing an “under the hood” change to address these growing pains in the industry around YANG-driven physical and virtual network equipment. This feature simplifies your ability to automate a heterogenous environment and allow services and infrastructure to evolve at their own rates. In fact, it provides a simple way to canary test new devices or services. Paired with our Layered Service Architecture (LSA), CDM allows almost unlimited horizontal scalability.
Finally, we touch on the topic of trust. While automation can undeniably benefit an organization, at some point we need to acknowledge that it can be a tool to do a great deal of harm, at scale and at machine speed. This is a topic we have been thinking about for some time. While NSO has always used templates and automated compliance checks to help secure infrastructure, NSO 5 introduces a number of new features:
- Secure Call Home – RFC 8071 support allowing devices to securely call home for management after a cold start without needing to open ports on the device
- Audit Trails – Fine grained audit trails of the nature and content of changed performed by NSO at the device and service layers
- Service Progress Monitoring – monitoring of service delivery times and ability to alarm SLAs in jeopardy or in violation
NSO 5.0 has been in early field trials with select customers for a while and has gotten positive reviews. NSO 5.1 will become orderable on 10 April and NSO 5.2 will be available at the end of June. If you are not yet familiar with NSO, you can download a free copy for non-production use by heading over to developer.cisco.com/nso – that site also has a ton of resources to help you get started.
Finally, if you are going to be at Mobile World Congress in Barcelona this week, swing by the Cisco booth to chat with the team and check out the demos—we are in Hall 3, booth 3E30.