
authored by Andrew Turner, Cisco Cybersecurity Manager
Data: the currency of all modern companies. Successful acquisition, secure storage and accurate analysis of data can uniquely position companies for competitive success, and as many examples have shown, failure to secure that data from breaches can be extremely costly.
According to the 2018 Cisco Cybersecurity Report, data breaches are occurring with alarming frequency and scale. In addition, human error, system failure, and other internal attacks represent nearly half of all data breaches in an environment focused on external threats. Often these breaches go undetected for weeks, even months.
Service providers have tremendous access to data from many sources and have made tremendous efforts to secure it. But with mass-scale network changes like the move toward 5G, virtualization, and IOT, service providers face increasing challenges as the attack surface grows larger and attack opportunities increase.
So how can service providers detect and repair data breaches quickly and completely? Leveraging Cisco Stealthwatch, a proven technology in big data, analytics and machine learning, Cisco is pleased to announce enhanced visibility for service providers in the LTE evolved packet core (EPC) and 5G converged packet core and network slices. Stealthwatch for EPC allows an operator to quickly and easily identify, investigate and remediate when elements in the core violate standard behaviors; and allows greater simplification of EPC operational controls and enforcement.
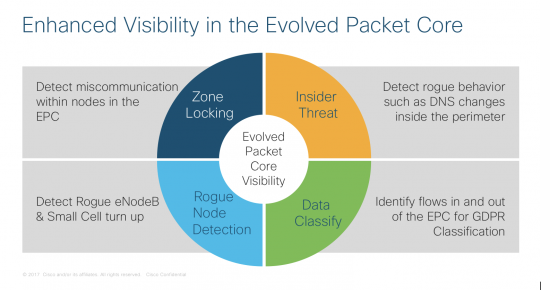
In addition, Cisco Stealthwatch for EPC uses big data analytics and machine learning across the infrastructure to detect data breaches and threats coming from within the network. These insider threats can come from rogue employees or the unauthorized use of valid login/passwords through email phishing. Detecting such internal attacks requires the ability to determine a change in intent on the part of the user, and are therefore harder to detect and prevent for traditional enforcement techniques.
Looking out to the edge, maintaining the operational integrity of the Radio Access Network (RAN) by detecting rogue eNodeBs can be a challenge. While options such as security gateways can mitigate the risk, it is not always practical to deploy security gateways in every location. Where they are not deployed, it is often impossible to ensure that rogue eNodeB and small cells are not being brought up on the network. By deploying Stealthwatch for EPC, an operator can be alerted the minute any eNodeB registers to the network and can then investigate if it’s a planned maintenance or a potential rogue. In this case, timeliness really matters.
Finally, as the regulation and compliance of data breaches continues to grow with examples of legislation such as the General Data Protection Regulations (GDPR) in the European Union, it is critical for the operator to be able to identify the flow of data in order to classify and protect it. Traditional perimeter enforcement techniques are very good at identifying what is blocked but identifying what passed through is much more difficult. Leveraging Stealthwatch for EPC, operators can now identify what flows pass in and out of the infrastructure and from there classify and protect critical data. Stealthwatch for EPC acts as the digital general ledger for network activity on your infrastructure.
The power of Cisco Stealthwatch for EPC in all of these use cases are applicable in LTE and 5G architectures and help service providers maintain operational integrity, manage risk, and secure customer data.
If you’re attending Mobile World Congress in Barcelona this week, stop by the Cisco booth and see a demonstration of Cisco Stealthwatch for EPC:
- What: Secure Your 5G Network
- Where: Cisco Security area inside Cisco Booth, Hall 3 Stand 3E30
- When: February 26-28 from 9a-7p | March 1 from 9a-4p




