October was National Cyber Security Awareness month and there’s been a lot of talk about how organizations should be doing more to protect their networks. One of the current trends in cyber security is that organizations are increasingly turning to trusted partners like Cisco for some or all of their incident response capability.
As a member of Cisco’s Incident Response Services team, I am regularly called upon by our customers to provide incident response (IR) expertise ranging from assessing a current IR process, building an IR program from the ground up, or assisting the customer in responding to a cyber incident from initial identification right through to remediation. When our team works with a customer on an active incident, we employ not only highly trained and experienced responders, but also all the gear that they need to get the job done.
A “go-bag” is a term used in a number of professions where unscheduled or last minute travel is common. While the contents may vary, the general idea is that a go-bag should be pre-packed with all the items necessary for a person in that profession to work away from their “normal office” for a number of days. For the Cisco Security Incident Response team, go-bags consist of all the tools required to land at a customer’s site within 24 hours of an urgent call-out.
At the core of our Cisco IR go-bag is a custom-built laptop to handle simultaneous data collection and analysis. The laptop is a little “chunkier” than most laptops found at a computer or electronic store. For starters, it has multiple solid state hard drives (SSDs) which run faster and more efficiently than traditional hard drives with no moving parts. This gives the laptops the ability to read, write and store large amounts of data very quickly.
In addition, the IR laptop has approximately four times the amount of Random Access Memory (RAM) that a system sold at a big box electronic store would. RAM holds data in current use “in memory” so that it doesn’t have to be constantly pulled from the physical SSD storage each time it is needed. RAM is volatile which means the data is only held as long as the computer has power. The more RAM, the faster a computer can process data.
Lastly, the Cisco IR laptop has a quad-core processor. The processor is the brain of a computer, and the more cores, the more activities the computer can accomplish at the same time. All these pieces together ensure the laptops that Cisco IR Analysts carry are more than powerful enough to collect and analyze data while in the field.
The next essential pieces of the IR go-bag speak to the ability to collect data from a customer’s environment in a manner that is considered “forensically sound”. This means that the data collected is unchanged from the original media (hard drive, USB, CD, etc.) from which it was sourced, and is accomplished using a device called a “write-blocker”. The write-blocker is deployed between the original media and the IR laptop during the data collection task, and, as the name implies, ensure that no changes are written back to the original media.
This provides a perfect segue to the next item. If the laptop is the media on which the copy of the data is stored, and the write-blocker ensures that there are no changes to the original media during the collection, how or what does the actual collection? And how do we ensure the copy is exactly the same as the original?
Cisco IR analysts are equipped with licensed forensic software that accomplishes both collecting the data, and ensuring the data is what was expected. Collecting the data via forensic software usually means creating a bit-for-bit copy of the original media. After the copy is complete, the forensic software takes the additional step of creating a hash of the original and the copy, and comparing them. A hash is a one-way cryptographic function that creates a fixed-length sequence from a variable-length string. It is essentially a digital fingerprint. If the copy is even one bit different from the original media, the hashes will not match. This is important to be able to prove, perhaps in a court of law, that the integrity of the image collected is intact from the time of collection through to completion of analysis.
Depending on the analyst, the rest of the go-bag may include various boot disks, an array of cables, small toolkits, cameras, anti-static bags, labels and multiple external storage drives to ensure all data can be collected.
Last but certainly not least, the bag itself is very important. A go-bag must be able to fit all the gear required and perform well over many miles and several years. A go-bag should have:
- one or more padded sleeves for laptops,
- enough main storage for write-blockers, power packs and cables,
- secure compartments for fragile items like hard drives and,
- plenty of small pockets for items like pens, batteries, phones and sticky notes.
Going on-site to assist a customer with an incident means sometimes meeting them for the first time on what could be the worst day in the history of their business. A fully-stocked and functional go-bag means the Cisco IR team can hit the ground running, and goes a long way to helping that “worst day” be the first step toward a better year.
And while this blog describes the contents of Cisco IR’s go-bags, your organization may want to consider building your own go-bag. The items you need may be the same or completely different, but being prepared will help make your response to any incident faster and more efficient.
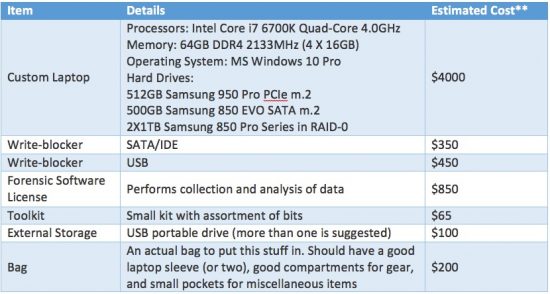
If your organization is considering putting together a go-bag, use the table below as a base for what you might need:
**All prices are estimates in USD and will depend on actual specifications and brands**
When responding to a cyber security incident, preparation goes a long way toward decreasing time to detection and resolution of an incident. In addition to building out your go-bag, this white paper provides additional insight into how you might build out your own incident response capabilities. And, of course, consider engaging with our Cisco Incident Response Services. We’ll help you prepare and respond to incidents, and our go-bags are already packed.






Very good article, well worth the read. My only comment was that it would have been nice to have listed some Forensic Software that Talos recommends or has at least used in the past to complete the article.