What is Email Spoofing?
Email spoofing is the creation of email messages with a forged sender address for the purpose of fooling the recipient into providing money or sensitive information. For example: a sender 401k_Services@yourcompany.com sends a message to your business email address stating that you have one day to log into your account to take advantage of new stock investments. The message uses your company’s letterhead, looks as legitimate as the 401k notices you’ve received before and has a login link.
Spoofing attacks became very noticeable in mid-late 2015 and more prevalent in early 2016.
What is it costing companies?
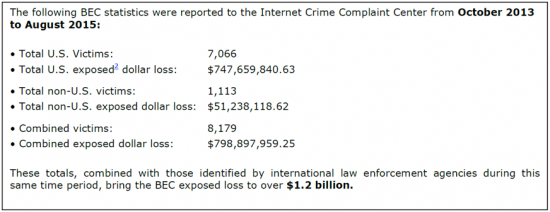
In August 2015, the FBI issued a public notice indicating that Business Email Compromise (BEC) is estimated to have cost companies over $1.2 billion between October 2013 and August 2015. Spoofing is one of many forms of BEC. See table below for more details.
A Recent Attack
In one recent example, employees of a Silicon Valley tech giant were warned to be on the lookout for email phishing scams directed at finance and HR personnel. A week later, on March 1, 2016, the company suffered an email attack impersonating the organization’s CEO that requested all of the employee W-2 forms. Subsequently, the 2015 W-2 tax form information for current and former U.S.-based employees was sent to an unauthorized third party. The employee responding to the request believed it was a legitimate internal business email.
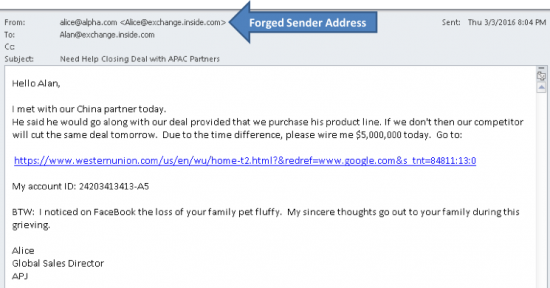
Typically, the forged address is owned by a fellow employee that the attack victim trusts. A particular category of spoofing, called whaling, involves a victim who is a high value target such as a CFO, CEO or CIO. Criminals involved in whaling perform extensive social media research prior to their attack. Figure 1 is a fictitious example of an attack on Alan who is an executive at the company called Alpha. The attacker sends this message to Alan from outside of the company. The forged address is owned by Alice, Alpha’s Global Sales Director, who is in Asia at the time of the attack.
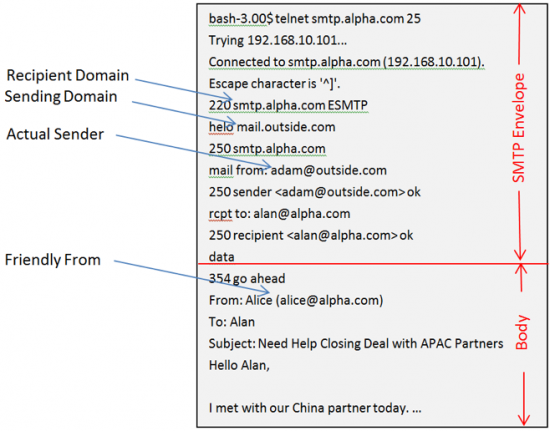
The spoof in Figure 1 is created by the attacker, Adam, in Figure 2. Adam, who lives in the domain outside.com, opens a telnet session to the victim’s mx record for alpha.com. Typing into his PC, he introduces his domain with “helo outside.com”, his real “mail from” address adam@outside.com and then the recipient’s address. In figure 2, this is identified as the SMTP envelope. Like a physical envelope in the mail system, with the city and street address on the outside, its purpose is similar for determining where the digital message is delivered. Email servers and gateways read the SMTP envelope, and people read the message body. The fact that Mail From doesn’t agree with the Friendly From makes this a forgery. The challenge to the mail recipient is that SMTP envelope information is not readily available, particularly on smartphones.
How can you protect yourself?
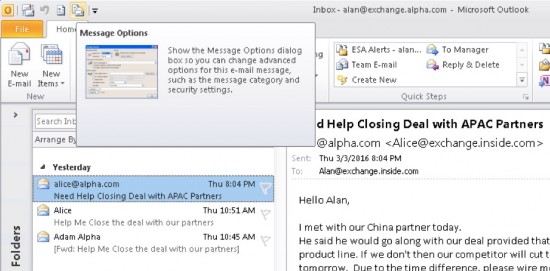
Spoofers play on an employee’s fear of consequences, a sense urgency that leads to dismissing careful verification in favor of quick reaction. In these situations it is better to slow down and use available tools. Mail user agents, like MS Outlook, can compare the Friendly From address in the body with the Mail From address in the envelope. In Outlook 2010 you can do this with the following two easy steps:
- Select the message and then select Message Options in upper-left tool bar, as shown in Figure 3.
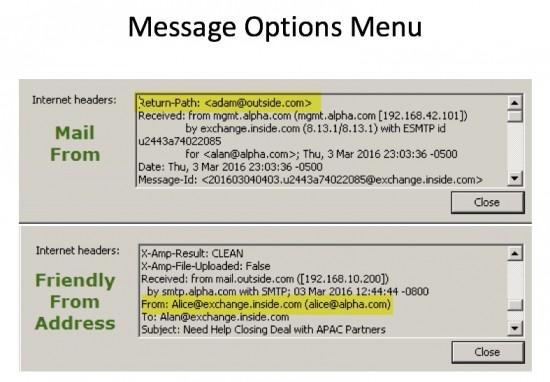
- Inside the Message Options menu, you can compare the Friendly From and Mail From addresses as shown in Figure 4.
All mail user agents have this ability. If this message were received by a Cisco customer, the next step would be to notify the company’s mail administrator and they would interact with Cisco support, or their Content Security sales team, to configure the needed filters that compare these address fields.
What about smartphones?
Typically mobile devices are too small to compare the Mail From and Friendly From addresses. If you suspect that your mobile device received a spoof, then you should wait until you have access to your laptop for more detailed verification.
To conclude…
We at Cisco continue to educate our email security customers and partners on how to use the current product features to combat this trend. And our email security engineers are building an even stronger automatic defense against spoofing and whaling attacks and integrating these into our Email Security solution. We offer a suite of anti-spoofing tools that include: DKIM, SPF, DMARC and content filters that verify the authenticity of the sender and allow administrators a choice of remediation.
For those of you who already own our products, please visit our new Email Security Best Practices page to obtain in depth information about how our solutions work to help you combat spoofing.
To learn more about Cisco’s email security solutions, please visit www.cisco.com/go/emailsecurity.






Nice article!
Good easy-to-follow advice for checking the validity of email. The Nigerian and Eastern European fake emails were easy to spot once upon a time, but are getting more and more difficult to weed out now – especially from phones when on the go. Good advice from Kevin on saving anything slightly suspicious or in need of anything more than a simple reply for the computer!
The bigger question is why are many email servers accepting spoofed or aliased messages from untrusted servers at all?
Placing filters that compare Friendly From and Mail From fields can lead to false positives. There are examples of ligitimate mail where these are different; a bounce message, a healthcare provider or 401K provider that sends mail internally and uses the companies mail domain.
well explained Kevin