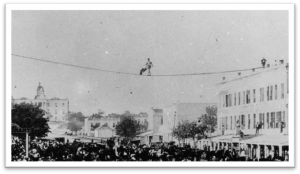
Here at the RSA Conference 2016, the theme this year is Connect to Protect. It is a fitting theme for a gathering of security professionals, given the widespread adoption of cloud and mobile technologies that make doing business and sharing information easier than ever. The need for securing data regardless of where it resides and is consumed thus becomes paramount. In my recent discussions with fellow conference attendees, a common thread has emerged: a major impediment to protecting data in the cloud and on mobile devices is usability. This need for end users to walk a tightrope between security of data and usability of the technologies that ensure efficient access to secured data has confounded IT professionals for years – requiring multiple steps for a recipient to read an encrypted email, for example, can frustrate users and lead them to seek less secure alternatives.
It is encouraging to see efforts being made on multiple fronts to address this “security v. usability” problem. Take email, for instance. There has been a movement towards secure SMTP over TLS by some of the more popular email providers including Google, Yahoo and Microsoft. They’ve introduced Transport Layer Security for both inbound and outbound email to protect the contents of messages, as well as to prevent sender and recipient spoofing. However they’ve only largely implemented opportunistic TLS, which while easy to enable, risks creating a false sense of security for senders of sensitive messages. Most recently, we’ve witnessed the roll-out of Google’s “open padlock symbol” to show when emails are received in clear-text. I’ve been anticipating this functionality for years. We routinely look for the locked/unlocked symbols in browsers that show us whether we are using HTML or HTMLS. Why not have a similar security symbol for email? Because of the traffic between these large email providers, between 50% and 60% of emails received by or sent to Gmail are now sent via TLS, thus securing them in transit. However these figures hide significant gaps. According to a recent report, of 700,000 other SMTP servers, only 35% are properly configured to allow server authentication for TLS. This is troubling because opportunistic TLS, by default, fails-over to clear-text transmission. It is particularly concerning because over 40,000 of these servers, in 193 countries, were found to have software corruption that prevented the operation of the STARTTLS command, thus potentially allowing eavesdropping.
A major factor that has held back widespread use of properly implemented email encryption is the user burden introduced by antiquated email encryption solutions like Pretty Good Privacy (PGP). This no longer has to be the case and some modern day email encryption solutions alleviate past challenges.
For example, our ZixGateway with Cisco Technology (ZCT) solution allows email encryption to be truly as simple as regular email. ZCT delivers highly secure email communications transparently, from inbox to inbox, with little or no additional steps required. Furthermore, ZCT customers become part of the largest email encryption community in the industry, with over 50 million members and growing. With ZCT, an organization’s private keys are kept under the control of the owner organization. ZCT combines the ease of use of Zix Email Encryption with the trusted delivery method of Cisco Post-X Envelope (PXE). PXE allows messages to be encrypted with a private key on a per-message or per-recipient basis, and even allows access to an email to be rescinded on a proactive basis. And thanks to ZCT’s Best Method of Delivery, mobile recipients are at most 2 taps away from accessing highly secure email on any device without the need for standalone apps.
Security versus usability is a major consideration when it comes to new innovations in IT. Thankfully, for email encryption, the balancing act is no longer difficult. If you’re interested in learning more, watch this quick demo video of ZCT in action.





