Lately, there are days I wake up and find it hard to believe it’s been 3 years since we began our Incident Response (IR) practice within Cisco’s walls. Coming in on the ground floor of such a monumental and important offering to our customers gave us the unique opportunity to define and shape our practice as it should be, without any baggage from the past. This allowed us to attract some of the best talent, grow extremely quickly, and assist our customers in both a proactive manner to shore up their defenses ahead of an issue as well as in a reactive state when the inevitable finally and unfortunately does happen.
As our team works through the process of assisting a customer during an emergency response, we constantly make recommendations, either tactical (e.g. you need to reset all your passwords), or strategic. Those recommendations vary from customer to customer and environment to environment. As I look through our recommendation data, I see some patterns that might be useful to share with the larger community. To that end, I present to you the top 5 IR recommendations that our IR team provides to our clients, along with some of my own insights on why we recommend them so often.
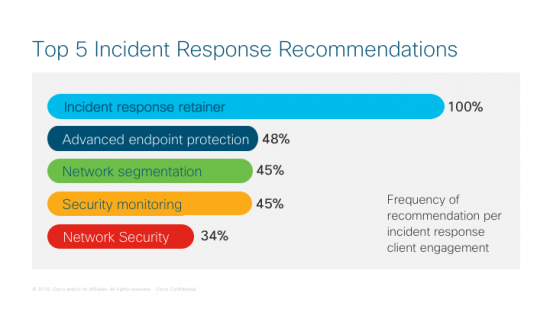
#1: Incident Response Retainer
It should be no surprise that we recommend an incident response retainer – it’s the cornerstone of our own portfolio. So, yes, you could argue we are biased on this one, however, simply put: there is a reason we are performing the emergency response in the first place. In this day and age, no company should go without having an incident response retainer, if not two or three IR firms on retainer – and, I don’t mean the zero-dollar some vendors ‘sell’ (remember, you get what you pay for).
It is extremely important to have independent firms you can partner with during a time of crisis. For example, at Cisco, we have the ability to bring in not only our IR team, but our Talos threat intelligence organization, crisis communications experts, product teams, project managers, and more. This is extremely powerful and helpful during a crisis. Additionally, the firm on retainer should not be passive. They should work with you throughout the year to shore up defenses via table top exercises, enhancing plans and playbooks, and even proactively and independently hunting for adversaries. At the end of the day, it should be a true partnership and when a partnership is involved, a crisis will go much smoother.
#2: Advanced Endpoint Protection
This is the first of two technology recommendations that cracked the top 5. When managing an active incident, a critical capability our responders require is insight into the larger environment and the ability to effectively respond. This is when we typically turn to Cisco Advanced Malware Protection (AMP). Having AMP’s built-in visibility and the response capabilities at our fingertips allows us to respond quicker and more efficiently than we would be able to otherwise. When coupled with other solutions in our Cisco security architecture, Cisco AMP also provides an extremely powerful and cohesive way to continuously monitor and respond to issues on the network.
#3: Network Segmentation
Many a network and organization has been taken down due to lack of controlling devices via network segmentation. We have had the unfortunate duty to work with client after client on fairly basic attacks that have decimated their environment and infected or locked up (via ransomware) hundreds to tens of thousands of machines. Yes, tens of thousands of machines. Additionally, in over 75% of ransomware cases we deal with, the backup server has been encrypted as well. The one item that may have provided a glimmer of hope as we begin to move forward in our initial call. In the past, segmentation was considered either a compliance issue or a way to control access to data. To me, segmentation is a required control mechanism and basic network hygiene.
Interested in learning more about building a better incident response program? Join our Security Webinar on May 10. For a technical demo of Breach Response Tools, register for our May 11 Demo Friday session.
#4: Security Monitoring
This one should be fairly self-explanatory, but it still does not get the attention it deserves which is why it lands so high up at #4. Still, in 2018, too many organizations seem to rely on outside organizations such as the FBI, or security news outlets to inform them that they have a security problem. These organizations should be doing sufficient internal security monitoring so that they can discover – and deal with – security issues on their own.
I have always felt that before you can purchase any security product, the vendor must provide a required resource estimate: an accounting of resources (e.g. people) required to run, configure, maintain, and monitor the product to be successful given the size of the environment. In addition, you must agree to hire and maintain that staffing level (I can dream). Too often tools are purchased as a crutch, and in place of humans, when they should be augmenting them. I recall a recent engagement where the incident response team logged into a security console to see what data was available and found it was lit up like a Christmas tree. The tool was doing its job of showing the alerts – if someone had been monitoring it, a massive crisis could have been prevented.
#5: Network-based Security
This is the final item to crack the top 5, and only the 2ndtechnology recommendation. Network-based security controls should be layered to prevent attacks from web and email-based threats. These controls should include items such as a spam filtering service or appliance, blocking uncategorized traffic at the proxy if possible, and DNS protection services to filter content, block further malware, protect against, botnets, and prevent issues with URL typos, such as Cisco Umbrella. Additionally, implementing these controls allows for monitoring to detect and restrict machines requesting domains associated with attacker activity or malware.
Outside of these recommendations, we do provide other ones on a routine basis such as two factor, penetration testing, and more focus on governance, risk and compliance (GRC). In regards to GRC, it is still surprising how many organizations have not done a basic security assessment and do not have a roadmap to get healthy. This becomes very apparent when working an active incident and the customer lead has a title of something outside of Security (e.g. Networking). Security is still not a priority to some organizations. Unfortunately, in this new era, security needs to be built into everything and everyone in IT needs to be working towards a common goal of protecting the company, its customers and users.
I hope you’ve found this data useful. Perhaps it validates what you see, know, or perhaps are working on yourself. I’d also recommend you check out the Cisco 2018 Annual Cybersecurity Report.
Please leave a comment below if you agree/disagree with these top 5 incident response best practices, or feel free to reach me on Twitter @SeanAMason.






Awesome Sean Mason! Thanks for sharing.
Number 1 is admittedly biased but makes perfect sense in a world where maintaining in-house security skills (with the available bandwidth and agility) is not getting any easier. Good job Sean.