Let’s say that you’re confident in your security posture. You have endpoint protection in place, firewalls defending the perimeter, and phishing filters on incoming email. You’ve leveraged tools to check for anomalies in your network traffic, rolled out an SSO solution, and implemented processes to securely connect to the network remotely.
These defenses make it harder for bad actors to compromise your organization. Not only that, but a strong security posture is more likely to push all but the most motivated bad actors to move on to other, less secure targets.
It’s at this crossroad, between motivation and less secure targets, where supply chain attacks sit. Bad actors will always look for weak points to attack. It may be that your weakest point is not within your own organization, but within one of your suppliers. You trust their products and services, relying on them to conduct business. Unfortunately, if their security posture isn’t as mature as yours, attackers can exploit that trust and use it in attacks.
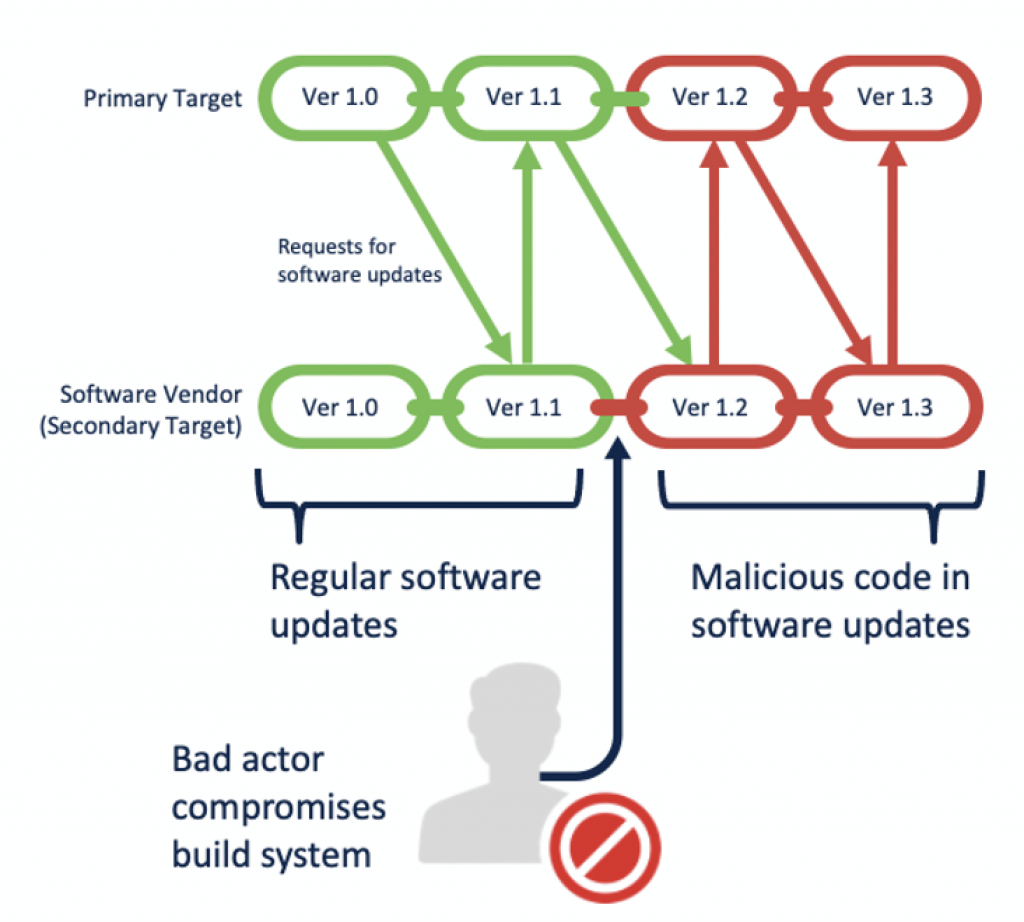
This is what a supply chain attack is. In these attacks, bad actors compromise a secondary organization that supplies software or services to a primary, target organization. Their goal is to compromise the primary target when they use the software or service of the secondary target. In short, they piggyback on the secondary target to get their malicious code into the primary target.
How the attack works
Although there are several ways to attack a supply chain, there is a general pattern seen in many attacks. First, the bad actors gather what information they can find about the external products and services used by the primary target. The attackers assess the suppliers of those products and services and then choose a secondary target, based on what they discover. This secondary target now becomes the fulcrum of the attack.
Next, the bad actors attempt to compromise the secondary target. The ways they go about doing so will vary, often choosing the path of least resistance. They could try anything from spear phishing to exploiting vulnerabilities at the network edge. The choice will largely depend on the secondary target itself—where the attackers perform reconnaissance to determine the approach most likely to lead to a successful breach.
Once in, the attackers move laterally, their objective often being to compromise the secondary target’s software build system, where the source code for their software is stored, updated, and compiled. One of the easiest ways to achieve this is by compromising a developer’s machine, or their credentials, gaining the required access. With access to the build system, the attackers can surreptitiously insert malicious code, like a backdoor or RAT, into the software in question. The secondary target, unaware of the presence of malicious code, compiles the latest updates, signs the binary, and then releases it.
At this point the attackers wait for the primary organization to download and install the compromised update. Once this occurs, the malware phones home and attackers are in, now having access into the primary organization they intended to compromise.
Notable examples
There are several supply chain attacks that have made headlines. One of the most notable happened last year, when bad actors compromised software updates to SolarWind’s Orion IT management software. The attackers managed to stay hidden for months, during which multiple US government agencies and corporations were compromised.
But this attack was far from the first to use a supply chain as a vector. In 2017, the wiper malware NotPetya is believed to have begun its spread by leveraging the update system of the Ukrainian tax software, M.E.Doc. This attack led to widespread compromises in the Ukraine, and across the globe, resulting in billions of dollars in damage.
Later that same year, bad actors managed to insert a backdoor into the popular PC maintenance tool, CCleaner. The compromised versions were downloaded over 2.27 million times, though only a small number of these installs were targeted to receive a secondary payload.
Supply chain attacks can be traced back further than this, having existed for a number of years. While relatively infrequent, likely due to the high sophistication and development complexity, their potency make them a viable option to motivated and well-funded attackers.
The defense dilemma
The toughest part about supply chain attacks is that the vector used to compromise the primary target is hidden within legitimate software. This makes supply chain attacks incredibly difficult to protect against, presenting a number of challenges.
First, supply chain attacks compromise software that your organization already uses and trusts. Inserting bad code into trusted software makes it notoriously difficult to identify the malicious activity.
Good security and software engineering practices within suppliers are indeed a way to combat supply chain attacks. However, audits of suppliers require no small investment of time and money, and don’t always scale across the number and variety of suppliers used by a given company.
Patching is a vital part of any security strategy. It is particularly ironic that in the case of so many supply chain attacks, the malicious functionality is distributed by abuse of the patching and update mechanism by bad actors.
This presents a catch-22, whereby an errant patch could result in a supply chain compromise, but not patching could lead to other security risks, such as exploitation via unpatched vulnerabilities.
Caught in the act
Given the enormity of the task of detecting a supply chain attack before bad actors gain access, in most cases, another approach will be needed. The silver lining here is that, while gaining access can be looked at as the sign of a successful supply chain attack, it’s still only the beginning when it comes to bad actors’ ultimate goals.
The fact remains that the system through which attackers gain their initial access isn’t usually their ultimate destination. An attacker will still have to traverse a network, moving laterally to get to their goal. Also, if stealing information is their aim, they will still need to exfiltrate said data. And through it all, they will need to perform command and control activity to instruct the malicious software to do what they need it to do.
These are all great touchpoints to detect, block, and remediate such an attack. Having policies in place to detect such activity can go a long way to alerting to a supply chain attack, along with a threat hunting program available to look for further evidence of a compromise.
For instance, keep an eye out for any of the following:
- Look for unauthorized changes or unusual software additions on endpoints. Attackers often modify endpoints, or install software like webshells, to further their attacks.
- Monitor for unexpected use of credentials. When machines are compromised, credentials are often scraped and used to log into other devices on the network.
- Pay particular attention to key systems, such as active directory servers or other domain controllers.
Focusing on response
With prevention being difficult, if not an unattainable goal, response becomes a more viable approach to defend against supply chain attacks. One way to do this is with extended detection and response (XDR) solutions. Such solutions give visibility across networks, endpoints, and applications to analyze, hunt, and remediate attacks.
The threat response feature in Cisco SecureX is ideally suited to assist in cases like supply chain attacks. As an integrated security architecture that automates integrations across Cisco Security products, it greatly simplifies threat investigations and responses. And these investigation and response capabilities combined into one convenient, efficient workbench.
For instance, if you suspect a supply chain attack, you can aggregate threat intelligence, drill down to see where specific activity began, track it across the network to get the larger picture, and then take corrective action directly from the interface, blocking suspicious items on the spot.
A critical component of this visibility is Cisco Secure Endpoint, providing both threat hunting and response capabilities in a single solution, leveraging the power of cloud-based analytics. Powerful tools like file trajectory and device trajectory use Secure Endpoint’s continuous analysis capabilities to show you the full scope of a threat and identifies all affected applications, processes, and systems.
Network visibility is critical in detecting attacks as they attempt to move throughout the network. Tools like Cisco Secure Network Analytics can detect suspicious and unexpected activity on the network, as well as data exfiltration, policy violations, and other sophisticated techniques used by attackers. Secure Network Analytics can even analyze encrypted traffic for unusual activity.
In addition, use Secure Network Analytics with Identity Services Engine (ISE) to segment the network. While segmentation will not stop a supply chain attack, a well-segmented network means malicious activity can be much more easily contained and creating more chances for detection. With ISE, know who, what, where, and how endpoints and devices are connecting. ISE even allows for software-defined access and automates network segmentation.
Detecting anomalies in application behavior can help identify a supply chain attack. To do this, solutions like Cisco Secure Workload can provide the ability to baseline the normal behavior of your applications, allowing you to quickly identify anomalies or suspicious behavior.
This can all be a little overwhelming. If you’re looking for assistance in dealing with a supply chain attack, Cisco Talos Incident Response (CTIR) is here to help. Whether you’re looking for an emergency incident response, help with playbooks, readiness assessments, threat hunting, purple team exercises, or more, CTIR can provide.
We’d love to hear what you think. Ask a Question, Comment Below, and Stay Connected with Cisco Secure on social!
Cisco Secure Social Channels





