Many organizations today fail in adequately acquiring the necessary visibility across their network to perform efficient and effective Incident Response tasks, one of which is Intelligence-Driven Incident Response; defined as driving intelligence mechanisms to dig deeper into detecting, containing, and eradicating the latest cyber threats. Occasionally, adversaries may leave evidence on compromised devices which may be helpful for identifying Techniques, Tactics, and Procedures (TTPs) of value for attribution of an attack to a particular group, association, or individual; which allows responders to identify additional affected systems and pursue further leads. Such critical components to threat intelligence include Indicators of Compromise (IOCs), but are not limited to: file names, file paths, hash values, IP Addresses, Uniform Resource Identifiers (URIs), and common tools used by known individuals or groups.
Organizations often struggle in achieving this next-level of proactiveness without the precise logs required to investigate thoroughly. Many organizations simply can’t ingest every single log type from each technology used within the organization, furthermore are typically limited to the number of Events Per Second (EPS) into a central log aggregator or Security Information and Event Management (SIEM) product, whether it’s a bandwidth constraint, limitation of the product or even a license issue. While some enterprises may be fortunate enough not to have such technological limitations, others may simply not have the man power or expertise necessary to provide efficient and effective monitoring and detection. Whether this is a resource deficiency or absence of skill, some organizations tend to ingest as many logs as they can, and then leverage use of these logs when an incident arises in an attempt to conduct a thorough investigation and response.
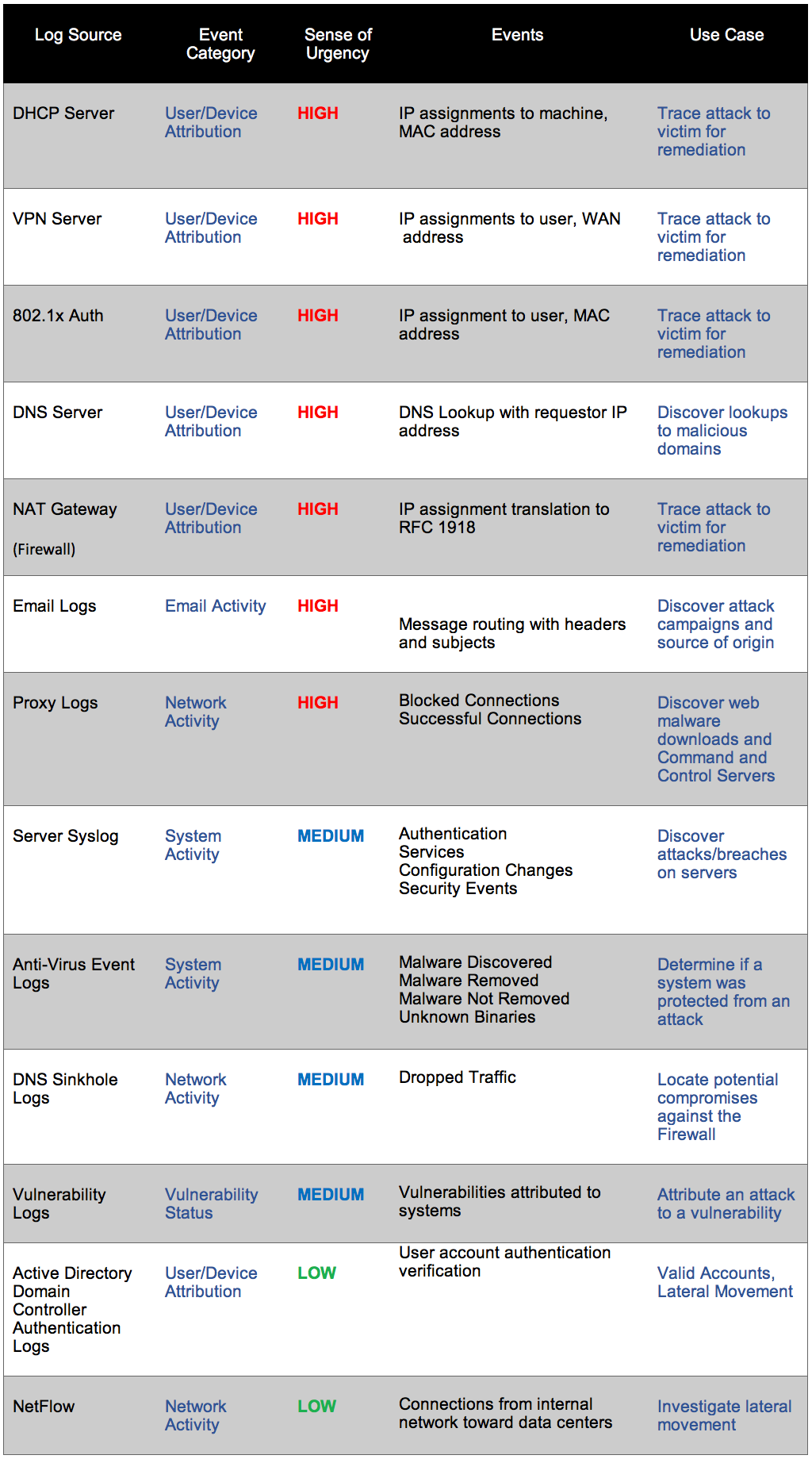
This is not the approach that should be taken and is why we here at Cisco, assist organizations in building effective, world-class Security Operations Centers (SOCs) that will help prioritize log sources based on the Use Case, Event, and Sense of Urgency desired to detect and prevent an attack as it happens, and impulse to more of an Intelligence-driven Incident Response competency, shown in the figure below. For instance, logs should not be ingested without first building a use case scenario for the business to determine if the use case can be successfully achieved. This is similar to building a business case for a particular investment in technology and answers the question of ‘What’s your end-goal’? All use cases have one end-goal which is attribution to the detection of a threat, a fundamental necessity to the response of an incident. However, a use case can’t be built without the technology logging the appropriate necessities, and vice-versa, attribution can’t be achieved without a successful use case.
A use case should also identify the key stakeholders, timeliness and lifetime, and the investment required (both from a time and monetary perspective) of the use case, for such to be fully operational, effective, and efficient within an environment. Regardless of where the limitation lies upon, addressing the constraint initially; will allow the organization to build a successful use case, incorporate the necessary logs, prioritize based on the industry relevancy that a threat (use case) may have based on previously discovered high impacted/high risk incidents.
By integrating such proactive measures, organizations can take an initiative to stay one step ahead before falling victim to a serious cyber security incident. Is your organization prioritizing the necessary log sources?
See how Cisco Security Advisory Services can help your organization here.






Just on time post.
Good Read. Keep putting out great work.