The bad guys aren’t going away. In fact, they are getting smart, more creative, and just as determined to wreak havoc for profit as they have ever been. The good news is Security solutions and methodologies are getting better. Next Generation Firewalls, Malware Protection, and Access Control are not only improving, but in some cases, working in concert together. This is good news for any security team and a lot of these solutions are part of any security stack.
But how do you know when you have been breached? How long has that attack been roaming through the network? Who is affected? These are the questions that visibility helps answer. Access Control solutions are now commonplace in letting us know the “Who”, “What”, “Where”, and “When”. Now we need to know the “How” and “Why”. We need to know these answers not just for the network, but for our Cloud solutions as well.
Visibility into the Conversation
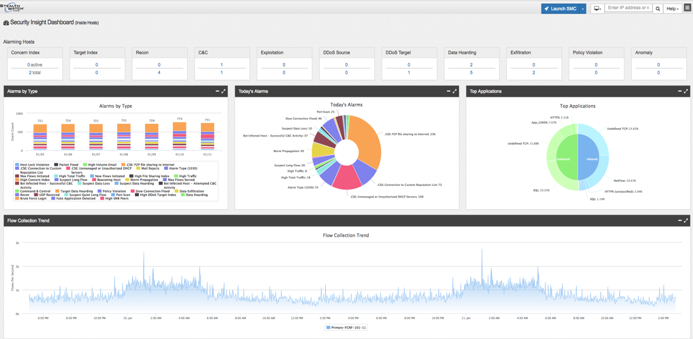
Learning what “normal” behavior looks like is a great place to start. Knowing how hosts behave and interact allows you to react quickly when a host deviates from the norm. Stealthwatch provides visibility into every conversation, baselines the network, and alerts to changes. Not all changes are bad and this level of insight will also provide critical information for network planning.
Visibility into the Files
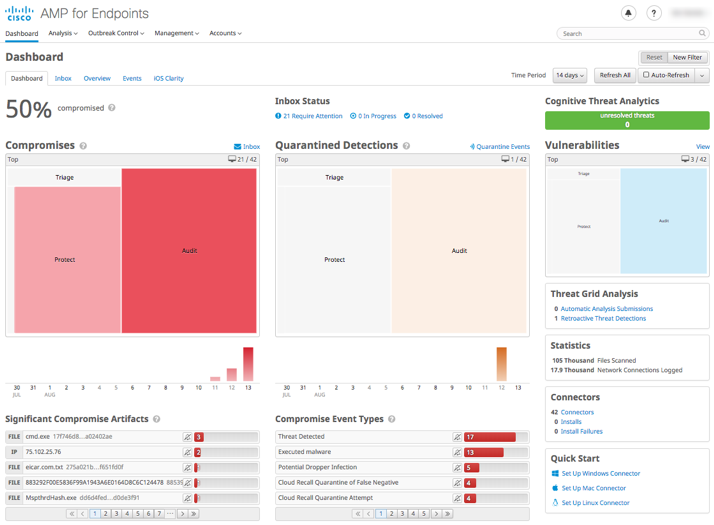
Since malware began, there has been a need to inspect files to ensure that they have not been compromised or the source of corruption themselves. A downloaded file that was benign yesterday could morph into something detrimental tomorrow. Exploits that are frequently paired with malicious files represent another problem of memory-resident malware, that doesn’t have any footprint on the disk and that attempts to inject into legitimate processes to stay undetected. Advanced Malware Protection (AMP) does retrospective analysis such that it doesn’t just inspect a file once and moves on. It has the ability to look back in time and see exactly when and how a file changed, what it did, who it effected. Additionally, a file discovered to be malicious on one machine can be quarantined and an update can be sent to all machines that prevents them from ever even opening that file, now limiting the exposure to the rest of the network. AMP for Endpoints goes even deeper and prevents malicious access to memory resources of most common applications and Operating System processes. AMP for Endpoints serves as the last line of defense for your endpoints, servers, and mobile devices, utilizing a protection lattice that combines multiple sophisticated techniques to counteract malicious actors. Learn more here.
Visibility into the Threats
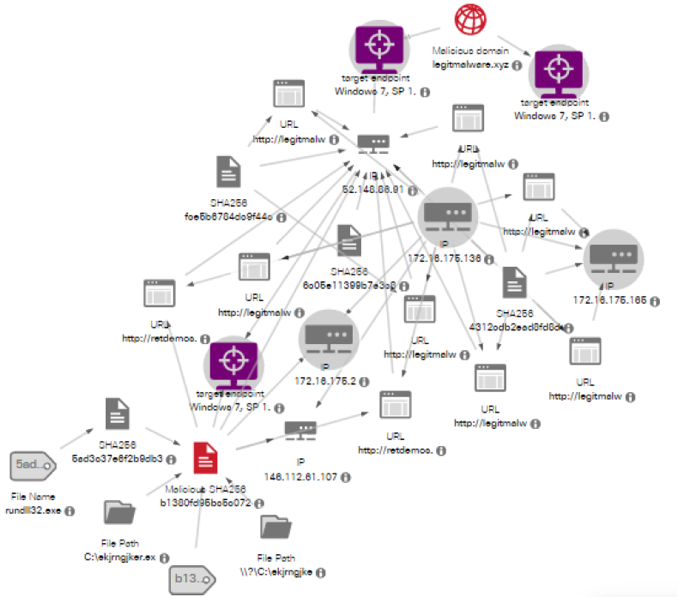
Since it’s not a matter if a breach will occur, but when, the ultimate goal is to limit exposure and remove the threat as quickly as possible. Threat hunting is costly, time consuming, and necessary in getting operations back to normal. Knowing where to begin, determining the impact, removing the threat, and ultimately protecting against it from happening again is a challenge in of itself. The longer the threat is in the network, the more damage it will do. Cisco Threat Response helps in finding the threats quickly, identifying those effected, and eliminating the threat faster than ever. Threat Response displays the entire path of the malicious event, including URL, SHA values, file information, and more. This information effectively reduces the time spent threat hunting.
Visibility into the Internet
We are also constantly being misled and misdirected to go to sites that we shouldn’t. Whether it’s as simple as a fat-finger or being intentionally misled, anyone can easily end up in a very dark place. Embedded links within an email that appears legitimate brings our guard down. The first URL you click on may be OK (think reddit.com ) but what happens as you go deeper? Should your employees be allowed to click on a link that is two hours old? How can I protect my employees when they are off-net? These are questions asked every day. Cisco Umbrella is built into the foundation of the Internet and as a DNS service, endpoints can be protected both on and off-net. Umbrella’s Investigate lets you explore deeper into the URL to get a complete picture of everything; from where the site is hosted, who owns it, it’s reputation, and even the files that are related to this site along with their threat scores (powered by integration with Cisco Threat Grid). Umbrella’s view of the Internet can prevent up to 90% of threats from ever making it to the endpoint, thus making the rest of the security stack that much more efficient.
Visibility is the Key!
The bad guys only need to be successful at breaching the network once. The good guys need to be successful EVERY time. Firewalls, Intrusion Detection, Endpoint protection, and other security solutions are critical in handling 99% of the risks. That’s a great number. It’s that 1% that gets through that keeps security people awake at night and is going to cause the most harm. Having the ability to see not just the north-south traffic, but the east-west, is vital to detecting anomalies early. When there is an event that requires research, reducing the time it takes to get to the bottom of it and ultimately eliminating the threat quickly keeps business humming optimally.






I am developing a new presentation for a couple of events in Sept! My theme is VISIBILITY!
We need to know what we have before we can protect it, but it also lends well to the investigation after something happens.
Thanks for the blog post!
Thanks for the feedback Perk! Visibility is absolutely the key to a successful security initiative. I'm glad you liked it!
This is great stuff! Nice article Ken~
Thanks very much!
Good & Informative stuff
Thanks Tariq! I'm glad you found this useful!