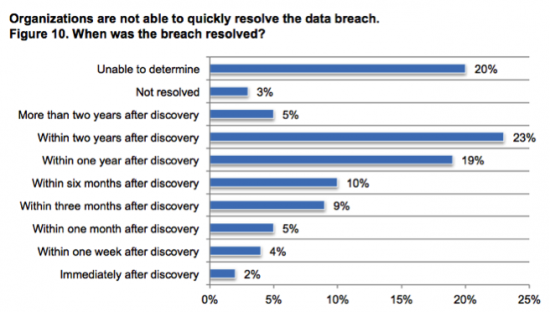
Ponemon Institute called 2014 the year of the “Mega Breaches,” which will be remembered for its series of mega security breaches and attacks. These “Mega Breaches” are perfect examples of what is commonly known as Advanced Persistent Threats (APTs). The Ponemon Institute survey asked, among many questions, “When was the breach discovered?” Surprisingly, the results revealed that ONLY 2% of the respondents in the survey discovered their breach within one week of after the incident and a staggering 90% were six months or longer, if at all.
Let’s take a look at how these APTs can create a seemingly insurmountable challenge to organizations. First lets start with a model that we can put some analysis against. In our “Simplified Threat Model,” an event is generated when the cyber attacker attempts to compromise one of the elements in the “Attack Vector” group. Although the simplified threat model shows only a single arrow to a single attack vector, each cyber attacker could in fact attack every other attack vector that the organization exposes to the external and internal cyber attackers. Continuing that model, each time a cyber attacker progresses to the next group, the theoretical security system generates an event. Once again, each attacker can attack every element in the next group and in this case the “Cyber Infrastructure.” The process repeats until eventually the cyber attacker reaches their “Cyber Asset(s) of Interest.”
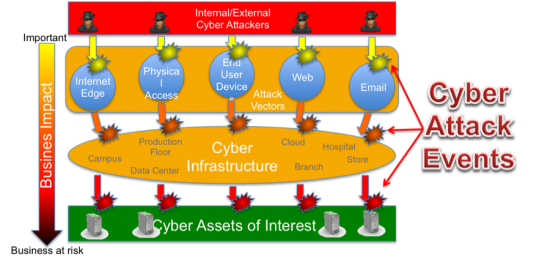
Not every cyber attacker in the world will find our attack vectors and not every cyber attacker will get through our defense measures so we need to add a probability factor. This model enables us establish a formula to quantify the events in the model. For the sake of saving time and the pains of the readers going through some deeper math equations, which can be found in the Cyber Threat Defense Solution Architecture Guide, the resulting simplified approximation formula looks like:
Cyber Attack Events = (Cyber Attackers) * (Attack Vectors * Probability of Being Attacked) * (Infrastructure Assets * Probability of Compromise) * (Assets of Interest * Probability of Successful Attack on Asset)
Let say our theoretical organization had the following:
- 500 Cyber attackers in the world trying to attack our company
- 60,000 Attack Vectors with protections at 80% effectiveness (laptops for employees for example)
- 100 Infrastructure Assets (network devices and firewalls devices for example)
- 50 Assets of Interest (point of sale devices and servers with customer data for example)
- 98% effectiveness of our cyber defense measures (2% is the factor that we put in the equation)
With those numbers, we can plug them in the formula and we get a result of 1.2 million cyber attack events at any given time. By now you are wondering where I am going with this, but here is the key point. Just like time is a compounding factor for the interest rate on a loan, time is also a compounding factor with cyber attack events. Lets assume that our time interval for the above calculation was 1 hour, we can then multiply the result above by 24 hours to get an approximate result of 28.8 million cyber attack events in a 24-hour period.
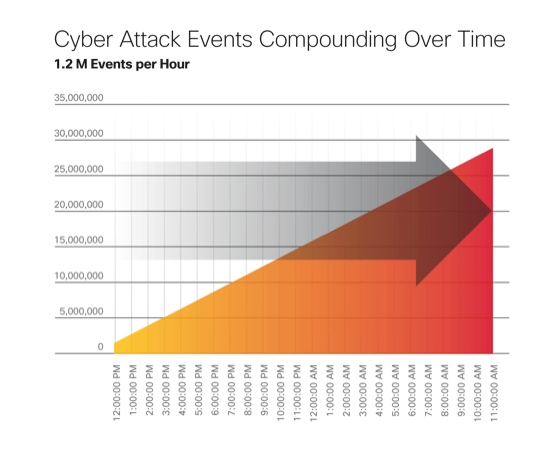
Looking back to the Ponemon Study where 90% of those companies that took over a week to discover their breach, you can imagine how those cyber attack events would have compounded to significant amounts with a high chance that there were numerous successful breaches during that time. Our hypothetical company in the model above would have seen over 201 million cyber attack events in a week. It is time to ask, how does a security operations team manage to address such a large number of cyber attack events? The model lets us see that there are two key compounding factors that can be impacted in how we design our security architectures and that is probability and time. Every time we deploy a new security technology or product we hopefully are reducing the probability of a cyber attack, but unless we address the time factor in the problem above the teams will never be able to effectively secure the networks.
The Cisco Cyber Threat Defense Solution solves for both probabilities and time
By having both the best of breed products and technologies combined with an unprecedented integration capabilities, the resulting solution is able to provide security operations teams with the ability to detect and remediate cyber threats either automatically or in the shortest time possible when manual intervention is required.
The Cyber Threat Defense Solution uses the FirePOWER Next Generation IPS and the Lancope’s StealthWatch as a foundation for both deep packet inspection and scalable visibility so that every flow can be inspected and analyzed across the entire network. On top of that foundation, the solution adds Cisco’s Integrated Services Engine for scalable segmentation an enabling dynamic remediation of the fabric. Having a solid foundation for managing the flows, the solution adds the powerful Cisco’s Advanced Malware (AMP) capabilities across the network, on the endpoints, across web traffic, email gateways and even on hand held devices. Cisco’s AMP ThreatGrid provides for continuous analysis and ensures all of the malware subsystems are updated in real time. Every hiding place that the cyber attackers might use is now exposed!
Cisco Cyber Threat Defense 2.0 Solution Cisco Validated Design is now available
You can see this solution being demonstrated and talk to the experts by visiting the Cisco booth at the BlackHat 2015 Conference in Las Vegas, Nevada on August 5th and 6th.






Personally we will only see a reduction in breaches when two things happen;
1. Boards provide suitable budgets and become proactive rather then reactive
2. Education
then there is a secure baud rate transfers between data and observation of movement of hachers