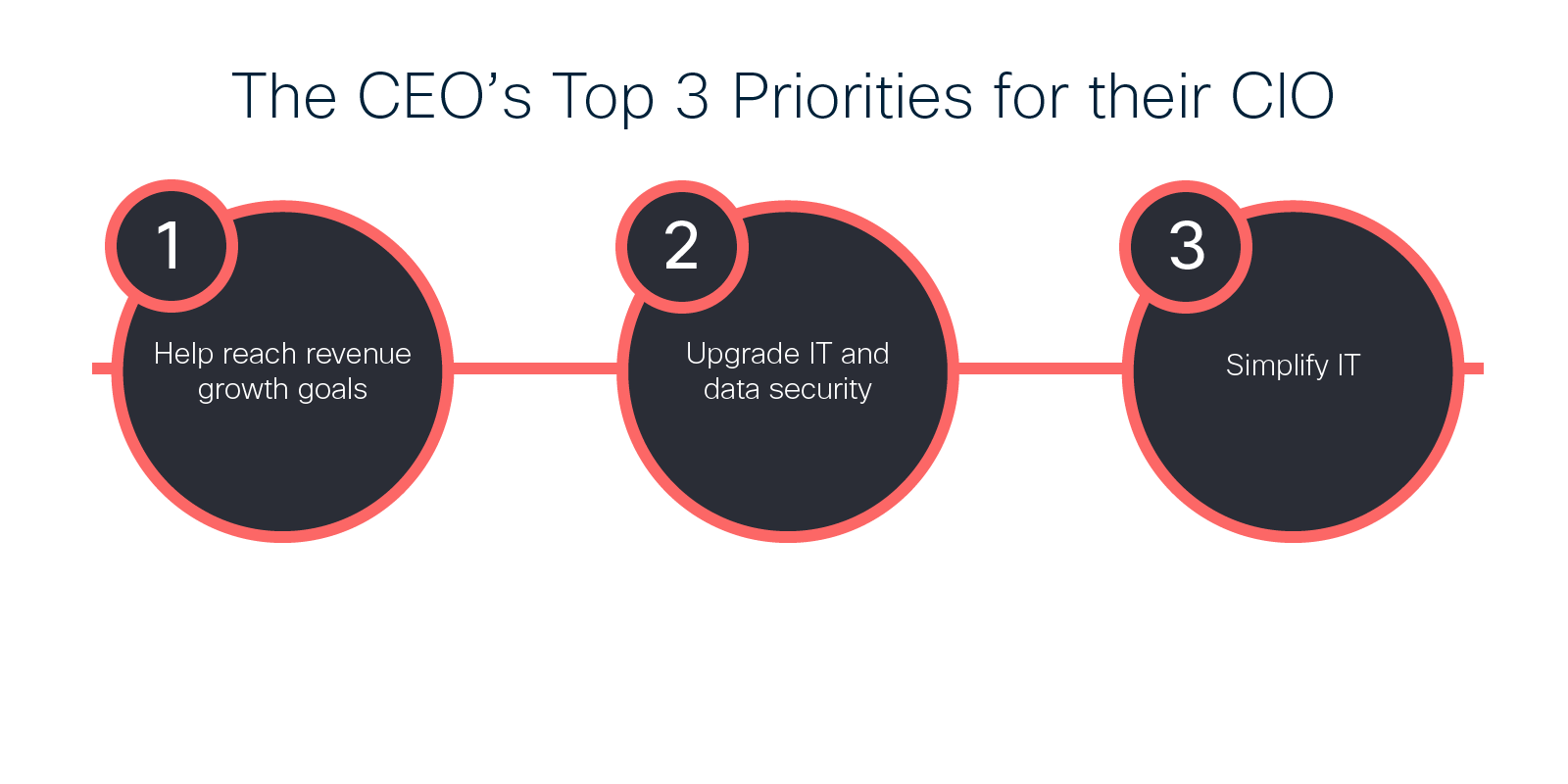
As the calendar turns to 2019 in a matter of weeks we will be bombarded with a series of new predictions and resolutions. We had the same barrage last year, including this one on what CEOs mandate to their CIOs:
- IT must do everything it can to help businesses reach revenue ambitious growth goals
- IT must improve data security and modernize their infrastructure and operation
- Above all, IT must simplify
SOURCE: CIO Magazine (January 2018)
These are fundamental goals for IT and these three mandates will remain relevant in 2019 and beyond. This reflects a core problem with enterprise technology: Each year many more technologies arrive, yet few ever seem to ever go away. Complexity naturally accretes, and simplification requires concerted effort.
The shift to the cloud is an example of this. Initially the cloud promise was that it would bring a shiny, new, clean and simple architecture. A decade into this new world, the reality is that rather than moving to the cloud, companies are “expanding to the cloud.” They maintain many existing systems running in private data centers, while taking advantage of new SaaS offerings.
And on of top that, end user expectations have increased. They want all of the benefits of the cloud—easy access using any device, anywhere, at any time—for all services even the ones still in private data centers. And the new threat landscape has created a need for IT to protect every app, every workload, every device, and every user across the entire enterprise at all times.
I believe we are now at a tipping point. The urgency of digital transformation demands that enterprises accelerate their “expansion to the cloud.” But, the enterprise landscape is already littered with digital transformation failures unable to meet even basic requirements for success. The complexity and security requirements of these transformations threaten to bury every IT departments. A simple way forward is required.
Secure Internet Gateway: Power of Consolidation & Simplicity
Enterprises can take many paths to address the complex problems facing their security and infrastructure. One path is to select best-of-breed, or what we like to call the “vendor buffet.“ While customers may gain access to some good technologies in this way, they also have to own the burden of making all these complex and disparate pieces fit together. The goal is to reduce complexity, not add to it. This may explain why more CIOs are opting for integrated solutions and vendor consolidation.
This is why we had the vision of Cisco Umbrella as the platform to build the industry’s first Secure Internet Gateway (SIG). Our goal is to help companies deliver security at the speed of business and the pace of growth. As I explained in my first blog about SIG, this isn’t about taking the old technology and just sticking it into the cloud. What is required is a seamless expansion of security, workflows, and policies into multiple clouds as part of a unified multi-domain architecture.
Since we introduced our SIG, we have been continually and steadily delivering on the critical parts to make the vision a reality for our customers. We recently introduced several innovations and integrations for Umbrella that drive better security in a simplified way across the Cisco portfolio. Highlights include:
- Cisco SD-WAN Integration: We made it easier than ever to deploy Umbrella across Cisco SD-WAN fabric to hundreds of devices in minutes. Customers are enabled with web and DNS-layer protection against threats such as malware, ransomware, and C2 callbacks. For additional granularity and control, admins can set policies and view reports on a per-VPN basis with three simple steps.

- App Discovery and Blocking: We built in core technology from Cisco Cloudlock into Umbrella to deliver automated shadow IT visibility and blocking. The App Discovery report shows cloud app usage and risk information to enable secure cloud adoption, plus blocking of unapproved apps. We saw this powerful capability in action in a major auto manufacturer who discovered and blocked dozens of unsanctioned cloud and SaaS applications in a few clicks.
- Meraki MR Integration: Meraki is all about taking simplicity in IT to the next level. Now with just a few clicks, our customers can deploy Umbrella across Meraki MR access points and instantly protect Wi-Fi users from malware, ransomware, and other threats. They can also enable Umbrella policies directly in the Meraki dashboard, and use existing Meraki Group Policies.
- Cisco Threat Response: This is a new platform that automates integrations across Cisco Security products and is designed to dramatically cut the time and effort needed to detect, investigate, and remediate threats to make security operations more efficient and effective than ever before. Through the Threat Response and Umbrella integration, users can now see both Umbrella activity and Investigate intelligence alongside information from their other Cisco Security products in a centralized place.
Umbrella is now a comprehensive, single security solution that can be layered on top of existing architectures and seamlessly added to new SD-WAN architectures. It is simple to deploy, provides deep visibility and protection, and consolidates multiple product offerings into one.
Summary
Enterprises are expanding into the cloud rapidly as digital transformation ambitions give way to actual projects and initiatives. Bolting on new technologies only adds to the complexity enterprises have to manage and is certainly a path to failure.
Therefore, it is critical that companies like Cisco think about new solutions and capabilities and ensure they evolve and align to our customers’ realities. The need to drive simplicity and security everywhere is at the heart of the Umbrella value proposition. As cloud-delivered security platform, Umbrella continually delivers product and feature introductions to meet the expanding needs of our customers.
Give Umbrella a try, and sign up for a 14 day free trial today.