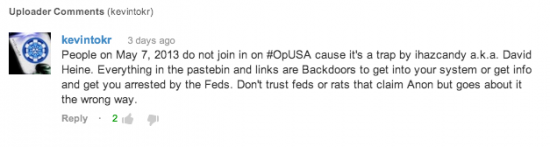
In the days leading up to #OpUSA, security professionals were busy making preparations for the supposed flood of new attacks coming on 7 May 2013. As we mentioned on 1 May 2013, publicly announced attacks of this nature can have highly volatile credibility. In some cases, the announcements exist only for the purpose of gaining notoriety. In other cases, they are enhanced by increased publicity. By 4 May 2013, speculation arose that #OpUSA was a trap; this likely caused some potential participants to rethink their plans to join. Posts similar to the one below were made on Twitter, Facebook, and YouTube.
So far, none of the expected DDoS components of #OpUSA appear to have materialized. One of the more prolific hactivist teams with actual DDoS capability, the Izz ad-Din al-Qassam Cyber Fighters, decided against participating.

This is not to suggest that nothing has happened so far as a result of #OpUSA. Groups such as AnonGhost Team, @Charafanons, Mauritania Attacker, X-BLACKERS INC., Islamic Ghost, Tunisian Hacker Team, Sir Abdou, Shadow Haxor, Indonesia Security Down, and Anonymous Algeria have all claimed to have done damage. There is a growing list of defaced or hacked sites from various participants located on a bullet titled “List of Websites,Email Accounts affected under #OpUSA; Updating list as defaced, hacked or down.” Most of the attacks are against small business websites or personal vanity domains. Several sites listed are from foreign Country Code Top Level Domains (ccTLDs) such as Russia and Brazil, which one would expect should fall outside of the #OpUSA target list.
Among the government targets, the only attacks that appear to have succeeded is a short-lived defacement of an Ohio Election Assistance Commission site; as 7 May 2013 was the date of primary elections for the State of Ohio, this particular site may have been targeted in part due to the potential for increased traffic. Additionally an attacker calling himself “Mauritania Attacker” claimed to have obtained a large list of email addresses and passwords belonging to various government officials, but we have reason to believe at least some of these reports may be false.

Financial targets haven’t yet been widely compromised either. We’ve witnessed claims of only a single small community bank website from eastern Arkansas being compromised: firstcommunitybank.us. The only other “banks” mentioned among the #OpUSA casualties, thus far, is the release of donor information from Blood Bank of America, along with a downed blood bank in Croatia (.hr ccTLD)
Cisco TRAC recommends that organizations continue to exercise caution while #OpUSA is still in progress. We may yet see evidence of more advanced attacks, but so far the damage from #OpUSA has been minimal.
References
http://pastebin.com/vpP9KZ6P
http://www.world-news.me/news/6gbTlWW56r?netloc=t_co&key=9d0IpJJ0
Published list of #OpUSA Targets (see appendix): http://pastebin.com/LXHKjsfg


Interesting….It seems that Cisco is on top of these threats? What about the Chinese hacking threats? It seems they can steal corporate secrets at the drop of a hat!!
Nice Article Jaeson!
You are now featured on senderbase.org as well 🙂
Nice post!
Jaeson-
Thanks for this post. I’m hoping to get in touch with you for an article about hacking. Email at address provided if you have a sec? manythanks
Great article Jaeson. You went in-depth into the hacking scene and showed how big it is. So many influential groups.