If you were to ask any security administrator who had to manage the security policies across an organization, they would probably define the “5-Tuple” as a “hard to understand, cryptic method leftover from the 1990s’ policy management for implementing access control and segmentation capabilities in networks.
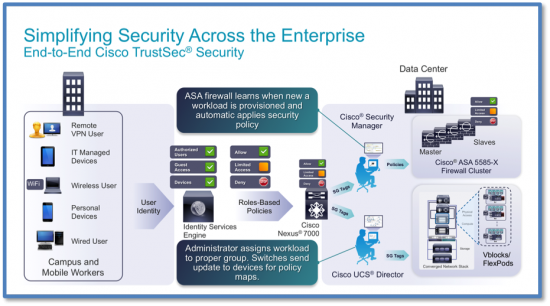
Despite its complexity, 5-Tuple has been a mainstay in performing access control and segmentation for decades. However, Cisco has provided an alternate deployment approach to the pains of the “5-Tuple” approach to managing security policies across the organization by delivering Cisco TrustSec across our product portfolio so that Security Teams could consolidate their security policies, scale segmentation, and create a security fabric that spans across the entire organization.
A Tough Task Becomes a Nightmare….
Without Cisco TrustSec, security administrators have to continue dealing with the “5-Tuple” challenge across their entire network; from the data center, desktops, branch offices, and even managing the policy explosion caused by the rapid adoption of BYOD.
Just imagine the Security Administrator’s worst nightmare coming true upon arriving at work to find out that the Data Center Server Administrators are now going to implement east to west hypervisor security by deploying a firewall per virtual machine, especially when the management of those firewalls are based on the dreaded “5-tuple.” Several operational challenges come to light:
- The control and management of those policies are in the hands of the server teams, but the responsibility of the organization’s security remains with the security team.
- Does the organization implement a unique firewall policy per machine or do they duplicate a policy across all of the machines?
- Realizing that the security architecture is now based on the “if a little is good, then a lot must be great” strategy. Implementing a firewall per virtual machine in a data center containing hundreds to thousands of virtual machines can easily become an operational nightmare.
Some operational decisions need to be made. Just to use an analogy, if you were to hand out 200 combination locks, do you assign each lock a unique combination or do you have all with the same combination? If they all have the same combination, then if a hacker can get through one, they can get through them all. If you give them each a unique combination, you have a policy explosion all being managed separately from your organization’s centralized policy management. Some vendors have tried to solve this problem by implementing “pseudo-role-based” policies to make it appear that they are easy to manage. What do I mean by “pseudo-role-based” policies? This is where the vendor will enable polices based on users and/or groups from the Active Directory server, but these policies are limited to the virtual machines in the data center. These policies are not pushed out across the entire organization and begin to break down the security team’s architecture which was designed to secure the entire organization.
This creates an island in the organization and provides a perfect hiding spot for the cyber attackers. They exploit this type of siloed approach to security where policies are disconnected, where application visibility in the data center is not correlated to the application visibility on the end points. Once again, contributing to a complete break down of the corporate-wide security architecture.
Don’t get me wrong, we need virtual machine-level security at the hypervisor and scalable segmentation with true “roles-based” policies, but it must an integral part of a complete solution. with
Security teams need to be able to connect the user posturing, device profiling, scalable segmentation, simplified and scalable policy management capabilities to have complete end-to-end visibility of applications, users, devices, and traffic flows across the ENTIRE organization. That was a complex way to say that everything must work together to secure the business. You simply cannot solve today’s security threats by adding more firewalls to the problem, especially when those are not integrated with other architectural domains of the organization. Customers need complete security solutions that correlate data, share context information across subsystems, and provide the ability to have retrospective security while having simplified and operational scalability in the data center and across the entire organization.
As for the original problem the server administrators were trying to accomplish with protecting the hypervisor level east to west traffic? Cisco easily solves this problem in the Secure Data Center for the Enterprise Solution Portfolio. Unlike some vendor solutions that tend to work only in the data center, which results in an island of refuge for hackers, our Secure Data Center Solution directly integrates with the security architecture across the entire business.
The Secure Data Center for the Enterprise provides scalable segmentation by connecting the entire organization with a comprehensive enterprise wide role-based policy architecture. Server administrators can deploy workloads with their automation tools into pre-defined “Secure Groups.” Users accessing the network with their devices can have a posture assessment and be placed into the appropriate “Secure Groups” based on their location and security administrators can continue to manage the organization as a whole as opposed to managing a collection of islands.
The Secure Data Center for the Enterprise also includes the Cisco FirePOWER Next-generation Intrusion Prevention System (NGIPS) for threat management capabilities, application and user policy enforcement, threat correlation across endpoints, advanced malware protection with retrospective security to understand the full extent of an infection, establish root causes and perform remediation. The Cisco FirePOWER NGIPS can be tightly integrated with Cisco’s Platform Exchange Grid (pxGrid) to have the Cisco Identity Services Engine provide automatic endpoint quarantine until proper remediation can be completed. This enables the security architecture to have a dynamic and automatic response to cyber threats across the entire organization.
I rattled on a while there, but it frustrates me to see customers still being compromised by cyber attackers when there is an effective, threat-centric solution to mitigate risks presented by today’s dynamic threat landscape. The answers are free on the Cisco Design Zone website.






Very interesting article, thanks a lot for the info!