Vulnerability Discovered by Tyler Bohan and Cory Duplantis of Cisco Talos
Talos has identified an exploitable out-of-bounds write vulnerability in the ELF Section Header parsing functionality of Hopper (TALOS-2016-0222/CVE-2016-8390). Hopper is a reverse engineering tool for macOS and Linux allowing the user to disassemble and decompile 32/64bit Intel-based Mac, Linux, Windows and iOS executables. During the parsing of ELF section headers, there is a user controlled size that is not validated, a malicious threat actor could craft an ELF file with specific section headers to trigger this vulnerability, potentially leading to remote code execution. A malicious threat actor could use a zip file containing the crafted executable to target threat researchers, sent via phishing or file sharing sites. This type of exploit can also be used as an anti-analysis measure in an attempt to defeat sandboxes and automated disassembly.
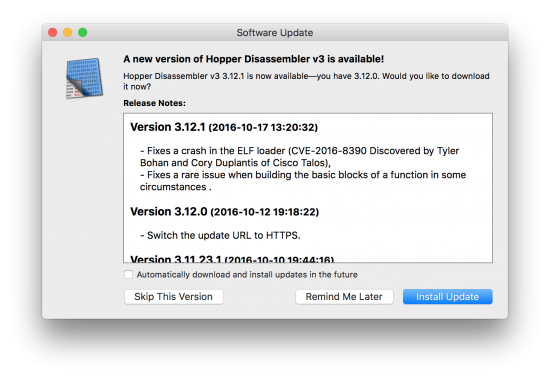
Hopper has been updated the changelog can be read at this URL: https://www.hopperapp.com/rss/html_changelog_v3.php






Very useful and nice tool. Thanks for sharing this interesting blog post. Definitely as usual.