Cisco Talos is currently observing a widespread campaign leveraging the Samas/Samsam/MSIL.B/C ransomware variant. Unlike most ransomware, SamSam is not launched via user focused attack vectors, such as phishing campaigns and exploit kits. This particular family seems to be distributed via compromising servers and using them as a foothold to move laterally through the network to compromise additional machines which are then held for ransom. A particular focus appears to have been placed on the healthcare industry.
Adversaries have been seen leveraging JexBoss, an open source tool for testing and exploiting JBoss application servers, to gain a foothold in the network. Once they have access to the network they proceed to encrypt multiple Windows systems using SamSam.
Technical Details
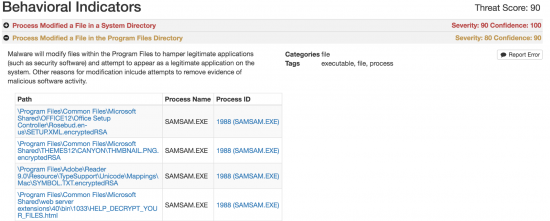
Upon compromising the system the sample will launch a samsam.exe process which begins the process of encrypting files on the system.