A severe cyberattack leveraging TrickBot malware compromises a company’s defenses, leading to significant financial losses. This was not due to a mere oversight, but rather a consequence of inadequate endpoint visibility. With effective monitoring and real-time insights into endpoint activity, the threat could have been detected and neutralized before causing extensive damage. This underscores the critical importance of comprehensive endpoint telemetry.
What is endpoint telemetry?
In cybersecurity, endpoint telemetry refers to data collected by monitoring activities on endpoint devices, such as computers and servers. This data is crucial for threat detection, incident response, and improving the overall cybersecurity posture by offering enhanced visibility.
Crucial role of endpoint telemetry
Visibility is crucial to stopping complex cyberattacks early in the kill chain. If you can’t see it, you can’t stop it. When it comes to stopping an attack, it’s always better to do so in the early stages of the attack chain.
According to the MITRE ATT&CK framework, which is commonly used by cybersecurity professionals, most enterprise-level attacks — such as Turla, ToddyCat, and WizardSpider (TrickBot) — involve various stages, known as tactics, which attackers can use in different sequences to achieve their objectives.
The MITRE framework catalogs a list of techniques and sub-techniques that attackers use to carry out each of these tactics on an endpoint. To detect malicious behavior early in the attack chain, it’s essential to monitor the endpoint and record activities that resemble these commonly used techniques. Capturing telemetry is therefore vital for identifying these techniques and intercepting attacks at an early stage. Endpoint telemetry also serves as a crucial data source for XDR, enhancing its ability to detect, analyze and respond to security threats across multiple environments.
Minimizing false positives
One of the main challenges in using telemetry to detect threats is managing false positives. Attackers often exploit Living Off-the-Land (LOL) binaries — legitimate tools and utilities that come with operating systems — to execute various techniques or sub-techniques. For example, the Lazarus Group, a highly sophisticated and notorious state-sponsored hacking group, is known to use Scheduled Tasks or PowerShell during the Persistence or Execution stages of an attack. Lazarus frequently employs these techniques as part of their broader Living Off the Land (LOL) strategy, which allows them to exploit legitimate system tools and binaries to blend in with regular network activity and avoid detection by traditional security solutions.
Since these actions mimic benign activities commonly performed in enterprises, detecting them incorrectly can lead to a high rate of false positives. We could address this challenge is by correlating the events and telemetry triggered around that activity or by using an XDR (Extended Detection and Response) tool, such as Cisco XDR. Cisco XDR correlates telemetry from various detection sources to generate high-fidelity incidents, enhancing the ability to identify and stop complex attacks while reducing the likelihood of false positives.
Capturing telemetry using Cisco Secure Endpoint
Cisco Secure Endpoint is an Endpoint Detection and Response (EDR) tool that collects and records a wide range of endpoint telemetry. It employs various detection engines to analyze this telemetry, identify malicious behavior and trigger detection events. We continuously fine-tune the product to capture more telemetry and detect events of varying criticality across different stages of the MITRE ATT&CK framework. Additionally, events from Cisco Secure Endpoint are ingested into the Cisco XDR analytics engine and correlated with other data sources to generate high-fidelity incidents within Cisco XDR.
Let’s explore the detection events captured by Cisco Secure Endpoint in the Events view, along with the telemetry recorded in the Device Trajectory view. We’ll focus on how Secure Endpoint provides visibility into the early stages of an attack and its capability to stop complex threats before they escalate.
Exploring detection events
All the events used in this example can be viewed from Management->Events page of the Cisco Secure Endpoint console.
Execution Tactic and Detection
Execution tactics represent the techniques used to run attacker’s payload on a compromised endpoint to perform some malicious activities.
Example techniques include:
- Encoded PowerShell — Using obfuscated PowerShell commands to execute code.
- Windows Management Instrumentation (WMI) — Leveraging WMI for executing commands and scripts.
- Native APIs — Utilizing built-in system APIs for code execution.
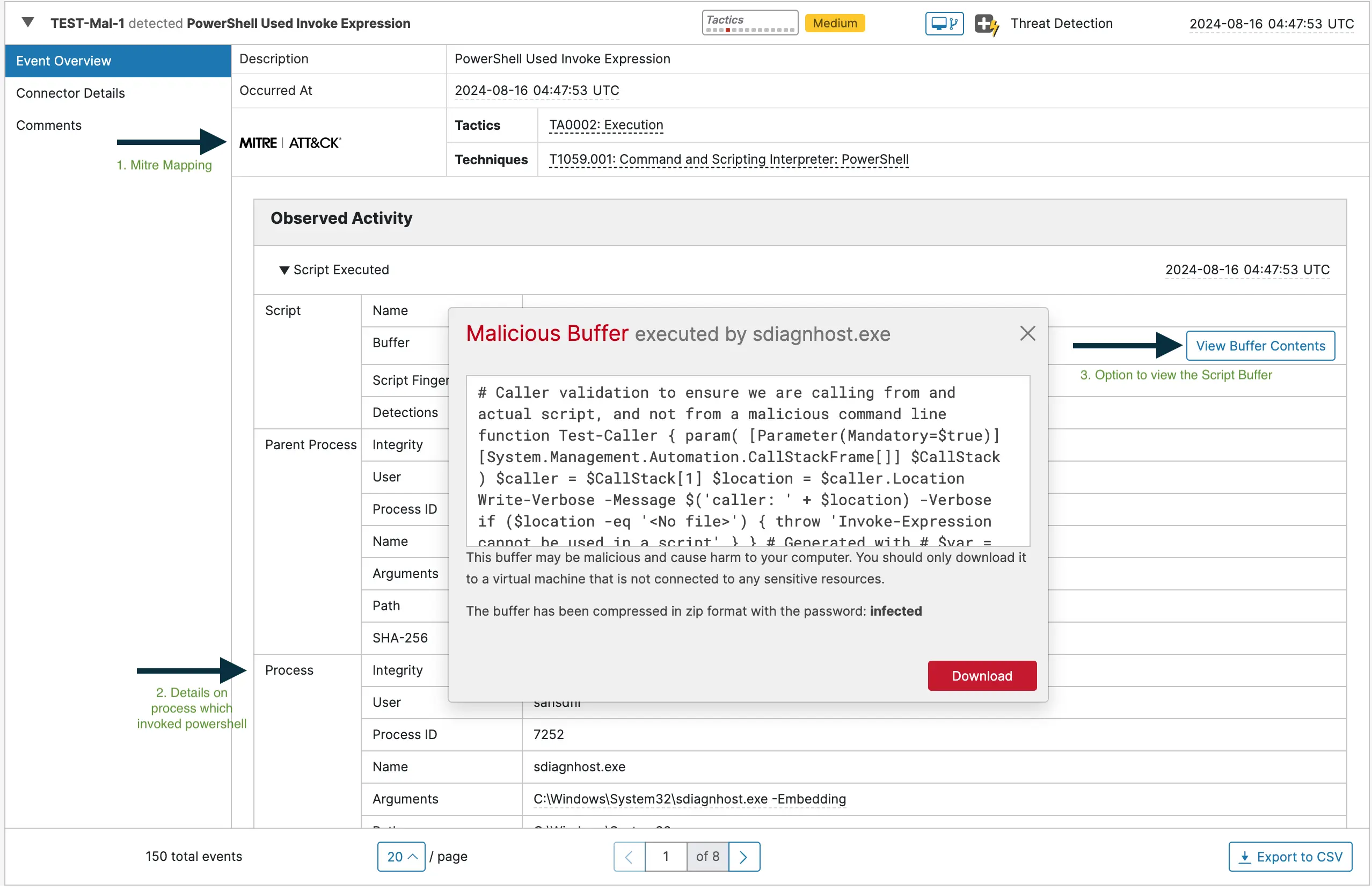
The screenshot below displays an event generated by the Behavioral Protection engine of Secure Endpoint, which detected a PowerShell command using “Invoke-Expression” and triggered by “sdiagnhost.exe”.
Persistence Tactic and Detection
Persistence refers to tactics that allow malicious payloads to remain on a compromised system and continue their operations even after reboots or other system changes. These techniques enable the malware to maintain communication with a command-and-control server and receive further instructions.
Example techniques include:
- Create or Modify System Process — This technique involves creating new services or modifying existing services to execute malicious code at startup or at specific intervals.
- Registry Modifications — Altering registry entries to ensure malicious programs execute on system startup.
- Creating Scheduled Tasks — Setting up tasks that run at specified times or intervals.
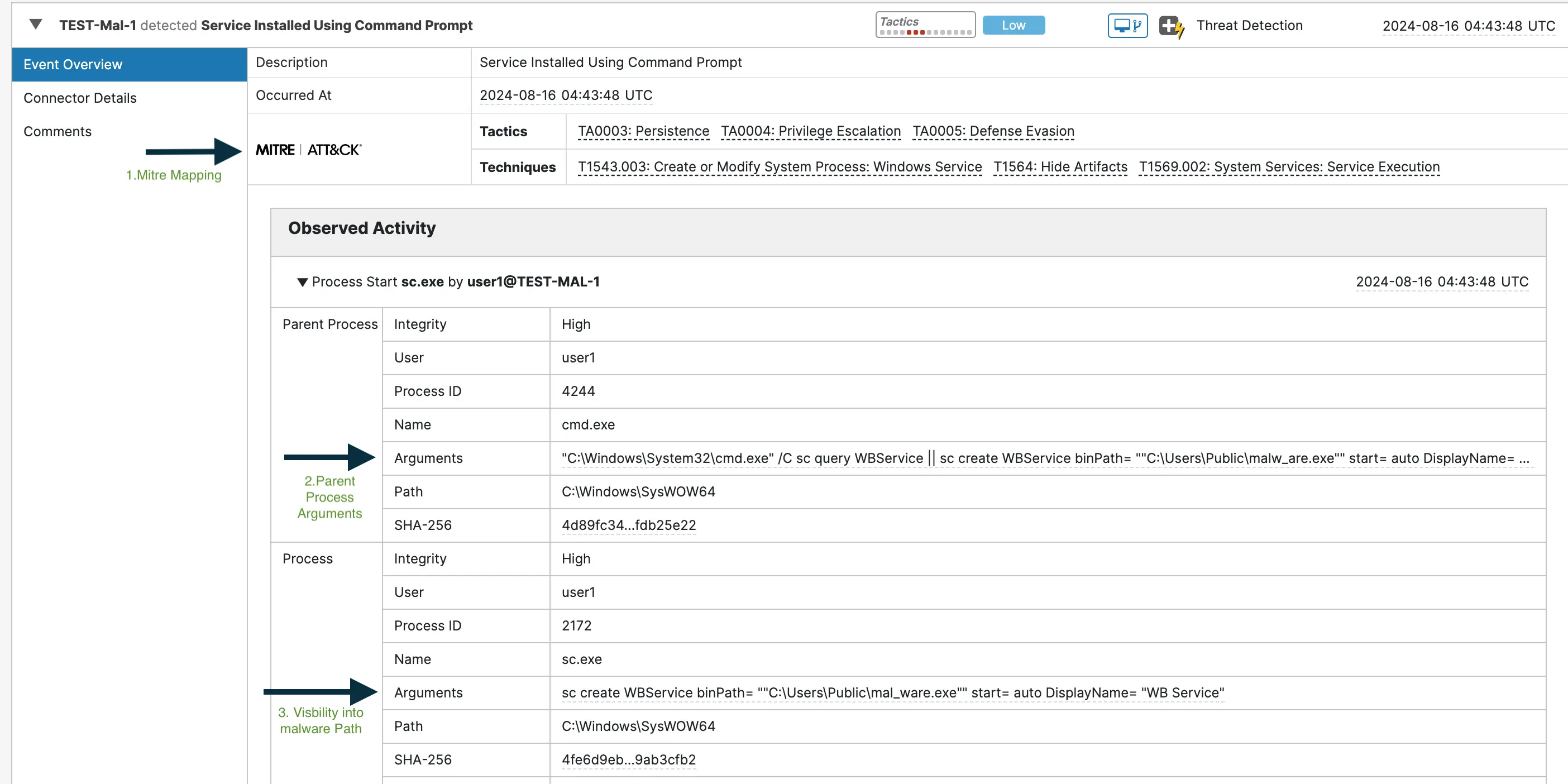
The screenshot below illustrates an event generated when a new service was created to run malware at startup.
Defense Evasion Tactic and Detection
Defense Evasion involves techniques used by attackers to hide their malicious payloads and avoid detection by security systems. The goal is to make it difficult for security tools and analysts to identify and stop the attack.
Example techniques include:
- Process Hollowing — It is a technique where a suspended process is created, and a malicious code is injected into the address space of that suspended process.
- Impair Defenses — Modify victim’s environment and disable defenses, like turning off anti-virus, firewall or event logging mechanisms.
- Masquerading — Making malicious files or activities appear legitimate to evade detection.
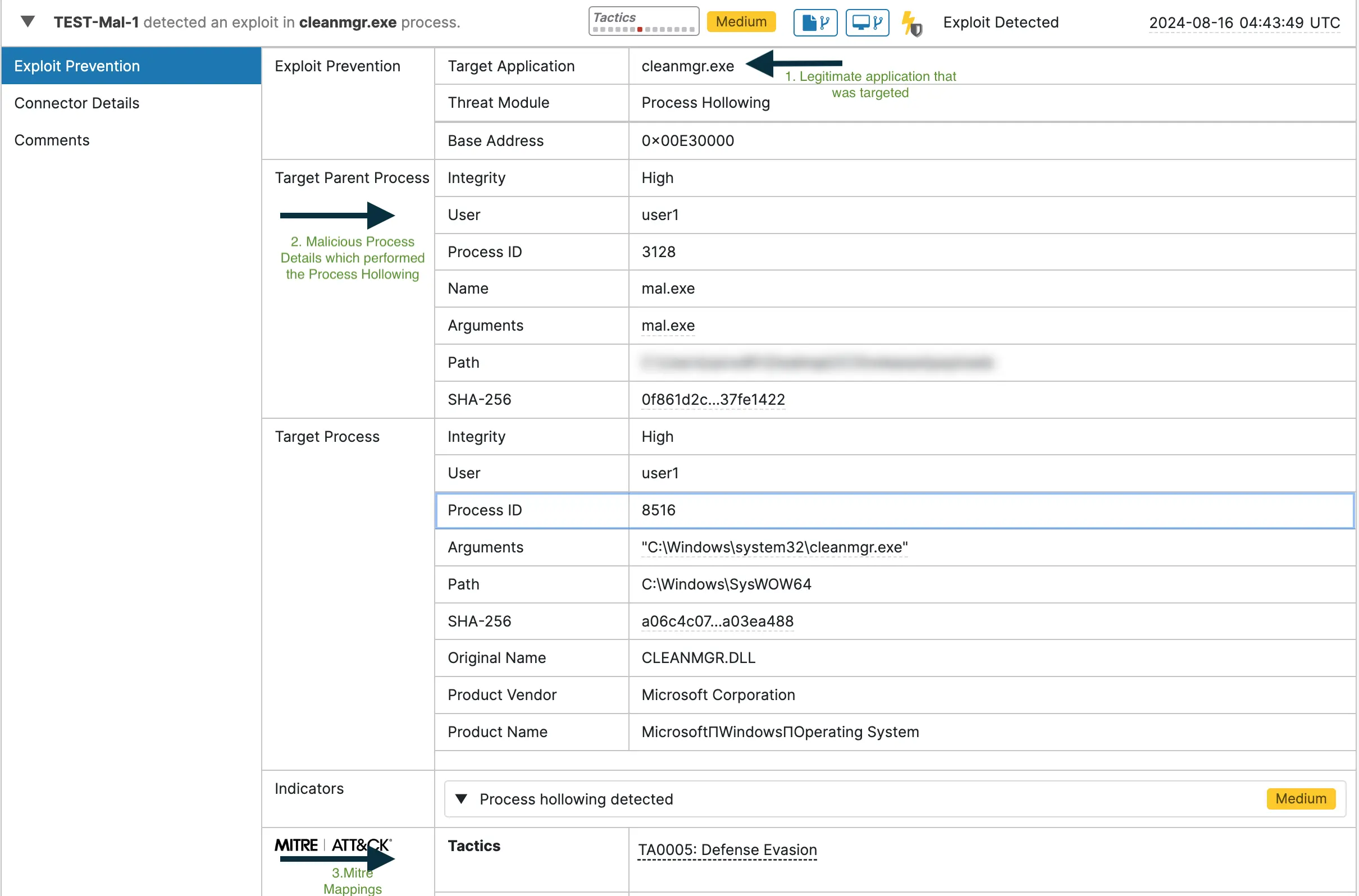
The screenshot below shows the Process Hollowing technique captured by the Exploit Prevention engine during the Defense Evasion stage of the attack.
Discovery Tactic and Detection
Discovery refers to the different techniques adversaries use to gather information about the victim’s environment.
Example techniques include:
- Process Discovery — Enumerating running processes to find valuable or vulnerable targets.
- System Information Discovery — Collecting details about the operating system, hardware and installed software.
- System Network Configuration Discovery — Identifying the network settings, interfaces and connected devices.
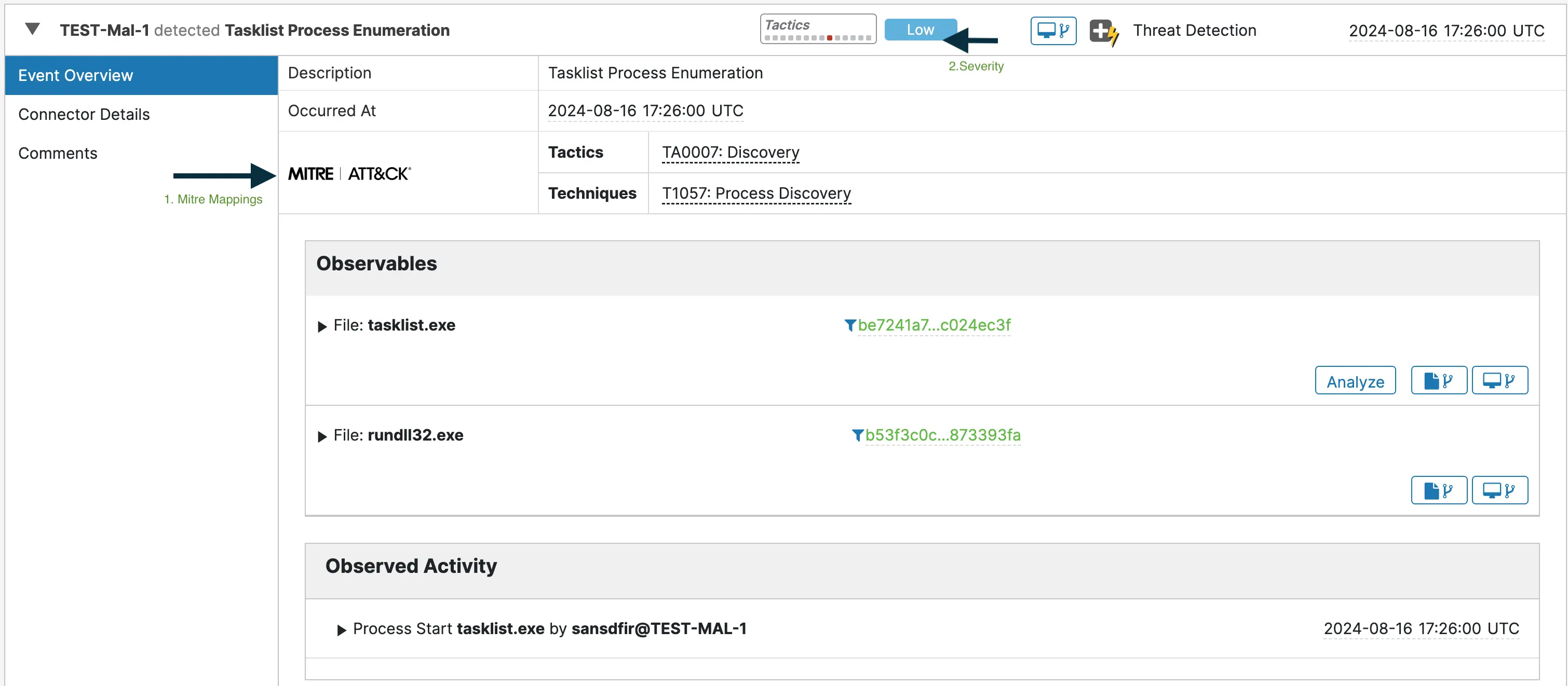
The screenshot below depicts the event Secure Endpoint generated on observing “tasklist.exe” usage in the endpoint in a suspicious manner, run by “rundll32.exe”, and mapping the behavior to Process Discovery technique.
Device trajectory telemetry
Cisco Secure Endpoint (CSE) captures two types of telemetry under Device Trajectory view: Activity Telemetry and Behavioral Telemetry.
Activity Telemetry
By filtering out unwanted data, this telemetry reduces noise and offers clear visibility into endpoint activities, including processes, parent-child process relationships, triggered events, files and network activity, whether malicious or benign.
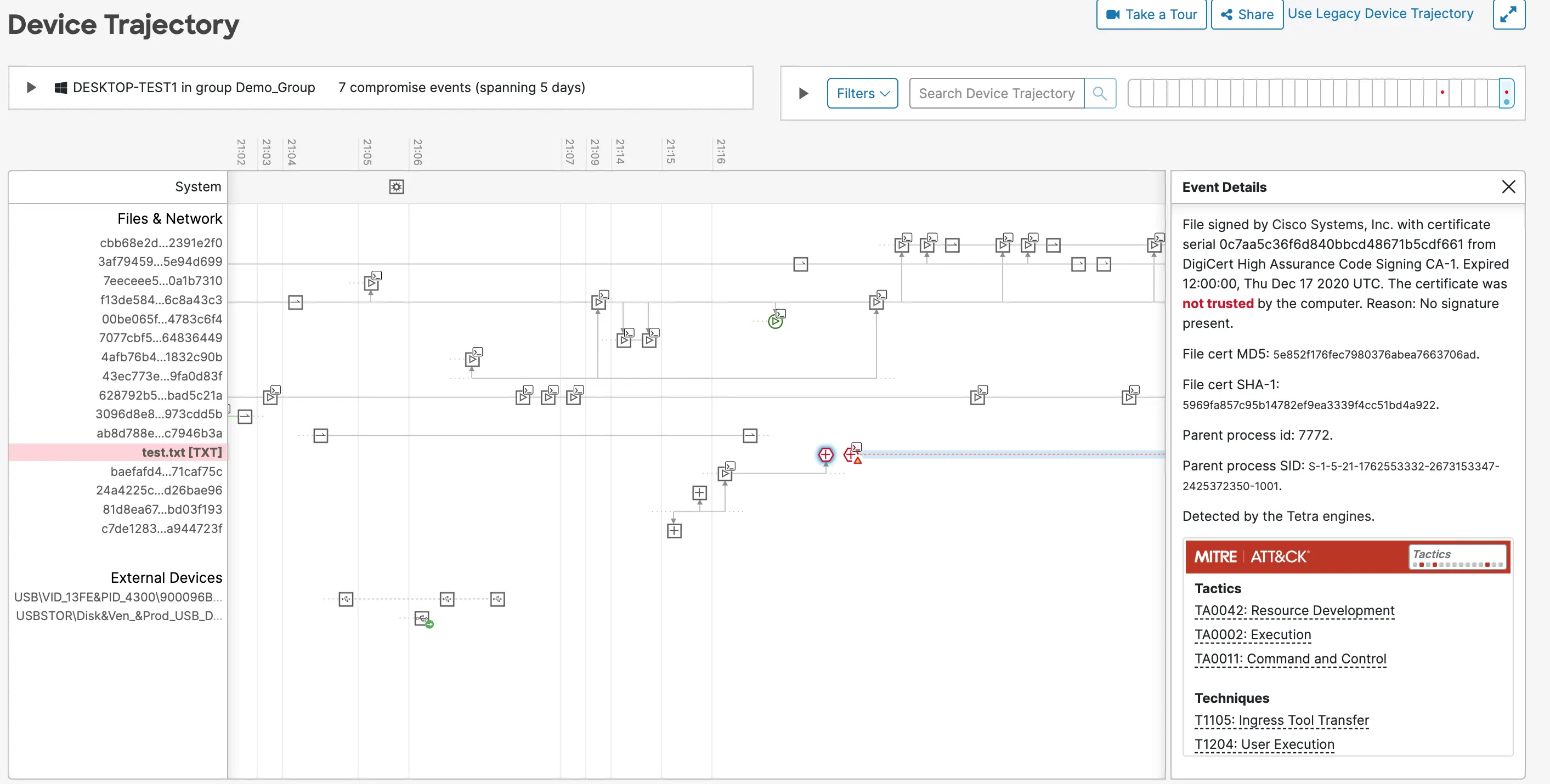
The screenshot below shows the Device Trajectory view in the Secure Endpoint console, with the Activity Telemetry captured.
Behavioral Telemetry
This specific type of telemetry is displayed in the Device Trajectory view after analysis by the detection engine. It is triggered when a malicious activity is linked to an otherwise benign activity, providing additional context to help distinguish between benign and malicious actions.
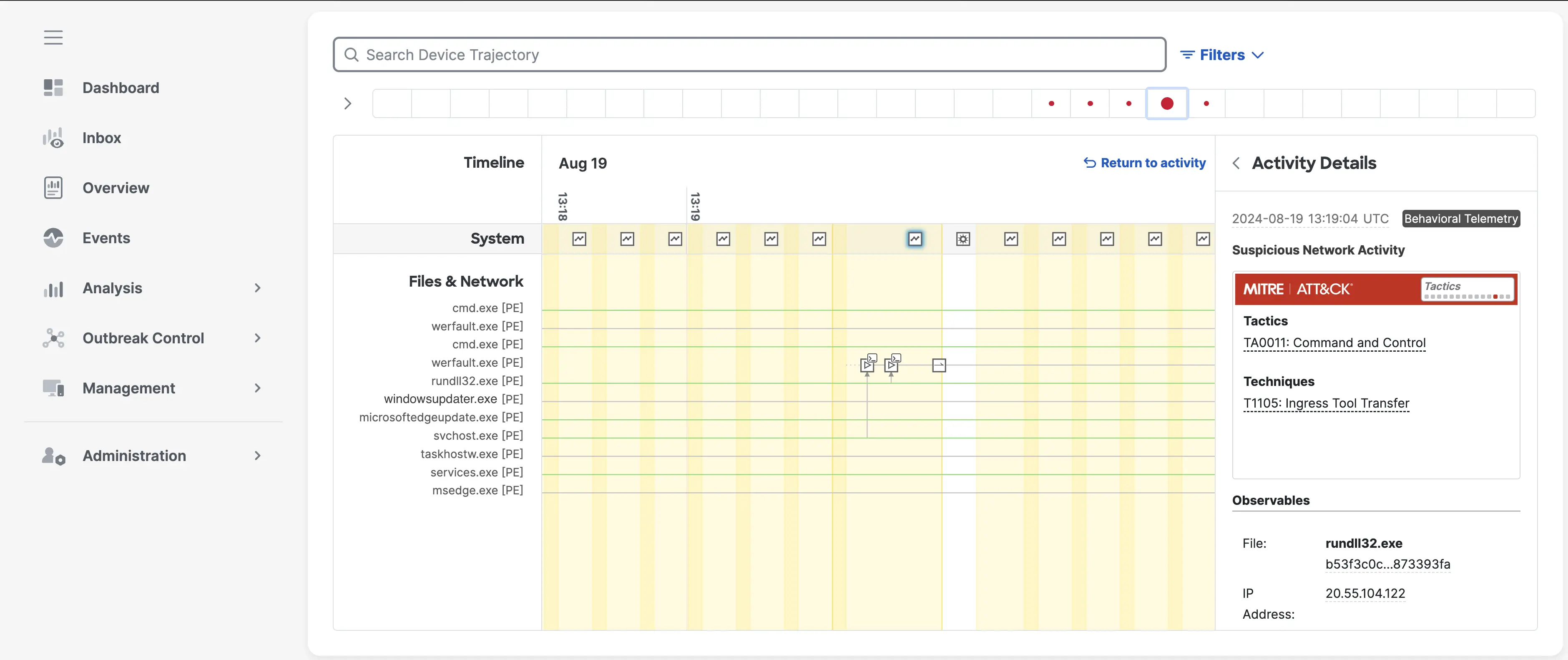
The screenshot below shows the Device Trajectory view in the Secure Endpoint console, highlighting Behavioral Telemetry identified by the detection engine. In this example, the rundll32.exe process is associated with suspicious network activity.
The telemetry details captured by Secure Endpoint in this view provide crucial context around the observed activity, allowing security teams to quickly assess the situation. This enriched information not only aids in identifying the nature and intent of the activity but also empowers teams to conduct more thorough and effective investigations. By offering a deeper understanding of potential threats, Secure Endpoint helps to streamline the threat detection process, reducing response times and enhancing overall security posture.
Conclusion
The exploration of Cisco Secure Endpoint’s detection events and telemetry highlights the power of visibility in early attack detection. By monitoring and analyzing endpoint behavior, organizations gain valuable insights into potential threats, allowing them to detect and respond to attacks at their earliest stages. This enhanced visibility is key to safeguarding critical systems and fortifying defenses against evolving cyber threats.
References
- Cisco Talos Blog — Hunting for LoLBins
- Cisco Talos Blog — Trickbot: A primer
- CISA Cybersecurity Advisory — TrickBot Malware
- MITRE ATT&CK Framework
We’d love to hear what you think. Ask a Question, Comment Below, and Stay Connected with Cisco Security on social!
Cisco Security Social Channels






Excellent write up!
Your blog post was insightful and well-written! I loved how you made complex ideas easy to understand with real-world examples. Great job!